← Security Now (Audio)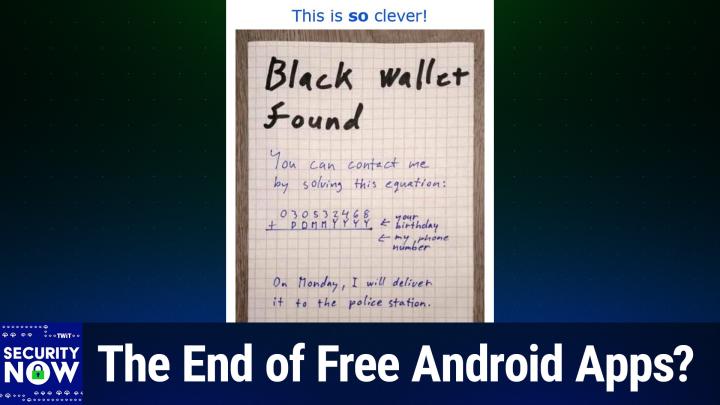
Security Now (Audio)
SN 1046: Google's Developer Registration Decree - The End of Free Android Apps?
02:44:44
The End of Free Android Apps?
Loading summary
Transcript210 lines
- [00:00]
Leo Laporte
Morning, Zoe.
- [00:01]
Steve Gibson
Got donuts. Jeff Bridges, why are you still living above our garage? Well, I dig the mattress and I.
- [00:08]
Leo Laporte
Want to be in a T mobile.
- [00:09]
Steve Gibson
Commercial like you teach me. So Dana. Oh no, I'm not really prepared. I couldn't possibly at T Mobile get the new iPhone 17 Pro on them. It's designed to be the most powerful iPhone yet and has the ultimate pro camera system. Wow, impressive.
- [00:25]
Leo Laporte
Let me try. T mobile is the best place to get iPhone 17 Pro because they've got the best network. Nice.
- [00:32]
Steve Gibson
Je free. You heard them. T mobile is the best place to get the new iPhone 17 Pro on us with eligible traded in any condition.
- [00:40]
Leo Laporte
So what are we having for lunch?
- [00:42]
Steve Gibson
Dude, my work here is done.
- [00:44]
Leo Laporte
The 24 month bill credit on experience.
- [00:45]
Steve Gibson
Beyond for well qualified customers plus tax.
- [00:47]
Leo Laporte
And $35 device connection charge credit send and balance due if you pay off earlier, Cancel Finance Agreement. IPhone 17 Pro 256 gigs 1099.99 A.
- [00:53]
Steve Gibson
New line minimum 100 plus a month.
- [00:54]
Leo Laporte
Plan with auto pay plus taxes and fees required. Best mobile network in the US based on analysis by Oklahoma Speed Test Intelligence Data 182025 Visit T mobile.com it's time for Security Now. Steve Gibson is here once again making you aware of issues in our community like the Tuesday vote in the EU on chat control. What's wrong with that? Well, Steve will explain. He'll also talk about Brave's assertion that it's three times faster than other browsers. Really? Researchers create the wildest battering RAM attack device you've ever seen. And then we will talk about Google's plan to require everybody developing for Android to register with them. Is that a good idea? I think not. Let's find out what Steve thinks next on Security Now. Podcasts you love from people you trust. This is Twit. This is Security now with Steve Gibson. Episode 1046 recorded Tuesday, October 7, 2025. Google's Developer Registration decree. It's time for Security now, the show where we get together with the brightest man I know and talk about the latest in security news. Technology with a dash of sci fi. And every once in a while a pretty funny little picture of the week.
- [02:21]
Steve Gibson
That's Stevenson actually do have a dash of sci fi, which we'll be getting to. We have a release date for the second volume or the second tome of Peter Hamilton's, whatever that means.
- [02:36]
Leo Laporte
I have to finish that thing.
- [02:38]
Steve Gibson
Oh, I. I don't know. We'll talk about it. I don't know. But yeah, we've got. I have A ton of news. That's it.
- [02:48]
Leo Laporte
By the way. That's when I bought the hardcover book. We were talking about having a lot of stuff, you know, physical media and how I love books, but I bought the physical book because I thought it'd be nice to have on my bookshelf. I can never move.
- [03:03]
Steve Gibson
As I said, you and I love books. I do, I do. I mean, I have a library.
- [03:09]
Leo Laporte
Whole room dedicated to books. It's beautiful.
- [03:11]
Steve Gibson
Well, and I remember, you know, that was all there was once upon a time. So you spent a lot of time paging through books and now you. I have this huge library. I was telling Leo before that I'm going to be, you know, basically downsizing where my wife and I are moving to another place and we're not going to bring anything that we don't actually need because it's a good thing to do.
- [03:38]
Leo Laporte
You're going to do the Marie Kondo thing. You're going to. Yeah, you know, you know about that, right? If it doesn't spark joy, get rid of it. You hold it up. You say, does this spark joy?
- [03:48]
Steve Gibson
Oh, unfortunately, Leo, pretty much everything sparks joy. So that's, that's not my cr. That's not my criteria. I would love to have the ability to hold just to keep everything. But I mean they're, they're. I'm pointing with my finger there. That is a hard disk exerciser for a Cal Comp CDC or something or other, you know.
- [04:14]
Leo Laporte
Well, you can never get rid of that.
- [04:18]
Steve Gibson
Actually I do. I, I and I have a garage full of PDP8s and PDP11s and things. So, you know, but I think I'm gonna, I'm gonna ask those guaranteed obsolescence guys how they would like to have some actual.
- [04:31]
Leo Laporte
There you go.
- [04:32]
Steve Gibson
Yeah, I think they would appreciate some.
- [04:34]
Leo Laporte
Reference, some reference gear. Yeah.
- [04:36]
Steve Gibson
Yeah.
- [04:37]
Leo Laporte
So what are we going to talk about on the show besides this great picture of the week?
- [04:41]
Steve Gibson
Lots of stuff. Are, are the. For. For 1046 the. Here's our, you know, first show of October, a ton of news. Qantas says no. No one can re leak their stolen data, which is the weirdest thing. We talked about this a few weeks ago. They got a temporary injunction. Now it's permanent. But what. Anyway, we'll get there. Braves. The brave browser's usage is up, but they make a claim that is just so annoying. I mean to me it just, it ends their credibility for them to say their browser is three times faster than, than the competition. It's like what it's Based on chromium. It's the same as the competition. Anyway. Next Tuesday, the eu. Oh boy, everyone's holding their breath on this one. There's been some motion among the various countries in the EU will be voting on chat control. That'll be the 14th so. So I don't think we'll have any probably results by next Tuesday's podcast, but certainly the one after. Microsoft has formally launched a security store. So maybe you can actually buy security from Microsoft. I wouldn't hold my breath, but okay, they're selling something. Outlook has decided that they Want to block JavaScript in SVGs. Oh, we have a new release of Chrome Gmail saying they will no longer pull external email via pop. That's not security related but I thought maybe that would affect our listeners so I wanted to let them know because I ran across it when I was digging around through other stuff. Google Drive to start blocking ransomware encryption, the UK has reissued an order to Apple. I love that they're ordering Apple to do something. Good luck. Researchers have created something called the battering ram attack device hacker 1 We've got news on their bug bounty payoffs imager. That service has gone dark across the uk. Guess why Netherlands has plans to say no to chat control. We'll be talking about that. Discord was breached and guess what leaked out. Oh boy, we saw this coming. Also Salesforce is saying oh no, that was not another new breach. They're trying to do some damage control still Signal introducing post quantum ratcheting. They have right now a double ratchet. That's not good enough for these guys. I mean they are really serious about encryption. We're getting a triple ratchet and it turns out your motherboard might. Your motherboard might actually support TPM 2.0 and you wouldn't know it and Windows wouldn't tell you. So finally, once all of that and a picture of the week and some feedback from our listeners and a brief mention about Spinrite and a little bit of sci fi. We're going to look at how Google has decided to force Android devs to register, provide formal identification and pay and what that means for the Android Store. We have. I found a really beautifully written response from a well known guy who has been doing a lot of work over at fdroid saying that basically F Droid is F'd toast. Google does this.
- [08:12]
Leo Laporte
I'm so disappointed. I really wanted to hear what you have to say about this.
- [08:15]
Steve Gibson
Yeah, it feels like a bait and switch. I mean like now, now, now that we've got you all here. We're gonna make you unmask. Anyway.
- [08:23]
Leo Laporte
Well, I don't know if you listen to Mac Break Weekly earlier, but we were talking about with Apple's withdrawal of Ice Block. Thank. At the request of the federal government, we were saying, you know, really, maybe the solution is having a second store or apps so you're not the sole place people can get apps from. But Google seems to be moving in the opposite direction. They like it. They like that. Lock in. Well, we'll talk about that in a little bit. Yeah, I have the picture of the week queued up. My reaction will be fresh and unsullied. I have.
- [08:57]
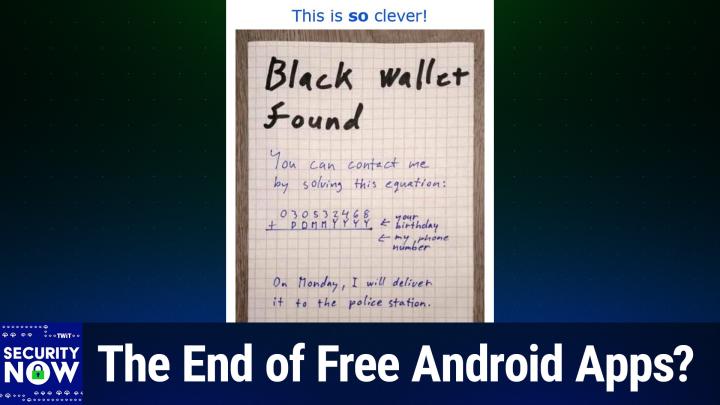
Steve Gibson
And not immediate. I should explain to our listeners what I already said to you. This is a wonderful picture of the week. I mean, this is like tailor made for this podcast. But when I saw it, I had to like, what? And like read it all about it and look, think about it for a minute. And then it was like, omg, this is the cleverest thing. Now, okay, I. I know it's not the cleverest thing I ever saw, but I want to say that it's.
- [09:28]
Leo Laporte
It's up there. It's in the top way.
- [09:30]
Steve Gibson
Isn't just great?
- [09:32]
Leo Laporte
Yes. All right, that's coming up as you continue, as we continue with security now and you continue to listen, we're glad you're here today. Our show brought to you by Threat Locker. If you, if you don't know about Threat Locker and you've got a business to protect, you're going to be glad you were listening. Ransomware is just killing businesses everywhere. Talked about Jaguar last week. There was another big ransomware attack this week. Oh, I've forgotten who it was, but it was like, oh, my gosh. I mean, it's just, it's not, it's. It's. I mean, right. How can you remember there's a new one every five minutes? Well, Threat Locker can prevent that. It can keep you from being the next victim being in the headlines. Oh, another company shut down by ransomware. Threat Locker does it in the best way possible. Threat Locker does zero trust. Yeah, it's a zero trust platform. That means it takes a proactive, and these are the keywords. Deny. By default approach, it blocks every unauthorized action unless you explicitly say, this person can use this app. This app can go here, this network device could be accessed by this person there. Unless you explicitly authorize it, it blocks it. That protects you from zero days threats, you know, but threats you never even heard of. Stuff coming in all sorts of ways. That's why if you cannot afford, can't afford to go down for one minute, you need threat locker. That's like, that's why JetBlue uses a threat locker. That's why the Port of Vancouver uses Threat Locker. Threat Locker shields you from zero day exploits from supply chain attacks and provides complete audit trails for compliance. It's the best of both worlds. As more and more criminals turn to malvertising and you've heard us talk about this, you need more than just traditional security tools to protect yourself. Attackers create fake websites. They're very convincing. They impersonate, you know, brands, you know, it's easy to do that by the way. It's trivial. A 15 year old can do it. They, they, maybe they look like your favorite AI tool or a software application or SaaS application, right? Then they distribute the links through social media ads and hijacked accounts. But their, their real trick is to use legitimate ad networks to deliver malware. Which means your employees browsing on work systems, even if they go to reliable, trustworthy sites are going to be exposed to that malvertising. And unfortunately, traditional security tools often miss these attacks. They're smart. The bad guys use fileless payloads. They run in memory only. They exploit trusted services that bypass typical filters. But they can't bypassed Threat Locker. Threat Locker's innovative ring fencing technology strengthens endpoint defense by controlling which applications, which scripts can access or execute. So it completely limits the possibilities for this malvertizing. It contains potential threats even if those malicious ads successfully reach the device. And frankly, as we've talked about Steve, they're gonna, it's almost impossible, you know, not to be exposed. But Threat Locker stops them cold. It works across all industries, works on PCs and Macs. They get, you get great 247 US based support and it enables comprehensive visibility and control. Ask Jack Senisap, he's director of IT infrastructure and security at Redner's Markets. Another, another company that doesn't want to be down for even one minute. He says, quote, when it comes to Threat Locker, the team stands by their product. ThreatLocker's onboarding phase was a very good experience and they were very hands on. Threat Locker was able to help me and guide me to where I am in our environment today, end quote. Where he is, he feels secure, he feels safe. Because bad guys can't traverse the network, they can't go anywhere they want, they can't run anything they want. Get unprecedented protection quickly, easily and cost effectively with threat locker. Visit threatlocker.com twit to get a free 30 day trial. Learn more about how ThreatLocker can help mitigate unknown threats and ensure compliance. That's threatlocker.com twit I will throw this in. You can quote me. Threatlocker makes it so easy to do zero trust. And I mean it's basically turnkey. And you will really appreciate the value you get from them. It's very affordable. Threatlocker.com Twitter if nothing else, if you get nothing else from this show, check them out. This is going to be a LifeSaver for you. ThreatLocker.com Twin I know you're going to get a lot of other things from this show, but even if you only get that one thing. Now we go back to Steve and I shall pull up the picture of the week and I will actually, you know what, let me leave all three of us on screen because I think this will fit. And I'm going to scroll up. This is so clever. You can see me trying to decipher this. It says, black wallet found. You can contact me by solving this equation. Okay, now I need to go full screen. You add your birthday to this number and that will give you your phone number. On Monday, I will deliver it to the police station. Ah, because the wallet has his driver's license, so the guy who posted this knows what his birthday is. So he has encoded his phone number. And you would only be able to get his phone number if you knew what your birthday was, if you're the owner. Brilliant.
- [15:15]
Steve Gibson
Exactly. Isn't that just so cool?
- [15:19]
Leo Laporte
Yeah. You know, the other day I was walking by a store, it said, lost keys come in. If, if you're missing your keys. And they hung the keys on the sign that said lost keys. That's not how you do it. You say, I've got them in my pocket. Can you describe them? Right, right. This is a great way.
- [15:41]
Steve Gibson
Right? I thought this was just so clever. So for those who are, or who are listening to this going, huh, huh, what? Okay, so some person, Lou, has left his wallet, you know, like it fell out of his back pocket when he was at the restaurant. And some clever person comes along and discovers the wallet and he thinks, okay, well, now I found the guy's wallet and I want to make sure it gets back to him. So how can I leave a note such that only the legitimate owner of the wallet will be. Will essentially authenticate himself and give me a. And, and call me so that we can arrange to get his wallet back to him. So the, the, the person who discovers the wallet knows what his his own phone number is. So he writes his own phone number out. Then beneath that, he puts down the day, month and year under the digits, right. Aligned of his phone number and subtracts those two numbers. The phone number will be 10 digits, so it's larger than the day, month and year. Subtracts the day, month and year. Getting a new number.
- [17:04]
Leo Laporte
You know that he did it that way because this is written on graph paper, so.
- [17:08]
Steve Gibson
Yeah.
- [17:08]
Leo Laporte
And everything fits nicely into a little square.
- [17:10]
Steve Gibson
They are, you're right, they are. They are lined up in, in, in the graph squares. Yes. Yeah, in the cells. So then he takes the resulting number and this is what he writes down on this piece of paper. Because since he, since his phone number minus the guy's day, month and year birth date created another number. When you take that other number and add the g. The, the lost wallet owner's day, month and year number, you'll get back the, the, the, the, the, the. The phone number of the person who discovered and is holding the wallet. Anyway, I just, this, I just thought this was so clever.
- [17:51]
Leo Laporte
Good way to do it.
- [17:52]
Steve Gibson
I like it, sir. Many of our listeners thought. Got it and thought it was great. A couple. Because there are listeners, of course, birthday collisions.
- [18:03]
Leo Laporte
Right. Birthday collisions.
- [18:04]
Steve Gibson
Not that as much as the fact that. Come on now, if the year is four digits, you know, it's gon be 19, maybe 20.
- [18:14]
Leo Laporte
Yeah.
- [18:14]
Steve Gibson
So anyway, they, everybody understands the, the, the, the nature of entropy. And we've gone over that for years and various, for re. Various reasons and forums in on the podcast. So they're like, you know, this could have been better. And other people wanted the, the, the day, month and year moved into other orders for various reasons or, or the digits interposed. I said, okay, you know, yeah, but you know what, the idea, you know what?
- [18:42]
Leo Laporte
And this is the idea. Just a filter system, right. So he has a second factor authentication, you know, like what, what's in the wallet or something like that. This is just a filter.
- [18:54]
Steve Gibson
Presumably there's a picture of the guy on his driver's license. So when the guy shows up, he's gonna be like, wait a minute, you used to have blonde hair.
- [19:02]
Leo Laporte
So I think you could just pop that in the mail and the post office will deliver it. But that's all right.
- [19:06]
Steve Gibson
I know, I just thought it was very clever. Okay. So we touched on this weird story in July after the Australian airline Qantas, you know, Australia's big famous airline Qantas, was able to obtain a temporary injunction. Get this. To prevent the use of data which had been stolen from them in a recent ransomware attack. Okay, what now? I mean, even then. Okay, so that temporary injunction has now been made permanent by the Australian New South Wales Supreme Court. This court order which Qantas now has, prevents third parties from publishing, viewing, can't even look at it, or accessing the data if it should be released by the attackers. Turns out that this was a bad breach. 5.7 million Qantas Airlines customers were compromised in a data breach, which there was one. It was a breach of one of the airline's call centers. The data that was stolen included the business and residential addresses attached to 1.3 million accounts, phone numbers of 900,000 customers, and the dates of birth of a further 1.1 million. So it's a mess. The ruling justice of the Supreme Court in this case also agreed to impose a six month non. What, what they called a non publication order, basically a gag order for the press over the names of the, this, they call them solicitors in Australia. You know, the, the attorneys who were acting on Qantas behalf in. The attorneys insisted that their identities not be published in any press coverage for fear of retaliation from the attackers. You know, this is the world we live in today where, you know, like everyone feels vulnerable even if you didn't do anything and you're not high profile. So the whole thing seems really bizarre now. I'm pretty certain that the attackers could not care less. The attackers, who were probably in Russia or China, could not care less who Qantas hired to obtain an order blocking the publication of their stolen data, any more than they could care about some Australian court order blocking the publication of that data. It's not as if anyone who might use the stolen data would be law abiding and would feel the least bit constrained by some court order issued by another country. You know, the data would be released to the dark web, perhaps you know, to be merged into a larger aggregate database which we've seen in the past. Who knows? But you know, no reputable law abiding entity that might manage to obtain the data would be republishing it anyway, with or without a Supreme Court order. So anyway, the only thing that makes sense to me, some of the coverage had a picture of the, the c. The Qantas CEO. The only thing that made sense to me is that this was just a, what you might call a CYA move by the Qantas CEO to appear to be doing whatever responsible thing could be arranged after one of their call centers was breached. So, you know, maybe this Looks good to the shareholders. Oh, we got a court order and the Supreme Court is given us a permanent injunction against our data being, you know, looked at by anyone who might see it after it's been released. It's like, okay, well, the bad news is, you know, you were breached. One would hope that they're spending equal time and money shoring up the security of their systems to prevent more trouble like this in the future. Because I don't think that the bad guys are going to be moved by the. By. By them obtaining a court order. Okay, this one, the news is the news that generated the posting from Brave was the Brave Browser has surpassed 100 million active monthly users, or monthly active. Yeah, MAU monthly active users is their abbreviation. So here's what they wrote and then we'll talk about it. Over the past two years, they said the Brave browser has seen an average of about 2.5 million net new users each month. This September, we officially surpassed 100 million monthly active users. MAU, they said, worldwide. At the same time, we surpassed 42 million daily active users. Of course, that's DAU they share with us for a D a DAU to MAU ratio of 0.42, underlining the high engagement that users have with Brave. And I completely agree with that. If you've got 42 million daily active users, though, you've got, you know, basically 42 million people for whom Brave is their browser. You know, they don't have it like, added to their collection of browsers. Let's see, what should I use today? Chrome? I'm. I want to use Firefox or Brave. No, they're just using Brave, they said. This growth has been fueled by a global awareness that Brave is an alternative to big tech and that users benefit greatly from a browser that preserves their privacy and is up to three times faster. Huh. Than competitors. Also, when users are given a choice, users exercise that choice and switch to new browsers. For example, daily installs for brave on iOS in the EU went up 50% with the new browser choice panel following the implementation of the DMA and the release of iOS 17.4 back in 2024. Okay, so they go on, but we don't care. Their usage numbers are nice, as I said, and they have an impressive, you know, upward pointing graph. But what really annoyed me was their utterly bogus claim. I mean, come on.
- [25:53]
Leo Laporte
Wait a minute. They've got weasel words up to three times faster. Means if you're using like Internet Explorer 6, right?
- [26:01]
Steve Gibson
Okay, but that's not a competitor, really. But they're saying. But yeah, yeah, if you got that, wait, my pine. My Palm Pilot browser.
- [26:11]
Leo Laporte
Exactly.
- [26:12]
Steve Gibson
I would imagine.
- [26:13]
Leo Laporte
I'm sure there are browsers that are a third as fast as if I.
- [26:16]
Steve Gibson
Took it out of the refrigerator and warmed it up. Yeah, yeah.
- [26:19]
Leo Laporte
By the way, are you going to take that with you when you move?
- [26:22]
Steve Gibson
So I, I call nonsense on this. Brave, as we know, is based on the same Chromium engine as Chrome, Edge, Vivaldi and Opera, their competitors. And believe me, if it was possible for any of those browsers to go any faster, they already would be. It's not as if the Brave folks have some magic pixie dust that they're, you know, they're keeping to themselves, which magically triples the speed of their browser. Brave is no faster than any of those others when it's doing the same job. And that's the key, you know, it can't be the only possible way for any browser that's using the same underlying engine code to render pages any faster would be for it to be rendering less of those pages. And that's the only way I can see Brave makes any claim at all, but 300%. Give me a break. If you managed to find a web page that's massively loaded down with large advertisements, bringing massive JavaScript blobs and tracking code and heavy scripting all being served by slow servers a long ways away, then okay, sure, okay, if if Brave's privacy enhancing policies block some of that crap from being loaded at all, it gets to declare done for that page faster than its sibling competitors. But only because Brave is choosing to render a partial page whereas the rest of them are are rendering the page's entire burden. So the claim did drive me to poke around the net to see what I could find. There are some useful head to head benchmarks comparisons on the Android platform where when Brave is loading a heavily privacy disrespecting page, it manages to perform around 21% better than browsers that are rendering the entire page. So that's useful. You know, it means that sometimes Brave will indeed be a little bit faster than other browsers. But you know, Brave should be ashamed of themselves for claiming that users will in any meaningful way actually ever experience Brave running three times faster than its competitors. As I noted, you know, they're actually all the same browser. They differ only in UI and feature policies, not in their underlying page rendering technologies. Is it sure that they can decide not to render some things that they think are privacy invading and in not rendering them, they'll Finish a little quicker than the browsers that do render everything that they're being asked to render.
- [29:37]
Leo Laporte
I guess the real question is, is the Blink engine or the Chromium engine any faster than Firefox's engine or WebKit Safari's?
- [29:45]
Steve Gibson
That would be, it'd be Safari or Firefox would be the actual alternative to compare. I just looked at this saying, you know, we're 300% faster than our competitors. It's like if you were, you wouldn't have any competition. You know, one of the things that we know Google found out very early on is how fast they had to make Chrome. And, you know, they spent a long time working on Chrome speed optimization back in the day. I have a chart here in the show notes, bottom of page three, showing the Brave adoption. And I mean, it's impressive. There's no doubt about it. I mean, Brave is doing well. People are responding to, you know, the, the, Well, I mean, I did when I, when I, when Firefox wasn't randomizing my fingerprint, I switched to Brave for a while. I came home to Firefox. But, you know, I could see people, you know, thinking, hey, I, I, what the hell, it's just as fast. Maybe it's three times faster. No, but I might as well use Brave.
- [30:51]
Leo Laporte
I don't like all other things crypto association with Brave and I'm not too crazy about Brendan Icke, so I don't. Yeah, you know, there are other choices. I use helium. Lately I've been using Helium, which is a chromium de googled Chrome chromium fork that has what, Ublock origin built in. So you, you get Ublock origin back and it's just like Chrome. And I bet you that's faster than Brave because it doesn't have all the bat tokens and all the other stuff Brave's doing.
- [31:20]
Steve Gibson
Right, right, right, right.
- [31:23]
Leo Laporte
It feels pretty snack.
- [31:24]
Steve Gibson
Okay, so next Tuesday, As I mentioned, October 14, the EU member countries vote on chat control, as it's informally known. Some news coverage from last Wednesday, which I had Firefox translate from German, reads the head of the messenger app Signal, who you know, we all know is Signals president Meredith Whitaker, threatens to withdraw from the European market. The reason is the EU's plan to install backdoors in apps that allow automatic search for criminal content. That's actually a pretty good, a pretty good explanation of what this boils down to. The head of this, the data. The translation continues. The head of the Signal app has criticized plans in the eu according to which Signal, messenger should have back doors to enable the automatic search for criminal content. Meredith Whitaker told the DPA news agency, quote, if we were faced and boys, you know, she just might have. She probably has this printed on her business cards. She just hands that out. If we were faced with a choice of either undermining the integrity of our encryption and our privacy safeguards or leaving Europe, we would unfortunately make the decision to leave the market. Which, you know, Leo, if this goes far enough, means that only our own administration will be using Signal. But anyway.
- [32:57]
Leo Laporte
By the way, that's one of the things about check control that the eu right legislators exempt government excludes.
- [33:07]
Steve Gibson
Yes.
- [33:08]
Leo Laporte
Holy cow, that's a towel right there.
- [33:11]
Steve Gibson
How exactly is that going to work in practice? Yeah, like you know, how, how do you tell, you know Signal? Oh, no, no, I'm with the parliament. So you can't look at, you can't look at my pictures. So the, the, this announcement said the European Union has been deliberating for three years. Yes, because I mean admittedly these are hard problems on a law to re. Regulate the fight against depictions of child sexual abuse. The proposal of the corresponding regulation stipulates that Messengers such as WhatsApp, Signal, Telegram or Threema should enable the content to be checked before encryption. Okay, now that's key should be checked before encryption. This is not the first time that we've seen this new language talking about checking the content before its encryption. If this were going to be done, that's the way to do it. You know, you have an image that's essentially in plain text before it's pushed through the encrypted tunnel. So don't screw with the encryption, don't mess with back doors or any of that nonsense. If you insist upon breaching the user's privacy, don't also weaken the integrity of their communications. At the same time, simply check the image before it's sent or after it's received. But here's where I hope somebody with some technical chops is paying attention. No application running on iOS or Android has any contact whatsoever with the underlying imaging hardware, either its capture or its display. All of the messaging and communications apps are application programs. So they are accessing an application program interface, which we short we shortened to API, which is published by the underlying operating system. To give its client applications, those programs, those apps running on it, access to camera and stored images and the device's screen. The API deliberately divorces all of the hundreds of thousands of platform applications from the underlying hardware. This allows the manufacturer the freedom to change their smartphone hardware at Will it explains why the same app can run on wildly differing smartphones without any trouble at all. And of course you know, this is all computer Science Operating Systems 101 during the first year, it turns out of my life, 70 years ago, between 1955 and 1956, just shortly before you were born. Leo General Motors research working with IBM developed the what was known as the GM for General Motors hyphen NAAIO system for the IBM Model 704 mainframe computer that work for the first time in human history used an I O abstraction layer between the programs running on the machine and its underlying hardware. I had no idea.
- [36:50]
Leo Laporte
Fascinating.
- [36:51]
Steve Gibson
Needless to say, the idea was a good one and it stuck and it's been evolving ever since. So here's my point. It is completely wrong headed for any legislation to be aimed at at any communicating platform application, whether it's encrypted or not. That's the wrong target. And if that's the target, that is. And if, if it is made to be the target, then we're playing an endless game of whack a mole. The legislation should be directed at the underlying operating system. It's the OS that runs the camera and the screen and the storage. It's not any messenger app's fault if it's given an abusive image to send. It's the operating system that gave that image to the messenger app in the first place. The operating system always sees the image first. And if the EU insists upon some behavior based upon the detected content of the image, then the operating system is the proper place to have that happen. If this is not done, then every application that communicates, whether encrypted or not, will need to be doing this. Including iOS's and androids will own built in encrypted messenger apps. You know we have printer drivers today so that every application doesn't need to bring along its own collection of printer drivers. Filtering messaging content is exactly the same. Rather than expecting every application to do this separately, which is crazy, especially since I, you know iOS and Android will also be needing to have this technology themselves to support their own legally EU compliant messaging apps. It ought to be centralized. And that solves the problem of of you of there being black market messaging apps that don't do this. Whereas the good apps are complying, if this is moved into the underlying os, no apps will have access to the hardware and there's no way to get around this. So I just wanted to make sure everybody understood that there is one place for this to happen. Lord knows Apple doesn't want to have anything to do with that. I don't know where Google and Android would stand, but, but that's, that's the right target for this legislation. So we don't know what's going to happen one week from today, but, you know, it's only a week away. Twelve of the EU bloc's 27 members are, have publicly stated that they are going to back the proposal with yays. Eight are against, and the rest have said they're undecided. The proposal will pass if the Council is able to obtain what they define as qualified majority. In this case, that means at least 55% of the 27 member states. So that would be 15 of 27, and that majority must also represent at least 65% of the EU's total aggregate population. Also, the measure could be blocked by at least four countries, which represent more than 35% of the EU population, voting no. So, you know, this is obviously a big deal. We'll know in a week or in a week or two, but the vote will be happening next Tuesday. So really interesting to see how this thing shakes out. With any luck, it'll just, it won't succeed again, in which case they'll, you know, who knows what, try to change it, amend it, you know, three years and counting. So this is obviously a heavy lift. Leo, we're going to talk about Microsoft's Security Store, which they just announced last week.
- [41:25]
Leo Laporte
Oh, I didn't know security was for sale.
- [41:28]
Steve Gibson
Oh, yeah, because that's a profit center, Leo. If you got bugs, you can charge for fixing them.
- [41:34]
Leo Laporte
The Security Store. Let's all go shopping.
- [41:38]
Steve Gibson
Securitystore.Microsoft.com for anyone who wants to jump ahead.
- [41:42]
Leo Laporte
Unbelievable. I swear. All right, we're going to take a little break and get back with security now. In just a moment. This episode brought to you by Delete Me. I love. You know what I love is that all of our advertisers are, I would say, applicable to all of you. Right? I mean, here's a perfect example. Have you ever wondered how much of your personal data is on the Internet for anyone to see? It's not good. In fact, I don't recommend you do this. Search your name, your contact info. Steve and I were probably not exactly shocked, but chagrined to see our Social Security numbers in a breach. Your home address, even information about your family members. It's all being compiled by this shady little, but not illegal business called data brokers. These people collect this, they build dossiers on you, they sell that information online. To anybody. And it's not. So it's not just marketers, it's not just advertisers, it's insurance companies, it's foreign countries. Anyone on the web can buy those private details and you can imagine the horrific side effects. Identity theft, phishing attempts, doxing harassment. What are you going to do? Well, I would like to make a suggestion and I know about this because we've done it. Protect your privacy with Delete me. Look, I live in public. People know all sorts of stuff about me. You can find out more than you know, like on my Wikipedia page as my birthday. Although Steve, thanks for outing me on that. Well, that was just my birth year. But you can see the birthday on Wikipedia. You can see a lot of stuff. My wife's name, my kids names. It's easy to find that. So while I'm already in public and I. But I still. There's still stuff like my Social Security number. I really don't want to be out there. Unfortunately, it's easier than ever to find personal information about people online. If you search for your name, not only will you see a bunch of stuff, you'll also see websites. And these are the data brokers who say, for, for A$50, I'll tell you what Leo's prison record is. You know, stuff like that. You've seen it, right? This is why I personally recommend and use Delete Me. Delete Me is a subscription service that removes that personal info from hundreds of data brokers. And this is the key by law, the data brokers, it's not an illegal business, but they're supposed to have a takedown page, a form. Right, but there's a couple of problems. First of all, everybody puts them somewhere different, usually hidden away. And second, there are literally hundreds of data brokers, hundreds of. So you, I mean, you're not going to go from site to site. Third, there's new ones every day because it's such a lucrative business. So this is why you sign up. In fact, Delete Me is a great deal if you think about it. You give Delete me the information that you want deleted, right? Because not everything. You know, maybe you want some stuff still up there, but their experts will take it from there. They will do that. They will go to each of the sites, they will do the takedowns. This is their job. They're professionals. They could do it fast. They know exactly where to go. Then they will send you regular personalized privacy reports. You just got. Lisa just got another one showing what info they found, where they Found it. And the most important part, what they removed. See, Delete Me isn't just a one time only service. It wouldn't be much use if it were because these guys, these data brokers are, they'll take it down. But then they immediately start rebuilding the dossier. And even if they don't, there's new data brokers all the time. But thankfully DeleteMe's there, always working for you. Constantly monitoring and removing the personal information you don't want on the Internet. To put it simply, DeleteMe does all the hard work of wiping you and your family's personal information from data broker websites. They do it for you, take control of your data, keep your private life private. By signing up for Deleteme. We've got a special discount for our listeners today. Get 20% off your Delete Me plan when you go to JoinDeleteMe.com TWIT and use the promo code TWIT at checkout. Again JoinDeleteMe.com TWIT use the promo code Twitter checkout. Now the only way to get 20% off is to go to JoinDeleteMe.com TWiT and use that offer code TWiT at checkout JoinDeleteMe.com Twitter offer code Twitter. The reason I say that address many times is don't go to Delete me dot com. That's a European company that does GDPR takedowns. It's not the same thing. You want to, you want to get off the data broker sites. So the URL is, The address is joinedeleteme.com Twitter. Okay, very important. Join delete me.com/twitter and use the offer code Twitter. Well, I can tell you it really works. In fact, when Steve and I did that little search for our Social Security numbers, we also searched for leases. Hers weren't there because she uses Delete Me. Back to the show we go.
- [46:46]
Steve Gibson
So anyone going to the urlsecurity store.Microsoft.com will find themselves looking at Microsoft's just launched security store as the name would suggest from which Microsoft is literally selling Azure solution solutions. So just to be clear, this is not for end users, this is not for, you know, us. But it's an Azure cloud based and there it is on screen. Discover, buy and deploy security solutions and agents.
- [47:25]
Leo Laporte
I think their tagline should be yes, your security is for sale.
- [47:29]
Steve Gibson
Oh wow. So last Tuesday the Microsoft Security community blog posted the under the title introducing Microsoft Security Store which starts out saying security is being re engineered because you know, we didn't get it right. The first time for the AI era. Of course, we had to get that in moving beyond static rule bound controls, an after the fact response toward platform LED machine speed defense. Oh, that all sounds wonderful. I wonder what it costs. We recognize that defending against modern threats requires the full strength of an ecosystem combining our unique expertise and shared threat intelligence. But with so many options out there, it's tough for security personnel professionals to cut through the noise. In fact, of course they're creating some more and even tougher to navigate long procurement cycles. Yeah, you don't want those. You just want to click a button and have it and stitch together tools and data before seeing meaningful improvements. That's why we built Microsoft Security Store, a storefront designed for security professionals to discover, buy and deploy security SSAs solutions and AI agents from our ecosystem partners such as Darktrace, Illumio and BlueVoyant Security. SaaS solutions and AI agents on security Store integrate with Microsoft security products including Sentinel platform to enhance end to end protection. These integrated solutions and agents collaborate intelligently, sharing insights and leveraging AI to enhance critical security tasks like triage. Wait, isn't that what happens after you get attacked anyway? Threat hunting and access management. So anyway, the page continues at some length describing how the Security Store essentially allows security professionals to browse, point, click, purchase, deploy and manage their cloud security more easily than ever before. No more waiting for those pesky purchasing cycles and authorizations. You know, just get what you need and start using Microsoft's new security Copilot solutions in minutes. So I have no doubt that we have many listeners who will probably find this new Microsoft packaging and deployment to be very useful. So I just wanted to make sure that those listeners were aware of this new facility. I am fortunate that I have nothing to do with Azure and why we'll be able to live out the rest of my life happily with that statement remaining true, I'm quite sure. Okay, so there's welcome news on the scalable vector graphics security front. Remember earlier this year the world saw a dramatic rise in the abuse of SVG format image files. To ours and many other people's surprise and astonishment, it turns out that SVG image files being formatted and formally defined as XML have always, from version 1.0 allowed, been allowed to contain JavaScript, which would be faithfully executed whenever the image was rendered by whatever was rendering it. Like unfortunately, people's email clients. So this capability pretty much sat idle for most of that image format's life, because SVG has been around for quite a while until it was recently rediscovered by malefactors and started being abused with increasing frequency. So much so that the, I mean, like everybody, all the security industry did articles on the the explosion in scalable vector graphics abuse. Various product vendors, you know, change the behavior of their SVG rendering code, you know, such as stripping out script tags and its related code before rendering the the images that were being described by the SVG files. And to that end, Microsoft has just announced that they are joining that group. They said, starting September 2025, outlook for web and new Outlook for Windows. Remember, there's the old Outlook for Windows and the new Outlook for Windows. So if you're on the old one, you're good luck. The new Outlook for Windows will stop displaying inline SVG images, meaning at all. They're not even going to show you the image, they're just like, no, they're going to instead show a blank space. They said this affects under 0.1% of images, improves security and requires no user action. SVG attachments remain supported organizations should update documentation and inform users. Okay, so images embedded in Outlook email so that they would normally be displayed. Like when you look at the email, that will no longer happen. You just get a little, you know, an empty rectangle. And this only applies to SVG images, which, as Microsoft correctly notes, accounts for a minuscule percentage of all email images. When any of us are sending images around in email, we're using GIFs, JPEGs and PNGs. That's your typical embedded email image format. So anyone who needs to send an email can attach an SVG file to the email. It will not be rendered, but it'll be there as an attachment. So tough luck, bad guys. You had what, nine months and then everyone finally responded. So unfortunately, nine months is quite a while. Still, Chrome has Advanced to version 141. The web functions that Chrome supports moved forward. There was something about wallet credentials being changed. I jumped on that thing. Oh, maybe this is wonderful. Turns out it was just an incremental little tweak. Nothing significant. There were two high, high priority vulnerabilities patched. The most severe of the two, which was patched in one 40, so it's been fixed in 141 was a heap buffer overflow in the web GPU component. The person who discovered that earned themselves $25,000. And I, I just. When I, whenever I see these bounties being paid by CRO, by Google and, and for, for, for Chrome, I think that's the right way to go. You absolutely need to incentivize the, the security researchers to, you know, spend some time looking around and they're finding things. The second critical or high priority vulnerability was also a heat buffer overflow, but that one was in the browser's video component and that earned its reporter $4,000. There was also a $5,000 bounty paid for a side channel information leakage which was found in the storage component. All told, 21 security problems were fixed and Google paid out a total, you know, that that 25K4 and an additional 5, a total of 49K to external security researchers. So anyway, it's just clear that the concept of paying researchers bounties for their responsible reporting of bugs is a winning strategy. I did want to also mention just because I saw this, as I mentioned before, one little more note about Google, specifically Gmail, not security related, but perhaps affecting some of our listeners. Starting January of next year, Google will be eliminating Gmail's POP fetching feature, which pulls email from other external accounts via pop, the Post Office protocol, into Gmail accounts. So Google recommends that users who wish to have their other email accounts sent to their Gmail inboxes instead of having Gmail pull it using POP to have their mail forwarded to Gmail in order to get the transfer. So push it from the recipient end rather than pulling it from the Gmail end. And in a move that I expect we're going to be seeing everyone adopt, actually a lot of companies have so far Google announced that their drive product for Windows and Mac OS has been enhanced now to detect and block ransomware. And of course, you know, they couldn't resist tossing in the fact that it's enhanced with AI because you know Leo, you sprinkle some AI on anything and.
- [57:13]
Leo Laporte
It makes it better. Yeah. Oh yeah, that's right.
- [57:17]
Steve Gibson
So they announced quote while native Google workspace documents and they said eg Google Docs and Sheets are not impacted by ransomware and Chrome OS has never had a ransomware attack. OG Ransomware, they wrote, is a persistent threat for other file formats, PDFs, Microsoft Office, etc. And desktop operating systems, for example Microsoft Windows. They said that's why we're enhancing Google Drive for desktop with once again AI powered ransomware detection. Because you know, Leo, you need AI to detect ransomware to automatically stop file syncing and allow users to easily restore files with a few clicks. I've got a picture of the pop up that they gave as an example where over on. On top of, of your, your Google Drive ui, it pops up and says ransomware detected. File syncing paused on 08-12-2025 at 08:29am Then they say, what is ransomware? Harmful software that prevents access to a computer system until an amount of money is paid. Then it says your files are safely stored in Drive, but you need to remove the ransomware from your computer. You should also make sure you have effective and up to date antivirus software installed. Then they add drive keeps old file versions for 25 days, so you should initiate a restore in less than 25 days. No one says fewer anymore. Follow the steps to below to begin local file recovery. And then they go on.
- [59:03]
Leo Laporte
So that's a personal pet peeve of mine, by the way. I just hate it when they use less instead of fewer. I just.
- [59:09]
Steve Gibson
Me too. I. I hear it all the time and it's like, well, okay, if you.
- [59:14]
Leo Laporte
Can count it, use fewer.
- [59:16]
Steve Gibson
Exactly, yeah. And they said in addition, the built in virus detection in Drive as well as in Gmail and Chrome helps to prevent ransomware from spreading to other devices with the aim of taking over an entire network. As a result, these defenses can help organizations in industries such as healthcare, retail, education, manufacturing and government, and which is to say pretty much all industries from being disrupted by the types of ransomware attacks that have been so destructive up to this point. Drive for Desktop, available on Windows and Mac os, is used to effectively and securely sync users files documents to the cloud. Let's see, I don't think there's anything else that we don't know here. When Drive detects unusual activity that supports that that suggests a ransomware attack, meaning like lots of files are being scrambled, it automatically pauses syncing of affected files, helping to prevent widespread data corruption across an organization's drive and the disruption of work. Users then receive an alert on their desktop via email guiding them to restore. Oh, I'm sorry, on their desktop and via email. I was going to say wait a minute, that's not really very good. If it's only an email on their desktop and via email guiding them to restore their files and also of course notifying them that they apparently have ransomware that they didn't know about. And maybe their IT department doesn't yet either. Unlike traditional solutions they said that require complex reimaging or costly drive, costly third party tools they didn't say, or paying ransoms. The intuitive web interface in Drive allows users to easily restore multiple files to a previous healthy state with just a few clicks. This rapid recovery capability helps to minimize user interruption and data loss. Even when using traditional software such as Microsoft Windows and Office, which you know are always being hit by that nasty ransomware. So anyway, bravo Google. Other well known cloud based file backup solutions like Dropbox, Backblaze, Veeam, File Cloud and Scale T have been marketing similar ransomware protections for their backup solutions. So pretty much anytime you have file versioning and file deletion protection in place, you're going to be able to recover from anything that attempts to, you know, bulk encrypt your files. But it's nice to have, you know, Google Drive, which I know lots of people are using, also added to this list able to detect and disconnect to minimize the impact of something trying to, you know, encrypt all of your system's data under if at first you don't succeed Last Wednesday Reuters headline was UK makes new attempt to access Apple Cloud data. Reuters re reported a Financial Times article which was also published last Wednesday, which mostly recounted everything we already know. What's new is that according to the Financial Times report, the UK has now reissued a new order to Apple requiring them to provide access to the icloud data of any UK citizen. This amended their previous quote, you know, we demand access to anyone's data anywhere, unquote. And once again, Apple was reportedly not impressed. As before, all we have to go on here is off the record hearsay and speculation because Apple is gagged. But it seems clear that this newer order won't go any further with Apple than the last one did. I mean, Apple already disabled for the UK Anyone turning on their ADP Advanced Data protection feature. That's the immediate thing they did. They didn't turn it off for anybody else in the world, just for the uk. Sort of, sort of signaling what they were, you know, might be, you know, feeling the need to do if this actually happened. And it does look like in in this case Apple could, you know, say, okay fine, you are prescribing this only for UK citizens, so we will, you know, push an iOS update and flip the switch off or tell people that they have to give them some length of time to do it themselves and then force it off or something. Who knows? Anyway, this revised UK order appears to be responsive to the U. S administration which stepped into the fray objecting to a foreign government demanding access to the private data of US citizens. So the US likely has no such worries over what the UK does with its own citizens. In other words, that's fine if that's what the UK wants to do, but we know that Apple will be unhappy. But if that's what the UK forces, they'll just turn off ADP we also know that the UK's Investigatory Powers Tribunal, the IPT confirmed last April that Apple had appeared and to appeal the UK's earlier order. So it's going to be interesting to see what happens next. It may be that Apple reappeals this, trying to say, please don't make us do this, they may lose that appeal and then just turn off advanced data protection for everybody in the uk. Even though, you know, I got to say again, the Internet really, you know, we got all this geofencing going on all of a sudden, right. Where like blue sky people are dark in Mississippi, except that it turns out that people near Mississippi are getting black holed also because the Internet really, you know, exactly. What's a Mississippi ip? There's no such thing technically.
- [65:49]
Leo Laporte
Right.
- [65:50]
Steve Gibson
Wow. Okay. Now this is not relevant to software security, but it was so interesting that I knew that our listeners would want to at least like, look, see a picture of this thing and you could stick it up on the screen, Leo, if you want. At the bottom of page eight, the battering RAM attack a team of Belgian academics built at, actually it was KU Leuven. Those guys built a malicious memory module that can be used to break the confidentiality of modern cloud computing. And this is why it was like, okay, well, you know, hammering RAM is more significant to my mind, but the module which they call battering ram must be deployed by a rogue data center employee.
- [66:43]
Leo Laporte
Ah, you need physical access, of course. Yeah.
- [66:45]
Steve Gibson
Well, and look at it. It's actually an exchange extender. So it sits between the RAM and the motherboard and can allow attackers to break the security features of intel and AMD processors, which power cloud servers.
- [67:01]
Leo Laporte
So this, the top part, the green part's the ram, this red thing is the battering ram and it's attached to, by the way, a Raspberry PI pico.
- [67:08]
Steve Gibson
Yep. Stuck off on the side.
- [67:10]
Leo Laporte
Yeah.
- [67:11]
Steve Gibson
And if you look at the red thing down in the lower half, you, you can see on, on the edges of it are, I mean it's, it's made to be the profile of dram. So you, so yes. So you pull the real RAM out, you stick this extender in, and then you plug the original RAM into the top of the extender. So basically this gives the Raspberry PI pico access where ne, where needed to the dram.
- [67:44]
Leo Laporte
So basically most servers are a little tighter packed than this. I don't know if you could fit this.
- [67:49]
Steve Gibson
That's exactly the problem. That is exactly the problem. There's no way that that's even going to fit in an actual server, right? So the, the guys that developed this said with battering ram, we show that even the latest defenses on intel and AMD cloud processors can be bypassed. We built a simple $50 interposer, as they called it, that sits quietly in the memory path, behaving transparently during startup and passing all trust checks later. With just a flip of a software switch, our interposer turns malicious and silently redirects protected addresses to attacker controlled locations, allowing corruption or replay of encrypted memory. Battering RAM fully breaks cutting edge Intel SGX and AMD SEV SNP confidential computing processor security technologies designed to protect sensitive workloads from compromised hosts, malicious cloud providers or rogue employees. Our stealthy interposer bypasses both memory encryption and state of the art boot time defenses invisible to the operating system. It enables arbitrary plain text access to SGX protected memory and breaks SEV's attestation feature on fully patched systems. Ultimately, battering RAM exposes the limits of today's scalable memory encryption. Intel and AMD have acknowledged our findings, but defending against battering ram would require a fundamental redesign of memory encryption itself. Unlike commercial passive interposers, which are exceedingly expensive and commonly cost over $100,000, we developed a custom built interposer that uses simple analog switches to actively manipulate signals between the processor and memory and can be built for less than $50. So it's just a, you know, it's meant to be a proof of concept device, but it does thoroughly prove the concept and this demonstrates why Apple has been so ruthlessly rigorous with the physical security of the servers in their icloud data centers. Remember that they like were x raying them and taking high resolution photographs. I mean really protecting the, the physical, the physical manufacturer of their devices, anything that they allow into the, the icloud data center because they recognize that like this is one line of attack, they fully realize that physical access to a server basically means that all bets are off anyway. So you know, the device, as you said, leo, is not practical to use since the DRAM is elevated about an inch and a half away from its original socket where it would likely not fit within, you know, any kind of a standard closed server chassis. Generally those have a bunch of RAM in a row, then they have a hood covering it and then forced air through the ram. So there's just no way you could even close the lid on the server or slide it back into the rack. So but the point was to create a proof of concept device rather than a Cracking attack platform.
- [71:29]
Leo Laporte
Yeah, yeah, you can make it smaller.
- [71:31]
Steve Gibson
Yeah, right. I wanted to mention that the HackerOne bug bounty platform paid $81 million to security researchers over the past year. The company received almost 85,000. Think about that. 85,000 valid bug reports and paid out an average of a thousand dollars and a thousand and ninety dollars per award. Some obviously much more than that because 85. I'm sure that there were, you know, many lower value payouts, but a total of $81 million paid to researchers. And also the. The report said that vulnerabilities in AI products were a rising category this year, with more than 2.1 million paid to researchers. Most of those reports were for the discovery of new prompt injection attacks. You know, where you sweet talk the AI into doing something that it's not. Not supposed to do technically. Oh, and I can't wait to talk about this next piece of news, which we will get to Leo after our next break.
- [72:44]
Leo Laporte
Oh, well, if you can't wait to.
- [72:45]
Steve Gibson
Talk because imager links are now broken.
- [72:49]
Leo Laporte
Oh, I saw that. Yeah, what a. I know that is. We'll get to that in a second. Continuing on with security now, but first, a word from our sponsor for this section of security now, the great folks at HOX Hunt. H O X H U N T H if you're a security leader, you get paid to protect your company against cyber attacks, right? But that's getting harder, isn't it, with more cyber attacks than ever. And the phishing emails are just getting better generated with AI. Turns out legacy one size fits all awareness programs don't really stand a chance. They send at most 4 generic trainings a year and most employees ignore them. And when somebody actually clicks, they're forced into embarrassing training programs that feel more like punishment. That's why more and more organizations are trying hoxhunt. Hoxhunt goes beyond security awareness and changes behaviors by rewarding good clicks and coaching away the bad. It's actually fun. I know this sounds hard to believe, but really, whenever an employee suspects an email might be a scam, HOX Hunt will tell them instantly. You know, you get a big border and everything, providing a dopamine rush that gets your people to click, learn and protect your company. They've gamified it as an admin. Hawkshunt makes it very easy for you to automatically deliver phishing simulations across slack email teams. You can use AI to mimic the latest real world attacks, just like the bad guys are doing. And the simulations are are actually personalized to each employee based on department on location and more. So these are really effective phishings, you know, fake phishing mails, while instant micro trainings solidify understanding and drive lasting, safe behaviors. They're quick, they're fast, they're fun. You can trigger gamified security awareness training that awards employees with stars and badges. Now, I know this sounds silly, but it's actually great. We all want the little gold star, right? This boosts completion rates, it ensures compliance. It's not a punishment anymore. It's fun. Choose from a huge library of customizable training packages. You can even generate your own with AI. Hawkshunt has everything you need to run effective security training in one platform, meaning it's easy to measurably reduce your human cyber risk at scale. But you don't have to take my word for it. Over 3,000 user reviews on G2 make Hox Hunt the top rated security training platform for the enterprise. They got easiest to use and best results. It's also recognized as customers choice by Gartner and thousands of companies like Qualcomm, AES and Nokia use it to train millions of employees all over the globe. Visit hoxhunt.com securitynow today to learn why modern secure companies are making the switch to Hox Hunt. That's hoxhunt.com securitynow h o x H U n T It's like a fox hunt with an H. Hoxhunt.com security now. You know, once it's fun, once it's something you enjoy doing, so much more effective you. We all know that that's the best way to learn. Hawkshunts.com Security Now Steve okay, so the.
- [76:16]
Steve Gibson
Extremely popular online image hosting site Imgur Imgur felt the need to remove its service from the uk. The first I heard of this was when the people I interact with in the UK testing the DNS benchmark reported that they were unable to use their preferred image posting and hosting site. Imgur.com Imgur has posted a page titled Imgur Access in the United Kingdom which says from September 30, 2025, access to Imgur from the United Kingdom is no longer available. UK users will not be able to log in, view content or upload images. Imgur Content Embedded Again, here's a real issue. Imgur content embedded on third party sites will not display for UK users. Wow. What we've been anticipating is happening. This is what that looks like. So here's what the BBC's reporting explained under their headline Imgur blocks access to UK users after regulator warned of fine they wrote. Image hosting platform Imgur has blocked people in the UK from accessing its content. Imgur is used by millions to make and share images such as memes across the web, particularly on Reddit and in online forums. And yeah, like GRC's news groups which are deliberately text only, so our anyone who wants to post something typically uploads it to an image hosting site, they wrote. But UK users trying to access Imgur on Tuesday as last Tuesday were met with an error message saying content not available in your region with Imgur Content shared on other websites also no longer showing the UK's watchdog, the Information Commissioner's Office. The ICO said it recently notified the platform's parent company, Media Lab AI, of plans to find Imgur after probing its approach to age checks and use of children's personal data. A help article on Imgur's US website seen by the BBC states that, quote, from September 30, 2025, access to Imgur from the United Kingdom is no longer available. UK users will not be able to log in, view content or upload images. Imgur content embedded on third party sites will not display for UK users, the ICO wrote. The BBC launched its investigation into Imgur in March, saying it would probe whether the companies were complying with both the UK's data protection laws and and the children's code. These require platforms to take steps to protect children using online services in the uk, including minimizing the amount of the data they collect from them. A document published by the ICO alongside the launch of its investigation stated that Imgur did not ask visitors to declare their age when setting up an account. It said on Tuesday it had reached initial findings in its investigation and on 10th of September issued Media Lab with a notice of intent to impose a fine. Tim Capel, an interim executive director at the ico, said, quote, our findings are provisional and the ICO will carefully consider any representations from Media Lab before taking a final decision whether to issue a monetary penalty. We've been clear that exiting the UK does not allow an organization to avoid responsibility for any prior infringement of data protection law and our investigation remains ongoing. So yikes, that's a little chilling, seems rather harsh, but I suppose that retroactive responsibility is an it is a necessary thing to impose, otherwise the law will just be ignored until notice is given, the BBC wrote. The Watchdog would not elaborate on what its findings were nor the details of the potential fine when asked by the BBC. Tim Capel said this update has been provided to give clarity on our investigation and we will not be providing any further detail at this time. Unquote. Some Imgur users and reports speculated as to whether Imgur moved to block UK users from its services rather than comply with child safety duties recently imposed on some platforms under the Online Safety Act. Among these are requirements for sites allowing pornography or content promoting suicide and self harm to use technology to check whether visitors are over 18. But both the ICO and Ofcom, the media regulator enforcing the Online Safety act, said Imgur suspending access for UK users had been its own commercial decision. An OFCON Ofcom spokesperson told the BBC, quote, imgur's decision to restrict access in the UK is a commercial decision taken by the company and not a result of any action taken by Ofcom. Other services run by Media Lab remain available in the uk, such as Kik messenger, which has implemented age assurance to comply with the Online Safety Act. So it feels as though we're going to be passing through a period of turmoil and confusion until the technology has the chance to catch up to the legislation, which is, as we know, barreling along without much apparent concern for the feasibility of implementing the controls that it is mandating. And I should note that Imgur is not alone. Last Friday, March 3, ICO, that's the UK's regulator, posted under their headline Investigations announced into how social media and video sharing platforms use children's personal information, they wrote, we're today announcing three investigations looking into how Tick Tock, Reddit and Imgur protect the privacy of their child users in the uk. Our investigation into Tick Tock is considering how the platform uses personal information of 13 to 17 year olds in the UK to make recommendations to them and deliver suggested content to their feeds. This is in light of growing concerns about social media and video sharing platforms using data generated by children's online activity in their recommender systems, which could lead to young people being served inappropriate or harmful content. Our investigations into Imgur and Reddit are considering how the platforms use UK children's personal information and their use of age assurance measures. Age assurance plays an important role in keeping children and their personal information safe online. There are tools or approaches that can help estimate or verify a child's age, which then allows services to be tailored to their needs or access to be restricted. The investigations are part of our efforts to ensure companies are designing digital services that protect children. At this stage, we are investigating whether there have been any infringements of data protection legislation. If we find there is sufficient evidence that any of these companies have broken the law, we will put this to them and obtain their representations before reaching a final conclusion. It should be abundantly clear by now that regardless of how anyone feels about it, and no one, you know objectively wants this, the accurate determination of the age of anyone using a social media or content sharing service will be part of the cost of doing business going forward in the future. It may only be in the UK And a few states in the U. S today, but the entire European Union doesn't feel far off and many other US States have their own legislation working its way through their internal legislatures. And this feels like something which will accelerate as more and more regions are seen to be successfully adopting these new laws.
- [85:28]
Leo Laporte
And it will be incumbent on every single site and app and everything. The problem is, you know, we have a mastodon. I don't know how I'm supposed to do this. I don't. We're going to have to shut down our, all of our forums and mastodon.
- [85:44]
Steve Gibson
And just like these accursed cookie pop ups, it's like, what a mess. Every site you go to. Yes, I'm fine. Use cookies, use cookies, use cookies, Use cookies.
- [85:58]
Leo Laporte
By the way, podcasts have no way of doing this. This is an RSS feed. We literally have no way of knowing anything about you, you except your IP address when you come to download it. How are we supposed to do that? Can we, are we going to be required to do that?
- [86:14]
Steve Gibson
How are we supposed to do. That's really interesting, Leo.
- [86:18]
Leo Laporte
Well, if in five years you don't have any social networks, you don't have any podcasts, you don't have any websites, you don't have any games, you can.
- [86:26]
Steve Gibson
Blame the people you elected.
- [86:28]
Leo Laporte
Yeah, you could thank the governments because that's what they're heading towards. It's just not, it's not viable, it's not feasible. I mean, it's going to affect me directly. You know, Facebook can do this, Google can do this. The incumbents, the big guys can do this. It only affects the little people. That's who it affects. The small independent sites and podcasts.
- [86:50]
Steve Gibson
Well, and wait till you hear what happened with Discord. But first, in other late breaking news regarding the embattled EU chat control legislation, the Dutch government of the Netherlands has stated that it plans to vote no on chat control when that measure comes up for a vote next Tuesday. Minister van Oosten's letter to Parliament states that the Netherlands cannot support the proposal in its present form, citing privacy concerns, encryption risks and proportionality issues. The Ministry emphasizes that that combating child sexual abuse remains vital, but insists on, quote, legally sound Effective and privacy respecting, unquote measures. Okay. To which I say these politicians want the impossible, which is why this is a supremely difficult problem. On the one hand, they say that they want a privacy preserving solution, but if the goal is to combat the sharing of illegal content and the only way it's possible to know whether content is illegal is for someone or something to look at it, then that by definition requires that everyone's privacy be compromised. You literally can't have it both ways. And as has been pointed out, breaching everyone's privacy is a direct contravention of the EU's existing and well established privacy protections. EU wide. Meanwhile, as last reported that Germany was planning to vote no. It has since been reporting that they are apparently succumbing to pressure and I don't know from where, and maybe voting in favor next Tuesday because they have.
- [88:52]
Leo Laporte
The most members of the European Parliament. So this is a big block.
- [88:56]
Steve Gibson
Because it does, it does, as I noted before, is about the size of their population.
- [89:04]
Leo Laporte
Yeah. This is the swing state for this whole thing.
- [89:07]
Steve Gibson
Wow. Wow. And Germany, you'd think they would like.
- [89:13]
Leo Laporte
No, they're big on privacy.
- [89:15]
Steve Gibson
Right.
- [89:15]
Leo Laporte
More than any country I know. By the way, this is a proposal from Denmark.
- [89:20]
Steve Gibson
Yes.
- [89:21]
Leo Laporte
Which is interesting. I, yes.
- [89:25]
Steve Gibson
Because Denmark, you know how, how the, the presidency of the EU rotates around and I don't remember who it was last, but they was, I mean, this thing's a hot potato. And it landed in Denmark's laugh lap and they decided, okay, okay, we're gonna do it. Let's have a vote now and see, you know, do the right thing. No, it, it is a, it is a mess. You know, all of the independent messaging platforms have said, all of them, that they would leave any jurisdiction that compels them to break their promises of absolute privacy. And iOS and Android both have their own native securely encrypted messaging platforms. What are they going to do? Apple tried to offer a solution and everyone said, e, we don't want any of that in our phone.
- [90:17]
Leo Laporte
It's actually a solution very similar to what's being proposed with chat control. Yes, it's that, it's that hash. That NCMEC hash.
- [90:25]
Steve Gibson
Yes, yeah. Yes. And, and they, the, and then there is a graph in the, in the, in the proposed legislation, a graphic where. And, and we've talked about this early on where if something is questionable, then the device contacts a central clearinghouse and, and you know, submits an image that may be against the law and you know, waits for a decision. So I mean, it's it is a real. Again, you can't have it both ways. They're saying we don't want anyone to be able to to to send transmit illegal content. If that's true, you must look at everyone's content. Something has to look at it to determine if it's legal or not.
- [91:18]
Leo Laporte
I feel sorry for whoever has to listen to all of our podcasts and then say, you know what? There's nothing at all in any of this.
- [91:29]
Steve Gibson
Yeah, who, who would even like bother with this? Okay, so reading about a breach that Discord just revealed, one of the factoids there caught my eye as usual. Hackers made off with sensitive user data. The breach occurred at a third party company that handles Discord's customer support. The stolen data includes names, email addresses, payment details, and customer support tickets. But guess what? The breached and stolen data also contained the scanned images of government issued IDs.
- [92:11]
Leo Laporte
Oh, that.
- [92:13]
Steve Gibson
That. Discord had been compelled to collect for age verification.
- [92:18]
Leo Laporte
Oh my goodness.
- [92:20]
Steve Gibson
So there it is. We don't yet have the infrastructure in place for securely allowing for the assertion of users ages online. So we've dropped to the lowest common denominator, which is to present some form of our most private information. I certainly don't want criminals to have front and back scans of my driver's license or other similarly clearly identifying document. And while I'm sure that the third party that was breached is not a criminal organization, they've just demonstrated that they are unable to protect our private data from disclosure. So the question we should ask is why they had retained that identifying information at all. Right. Once an age verification has been made, that data that's required to do the scan and, and to be examined should have been erased. But people like to collect data. It's like, oh, data is good. We got big hard drives, let's fill them up. And we have no way to force its deletion after it's served its purpose. Right. It's out of our control. As, as is often noted, anything that gets loose on the Internet, you never, you know, it's like it's gone. The Internet has it now. So the only way to prevent the inadvertent disclosure of our personally identifying data is to never provide it in the first place. Which is why we need technology that we do not yet have. But you know, you, if you need, if you want to go use Discord and you have to prove for some reason that you are of age, you're over 18, you have to, right, hold your driver's license up to the camera I don't know.
- [94:16]
Leo Laporte
I don't think I've ever had to do that. Of course, we have a very active Discord club. Twit members. Have you been asked for your ID to use Discord? I wonder where that happens. Maybe it's not in the US There.
- [94:29]
Steve Gibson
Must, it must be some, some adult content.
- [94:33]
Leo Laporte
Oh, maybe it's an adult site. Yeah, yeah. That Discord has none of my information. They don't.
- [94:39]
Steve Gibson
Right.
- [94:39]
Leo Laporte
You know, just my login. Huh.
- [94:42]
Steve Gibson
Wow.
- [94:43]
Leo Laporte
Yeah. The. Our club is saying no, we've never had to do that. So I don't know where you would. Where they did that.
- [94:48]
Steve Gibson
Yeah, well, I'm. And all of your content is, is pg, right? Yeah.
- [94:52]
Leo Laporte
We don't even allow swearing.
- [94:54]
Steve Gibson
Right. And you got John in there to. Yeah. To just stomp on anybody.
- [95:00]
Leo Laporte
Yeah. He just yells every time somebody says a bad word. So I, I, I don't have to think about it. Hey, I'm sorry, John.
- [95:10]
Steve Gibson
Okay, so Salesforce, God, that this was really bad. I hope they've really, really learned some lessons here. They Lord knows they've got all the technology they could ever ask for, so this had to hurt them. Last Thursday, they explained that the new extortion attempts their customers have been receiving are not the result of another hack. Their headline was, quote, security advisory, Ongoing response to social engineering threats. And you gotta love the language here. This is what they posted. We are aware of recent extortion attempts by threat actors which we have investigated in partnership with external experts and authorities. Our findings indicate these attempts relate to past or unsubstantiated incidents and we remain engaged with affected customers to provide support. At this time, there's no indication that the Salesforce platform has been compromised, nor is this activity related to any known vulnerability in our technology. We understand how concerning these situations can be. Protecting customer environments and data remains our top priority and our security teams are fully engaged to provide guidance and support. As we continue to monitor the situation. We encourage customers to remain vigilant against phishing and social engineering attempts, which remain common tactics for threat actors. Brought to you by the Salesforce public relations department, I'm sure.
- [96:53]
Leo Laporte
Notice they don't actually say anything like.
- [96:58]
Steve Gibson
No, that said absolutely nothing. It was beautifully crafted.
- [97:03]
Leo Laporte
They don't say it didn't happen. No, no.
- [97:08]
Steve Gibson
I tracked down the posting that the group calling themselves Scattered Lapsus Hunters, which we know is a concatenation of three different groups posted over in breach forums. Leo, it's here at the bottom of or in the middle of pay. Oh, conveniently, page 13. Lucky 13. This is posted over in Breach forums. I was unable to determine its posting date. What the posting does make very clear is the sales force deadline, which is 10102025 this coming Friday. The breached forums posting cites 989.45 million and they say approximately 1 billion records. So they're saying they have around a billion records which I don't know how that you could possibly have a billion records, but that's what this thing says and it says to. To negotiate this ransom. All your. Yeah, you're right. Misspelled negotiate this ransom or all your customers data will be leaked. If we come to a resolution, all individual extortions against your customers will be withdrawn from. Nobody else will have to pay us. If you pay Salesforce Inc. In case. If Salesforce does not engage with us to resolve this, we will completely target each and every individual customers of theirs listed below. Failure to comply will result in massive consequences. If you are listed below, we advise you to take every action to protect yourselves and reach out to us to resolve this. Do not be mistaken that your SAS provider will protect all of you. They won't. Don't be the next headline. Make the correct decision and reach out. And then there's just. It has a line Salesforce Inc. Deadline 10102025 Status negotiation required so we may have another bit of news to report next Tuesday after the shoe has dropped on this one.
- [99:45]
Leo Laporte
Wow.
- [99:46]
Steve Gibson
Because I don't. As far as I know, Salesforce is not capitulating and the bad guys have demonstrated that they did launch a very effective massive phishing attempt. You using that was effective against some of Salesforce's customers using persistent OAuth tokens which unfortunately allowed people to to get in through Salesforce accounts that were logged in through automation and then pivot. So boy, what a mess.
- [100:19]
Leo Laporte
Wow.
- [100:22]
Steve Gibson
Signals sparse post quantum ratchet. Known as spqr. The Signal messenger system has just been further enhanced. It'll be a rolling upgrade that at no point will obsolete any existing clients. They've come up with a way of just sort of incrementally releasing it. And. And when you have two clients that both support the new sparse post quantum ratchet, then they will use it. As we covered previously, Signal already incorporated post quantum encryption protection and they did it the right way. They. They have both pre and post quantum encryption and they're using both. So if there's a problem with either, the other one will still provide protection. But these guys are seriously never satisfied. We also previously covered the operation of their double ratchet technology, so they have added another ratchet to create a triple ratchet and this one, this third ratchet in the trio is quantum computing safe. Now the details are interesting and plenty so I am thinking that it might be time for a deep dive next week into the operation of Signals new triple ratchet. The third one as I said being quantum safe. We'll see what the news is and if I've I'm I'm thinking that it would be fun to talk about how that works. We have, we have previously covered all of Signals operation in detail and I know that those were some popular podcasts, so probably fun to talk about how that's working. I got a piece of very nice email from a Goran Jordanoff who said hello Steve, I'm a longtime fan of the podcast and recently decided to try Spinrite and try to revive some old drives from a TrueNAS system. Spinrite did a phenomenal job of repairing a few hard drives, speeding up some SSDs and detected a bad out of the box inland NVMe. A bootable spin right on a USB stick will now be part of my must carry collection of USBs. Thank you and Garon, thank you for sharing your success with spin Right Steve Penfold said, I've just spotted the supposed release date on Amazon here in the UK for book two in Peter F. Hamilton's latest two book Exodus series. And seeing that name Leo Exodus is what I'm doing.
- [103:22]
Leo Laporte
I didn't finish it. I tried. I got blocked.
- [103:25]
Steve Gibson
I understand. So Steve said, I thought that that you, Leo and the Security now audience might like to know how long we all have left to wait. He said, I assume that the release date will be fairly consistent across countries. Regards Steve Penfold and I actually remember that I think the uk, you know, Peter's own locale gets them a little bit before Amazon does. I kind of think I remember that before. Anyway, the title will be Exodus the Helium C. Okay with a Release date of June 16, 2026.
- [104:04]
Leo Laporte
Oh well, I got plenty of time.
- [104:07]
Steve Gibson
Yes, you have. Yeah, yeah, nine months. He so I was actually I happened to be working on the DNS benchmark code when Steve's email arrived and my EM client popped up a notification of email from a Security now listener. So I quickly thanked Steve for his note and to that he replied, I thought you might like that. I'm holding out before reading the first book until they're both available. Okay, well first of all, amen to that. I now regret that I already read.
- [104:43]
Leo Laporte
The first half because you got to reread it.
- [104:45]
Steve Gibson
Oh Leo. The plot was so convoluted with like behind the scenes machinations and subtle long range manipulations. I mean, it's all about a weird hierarchy of post human creatures and pulling the strings on little puppet people that they, that they're, that they're sending messages to over long distances and long periods of time. You know, you really need to be taking notes along the way. But I didn't know that when I started and since I pretty much forgotten everything I knew about who, what, where, when and why of this, of this plot, you know, and frankly, I didn't feel that the book was really that good, you know, like, you know, I'm sorry to report that this, you know, this much beloved author's work seems to be on a steady decline. I loved Fallen Dragon. I loved Pandora's Star and Judas Unchained. I mean, those were just works of art.
- [105:54]
Leo Laporte
What was the one with Al Capone? I wasn't that crazy about that one.
- [105:58]
Steve Gibson
That was the Reality Dysfunction Knights dawn trilogy. Oh, yeah, and I agree it was a little fantastical from my, you know, when you got Al Capone coming back to life, it's like, what, What? Yeah, I mean, literally, I, you know, the, the Greg Mandel series. Those were where.
- [106:16]
Leo Laporte
Those were great.
- [106:16]
Steve Gibson
Yeah, yeah, those were really fun, you know, but I don't know, Peter's later works and then the whole dreaming thing, the.
- [106:24]
Leo Laporte
The dream, I didn't like that. Yeah.
- [106:26]
Steve Gibson
Stuff, you know, it's like.
- [106:27]
Leo Laporte
Yeah.
- [106:28]
Steve Gibson
Anyway, I'm not even sure that I had the energy to reread the first Exodus book again once the story's conclusion is available. You know, I suppose I will probably, maybe, you know, Jammer B can just tell us what happened.
- [106:43]
Leo Laporte
He loves it. He says he's read it twice already. He can't wait to read it, reread it a third time. Wow, he really loves it. I'm gonna give it a chance when the new. But I'm gonna wait till the second volume comes out and then I'll read them both together.
- [106:56]
Steve Gibson
Yeah. Well, we're at an hour and a half. Time for yes. Time for our Almost to the almost. Our penultimate break.
- [107:07]
Leo Laporte
Our penultimate break.
- [107:09]
Steve Gibson
Our penultimate break. We're going to do a little more listener feedback and then we'll spend some time looking at what Google has decided to do.
- [107:16]
Leo Laporte
All right, well, this penultimate break is the ultimate in keeping your passwords safe. This episode of Security now is brought to you by Bitwarden. Love Bitwarden, the trusted leader in password passkey and secrets management. Bitwarden is consistently ranked number one in user satisfaction by G2 and and software reviews. More than 10 million users across 180 countries. Over 50,000 businesses. It's the first thing I installed. I just set up a brand new desktop computer and of course the first thing you install, after you install the browser is Bit Warden, because that's how you get into everything else. And everything is in Bit Warden. My SSH keys. I love this new feature they've added where you can generate and scroll down, store both your public and private keys securely, which makes it easy to log into SSH and so forth. I mean there's just, they, they. The thing that's great about Bitwarden, and I think it's because it's open source, is they're always, it's always getting better. They're always adding new features. For instance, they now have an MCP server. This is, this is brand new. So it's available on the Bitwarden GitHub. It's not yet. You can install it through Bitwarden. You have to go to their GitHub. But, but what does it do? It lets you securely integrate your AI agents with your credential workflows. Because if you think about it, in fact, just the other day I was working with Claude and they wanted to know my password and I thought, do I want to send my password up to the cloud? No. But with this MCP server, Bit Warden can handle the credential workflow without revealing anything about you or your credentials. Now they are planning this as a regular distribution. They're going to have better documentation and so forth. But if you want to see it early on, go to their Bitwarden GitHub. This is a secure way, a standardized way for AI agents to communicate with Bitwarden users. You benefit because this is a local first architecture for security that the Bitwarden MCP server is running on your local machine. So all the client interactions happen within the local environment, which minimizes exposure to external threats. It integrates with the Bitwarden command line interface. Another reason I love Bitwarden, I love the cli. And users can also opt for self hosted deployments for greater control over system configuration and data residency. That's one thing I haven't done yet. I really trust Bitwarden with my vault, but if you want to run it locally, you can. In fact, because it's open source, there are a number of third party, very good third party vault servers for Bit Warden. It's just, it's an ecosystem. In fact, if, if I want to If I'm talking to somebody, I want to know, are they real? Are they the real deal? Are they really geeks? I ask them a couple of questions. What browser they use and what password manager they use. If they say Bitwarden, I know they know what they're talking about. MCP servers. Let's get back to that. I'm sorry, I got distracted. Mcp, of course, is the open protocol for AI assistance. These servers let AI systems interact with commonly used applications that could be a content repository like GitHub, business platforms like Salesforce, developer environments. And they do it through a consistent open interface. That's why we like mcp. Driving secure integration with agentic AI. The Bitwarden MCP server represents a foundational step towards secure agentic AI adoption. The Infotech Research Groups streamline your security and protect your organization report. You can still get this. It highlights how enterprises in the Forbes Global 2000 are turning to Bitwarden to secure identity and access at scale. The report emphasizes growing security complexity. You're living that. We are all living that right now. Globally distributed teams, fragmented infrastructure, credentials dispersed across teams, contractors and devices. Enterprises need to address credential management gaps and strengthen their security posture. They do it by investing in scalable enterprise grade solutions like yes, Bitwarden. Bitwarden setup is easy. It supports importing for most password management solutions. So if you're tired of that stale old system you've been using, it's easy to move to Bitwarden. And of course, Bitwarden is open source. That's huge. It means that you can inspect the source code, make sure it's doing what it says it'll do. They get regular third party audits. They publish the full reports from those audits. And Bitwarden meets SoC2 type 2 GDPR HIPAA CCPA compliance. It's ISO 270012002 certified. You know all the highest standards of security. Get started today with Bitwarden's free trial of a teams or enterprise plan or get started for free across all devices as an individual user@bitwarden.com twit this is the way bitwarden.com twit we thank him so much for doing a great job with a great product and of course for supporting Steve and security. Now we know the very first thing you gotta do is use a password manager. Passkeys too, by the way, and Yuba keys and all the other stuff. All right, Steve, on we go.
- [112:27]
Steve Gibson
So Mike Lendvay wrote, hi Steve, in the past few episodes, you've mentioned that your iPhone 12 does not support Liquid Glass. However, nothing online from Apple or anywhere else indicates that a subset of iPhones that support iOS26 don't support the new design. Is it possible that you have accessibility settings enabled that tone down the new visual effects such as reduce transparency or reduce motion? And then he gives me the menu locations in those. He says this is a small and perhaps unimportant clarification, but it's been bugging me since I can't confirm this piece of information anywhere else. Much thanks to you and Leo for the show. I look forward to it every Tuesday. Mike, thank you for challenging me that on that and I can confirm that you are 100% correct. After reading Mike's note, I checked the settings on my older iPhone 12 and sure enough, I had previously disabled all of the previous nonsense. So when I upgraded that phone to iOS 26, Apple continued to honor those settings. So all I saw was relatively minor changes to the UI. Curious to see what iOS26 looks like for everyone else, I flipped those switches back to their normal defaults and wow. And not in a good way. My most honest impression is that this is a demonstration of Apple having run out of anything useful to do. The phone has become cartoony. You know how Leo like when the Wile E. Coyote is about to take off chasing the Roadrunner in in true cartoon fashion, Wiley will first pull back a little bit, as if to kind of compress some imaginary invisible spring to help him launch out after the Roadrunner.
- [114:32]
Leo Laporte
Oh, now I'm never going to be able to unsee that.
- [114:35]
Steve Gibson
No. And when also when, when something like lands, it like goes a little too, too far and then comes back like it's bouncing off sort of like an invisible barrier when unrestrained iOS 26's various elements give little extra hops and giggles and splurts just like that. Because apparently it's not actually the content in the phone that we want to focus on. We want to have our attention called to admire Apple's amazing animated user interface. Long ago, it was observed that the best user interfaces were those that went unnoticed and which did not call attention to themselves. The example of this that I've always loved most was the telephone handset. When you're using it, you don't think in terms of speaking into a mouthpiece and a microphone. No, your attention extends past the phone, all the way to the person to whom you're speaking. At the other end, the phone disappears, as it should. But here we have Apple's new user interface Jumping up and down like a spoiled infant going out of its way to constantly call attention to itself and to make everything about it. It's really over the top. But the good news is, turns out it's possible to tone that way, way down. So the only thing you see is some improved visibility enhancements. And those I very much like. You know, like, things are a little, they're like outlined with a thin, you know, rule line around them. And, you know, so they're kind of nice. I mean, there's still a little bit of jump and wiggle, but okay, at least it's not what it was. And boy, I mean, I really, I found myself trying to look through some drop of water as, as something that was blurry behind it. It's like, what is that? What, what, what? You know, obviously you're not supposed to wonder, but you know, again, it's like, wow, Apple just seems dumb to me. You know, at least we don't have, you know, wood grain any longer. We got tired of that so we went to.
- [116:55]
Leo Laporte
Yeah, we kind of went the other direction. Yeah. Yeah, we're in the future now.
- [117:00]
Steve Gibson
Wow. Eric Perry said. Hi Steve, I really enjoyed your show 1045. So that was last week, he said. I've been listening since my career change about five years ago. I'm an admin of a Microsoft 365 tenant and your read of the passkey authentication from Microsoft accounts felt all too familiar. I wanted to share some additional knowledge that I found is unique with Microsoft over other passkey accounts I've worked with. He said. There are several issues I've run into with Microsoft passkey configuration. If you attempt to use Pass keys with LastPass, the setup fails when registering with a Microsoft account. I don't know if the same goes for bit warden or not. I personally use a Yubikey registered as a passkey and the experience is great. Although we have users testing the Microsoft authenticator method and it's exactly as that listener described. It's clunky, far too many steps and defeats the whole point of making login easier and more secure. If Microsoft fixed the Last pass or any third party storage of pass keys, this would have really greatly improved adoption in my opinion. Especially if the password managers are managed and compliant with company policies. Love the show. I look forward to it every week. Thanks, Eric. Okay, so that's really interesting. As Leo, you noted last week, your experience with passkeys is entirely different because you're able to store your passkeys in Bitwarden that's able to perform all the required cryptographic operations on behalf of its user. So the entire process is smooth and seamless. But our listener Eric notes that Microsoft refuses to work with password managers, at least with LastPass. One of the things that we learned way back at the dawn of all this was that the Fido 2 specification for pass keys allows sites to determine the nature of the authenticator being used and can refuse to accept what they may feel is insufficiently secure. And that appears to be what's going on with Eric's observation at this time. Entra ID and Azure ID do not accept browser based pass keys authenticators. So this is a deliberate policy decision by Microsoft to force you to use Microsoft's authenticator, yeah, with its pass keys.
- [119:57]
Leo Laporte
Yeah, yeah.
- [120:01]
Steve Gibson
Yeah. Andrew Iyer in Perth, Western Australia raises a very interesting question. He said, hi Steve, I thought you and your listeners might find the following helpful My son has a PC which is only three years old running Windows 10. Windows 10 said that the PC did not meet the minimum hardware requirements. After a bit of digging, it appears that the reason was that he has TMP, but he meant TPM. TPM 2.0 could not be found. He said, and I love this. I used Chat GPT to find the Windows command to identify the motherboard. Then I asked Chat GPT if that motherboard did have a TPM 2.0, which it replied yes. After more chat gpting and frowning, to my relief, I was able to discover that a BIOS update would likely make TPM 2.0 appear to Windows. I asked Chat GPT how to upgrade the BIOS. Upgrading the BIOS on some gaming machines is not that simple, and it diligently provided all the steps for the motherboard in question. The PC then qualified for a Windows 11 upgrade and was upgraded successfully. This begs the question, how many PCs around the world are perfectly good and will end up as e waste and will never be upgraded to Windows 11 simply because of an older BIOS or an incorrect BIO setting? Chat GPT saved me hours, I thought. Other listeners may find this experience useful, and of course Andrew's observation is extremely useful. TPM provisioning can be through either a discrete TPM chip soldered onto the motherboard or via the motherboard's own firmware. Firmware TPM is a thing in the case that Andrew cited, his son's relatively new only 3 year old gaming PC was still using a using firmware based TPM. It was using a firmware based TPM and it was on 1.2 and since its initial release when the Motherboard's firmware was set. Newer firmware was released for that motherboard which Then included TPM 2.0. So this is a very important observation. Thank you Andrew. And to our listeners. If you've got systems where Windows is saying love to help you out here, move you to Windows 11, except you've got TPM 1.2, find out whether your Motherboard's TPM is hardware based or firmware based. And if it's in firmware, it might be that there is newer firmware for it updating that will bring you to 2.0 and then Windows 11 will happily or Microsoft will happily upgrade to Windows 11. So very, very cool. Thank you. Let's not something that we talked about and covered. Okay Leo, why don't we take our last break. That way we'll do we'll do the rest of this uninterrupted while we talk about Google's developer registration decree and what it means for yeah big I can't wait to talk to you pool of users.
- [123:51]
Leo Laporte
Yeah, I'm a little disappointed to be honest. But but I want to hear what you have to say about it. Our show this portion of security now brought to you by Veeam. When your data goes dark, Veeam turns the lights back on. Veeam keeps enterprise businesses running when digital disruptions like ransomware strike. Man, I could think of a few businesses who wish they were using Veeam. Don't you be in that group. How does Veeam do it? By giving businesses powerful data recovery options that ensure you have the right tool for any scenario. Broad, flexible workload coverage from clouds to containers and everything in between. Full visibility into the security readiness of every part of your data ecosystem and tested, documented and provable recovery plans that can be deployed with a click of a button. That's why Veeam is the number one global market leader in data resilience. Just call them the global leader in helping you stay calm under pressure. With Veeam, it's all good. Keep your business running@veeam.com that's V E E A M dot com. I told you about it. Now there's no excuses. I don't want to. I don't want to be talking about how you got hit by ransomware. You need data resilience. You need Veeam. Veeam.com thank thank you Veeam, for supporting Steve Gibson and security. Now thanks to Grayson too. Just gave us a super chat. $5. Thank you Grayson. He's a regular. Always in, always in our our chats Watching the show.
- [125:29]
Steve Gibson
Grayson Petal, right?
- [125:31]
Leo Laporte
Yeah, you know him? Yeah. Petty. Yes.
- [125:34]
Steve Gibson
Petty, yeah. Okay, so I encountered a posting over@f droid.org f-droid.org that I wanted to share because I thought it was so well conceived and heartfelt. It was written by a well known developer of a system called Skip Tools which enables the creation of native Swift UI apps for iOS and Android. Here's what Mark wrote. He said for the past 15 years, F Droid has provided a safe and secure haven't for Android users around the world to find and install free and open source apps. When contrasted with the commercial app stores of which the Google Play Store is the most prominent, the differences are stark. They are hotbeds of spyware and scams, blatantly promoting apps that prey on their users through attempts to monetize their attention and mine their intimate information through any means necessary, including trickery and dark patterns. F Droid is different. It distributes apps that have been validated to work for the user's interests rather than for the interests of the app's distributors. The way F Droid works is simple. When a developer creates an app and hosts the source code publicly somewhere, the F Droid team reviews it, inspecting it to ensure that it is completely open source and contains no undocumented anti features such as advertisements or trackers. Once it passes inspection, the F Droid build service compiles and packages the app to make it ready for distribution. The package is then signed either with F Droid's cryptographic key or, if the build is reproducible, enables distribution using the original developer's private key. In this way, users can trust that any app distributed through F Droid is the one that was built from the specified source code and has not been tampered with. I mean, this is all just beautiful and exactly done right, he said. Do you want a weather app that does not transmit your every movement to a shadowy data broker, or a scheduling assistant that doesn't siphon your intimate details into an advertising network? F Droid has your back. Just as sunlight is the best disinfectant against corruption, open source is the best defense against software acting against the interests of the user. The future of this elegant and proven system was put in jeopardy last month when Google unilaterally decreed that app that Android developers everywhere in the world are going to be required to register centrally with Google. In addition to demanding payment of a registration fee and agreement to their non negotiable and ever changing terms and conditions, Google will also require the uploading of personally identifying documents, including government id, by the authors of the software, as well as enumerating all the unique application identifiers for every app that is to be distributed by the registered developer. The F Droid Project cannot require that developers register their apps through Google, but at the same time we cannot take over the application identifiers for the open source apps we distribute, as that would effectively seize exclusive distribution rights to those applications. If it were to be put into effect, the Developer Registration Decree will end the F Droid Project and other free open source app distribution sources as we know them today, and the world will be deprived of the safety and security of the catalog of thousands of apps that can be trusted and verified by any and all F Droids. Myriad users will be left adrift with no means to install or even update their existing installed applications. How many F Droid users are there exactly? We don't know because we don't track users or have any registration. No user accounts by design while directly installing or sideloading software can be construed as carrying some inherent risk. It is a false to claim that centralized app stores are the only safe option for software distribution. It is false to claim that they're the only safe option for software distribution. Google Play itself has repeatedly hosted malware, proving that corporate gatekeeping doesn't guarantee user protection. By contrast, fdroid offers a trustworthy and transparent alternative approach to security. Every app is free and open source. The code can be audited by anyone. The build process and logs are public, and reproducible builds ensure that what is published matches the source code exactly.
- [131:18]
Leo Laporte
That's really important. They always do reproducible builds. That's huge.
- [131:22]
Steve Gibson
Yes, yes. This transparency and accountability provides a stronger basis for trust than closed platforms while still giving users freedom to choose. Restricting direct app installation not only undermines that choice, it also erodes the diversity and resilience of the open source ecosystem by consolidating control in the hands of a few corporate players. Furthermore, Google's framing that they need to mandate developer registration in order to defend against malware is disingenuous because they already have a remediation mechanism for malware they identify on a device. The Play Protect service that is enabled on all Android certified devices already scans and disables apps that they have that have been identified as malware regardless of their provenance. Any perceived risks associated with direct app installation can be mitigated through user education, open source transparency, and existing security measures without imposing exclusionary registration requirements. We do not believe that developer registration is motivated by security, we believe it is about consolidating power and tightening control over a formerly open ecosystem. If you own a computer, you should have the right to run whatever programs you want on it. This is just as true with the apps on your Android or iPhone mobile device as it is with the applications on your Linux, Mac and Windows desktop or server. Forcing software creators into a centralized registration scheme in order to publish and distribute their works is as egregious as forcing writers and artists to to register with a central authority in order to be able to distribute their creative works. It is an offense to the core principles of free speech and thought that are central to the workings of democratic societies around the world. By tying application identifiers to personal ID checks and fees, Google is building a choke point that restricts competition and limits user freedom. We must find a solution which preserves user rights, freedom of choice, and a healthy competitive ecosystem. So what do we propose? Regulatory and competition authorities should look very carefully at Google's proposed activities and ensure that policies designed to improve security are not abused. To consolidate monopoly control, we urge regulators to safeguard the ability of alternative app stores and open source projects to operate freely and to protect developers who cannot or will not comply with exclusionary registration schemes and demands for personal information. If you are a developer or user who values digital freedom, you can help write to your Member of Parliament, Congressperson or other representative, sign petitions in defense of side loading and software freedom, and contact the European Commission's Digital Markets act team to express why preserving open distribution matters. By making your voice heard, you help defend not only F droid but but the principle that software should remain a commons, accessible and free from unnecessary corporate gatekeeping. Wow. As with any high quality dispute where both sides are engaged in a good faith discussion, it's possible to empathize with each side of the argument. We absolutely know that malware is a problem on the Android platform. We also know that Google's Play Store is a sewer of shenanigans. We've covered many of them in the past on the podcast, so it's understandable for Google to wish to somehow get a handle on the mess that has evolved from their original good intentions. And I would bet that there are those inside Google who are no more happy with this decision than the author of this F droid piece. For one thing, Google is dramatically changing the game in what amounts to a bait and switch tactic. The requirement to completely de anonymize all Android developers is doubtless a big deal, but so much real damage is done through the abuse of the absolute freedom of anonymity that holding developers accountable for the actions of their code would likely go a long way toward cleaning up the mess that the Play Store has become. And then there's the requirement of a developer fee to register. I suppose I can understand Google feeling that they have a right to cover their registration costs, although Google doesn't need the money, but obtaining payment from someone creates another barrier to malicious registrations. It's also worth noting that Google's Play Store is currently home to over 2 million apps. Let me say that again. 2 million apps. I have no right to judge, but does anyone really believe that more than a tiny fraction of those 2 million apps could possibly be useful? One thing seems sure, which is that this move by Google will change the nature of the Play Store. And it sounds as though it may spell the end of F Droid unless they're able to work around the limitations. At one point Mark wrote, the F Droid project cannot require that developers register their apps through Google, but at the same time we cannot take over the application identifiers for the open source apps we distribute, as that would effectively seize exclusive distribution rights to those applications. To which I say, so what? I certainly get it that F Droid would not choose or wish to take over the application identifiers of the open source apps they distribute. But that may be the solution, assuming that Google allows them to do that. Given what Mark wrote, F Droid is already fully, deeply and thoroughly inspecting and vetting any app they distribute, and they're building them and signing them themselves already, so they should not have any trouble signing the result with their developer's id. And if F Droid became the sanctuary for all those legitimate Play Store developers who do not wish to reveal themselves to Google, then that could be good for F Droid too. Though the tsunami of developer submissions might be a lot to handle. I wanted to finish with a pair of posts I found over on Y Combinator. The first is in reply to Mark's F Droid post and then he replied to that. So the first says, I contacted the European Commission DMA team on this gross abuse of power. Google just followed Apple in this regard, who reacted to the DMA by coming out with this notarization for developers and this poster said, here is their flaky answer. Dear Citizen, thank you for contacting us and sharing your concerns regarding the impact of Google's plans to introduce a developer verification process on Android. We appreciate that you have chosen to contact us as we welcome feedback from interested parties. As you may be aware the Digital Markets Act, DMA obliges gatekeepers like Google to effectively allow the distribution of apps on their operating system through third party app stores or the web. At the same time, the DMA also permits Google to introduce strict, necessary and proportionate measures to ensure that third party software apps or app stores do not endanger the integrity of the hardware or operating system or to enable end users to effectively protect security. We have taken note of your concerns and while we cannot comment on ongoing dialogue with gatekeepers, these considerations will form part of our assessment going forward. Kind regards the DMA team and then they and then this guy finishes saying the DMA is in fact cementing their duopoly power the opposite of the objective of the law. And to this Mark replied post author here I've also been in various DMA enforcement workshops and consulted with EU regulators on the topic of app distribution. The strictly necessary and proportionate measures to not endanger the integrity of the hardware or operating system, unquote defense comes up time and time again and is clearly a primary talking point for those lobbying against effective enforcement. From a developer's perspective, this stipulation is obviously intended to ensure that that the existing on device protections, sandboxing, entitlement enforcement, signature checks, et cetera are not permitted to be circumvented by third party app stores. But the anti DMA brigades have twisted their interpretation to imply that gatekeepers are permitted to keep on gatekeeping. Apple still requires that all software be funneled through it's app review. They call it notarization but it is the exact same thing as review developer fees, terms and conditions, arbitrary review delays, blocking apps based on policy, etc. Before it is signed, encrypted and redistributed to third party marketplaces like Alt Store. And now Google is going to introduce its own new gatekeeping for all software on Android certified devices which covers 95% plus of all Android devices outside of China. The lack of alarm has been for me quite alarming. Every piece of software installed on billions of mobile devices around the world is going to be gatekept by two US companies headquartered 10 miles of away from each other and with increasingly authoritarian friendly leadership. If you have an Android device, install F Droid today and let it be known that you won't give up your right to free software without a fight. So I completely understand where Mark is coming from. But the scourge of Internet malware and Internet malconduct is changing the nature of computing. Windows developers now need to sign their code to have it Pass Windows defenders. Guilty until proven innocent Deletion. The author of Notepad discovered this when he attempted to push an unsigned update and it was a disaster. It did not go well. And code signing certificates do not come cheap. Fortunately, Microsoft no longer gives EV code signing certificates any extra benefit treatment. So my own next certificate will be much less expensive. But not free means that it's becoming much more difficult for freeware authors who just want to contribute to the community to do so. Unfortunately, to me, all. You know, to me, all of this change, which is taking us in the direction of having less freedom, feels inevitable. I feel as though the handwriting has been on the wall for some time. I believe that big tech is going to continue exerting its influence toward its own ends and that governments are going to inevitably regulate more and more of what can be done by us on the Internet. Are these actions by the powerful being taken in response to crime, or is crime just their excuse? No one will argue against protecting children, but whatever the reason, the outcome is the same. New gates are being erected and those. And with those gates come gatekeepers. The truth is the Internet remains an incredible place. It is an incredibly rich asset for anyone who wishes to plummet's depths. And we'll be back here next week to do some more plumbing and discuss what's going on.
- [144:51]
Leo Laporte
Oh, you're more than a plumber. Yeah. I've been really intrigued. Grayson uses a version of Android that I've been thinking of Putting on my Pixel 9 for some time called Graphene, which does let you. It's supposedly more secure. It's third party, it's open source. It does let you use the Google Play Store in a sandbox. They don't include it though. They don't put services on there and you can use F Droid on it. And I think this might be just the push I need to.
- [145:25]
Steve Gibson
It's got a great logo. Wow.
- [145:27]
Leo Laporte
Yeah, it's graphene. Get it? Of course you get it. Yeah, yeah. There are a number of third party ROMs like this. Of course, the response to this is, and I imagine Google will be doing it any day now, is locking down the bootloader so you can't modify the operating system. All in the, you know, security users benefit your security.
- [145:50]
Steve Gibson
Yeah, that's right. I wonder if they're going to do that. There was a huge concern that Microsoft was going to lock, you know, Windows systems so that you had no choice to install another OS that might be. We haven't seen that yet.
- [146:09]
Leo Laporte
They came close. I had to turn off Secure boot, of course, to put Linux on my new desktop.
- [146:14]
Steve Gibson
But they do let you turn offs. Yes.
- [146:17]
Leo Laporte
Yeah. Samsung has locked down in the past, has locked down its bootloader. Some manufacturers do. Google does. Not yet. I just, I don't know. I don't know. I think there's a. I think they're not too worried about it because it's such a techy, kind of geeky thing to do that.
- [146:36]
Steve Gibson
Yep.
- [146:37]
Leo Laporte
The mass number of users isn't going to do it, but boy, I think people need to really start looking at open source. I love Linux. I mean as, as Apple goes down the chute and Microsoft's really gone down the chute more and more. I like open source solutions. That's just.
- [146:55]
Steve Gibson
Well, it's going to be interesting too to see. I mean Google is going to do this. They've announced it, so it'll be interesting to see how it reshapes the Play Store. How many apps disappear, first of all, because they've been abandoned years ago and they're just sitting around. I mean, I imagine if they're, if they're not from a registered developer, Google will give it some time and then we'll just say, okay, we're, you know, we're, we're gonna delete this.
- [147:20]
Leo Laporte
Yeah, yeah. You know, they've backed down in the past. They could back down if they get enough pressure. This could just be a trial balloon. Let's hope it is.
- [147:32]
Steve Gibson
Well, anyway, I know for sure, Leo, that this podcast is not a trial balloon.
- [147:38]
Leo Laporte
No.
- [147:39]
Steve Gibson
Because I have the lack of hair to prove it.
- [147:42]
Leo Laporte
If it is, it's a very long. We're playing the long game. Very much so. 1046 episodes later, we're, we're doing our best here to figure it all out. You can listen to the show every Tuesday. We do it right after Mac Break weekly. We actually stream it live. If you want to get the freshest version, you don't need to, but if you want to, it's around about 1:30 Pacific, 4:30 Eastern, 20:30 UTC. We stream, of course, to the club in our club Twit Discord. And if you're not a member of the club, I would love you to join. That makes a big difference to us and our ability to keep doing what we're doing. Protecting and preserving your privacy. We don't know how old you are. We don't care. We don't know who you are. We don't care. We don't give advertisers your information. We have ads, but it's up to you, whether you want to participate and listen to them or not. If you don't, join the club, Twit TV Club Twit. If you're in the club, you can watch in the Discord, but everybody can watch on YouTube, Twitch TV, TikTok, X.com, facebook, LinkedIn and Kik. So seven other ways to watch us live after the fact Just download a copy of the show now A good place to go be Steve's site GRC.com There's a few reasons you might want to go there. One, to support Steve, because that's where his bread and butter Spinrite lives. The world's best mass storage maintenance, recovery and performance enhancing utility. You got to have it. If you got mass storage, you got to have it. Even works on things like Kindles. That's called spinrite. It's@grc.com if you go to grc.com securitynow you can get a copy of the show. There's some. Steve has entirely unique versions of it. He's got a 16 kilobit version for the bandwidth impaired. He's got a 64 kilobit version which is smaller than ours. So those are both audio. He has the transcripts written by the wonderful Elaine Ferris, a human being, not an AI, who actually writes down every word and does it thoughtfully and does a very good job. He's also got the show notes there. You can have Steve email you the show notes if you go to GRC.com email He that's a chance for you to whitelist your email address if you want to submit things to the show, like the picture of the week and that kind of thing. You can also check those boxes. They're unchecked by default, but if you check them below, one is of course for the show notes every week and one is for a very infrequent email. In fact, he's only sent out one in all the years he's been doing it. But there will be one soon. I have a feeling for the DNS benchmark Pro. I'm hoping we're counting on it. And you'll get. You'll get notified if you check that box as well. You never have to worry about Steve. He's a privacy advocate.
- [150:24]
Steve Gibson
Quite clearly, every piece of email contains an unsubscribe link, so.
- [150:29]
Leo Laporte
Nice.
- [150:29]
Steve Gibson
Yeah. Yep.
- [150:31]
Leo Laporte
Yeah. He does his own emailing, you know, running his own software. We've talked about it before. He's really, of course, very focused on protecting you and your privacy. He also has some great forums. Another way you can interact with other listeners in the show. At GRC.com we have copies of the show on our website, Twitter TV SN. We have 128 kilobit audio, which, I'll be honest, doesn't sound any better than 64 kilobit audio. But we do that because Apple transcodes it and we got to give them a higher bit rate. And there's a long story behind it. We also offer video, which Steve does not have. If you want to see the mustache at work, GRC. I'm sorry, TWiT TV SN. You can subscribe in your favorite podcast player. That's another way to get it automatically. Audio or video. That's free. And there's a YouTube channel, which I like for sharing little clips from the show. Great way to let people know, you know, if you hear something, you go, oh, my man, I gotta tell my friend this or my IT director or whatever. You can do that. Hey, thank you, Chad. Another super chat contribution. $10 pear character bowing down says thank you. Thank you, Chad. We appreciate all of the help we get from a great community. I know, Steve. You appreciate your community. It's really amazing what you've done.
- [151:49]
Steve Gibson
Yeah, the. The feedback is. I mean, it's.
- [151:52]
Leo Laporte
It's.
- [151:53]
Steve Gibson
It means everything.
- [151:54]
Leo Laporte
Yep. 20 years we've been at this. Let's. Let's go for another 20 more.
- [151:57]
Steve Gibson
I like it.
- [151:58]
Leo Laporte
Well, we'll only be in our 90s.
- [152:01]
Steve Gibson
Yeah, piece of cake.
- [152:03]
Leo Laporte
Nowadays, that's not nothing. Nothing. Thank you, Steve. Have a great week. We'll see you next week right here on Security Now.
- [152:10]
Steve Gibson
Right? Oh, Security Now.