← Security Now (Audio)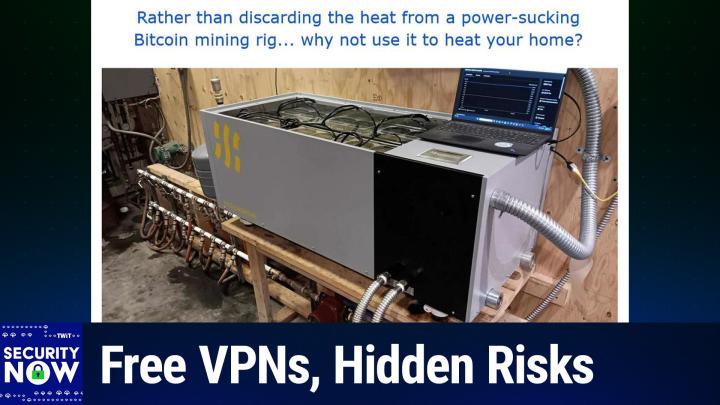
Loading summary
Transcript160 lines
- [00:00]
Leo Laporte
It's time for Security Now. Steve Gibson's here with our last episode of the year. We're going to talk about North Korea, the billions of dollars they've made hacking us. We'll talk about insecure Docker servers. Maybe why you want to think a little bit harder about before putting that Docker container up on the Internet. We'll also talk about let's encrypt free automated certs, the future of that. And then how a ping icon was used to infect 50,000 Firefox users. Security now is next.
- [00:34]
Steve Gibson
Podcasts you love from people you trust.
- [00:39]
Leo Laporte
This is twit. This is Security now with Steve Gibson. Episode 1057, recorded Tuesday, December 23, 2025. Ghost poster. It's time for Security now, the last show of 2025. Hello, everybody. I'm Leo Laporte Joining me now, the man in charge. The man, the myth, the legend.
- [01:06]
Steve Gibson
Wait a minute.
- [01:06]
Leo Laporte
Steve Gibson. You've got a Santa baseball cap on.
- [01:11]
Steve Gibson
Yes, I do.
- [01:12]
Leo Laporte
Oh, I thought we were celebrating St. Patrick's Day.
- [01:14]
Steve Gibson
I clearly have. Yeah. Well, you got the green. You need some green. And you have a nice tree shirt.
- [01:21]
Leo Laporte
This. Yeah.
- [01:22]
Steve Gibson
You look like a jungle now. That's good.
- [01:26]
Leo Laporte
This is the last show of the year, two days before Christmas, week before New Year's Eve. We will next week on December 30, air a very special Security Now. It'll be the Vitamin D episode we recorded way back 16 years ago in 2009. Hard to.
- [01:45]
Steve Gibson
Way back before anyone had heard of Vitamin D. Vitamin what? What? That's right.
- [01:50]
Leo Laporte
But, you know, in the intervening years, you've been proven spot on. So I think that it is kind of timely. We also, because it was back when we did audio only, Anthony Nielsen has created a marvelous geek yule log for the show. So you will want the video version of the show. The content is all audio, but while you're listening, you can relax by the digital fire. And it's got some Easter eggs. It's very, very cool. He did a really neat job with that, so. And I think he said it's got a periodicity of, I think, 30 minutes or more. I mean, it goes on for quite a while, so. Oh, yeah, you might want to put it on your big screen and just, you know, have it running all Christmas.
- [02:35]
Steve Gibson
Geek out. That's right.
- [02:37]
Leo Laporte
So, Steve, is there any security news this week?
- [02:40]
Steve Gibson
Yeah, we all mean. I mean, that's the advantage of this podcast. Leo, when you suggested it to me 21 years ago, I thought, what? Okay, we'll talk for A couple weeks and run out of stuff.
- [02:51]
Leo Laporte
But it's probably worse this time of year actually. Right.
- [02:54]
Steve Gibson
I don't really see much seasonality to it there. Does the bad guys do seem to take some time off too. So there is that. But today's topic is something called Ghost Poster, which was the name given to a a malicious extension for Firefox. What's interesting is that the malicious code is stored using steganography in a PNG icon. The extensions PNG icon. I forgot to follow up on this, but several times they mention that this is one of 16 or 17 extensions which are in the same family of bad and. And they kept saying and they're still available. It's like what's wrong with you people? Get it. Get Mozilla to take it down. Anyway, it's infected 50,000 Firefox users and it's not good. So that'll be our main topic for this episode 1057, this final episode on December 23rd of 2025. But bizarrely enough, some things aligned. I don't know why, but about cryptocurrency North Korea's profitable fix. We're going to talk about on of on cryptocurrency. Amazon uncovering a crypto mining agent sneaking into their customers clouds. Insecure Docker API servers which turn out to be a thing are also found to be hosting crypto miners. In addition, we have a new and truly massive smart TV based botnet discovery. I'm going to briefly mention that the DNS benchmark is now in its fourth release and I'm actually working on a fifth that's going to add some additional features and I'll talk a little bit about that then. Also some listener feedback drew me into a sort of a revisiting let's encrypt an automated certificates and that whole world. And then we got some additional listener feedback and we're going to talk about how this, this Ghost Poster infected PNG icon. So I think another great podcast for everybody as we wrap up 2025. I don't know what happened to the year, but it seems to be gone. And of course a great picture, Picture of the week would be the.
- [05:30]
Leo Laporte
Yep. Sometime you have to publish a book of all the pictures of the week or something like that. I think it'd be very popular.
- [05:36]
Steve Gibson
That would be fun.
- [05:37]
Leo Laporte
Yeah, coffee table.
- [05:38]
Steve Gibson
I mean I'm getting more people saying I don't like clicking. Can I, can you please wrap up these podcasts into annual archive sort of thing? So you know we can do that. There's that I'll talk to.
- [05:52]
Leo Laporte
I'll talk to our editors if you want.
- [05:53]
Steve Gibson
It would be a big hit. People are saying, you know, I want all this stuff, but I just got to go click and then download.
- [05:59]
Leo Laporte
The easiest thing to do would probably just be make a YouTube playlist. We could certainly do that. Of everything in the last, say, seven or eight years, going back 20 years, I think that's going to take a shovel, a pick, and a miner's lamp, I think. But we might be able to do that. We'll have to figure that one out. I was, you know, it's funny you forget, but, I mean, I was surprised when I saw that our Vitamin D episode was audio only. It's like, oh, yeah, I guess we didn't have video all the whole time. Now the whole world says podcasts are video, which we didn't think that was the case for a while. A lot of people, by the way, in our YouTube chat and elsewhere are saying, vitamin D saved my life. I haven't been sick in four years. Things like that. So that will be an episode to listen to next week, if you're at all interested.
- [06:46]
Steve Gibson
The reason, I mean, there are many supplements that I take. There are. And I, as I was, as I was mentioning before, before I turned 50, I had just finished spin. Right. Five, I think it was, or maybe it was six.
- [06:58]
Leo Laporte
And.
- [06:59]
Steve Gibson
And I didn't have anything to do, so I just started reading and I went, vitamin A, vitamin B, vitamin C, vitamin D vitamin, and so on. And of all the things that I encountered and that I myself take, it is the biggest bang for the buck. It's the, it's inexpensive, it costs nothing, $15 for like a year's supply. And I mean, there are some other stuff that's very expensive, which I also believe in. But, you know, it's not, it doesn't make sense for everybody. It's not. It doesn't have the same return on investment, so to speak. So that, that, that's why Vitamin D got singled out for that podcast is I couldn't think of anything else that was easier to do. They're all. Also, there are a lot of people don't like swallowing big pills. I. I was something I recommended to my mom once, and she said, she called me, she said, honey, this is an suv, so I can't swallow this.
- [07:55]
Leo Laporte
I have cast calcium pills that. Horse pills. I don't know what.
- [07:59]
Steve Gibson
Yeah, because they're bulk. Yeah, they are.
- [08:00]
Leo Laporte
They're.
- [08:01]
Steve Gibson
Anyway, so. So, you know, vitamin D. I mean, in fact, Lori said To me. My. My wife.
- [08:06]
Leo Laporte
We.
- [08:06]
Steve Gibson
We were FaceTiming this morning because I left the house to. To cut. To come here to get an early start. And, and she. While we were FaceTiming, she said, oh, she said, I see the vitamin D twinkling on the floor in the kitchen because she dropped one and it just disappeared because it's. It's a little tiny droplet. So anyway, I call them little drops of sunshine, as you'll hear in the podcast. And anyway, I couldn't. I. I think it's just a. It's a. You know, it's a complete win. Nowadays, you need to combine it with K D3, with K2, and.
- [08:36]
Leo Laporte
Right. Oh, my. We lost you, Steve. Hold on.
- [08:42]
Steve Gibson
Oh, that.
- [08:43]
Leo Laporte
You just disappeared.
- [08:44]
Steve Gibson
I hear you. Oh, there I am. Weird. So.
- [08:47]
Leo Laporte
Well, I got an ad to do.
- [08:49]
Steve Gibson
You do. And then we got a picture of the week.
- [08:51]
Leo Laporte
Don't. Don't move on because I want to tell everybody about our sponsor for security now, Zscaler, the world's largest cloud security platform. You probably want to know about this. You see, we live in an interesting world, and that could be a blessing, and that could be a curse. AI is an absolute blessing in many ways. Many businesses are discovering AI can really help them become more efficient, more effective. We're finding all sorts of ways to use it, but unfortunately, so are the bad guys. They're finding new ways to attack, thanks to AI. The potential risks and rewards of AI are just too great to ignore. And then there's also the issue of using AI, your employees using AI at work, and accidentally exfiltrating proprietary company information. It really can be a mess. But Zscaler can solve all of those problems. Generative AI is. Is increasingly being used by bad guys to make incredibly effective phishing lures. You know, stuff that you know is letter perfect. They're using it to write malware. They're even using it once they break into your system to automate data extraction, because that's the new thing, right? You don't just ransomware somebody. You want to also blackmail them with the data that you download of their. Of their customers. You don't want to get there. You don't want to be on that train. There were 1.3 million instances. And this is the other side of it, the data leaks. There are 1.3 million instances of Social Security numbers leaked by accident to AI applications. ChatGPT and Microsoft Copilot saw nearly 3.2 million data violations themselves. So it's clear we really need to think seriously about your organization's Safe use of Public and Private AI well, we got a great answer. In fact, check out what Siva, the Director of Security and Infrastructure at Zora, says about using Zscaler to prevent AI attacks. Watch With Zscaler, being in line in a security protection strategy helps us monitor all the traffic. So even if a bad actor were to use AI because we have a tight security framework around our endpoint, helps us proactively prevent that activity from happening. AI is tremendous in terms of its opportunities, but it also brings in challenges. We're confident that ZSCALE is going to help us ensure that we're not slowed down by security challenges, but continue to take advantage of all the advancements. With Zscaler Zero Trust plus AI you can safely adopt generative AI and private AI to boost productivity across the business. Their Zero Trust architecture plus AI helps you reduce the risks of AI related data loss and protects against AI attacks to guarantee greater productivity and compliance. Such a great solution. Find out more. A zscaler.com security make it right write that down zscaler.com/security and don't forget that slash security because that's how they know you saw it here. Zscaler.com Security we thank him so much for supporting the good work Steve's doing on security. Now I am ready for a picture of the week sir.
- [12:09]
Steve Gibson
So our title for this picture is rather than discarding the heat from a power sucking bitcoin mining rig, why not use it to heat your home?
- [12:23]
Leo Laporte
It looks like a furnace.
- [12:24]
Steve Gibson
It is, it is. Literally it is a bitcoin mining furnace. So what we see just having reverse engineered this from the photo, AC power is coming in at the right, that big silver spiral cable going in to deliver power to it. Down below we see two silver hoses. So this is a fluid cooled bitcoin mining rig. And then you can see mounted down below in that dark, that dark red in the center is a, is a circulating pump which then runs out off to the upper left where, where you see a series of hoses. So what this thing is doing is it is a radiant heating system where all those hoses are going off carrying hot water to radiators scattered around the house that have air being pushed across them. They pick up the heat from the fluid, push it into the air, returning cold fluid back to the mining rig which then it of course reheats and the cycle repeats. So it is a, it is a power efficient heater for money making heater people who live in cold climbs.
- [13:50]
Leo Laporte
Wow.
- [13:50]
Steve Gibson
Yes. And of course above that is A laptop sitting there hooked up to the Ethernet. You see the yellow Ethernet cable plugging in on, on, on the right. And it's connected to the mining rig monitoring the, the money that this thing is making while it heats your house. Wow. So anyway, just. And that it turns out this is a commercial enterprise. There are, there is, there are companies selling commercial home heaters which make money at the same time.
- [14:18]
Leo Laporte
What a world.
- [14:19]
Steve Gibson
Very cool. Yeah. And speaking as I said, this is like, there's a, like a weird conjunction of, of crypto mining all happened today or this week. The blockchain analytics company we've talked about before Chainalysis posted an interesting end of the year piece just last Thursday which they titled North Korea drives record 2 billion crypto theft year pushing all time total to get this $6.75 billion.
- [14:56]
Leo Laporte
Oh my God.
- [14:58]
Steve Gibson
Yeah. I mean there is as they say, money to be made in them thar Hills. So $2 million North Korea stole from just generally crypto. And, and we'll take a look, take a look at the breakdown here in a second. But that is, but their all time total is $6.75 billion that North Korean hackers have made by basically figuring out how to get a hold of other people's money thanks to, unfortunately it's digital currency. And as we know, digital security is the reason we spend a couple hours every week here for the last 20 plus years trying to see how we can get it right. So the article was lengthy. I'm not going to share it all, but it provides it, as I said, a really interesting breakdown into today's digital asset industry. The article starts by laying out five points about North Korean. They said first, North Korean hackers stole $2.02 billion in cryptocurrency in 2025. And this is interesting, a 51% year over year increase from the from 2024, which as I said pushed their all time total to 6.75 billion. Now this is, this is interesting too also, despite there being fewer attacks, which means they're getting, they're netting more per attack this year than they were last year. Second, the DPRK is achieving larger thefts. Oh, this is, they're just making the point I did with fewer incidents, often by, oh, here's a frightening tidbit. By embedding it workers inside crypto services or using sophisticated impersonation tactics targeting executives. So I mean they're like sitting around, what can we do to get those fat Westerners cash? Third, the DPRK shows clear preferences for Chinese language Money laundering services, bridge services, and mixing protocols with a 45 day laundering cycle following major theft. So we've, we've talked about that before too. In fact, it was, there was these guys, North Korea, that was behind that massive theft. I think it was in February. I, I have it in the notes where a, a huge amount of money was lost and then immediately like it dissolved into like across blockchains. The idea was you don't leave it all in one place, right? You break it up into small pieces and you start moving, moving it around, swapping it in and out of blockchains. You want to make it difficult to find, you know, in other words, modern day crypto laundering is now a well established sub industry. They said individual wallet compromises, you know, like individual people's wallets, surged to 158,000 incidents. 158,000 individual wallets were somehow penetrated, affecting 80,000 unique victims. During this year, 2025 though, the, the total value stolen, which was $713 million, so 0.713 billion, 713 million decreased from what was stolen from individuals in 2024 last year. And despite increased total value locked in defy hack losses remain suppressed in 2024-2025, suggesting some improved security practices are making a meaningful difference. Okay, so then to give a little bit more flesh on this, they explain the cryptocurrency ecosystem faced another challenging year. Yeah, you could say that. 2.1 billion in 2025. With stolen funds continuing their upward trajectory. 51% gain. Right. This year over last. Our analysis reveals a shift in crypto theft patterns characterized by four key developments. The persistence of the Democratic People's Republic of Korea, the DBRK as a primary threat actor in this theft industry. The growing severity of individual attacks on centralized services, a surge in personal wallet compromises, and an unexpected divergence in decentralized finance hacking trends. These patterns emerge clearly from the data and reveal significant changes in how crypto theft is occurring across different platform types and victim categories. As digital asset adoption expands and valuations reach new heights, understanding these evolving security threats has become increasingly critical. It's worth noting too that, I mean, there's just a lot more of it this year than there was last year. Right. So there's just more potential for, for loss with more crypto sloshing around in all of these blockchains. They said the cryptocurrency industry witnessed over $3.4 billion in theft from January through early December 2025. So there, you know, North Korea was a huge piece of it. But 3.4 billion so far this year with oh, and here's the one we were talking about with the February compromise of BYBIT alone accounting for one and a half billion. Remember that? They just, they really got taken to the cleaners and, and said, you know, please we'll, you know, we'll give you some if you'll give us most back. And that just never happened because again, North Korea. So anyway, it was in March, it was toward the end of February that that BYBIT hack happened which we then immediately picked up on and covered early in March of this year. And so remember that they used a third part, they meaning by bit, used a third party multi sig wallet provider. They had outsourced their multiple signature wallet security to an outfit called unfortunately Safe Wallet. The extremely clever North Korean hackers injected malicious code into the Safe Wallet domain which selectively targeted by BIT's smart contracts and their multi signature process which allowed them to compromise BYBIT and extract all that money. But aside from all that, you know, just during 2025 this year the concerted efforts of North Korean hackers sitting in North Korea netted the the DPRK US$3.4 billion in digital cryptocurrency. So you can imagine they're probably, that group of elite hackers are probably being treated quite well by North Korean government. That chain analysis continues. Explaining beyond the headline figure, the data reveal important shifts in the composition of these thefts. Personal wallet compromises have grown substantially increasing from just 7.3% of total stolen value back in 2022, so 7.3 in 2022 to 44% two years later through 2024. And in 2025 the share would have been 37% if it weren't for the outsized impact of that single BYBIT attack. Meanwhile, they said centralized services are experiencing increasingly large losses due to private key compromises. And we know we've, we, I've stopped talking about it because there was so much of that going on that it was like oh, these people lost billions here and billions there. And it's like how can there be all this money? They said. Despite their institutional resources and professional security teams, the these platforms remain vulnerable because of this fundamental security challenge. While such compromises are infrequent, their scale still drives enormous shares of stolen volume when they do occur, accounting for 88% of all losses in the first quarter of 2025. The persistence of high threat volume indicates that while some areas of crypto security may be improving, attackers continue to find success across multiple vectors and I'm going to talk a little bit about that as soon as I wrap up with this. They said stolen fung activity has always been outlier driven, with most hacks relatively small and some immense. But 2025 reveals a striking escalation. They said the ratio between the largest hack and median of all incidents has crossed the thousand x threshold for the first time, meaning that the big ones have gotten far bigger and the median attack size has shrunk such that the ratio between the the largest and the median is now a thousand times. They said funds stolen in the largest attacks are now now a thousand times larger than those stolen in the typical incident, surpassing even the 2021 bull market peak, as they termed it. They said these calculations are based on the US dollar values of funds stolen at the time of their theft. This growing discrepancy has concentrated losses dramatically the top three hacks in 2025. So the top three in 2025 account for 69% of all all service losses, creating a landscape where individual incidents have an outsized impact on yearly totals. While the number of incidents may fluctuate and median losses grow with asset prices. Right, because you know, Bitcoin is like way more valuable now than it was a couple years ago. The potential for catastrophic individual breaches is escalating faster still. The Democratic People's Republic of Korea DPRK continues to pose the most significant nation state threat to cryptocurrency security, achieving a record breaking year for stolen funds despite an assessed dramatic reduction in attack frequency. In 2025, North Korean attackers were back to stole at least 2 billion in cryptocurrency, 681 million more than in 2024, representing a 51% increase year over year. This marks the most severe year on record for DPRK crypto theft in terms of value stolen, with DPRK attacks also accounting for a record 76% of all service compromises. So overall, 2025's numbers bring the lower bound cumulative estimate for cryptocurrency funds stolen by the DPRK. So 2025 brings the lower bound cumulative to $6.75 billion. In other words, they're not going to stop. I'm sure the, those, those, those hackers are considered elite and they're being treated quite well. North Korean threat actors, they said, are increasingly achieving these outsized results, often by embedding IT workers, one of DPRK's principal attack vectors inside crypto services to gain privileged access and enable high impact compromises. Part of this record year likely reflects an expanded reliance on IT worker infiltration at exchanges, custodians and Web3 firms, which can accelerate initial access and lateral movement ahead of large scale theft. More recently, however, DPRK linked operators have flipped this IT worker model on its head. Instead of merely applying for roles and embedding themselves as employees, they are increasingly impersonating recruiters for prominent Web3 and AI firms, orchestrating fake hiring processes that culminate in technical screens, as they call them, designed to harvest credentials, source code and VPN or single sign on access to the victim's current employer. Right, so they're pretending to be recruiting people from these firms, getting inside information in the process and then using that against them because they have no intention of hiring anybody at the executive level, they said. A similar social engineering playbook appears in the form of bogus outreach from purported strategic investors or acquirers who use pitch meetings and pseudo due diligence to probe for sensitive systems, information and potential access paths into high value infrastructure. An evolution that builds directly on the DPRK's IT worker fraud operations and their focus on strategically important AI and blockchain companies. So just think about that for a minute. I mean basically we have a hyper aggressive state backed hacking community that is, I'm sure, where, you know, speaking English with as little accent as possible is highly valued that are doing everything they can think of every clever social and engineering approach to take people's money, they said. As we've seen in years past, the DPR continues to undertake significant high value attacks than other threat actors. Significantly higher value attacks than other threat actors. As shown in in the chart from 2022 to 2025, DPRK attributed hacks occupy the highest value ranges, while non DPRK hacks show more, more normal distributions across all theft sizes. This pattern reinforces that when North Korean hackers strike, they target large services and aim for maximum impact. This year's record haul came from significantly fewer known attacks. This shift, fewer incidents yielding far greater returns reflects the impact of the massive Bybit hack in February. So that did that, that thing that, that separate 1.2 or no one and a half billion dollars that did tend to skew a lot of, a lot of these percentages and charts because you know that's a one off.
- [30:30]
Leo Laporte
You realize that North Korea's GDP is only $18 billion. So this is a significant source of hard.
- [30:37]
Steve Gibson
Yes, it's a third, A third of their cash.
- [30:41]
Leo Laporte
Yeah, this is significant.
- [30:43]
Steve Gibson
You see why they do it and. Yes, exactly. It's why they do it. And I mean it it also ought to, it ought to raise the anxiety level on the, the people in charge of security at, at you know, all of these major exchanges to just to know that because you know, motivation, as we know motivation and, and pushing and wanting and, and, and being as clever as you can is not something you want an attacker to have towards your organization. They, they will find a way in. The human factor is the weak link. It's, it's just, it's. I, I would think it would keep people, you know, executives and people in charge of security up at night wondering can they trust their own employees? Are they all really loyal and faithful? Where'd they come from? I mean I'm, I'm, they must be doing deep background checks on anybody that they hire.
- [31:43]
Leo Laporte
Yeah.
- [31:44]
Steve Gibson
So another way to look at this is that they are leveraging North Korea is leveraging trust at every level. You know, they might observe and determine who provides janitorial services for an intended target, then play obtain employment there and arrange to obtain access to their target's physical plant facilities. Or they masquerade as recruiters who are attempting to hire employees away from their target and use the departing employees access and their desire to, you know, impress their would be next employer or recruiting firm. You know, they're trying to get a higher paid job so that maybe they leak a little bit of useful insider information. Unfortunately, while we're all, you know, hard at work generating income, they're spending their time over in North Korea coming up with new and clever ways to separate us from that income we've generated. And they've got a lot of motivation. Chainalysis then spends a little bit of time talking about the money laundering employed by the dprk. But their discussion of, of the escalating threat from the number if not the size of personal wallet compromises I thought was interesting because anybody who's holding cryptocurrency they wrote. Through analysis of on chain patterns, in addition to the reporting from victims and industry partners, we can gain an understanding of the magnitude of personal wallet compromises. Although the true number of compromises is likely far greater than based on our lower bound estimates, personal wallet compromises now account for 20% of all value. So think about that one out of five, 20%, 1/5 of all value stolen this year in 2025, down from 44% of the total in 2024. So it's better this year was 44% of the total. On the other hand, remember that there was that one by bit one and a half billion which tended to skew Things representing an evolution in both scale and pattern. They said the total number of theft incidents surged to 158,000 in 2025, nearly triple the 54,000 back in 2022. So not just last year, but in 2022. So since, since three years ago, which was 54,000, we've. It's tripled to 158,000 in this past 2025 year. They said these dramatic increases are likely due to greater crypto adoption. For example, Solana, one of the blockchains with the greatest number of active personal wallets, had by far the largest number of incidents, around 26,500 victims. Yet despite they wrote more incidents and victims, the dollar did the total US dollar value stolen from individual victims actually declined from 2024's peak of one and a half billion dollars. Okay, so just take that last year, individual victims collectively, and this is lower boundaries estimates the, you know, the numbers that they're sure of. 2,024's lost one and a half billion dollars. That's down about half. This year it was only seven. Only 713 million from individual victims. They said this suggests that attackers are targeting more users but are managing to steal smaller amounts per victim. Network specific victimization data provides additional insight into which domains present the greatest risk to crypto users. They said, when measuring crime rates per 100,000 wallets in 2025 this past year, Ethereum and Tron show the highest rates of theft. Ethereum's large size indicates both high rates of theft and a high victim count, while Tron's position shows elevated rate of theft despite a smaller active wallet base. In contrast, Base and Solana show lower victimization rates despite significant user bases. These measurable differences highlight that personal wallet security risks are not uniform across the crypto ecosystem. The variation in victimization rates across chains with similar technical architectures suggests that factors beyond technology, such as user demographics, popular applications, and criminal infrastructure play important roles in determining theft rates. So a bunch of information I thought was really interesting about where this whole cryptocurrency industry stands on the dark side. You know, a lot of money is leaking from people's wallets and a lot of is leaking over to the dprk. And what all this says, I think ultimately for the end user is that anyone who is technically capable of transferring any cryptocurrency they do not need to have online into an offline wallet has nothing to lose and everything to gain. Right? It's not like you have to have it online to have its value keep increasing no. You know, you pull your cryptocurrency offline, if you can. If I today owned any appreciable amount of cryptocurrency, I would not be inclined to leave it sitting in an online account of any kind. The. The beauty of this technology is that another wallet can be created with a private key that has never been seen online, and the currency can be then safely transferred into that wallet under that key. And yeah, it's true that, you know, at that point, you are then utterly responsible for its safekeeping, which, yes, is a lesson that Leo and I both painfully learned the hard way, back before our crypto had become, you know, before it had any value at all.
- [38:15]
Leo Laporte
So, you know, there has been talk at the federal level of outlawing custody, personal custody, wallets. No. Yes. Because of course, then you're out of.
- [38:31]
Steve Gibson
You can't be tracked out of the system.
- [38:33]
Leo Laporte
You're out of the system. And so they don't want you to have your own wallet. They want you to have a custodial wallet.
- [38:43]
Steve Gibson
Wow.
- [38:44]
Leo Laporte
This is. I.
- [38:48]
Steve Gibson
Well.
- [38:48]
Leo Laporte
And honestly, I wish I had had a custodial wallet because I'd probably be rich right now. But nevertheless, less.
- [38:53]
Steve Gibson
Right.
- [38:55]
Leo Laporte
I'm glad I didn't. And I didn't on purpose because I. I wanted my own wallet. Right.
- [39:00]
Steve Gibson
Well, Leo, we didn't. There were no exchanges.
- [39:02]
Leo Laporte
There was no money.
- [39:03]
Steve Gibson
There was nothing.
- [39:04]
Leo Laporte
There was.
- [39:05]
Steve Gibson
You. Bitcoin was free. There was a. There was a bitcoin faucet that was dripping bitcoin and you could just go get yourself some.
- [39:14]
Leo Laporte
This is why we need time machines. All right.
- [39:20]
Steve Gibson
Yes. That was the most expensive installation of Windows 7 I have ever, ever.
- [39:25]
Leo Laporte
Think about it. You're watching Security now. That's Steve Gibson in the cute hat. I'm Leo Laporte. I've doffed my cap, but I've doff it to Steve as our last episode of the.
- [39:37]
Steve Gibson
Of the year.
- [39:38]
Leo Laporte
Steve did it here on Sunday on our holiday episode of Security Now. It was really fun. Thank you for being here with Paris Martineau and Mark Micah Sargent. We covered all the big stories of the year and we had a great time. Three hour marathon. Yeah. But it was a lot of fun, so I appreciate it.
- [39:53]
Steve Gibson
And not surprising a lot of time was spent on AI because after we stepped into that puddle, it wasn't easy to step get out of it.
- [40:01]
Leo Laporte
It's like a quicksand. McQuagmire. We did a little security talk too, though. We talked a little bit about that. On we go. Let's go. Security now continues.
- [40:09]
Steve Gibson
On Steve okay, so last week Amazon's AWS Security blog shared the news of their discovery of an advanced crypto mining operation targeting AWS users whose credentials had leaked. So not Amazon's fault, right? These people had a bad password or whatever. The brief start of their blog posting reads like a sales and marketing piece, but I need to share it just as a means of establishing the context. So, you know, hold your nose. They wrote Amazon GuardDuty and our automated security monitoring systems identified an ongoing cryptocurrency Perens crypto like thank you for the abbreviation mining campaign. Beginning on November 2, 2025. The operation uses compromised AWS identity and access management credentials to target Amazon elastic Container Service ECS and Amazon Elastic Compute Cloud EC2 Guardduty Extended Threat Detection was able to correlate signals across these data sources to raise a critical severity attack sequence finding Using the massive advanced threat intelligence capability and existing detection mechanisms of Amazon Web Services, AWS GuardDuty proactively identified this ongoing campaign and quickly alerted customers to the threat. AWS is sharing relevant findings and mitigation guidance to help customers take appropriate action on this ongoing campaign. It's important to note that these actions don't take advantage of a vulnerability within an AWS service. Rather, they require valid credentials that an unauthorized user uses in an unintended way. Nice way to put it. Although these actions occur in the customer domain of the shared responsibility model, AWS recommends steps that customers can use to detect, prevent and reduce the impact of such activity. Okay, so essentially they're saying our guard dog sniffed out some suspicious activity. Oh by the way, using our massive threat intelligence and we found that bad guys were abusing our customers accounts after having somehow obtained their IAM account credentials. Then we begin to get to the interesting details, which are they write the recently detected crypto mining campaign employed a novel persistence technique designed to disrupt incident response and extend mining operations. The ongoing campaign was originally identified when GuardDuty security engineers discovered similar attack techniques being used across multiple AWS customer accounts, indicating a coordinated campaign targeting customers using compromised IAM credentials operating from an external hosting provider. The threat actor quickly enumerated Amazon EC2 service quotas and IAM permissions before deploying crypto mining resources across Amazon EC2 and Amazon ECS. Within 10 minutes of the threat actor gaining initial access, crypto miners were operational. A key technique observed in this attack was the use of modify instance attribute, which is an API call with disable API termination set to true. So disable API termination they and they wrote forcing victims to re Enable API termination before being able to delete the impacted resources. Disabling instance termination protection adds an additional consideration for incident responders and can disrupt automated remediation controls. The threat actor Basically, the bad guys figured out how to turn on a firewall to prevent us from turning off their crypto miner, right? So they said the threat actors scripted use of multiple compute services in combination with emerging persistence techniques represents an advancement in crypto mining persistent methodologies that security teams should be aware of. Okay, so they said, or so so that. That's that. So this use of disable API termination, also known as termination protection, is a setting on an Amazon EC2 instance that prevents that instance from being terminated using AWS provided APIs, the AWS command line interface, or the AWS Management Console or the API. None of them work. I mean, so this is obviously there. You know, the intent is to give EC2 users a means of preventing the accidental termination of some service or process that absolutely, positively always needs to be present and running. So who would be surprised that bad guys who know their way around the operation of AWS EC2 compute services would enable blocking their crypto miners termination? It's like, duh, that seems like a good thing to do. We then learn that a malicious Docker Hub image was created a few days prior to the first observed instance of this intrusion. Docker Hub being sort of like reminiscent of GitHub, right? It is a source of Docker images. So on October 29, something with over 100,000 pulls had been created. That Docker Hub image was used to deploy crypto miners to containerized environments. Now, inside that image, they found something known as SRB miner hyphen multi, the SRB minor hyphen multi binary. I'll be talking about that in a minute. For crypto mining, this specific image having been identified as malicious, I.e. the entire docker image has since been taken down from Docker Hub. But we know that threat actors will probably deploy similar images under different names. You know, like why wouldn't they? We know they do. The AWS security guys also discovered that the attackers employed the AWS SDK for Python, known as Boto3, the user agent to deploy Python based automation scripts to. Throughout the entire attack chain. The crypto mining domains were asia, rplant, xyz, EU R, Plant XYZ and Na R Plant XYZ used for the the miners. Now, Amazon's mention of the SRB miner reminded me of something I had seen earlier. So I tracked down a different recent piece in the Hacker News titled Cybercriminals exploiting Docker API servers for SRB minor crypto mining attacks, the Hacker News wrote. Bad actors have been observed targeting Dr. Docker remote API servers to deploy the SRB Miner crypto miner on compromised instances, according to new findings from Trend Micro. The Trend Micro researcher said. In this attack, the threat actor used the GRPC protocol over H2C to evade security solutions and execute their crypto mining operations on the Docker host. The attacker first checks the availability and version of the docker API, then proceeds with request for GRPC H2C upgrades and GRPC methods to to manipulate Docker functionalities. Unquote. The adversary writes the Hacker News the adversary checks for GRPC methods that are designed to carry out various tasks pertaining to managing and operating Docker environments remotely, including those relating to health checks, file synchronization, authentication, secrets management, and SSH forwarding Okay, so there's a bunch of Docker specific jargon flying back and forth here. What's happening is that the Internet, it turns out, now contains of course a population of publicly accessible Docker remote API servers which should not be publicly exposed almost certainly and of course when not properly secured, can be remotely exploited to accept host and run attacker provided crypto miners. The Docker docs talk about this. There's a page on Docker Doc titled Configure remote access for Docker daemon, which says by default the Docker daemon listens for connections on UNIX sockets to accept requests from local clients, local being the keyword. By default, the Docker daemon listens for connections on a Unix socket to accept requests from local clients. They said you can configure Docker to accept requests from remote clients by configuring it to listen on an IP address and port, as well as the Unix socket. Unix sockets being a local in, you know, intra machine technology. But then they have a big impossible to miss warning box in a different background color. You can't miss it and it says warning. Configuring Docker to accept connections from remote clients can leave you vulnerable to unauthorized access to the host and other attacks. It's critically important, they wrote, that you understand the security implications of opening Docker to the network. And they're not necessarily even talking about the Internet, right? Just just your own in whatever it is, your lan, your enterprise, however big. Putting Docker on a network puts that machine's resources on the network. They said if steps are not taken to secure the connection, it's possible for remote non root users to gain root access on the host remote Access without TLS is not recommended and will require explicit opt in in a future release. Oops. But not yet, apparently. For more information on how to use TLS certificates to secure this connection, see another link. Protect the Docker daemon socket.
- [52:07]
Leo Laporte
This is kind of ironic because one of the things people use Docker for is to run home servers, right? Very popular way to install self hosted software almost always. I mean, very frequently you're going to.
- [52:20]
Steve Gibson
Put it online, right? Well, and so are you using it to host a server on your own machine or, you know, on a machine.
- [52:29]
Leo Laporte
Right here that is open to the Internet? Of course, the smart way to do it was with tailscale, you know, and hide it behind a VPN and a firewall so that you have to log into the VPN and then you have access to. To it on the lan.
- [52:44]
Steve Gibson
That is exactly the right way to do it.
- [52:46]
Leo Laporte
It's very tempting to just say, well, I have this fine, you know, server, I'd like to put it on the Internet, right? And that's how people do it with Docker very frequently.
- [52:56]
Steve Gibson
So we learn that Docker themselves. It's not. This is not Docker's fault, right? No. Docker themselves did everything right. The default is secure local machine only and accessed by clients running on the local machine connecting to Docker through the local UNIX socket interface. So it appears that there are those who wanted to have their Docker interfaces available across the network. And Leo, who knows about authentication, right? I mean, and this is the problem, you know, is that, well, I get to it. So, you know, did they intend it only for the lantern and not the wan? Was this a misconfiguration of an important option? Or did they deliberately make their Docker instances available across the entire global Internet? Certainly they didn't intend to expose Docker itself, right? It's one thing to run a server on Docker and have that server's services exposed through the Docker container. It's different, though, to expose the Docker API itself, which then gives anybody who has access to it access to your, you know, to, to your underlying machine. So I should spend some time distilling a short list of fundamental laws of security. At some point, Leo, maybe we'll get around to that. Isaac Asimov, you know, created his three laws of robotics. This podcast could have a similar short set of laws.
- [54:30]
Leo Laporte
It's a great idea.
- [54:31]
Steve Gibson
If we did have such, right up there near the top, would be never rely upon the strength of remote authentication. Period. That's it. Never rely upon the strength of remote authentication. We see instance after instance, time and time again. It doesn't work. Microsoft always thought RDP had authentication, right? I mean, you have to authenticate, you have to log in. Didn't stop pretty much anybody from, from logging in when, you know, in its original incantations. So never rely upon the strength of remote authentication. Would have been one of our golden rules. So, you know, we just keep seeing that mistake being made over and over. But for whatever reason, Docker's API, not the services it's hosting, but its API is being published. Maybe just people don't understand, like, what they're doing. So it's like, oh, this is easy.
- [55:32]
Leo Laporte
Yeah, yeah, because it's really easy to get up and running.
- [55:36]
Steve Gibson
That's too easy.
- [55:37]
Leo Laporte
Beauty of it.
- [55:39]
Steve Gibson
Yeah. So for whatever reason, the Docker API is being published on the Internet and bad guys are now scouting around looking for them. So this is a variant on the AWS EC2 case that we first talked about. In this second instance, bad guys have figured out a way to bypass several layers of intended security. Trend Micro and the Hacker News both concluded their coverage with the advice to better secure all publicly exposed instances of Docker API servers. Duh. Yeah. Okay, now I also should clarify that this SRB miner that was implicated in both of these instances is not in any way itself malicious. It is a beautiful piece of work. In fact, it's a CPU plus GPU miner which mines using a systems processor. Plus if you've got them, I hope you do an amd, Nvidia or Intel gpu depending upon the build of of the miner. It's able to mine using up to four different algorithms at the same time, which is to say four different cryptocurrencies is able to mine simultaneously, which is why they called it SRB minor hyphen multi, because it's multi algorithm. It's available to run on 64 bit instances of either Windows or Linux. And it can be found at srbminer.com srb m I-N-E r.com poking around over there, we see a list of interesting features. Mine up to four algorithms simultaneously. Guided setup mode run in background without a window hash rate watchdog that restarts miner on a gpu. Error monitoring of GPU temperature and auto turn off if temperature is too high. System shutdown on too high GPR GPU temperature. Minor auto restarts on too many rejected shares. API to obtain minor statistics. Web based GUI interface for minor statistics. Multiple pools with failover support. Difficulty monitor reconnects to pool if difficulty is too high. Job Timeout monitor reconnects to pool if no job received for a long time and a bunch of other useful features. So it is distributed there on that site and also through their GitHub repo. The reason I wanted to share these two recent examples of surreptitious mining is that they dovetail so nicely with with the chain analysis report about North Korea. All of these instances have a single common thread. That thread is money. It's about money. It's all about money. And it's only about money. That's also, of course, the entire motivating factor behind all of the breaches and the ransomware and the extortion that we're now looking at and, and seeing and, and, and, and reporting on and which are growing. The bad guys want to obtain an advantage and they want to leverage that advantage to get themselves as much of someone else's money as they can. They could not care less, frankly, about some random company's client list or random people's Social Security numbers or anything else that might be stored in an exfiltrated database or that's not money. But if they can figure out a way to turn that data, which they themselves have no interest in whatsoever, into some cold hard cash, that unfortunately for the original owners of that data, they will be highly motivated to find a way to do just that. It's all about money. They want ours. And sadly, today's network and other security practices are proving not to be strong enough to keep them from finding ways to get our money. 153,000 wallets, what was it? 80,000 individual users? Had they lost some of their money because the bad guys want it? And today's security, while it seems to be improving, still isn't enough to patch the leaks of that cash. Really interesting. Yeah. Now would be another good time to take a break because I'm about to get into a really interesting question of why have our smart TVs become so sluggish?
- [60:28]
Leo Laporte
Sounds like a personal problem, but we'll get to that in a moment. You're watching Security now with Steve Gibson year end episode. So glad you're here. Especially a thanks to our Club Twit members who make all of our shows possible without you. Well, we just, we wouldn't be able to do what we do. And that's why we would really love to have you join Club Twit. You get ad free versions of all the shows, including this one. You also get access to the Club Twit discord, which is sometimes I call it the Club Twit. Disco because it's so much fun. This is where our club members hang out to chat. You see, Darren has designed already that didn't take long. The book cover for your new book, the Three Laws of Security. I love that. And apparently I wrote the forward. Although there was a group of people saying it should be Bill Gates really. But anyway that's just part of what goes on in here. They're talking about the shows but they also talk about all the other subjects geeks are Interested in from 3D printing to coding to gaming. We have a couple of club TWIP Minecraft servers people hang out on. We do a lot of events in the club. In fact I'm going to interview a comedian an la comic named Mark Malkoff on January 2nd, just when we get back about his new book. Love Johnny Carson. I know it's crazy. I'm a Johnny Carson fan, has nothing to do with tech. Mark emailed me, he said I know it's not tech, but do you ever want to talk? I said I'd love to talk to you. So that'll be fun that following that immediately, our very popular AI user group. We do that on the first Friday of every month. A great way to share what you're doing in AI with other members of our club. And we have some people doing some amazing stuff. We record some of our shows that are not in public the club shows, we call them in the club so you could be part of those. Stacy's book club is coming up. Micah's Crafting Corner photo time with Chris Marquardt. The book for this month actually is gonna be January 30th so you have plenty of time more than a month to read. It is quite interesting. It's called the Heist of Hollow London. Stacy picks these, you vote on them. We do a book club every other month on usually it's a sci fi story. This is a very much a sci fi story. So that's just one reason to join the club. The other reason is really the most important reason to me which is it supports the work we do. 25% of our operating expenses are paid for by you, our club members. We're very, very grateful. If you're not a member, consider joining. We do have a 10% off coupon good through the 25th so you have a couple more days when you sign up for a year. Make it a good gift though. And you know what the nice thing about it, it will be ready in time for Christmas. I'm just saying you can also have their family plans and there's corporate plans, and you can also buy it for yourself. Twit TV Club. Twit. We really, really would love to get almost everybody who listens to these shows into the club. It would make life a lot easier. We wouldn't have to worry about advertising. You'd be supporting the programming that you love. And to me, that seems like the best of all possible worlds. All right, that's enough of me. Let's get back to Steve and security now.
- [63:48]
Steve Gibson
So I ran across an interesting description of a new, quite large and distressingly capable Android based DDoS botnet that preferentially inhabits smart TVs. This botnet appears to be capable of generating around 30 terabytes. 30 trillion. I'm sorry, 30 terabits. 30 trillion bits of DDoS flood per second. And it has so many other features that would concern anyone who knew that it had taken up residence in their family's smart tv. The security company that received a sample of this bot and reverse engineered its operation posted their complete analysis under the title Kim Wolf. That's their name for it. K I M W O L F. For reasons we'll see in a second, Kim Wolf exposed the massive Android botnet with 1.8 million infected devices. Remember, Leo, those quaint days when a couple thousand, you know, commandeered routers? Like thousands. Oh my God. Oh, 1.8 million.
- [65:06]
Leo Laporte
Now that's amazing.
- [65:08]
Steve Gibson
They wrote on October 24, 2025. So a couple months back, a trusted partner in the security community provided us with a brand new botnet sample. The most distinctive feature of this sample was its command and control domain. And it's 14 em e e l I a that's 14 Emilia. Then we see the word terrace T E R R A C E then West Brockbury MA and then 02132. That's a street address of somebody. Dot Su is the command and control domain they. And get this, they wrote which at the time ranked. So that wacky domain name at the time ranked second in the Cloudflare domains ranking. A week later it even surpassed google.com to claim the number one spot in Cloudflare's global domain popularity rankings. They said there is no doubt that this is a hyperscale botnet. Based on the information output during runtime and its use of the Wolf SSL library. We have named it Kim Wolf. Okay, now just to clarify here, what they what they intend by citing Cloudflare's domain rankings is that Cloudflare tracks, ranks and reports the domain. The popularity of of the domains being used across the Internet. From their view, there are so many instances of this newly discovered botnet that it was briefly taking the number one slot globally in Cloud Flare's global rankings, pushing even Google down from its normally secure first slot ranking down into second place. So that is a lot of activity. Okay, so get a load of what they discovered about this massive newcomer, they wrote. Kim Wolf is a botnet compiled using the NDK that's Android's native developer kit. In addition to typical DDoS attack capabilities, it integrates proxy forwarding, remote reverse shell and file management functions. Okay, so it's, it's, it's a proxy meaning that other traffic can be routed through your smart TV and stuff appears to be coming from you. A reverse shell meaning they're able to, you know, talk, log into your Android instance running in your smart TV and file management, you know, load, save, you know, get files and so forth, they said. From an overall architectural perspective, its functional design is not complex, but there are some highlights worth noting. For example, the sample that they received uses a simple yet effective Stack XOR operation to encrypt sensitive data. Meanwhile, it utilizes the DNS over tls.protocol, which actually is built into Android. So that would make sense to encapsulate DNS requests to evade traditional security detection. Furthermore, its command and control identity authentication employs a digital signature protection mechanism based on elliptic curves. So the command and control is is the command and control system is now using elliptic curve digital signatures to to prevent anybody else from act from from from commandeering control of the botnet. Different world than we were than we used to be in they said where the bot side will only accept communication instructions after the signature verification passes. Recently it's introduced ether hiding technology to as an ether block Ether Ethereum ether hiding technology to counter takedowns using blockchain domains. These features are relatively rare in similar malware. Based on our so this is a sophisticated little bot. Based on our analysis results, it primarily targets Android platform TV boxes. The welcome to Android Support center message displayed on the command and control back end also corroborates this. The Kim Wolf samples use a naming rule to identify version numbers. The sample previously provided by our community partner was version four. After completing the reverse engineering analysis, we imported the samples intelligence into the XLabs and these are security researchers from XLAB into the XLABS Cyber Threat Insight and Analysis system, successively capturing multiple related samples including they got their own copies of V4 and also the next one V5, thus achieving automated continuous tracking of this family, meaning that now, now that they're in they, they will automatically be updated when, when the botnet system updates, they said. On November 30, we captured another new sample of this botnet family and successfully took over one of the C2, one of the command and control domains, thereby obtaining the opportunity to directly observe the true operating scale of this botnet for the first time. Based on statistics from source IP data that establish connections with our registered C2 address and whose communication communication behavior matched Kim Wolf command and control protocol characteristics, we observed a cumulative total of approximately 2.7 million distinct source IP addresses over the three days from December 3 through December 5. 2.7 million, they said. Among them, we observed approximately 1.36 million active IPs on December 3, 1.83 million on December 4, and 1.5 million on December 5, they said. There's an IP overlap between different dates. Analysis indicates that Kim Wolf's primary infection targets are TV boxes deployed in residential network environments. Since residential networks usually adopt dynamic IP allocation mechanisms, you know, Dhcp, the public IPs of devices change over time, so the true scale of infected devices cannot be accurately measured solely by the quantity of IPs. In other words, the cumulative observation of 2.7 million IP addresses does not equate to to 2.7 million infected devices. Despite this, we still have sufficient reason to believe that the actual number of devices infected by Kim Wolf exceeds 1.8 million. This judgment is based on observations in the following areas. First, Kim Wolf uses multiple command and control infrastructures. We took over only a portion of of the command and controls, so we could only observe the activity of some bots unable to cover the full picture of the botnet. Also, on December 4th, the number of bot IPs we observed reach approximately 1.83 million, a historical peak. On that day, parts of the command and control normally used by Kim Wolf were taken down by relevant organizations, causing a large number of bots to fail to connect to the original command and controls and, and in turn to try connecting to, to the C2 we preemptively registered. So that means that there's an algorithm, right? We've talked about this in years past. An algorithm by which the bots generate the domains which they'll be using, and it's possible to look into the future and, and register a domain before the bad guys get to it, and then wait there for the bots to, to generate that domain name and then start, you know, send out DNS queries for it and then start connecting to it by ip. So they said this anomalous event caused more bots to be centrally exposed in a short period, so the data for that day may be closer to the lower limit of the true infection scale, that being 1.83 million devices. They said infected devices are distributed across multiple global time zones affected by time zone differences and usage habits, for example turning off devices at night, not using TV boxes during holidays, etc. These devices are not online simultaneously, further increasing the difficulty of comprehensive observation through a single time window. And and finally, Kim Wolf exists in multiple different versions, and the command and controls used by different versions are not completely identical, which is also one of the important reasons why we cannot obtain a complete perspective. Combining the above factors, we conservatively estimate that the actual number of devices infected by Kim wolf has exceeded 1.8 million. A botnet of such scale possesses the capability to launch massive cyber attacks, and its potential destructive power cannot be ignored. While working hard to track new versions, we were also full of curiosity about the old versions through source tracing analysis. Although we failed to capture old versions like V1 and V2, we we surprisingly found that Kim Wolf is actually associated with the Asuru botnet. Kim Wolf relies on the APK file to load and start it during runtime. A Dex file uploaded to virus total VT from India on October 7 showed obvious homologous characteristics which with Kim Wolf's APK. Subsequently, on October 18, the parent APK of that DEX was uploaded to VirusTotal from Algeria. The resource files of this APK contain asuru samples for three CPU architectures x86, x84 and ARM. We speculate that in the early stages of this campaign, the attackers directly reused Isiru's code. Subsequently, likely because Isiru samples had high detection rates in security products, Android platforms have more maturity more mature security protection systems compared to IoT ecosystems. The group decided to redesign and develop the Kimwolf botnet to enhance stealth and evade detection. So this is an evolution, an outgrowth of what was previously the largest, most powerful botnet known, they said from the monitoring data of the XLAB command tracking system. Statistics show that the main functions of the Kim Wolf botnet are usually concentrated on traffic proxying with a small amount of DDoS attacks. However, between November 19th and 22nd it went suddenly crazy. In just three days it issued 1.7 billion DDoS attack commands, with the attack range covering massive amounts of IP addresses globally. This high profile spree follows on the heels of the command and control domain's unprecedented rise to the number one to number one spot in in global popularity. Theoretically, such a large number of attack commands and targets may not be able to produce substantial attack effects on the targets, Right, because they're too short lived. This behavior may have been purely to demonstrate its own presence. Currently, the security community's understanding of Kim Wolf presents a polarized situation. Information in the public intelligence field is scarce, its propagation path is not yet clear, and the detection rate of related samples and their command and control domains on VirusTotal is extremely low. At the same time, due to the adoption of COVID technologies like dot, the association between its command and control and samples has not been effectively discovered. However, at the non public threat confrontation level, the situation is entirely different. We observed that Kim Wolf's command and control domains have been successfully taken down by unknown parties at least three times, forcing it to upgrade its tactics and turn to using ENS Ethereum name service to harden its infrastructure, demonstrating its powerful evolutionary capability. Given that Kim Wolf has formed a massive attack scale and its recent activity frequency and attack behaviors show a significant upward trend, we believe it's necessary to break the intelligence silence. We hereby release this technical analysis report to make relevant research results fully public, aiming to promote threat intelligence sharing, gather community strength to jointly respond to such threats, and effectively maintain cyberspace security. Okay, now everyone has a good sense now for what's going on with this apparent descendant of the previously massive and famous Assuru botnet. So one question is where are these infected TV boxes? Who has them? Since these researchers were briefly in the position to be receiving incoming bot traffic to their Command and Control IP to the tune of 1.83 billion IPS. No, sorry, 1.83 million IPS they were able to obtain the bots demographics Infected devices are distributed across, well, pretty much everywhere. 222 countries. How many countries are there? So the top 15 countries are in order of most to last the top 15 Brazil is the highest percentage of infections in consumer TB TV boxes of Kim Wolf at nearly 15% of of this 1.83 million devices are in Brazil 14.63 India's number two at 12.71% and we proudly the USA at 9 and a half 9.58% so we're in third place. So we are. So we are one ju just shy of 1/10 of the total Kim Wolf botnet infestation percentage. Argentina at 7.19 South Africa 3.85 the Philippines 3.58 Mexico at 3 China also at 3 Thailand 2.46 Saudi Arabia 2.37 Indonesia 1.87, Morocco 1.85, Turkey 1.60, Iraq 1.53 and Pakistan at 1.39. So with all of the last bunch of those, Indonesia, Morocco, Turkey, Iraq, Pakistan at a little over 1% and this being the top 15 out of a total of 222 countries, obviously there's a huge, I mean there's a massive spread, but all the other countries are just minuscule populations. But Brazil number one, India number two, USA number three, and we've got just shy of 10%. So I'm going to share one more piece. From their extensive research, they wrote readers familiar with DDoS might be curious and they have a quote. For such a huge botnet, what level has its attack capability actually reached? Okay, so they said although we cannot directly measure it, through observations of two large scale ddos events and a horizontal comparison with Isuru, we believe Kim Wolf's attack capability is close to 30 terabits per second first, and they have, they have three factoids, they said first, a well known cloud service provider observed a 2.3 billion packets per second and remember, each packet is made out of many more bits. So 2.3 billion packets per second attack at 2209 Zulu on November 23rd with 450,000 participating IPS, they said we confirmed Kim Wolf's participation. Second, a well known cloud service provider observed an attack nearing 30 terabits per second and 2.9 gigapackets per second at 09:35 Zulu on December 9. After data comparison, both parties confirmed Kim Wolf's participation. And finally, Cloudflare pointed out its third quarter 2025 DDoS threat report that ISIRU was one of the strongest known botnets currently with a control scale of millions of IoT network devices capable of sustaining terabits per second, level of tax and even peaks approaching 30 terabits per second and more than 10 billion packets per second. So they said, in fact, we believe that behind many attacks observed by Cloudflare attributed to aciru, it may not just be the ISIRU botnet acting alone. Kim Wolf may also be participating or even led by Kim Wolf. These two major botnets propagated through the same infection scripts between September and November, coexisting in the same batch of devices. They actually belong to the same hacker group. Okay, now if 9.58% of Kim Wolf's infections have been seen in the U. S and if there are Conservatively more than 1.8 million operating instances of Kim Wolf, that's more than 172,000 172,000 Android based smart TVs currently infected with Kim Wolf just in the US these guys conclude their very thorough analysis and I've got a link to the original posting because there's a they did they did a complete reverse engineering of this bot, but they wrote this is the majority of the intelligence we currently possess on on the Kim Wolf botnet. Giant botnets originated with Mirai in 2016 with infection targets mainly concentrated on IoT devices like Home broadband routers and cameras. However, in recent years information on multiple million level giant botnets like Bad Box, Big Pansy, Vald and Kim Wolf has been disclosed indicating that some attackers have started to turn their attention to various smart TVs and TV boxes. These devices generally suffer from problems like firmware vulnerabilities, pre installed malicious components, yikes, weak passwords and lack of security update mechanisms making them extremely easy for attackers to control long term and use for large scale cyber attacks. One of our motives for disclosing the Kim Wolf botnet this time is to call on the security community to give due attention to smart TV related devices after attackers gain root privileges on smart TVs, the resulting attacks are not limited to traditional cyberspace Attackers can use controlled terminals to insert tampered, biased or extreme videos in the legal systems of many countries, inserting content without written permission violates the contract between the viewer and the TV program provider and is illegal. This is our second motive for disclosing the Kim Wolfbotn at this time, calling on law enforcement agencies to consider scrutinizing such suspected illegal activities related to smart TVs against the backdrop of overlapping threats. Whether ordinary TV boxes, sales channels, operators or regulatory departments and manufacturers, all must attack attach great importance to the security of TV boxes. Among them, TV box users should especially ensure devices come from reliable sources, use firmware that can be updated in time, avoid setting weak passwords and refuse to install APKs of unknown origin to reduce the risk of being infected and controlled by botnets. And remember social, you know social techniques for for penetrating trust are are going to be high up on the list of what attackers do. They said we sincerely welcome CERTs from all countries to contact us, share intelligence and vision, join hands to combat cybercrime crime and jointly maintain global cyber security. If you are interested in our research or have inside information, feel free to contact us via the X platform. So as I said, I placed a link to their entire analysis, most of which I skipped over because it's way more than what's needed here. But they they provide everything anyone knows to, to understand and identify Kim Wolf. So for anybody who wants to get a very clear look into the guts of the operation of a massively successful state of the art global botnet, you know, these guys have published that and I, I would heed their advice. I can't think of anything more, more useful and significant than, you know, you do not want this operating inside your smart tv. I have the feeling, Leo, that there are, there's a huge population of non mainstream top drawer TV boxes, you know, available.
- [89:48]
Leo Laporte
I don't think These are Apple TVs.
- [89:50]
Steve Gibson
Right. AliExpress and, and who knows where, you know, or you know, also ran things on Amazon where it's just, oh look, I can get a smart TV with Android for you know, $25. It's like woohoo. Yeah. And you also end up with, you know, Kim Wolf pre installed.
- [90:11]
Leo Laporte
Although I doubt most TVs or TV set top boxes have much security.
- [90:16]
Steve Gibson
I mean you're right, I, I, you know, it's, I would agree with you.
- [90:21]
Leo Laporte
Yeah.
- [90:22]
Steve Gibson
Wow. And I would think that, that typically you have to create a password with some horrible on screen keyboard.
- [90:31]
Leo Laporte
Yeah.
- [90:31]
Steve Gibson
People are probably going xxxx in order to just make it easy for themselves. So I would imagine that the passwords on these things are atrocious. Also, I did want to take a mention, as I said at the top of the show, to just sort of tell everybody something I really, I don't think I've said is that I am very pleased with the way this commercial launch of this second version of the GRC's DNS benchmark after a year of work on it has rolled out. It's still in the process of settling down, which is what I expected. We're now at release four. It acquired a couple of new features. I fixed two bugs that has escaped notice until now. Windows 11. Turns out its new smart app Control, which I mentioned last week, did block another person's use of the product. But now we know to ask them just to try again. When they did, they had no trouble. So you know, so far no one's been permanently blocked, but that's going to be probably an annoyance for a while. So we have a new solid commercial offering. I, I, I received a piece of email from someone who said that he'd been listening to the podcast since he was much younger, obviously 20 years younger, and that it was underpriced at 9.95, so. Oh, I appreciated the sentiment. So nice. So thank you. So anyway, I'm really happy with the way it's going. And I've got a couple more ideas for similar sort of inexpensive commercial goodies before I settle down and get to work on Spinrite 7. So that is the game plan. Let's see. Is it time for a break?
- [92:25]
Leo Laporte
Yeah, it's time. It's a good time for a break.
- [92:28]
Steve Gibson
Let's do that. And then we're gonna. We're gonna do some listener feedback. And I've got one long piece that it's gonna be a lot of fun.
- [92:32]
Leo Laporte
Okay, good. There's not much of a break here because it's the end of the year. So we're just gonna say thank you. Happy Holidays. We appreciate your support and your viewership and we hope you keep listening. Security now in 2026, goodness knows things aren't going to get any more secure.
- [92:51]
Steve Gibson
No sign of that. No, no.
- [92:54]
Leo Laporte
On we go with security now, Steve.
- [92:56]
Steve Gibson
Okay, so Jamie said. Hello Steve, Huge fan, very long time listener. Just wanted to give you some quick information that might be helpful to your listeners. A very quick and painless way. Oh, okay. This is about running the DNS benchmark. It's a cool tip though, which has a much wider application. A very quick and painless way to run the DNS benchmark and I would argue and any Windows app on any Linux system is to install Steam. Add a non Steam executable to your library.
- [93:28]
Leo Laporte
I didn't know.
- [93:28]
Steve Gibson
And use Proton.
- [93:31]
Leo Laporte
Yeah, you could do that. I thought it was just the games in the. In the Steam store.
- [93:35]
Steve Gibson
Right. And he says and then use Proton as the compatibility layer. Yeah, he says it takes about 15 seconds and the benchmark runs perfectly. He said. And a couple of episodes you mentioned wanting some more insights into traffic entering and exiting your network. Take a look at the. NET Data plugin for PF Sense. If I have any bead on your interests, you might want to set aside an afternoon to dive into it. It gives you an incredibly deep and insightful look into your traffic. And he finished. Thanks. Thanks for everything you do. Much love to you and Leo. Thanks Jamie. In Las Vegas I took a look at net at the NetData plugin and it looks very interesting. There is a free non subscription. You know it. It lacks a bunch of features that enterprises don't need. It looks like it does everything that I would want and so I will definitely set aside some time to take a look at it. And of course putting it in pfsense in your pfsense you know border router is where it needs to be in order to see have to have visibility into your entire network. There are versions for Windows and Linux, but then it would only be seeing what your own, you know, what, what your own local machine is doing. So anyway, thank you Jamie for the tip. And as for Steam and Proton, I did a little bit of digging and I agree with you, Leo. It turns out to be a terrific suggestion.
- [95:02]
Leo Laporte
I had no idea.
- [95:04]
Steve Gibson
So it, the, the, the path is install Steam on Linux, which is most people have already. Yeah, right. Launch Steam and then go to add a game. And then under Add a game you'll find add a non Steam game.
- [95:21]
Leo Laporte
Okay. He says be a game, it could be any xe.
- [95:25]
Steve Gibson
Right. Then, then select the Windows DNS benchmark xe right click the entry properties and they see he said. And then enable, force the use of a specific compatibility tool and select Proton and then he said click Play and that's it. And it runs. So thank you, Jamie. I've been looking for a simple way to solve the, you know, running GRCs, Windows apps on Linux and Mac because there's been a surprisingly strong interest in that. And I'm not done with Windows apps. So, you know, having a solution that works very easily, that's, you know, super.
- [96:05]
Leo Laporte
Useful, almost certainly will not work on a Mac. It would work on Linux.
- [96:08]
Steve Gibson
Okay.
- [96:09]
Leo Laporte
And Windows because they're both Intel. It's the same problem with games you can't run. You can run many Windows games on Linux, but you can't on Mac unless they're specifically ported to the Mac.
- [96:20]
Steve Gibson
Okay. I do know that we've got the DNS benchmark running on ARM Macs.
- [96:26]
Leo Laporte
Yeah. But not using Steam, using some.
- [96:27]
Steve Gibson
Oh, okay, okay. Gotcha, gotcha. Rick Andrews said. Steve, in this episode you noted, and I guess that was last week, that hundreds of millions of certificates. Oh yeah, well we talked about that. Issued by let's Encrypt represented a huge risk saying that quote, and he quotes me. A billion websites are, are all now dependent upon a single service for their certificates, he said. But many other public CAs, including DigiCert offer Acme based service to automatically obtain a certificate that chains up to one of their routes. In other words, you can use ACME with someone other than let's Encrypt and if more people did that, it would reduce and spread out the risk. I just wanted to clarify that. Signed Rick Andrews. So Rick is absolutely correct. To the best of my knowledge, there are only two providers of domain validation web certificates who offered them at no charge. Okay. Now I actually learned something after these show notes arrived yesterday early afternoon and in the mailbox of someone who has a site devoted to the to Acme protocol development. It turns out Google has a a service that I will have more to say about next week. I just learned about it after the after everything was assembled. But so it's let's Encrypt and Google's is no charge. Also the one that I knew about was one called zero ssl. Unfortunately zero SSL wants to sell you stuff. They show that their free certs are limited to three per customer. What? Okay. They also require you to create an account, verify your email and all that rigmarole which you know, we're all too familiar with. So in my opinion there is only let's encrypt. And now I know about Google who has the fundamentally correct ethics around truly free certificates. But looking at the point that Rick has made another way, it's ob. It's utterly obvious that with the shortening life cycle of TLS web certificates eventually marching down to 47 days, any certificate authority that wishes to remain in business must already have or rapidly be working to bring Acme certificate issuance automation online. You're not going to be in business unless you can, you know, if you like, offer your customers Acme I'm thinking about this caused me to wonder who exactly is paying the bills for less Encrypt because users aren't a service that as we know that's wonderful to have, but it's also quite easy to take it for granted. You know, you set it up, you forget it, the problem is solved. But a number of times we've looked at the scaling, we've talked about this, you know, in the not too distant past that let's Encrypt needs to do, especially as certificate lifetimes continue to shorten because that means that they're going to be like way busier than they were before. So again is let's encrypt really and truly a free lunch? After a bit of a little bit of digging, here's what I found. First of all, as I noted last week, let's Encrypt is operating, is operated by a service of. It is operated by and is a service of the non profit Internet security research group isrg. And the ISRG is funded entirely through charitable contributions, through sponsorships and grants and donations from individuals and corporations that you know are supporting it. And that's 100 of its funding comes from these contributed sources rather than from any user fees. So who Google, the Mozilla Foundation, Cisco, OVH Cloud, Facebook, you know, Meta AWS, Shopify, Nginx, the Internet Society, SiteGround, Automatic Host Point Discourse, Infomaniac and Planet Hoster are the, you know, officially recognized supporters for ISRG and also the ietf. I'm sorry, the EFF and the Ford foundation are also backers as well as the Open Technology Fund. So I had never really stopped to think about the question of who pays for all this because, you know, they're taking on a seriously big responsibility, right? They're talking about a crossing into a billion sites being supplied with certificates and, and a huge volume of re of certificate re issuance on an ongoing rolling basis crossing significant thresholds last year. So I'm not yet using let's and let's Encrypt certs. I'm still happily with digicert because I last purchased certs at a time when they still had a long life. But the decisions that the CA browser forum have made regarding web certificate lifetimes means that I'll be moving to let's Encrypt. And I also plan to be voluntarily supporting let's Encrypt much the way I do Wikipedia, because having access to let's Encrypt is a privilege, I think that should never be taken for granted. They are doing a lot of work for us and maintaining a massive network and I, I hope they, they never go offline. But this brought me to wonder about the stance of a major, actually the Majority Certificate Authority with whom I've proudly hung my hat since I left VeriSign. You know, as a DigiCert customer, I've received their email announcing their support for Acme Certificate Issuance Automation years ago. You know, they're completely up to speed and, and raring and going forward. And I like DigiCert, so I wanted to be certain that I would not be able to remain with them. Like maybe they offer the same thing. Let's Encrypt. Let's Encrypt does. So I went over to DigiCert and used their site search to search for free SSL TLS certificates. The first link that came up was titled the Fraud Problem with Free SSL Certificates. And I thought, oh, this ought to be interesting. What does the company that's never been in the business of issuing free certificates have to say about those who do? So here's digicert's take on why they do not offer free web certificates. They start off, SSL certificates are the de facto standard for online trust today. SSLs are so important to online security that Google gives a ranking boost to sites that secure their content with HTTPs. And I thought, wait, what? You cannot have a site today that's not HTTPs. I mean, Google probably won't even list a site that's not HTTPs. So I, I was already curious like what was going on due to their use of the, of the abbreviation ssl, right, rather than tls, which is completely supplanted. So I went looking for a date on that posting and I found it. That was written 4-6-2015. So this is 10 and a half years ago that they had, you know, the fraud problem with free SSL certificates. I still wanted to know what they thought, especially since their policy hasn't appeared to change. And I wanted to see whether there might be anything there to learn. So they wrote. Savvy Internet users have come to recognize and expect that any website asking for sensitive or personal information to display the universal symbol, the padlock, before typing any sensitive information. In a tech ed survey, users reported that without knowing the identity of the organization conducting business, over 35% would consider entering a. Over 35% would consider entering a credit card number from a site using a plain SSL certificate. So they say, are SSLs less trustworthy than we think? To answer this question, we have to consider the fact that not all SSL certificates are created equal. So then they dis on DV on domain validated certificates saying no identity verification is done. The certificate authority sends an automated challenge email and the site owner clicks on a link to approve the certificate. Information is encrypted, but no assurance is made that the organization should be trusted. Because of the lack of trust and the frequent use for fraudulent purposes. Digicert does not issue cheap domain validated certificates. Now they didn't say free, right? They said cheap. So they then talk about organization validation, extended validation and saying that the problem with free certificates is that you know nothing about the person behind them. So okay, we understand that, right? And I had also forgotten when talking about organizations that offer free ssl, I'd forgotten about Cloudflare. While Cloudflare is not an ACME user, right, because they've got all their whole other own infrastructure. Anyone using Cloudflare's hosting, including their free tier, gets HTTPs connections at no cost. So a website with an, with an SSL certificate or TLS certificate, you know, Gets that benefit just by using Cloudflare. Anyway, they, they go on basically to talk about upselling ev. Unfortunately, we know that EV no longer matters at all because years ago the, you know, when the presence of EV Certs was apparent in the browser Chrome, I Took the time to do it. All the browsers backed off of that. Stop showing you anything special because, you know, the contention was that users were being confused by this, you know, the extra green or whatever it was that the browsers were showing. They were, they were supposed to be trusting that. But bad guys could get bad ev just as they could get, you know, bad OV or dv. So, you know, we know that all of that's changed. No more benefit for extended validation, no more special treatment for code signing of extended validation. Microsoft also backed off of any special treatment there. So, you know, I was, I, I was looking for some contemporary benefit to justify the, you know, an investment in something beyond a domain validation. And I don't find it. I get it that they've got a strong enterprise, they digicert a strong enterprise certificate presence. But you know, they're just not going to be competing in the free certificate business. And we know that let's Encrypt is now about 2/3 of all the certificates on the web. And that's going to be going up as people migrate to look for an automated solution. And they're getting what they need, right? They're getting domain validation, they're getting authentication of their domain and they're getting secure encryption for their visitors. And that's all you need. I also ought to mention also that that the BE ME certificates require extended validation assurance, which surprised me when I had to do it. And it just surprised me again. I needed to get RE EV certified in order to, to re renew my Beamy. Remember, BEME allows me to have a logo in my email and I went through all, all of that back when I was bringing GRC's email system up to speed. Sue, my office manager first needed to make an appointment in order to be present at our official corporate phone number which is published in some directory. There are several that they use. Dun and Bradstreet is one, for example. So, so that you are a known business entity that it turns out that appointments were booking four days out at that point, so we had to wait for that. Once that was done, I needed to engage in another video conference similar to the previous one. Remember that I first had to send DigiCert a high resolution photo of my driver's license. Then in front of a camera, I followed instructions to look into the camera, then hold the same driver's license up next to my face, move it around, pass my other hand between my face and the driver's license that the very nice and patient young woman who was on the other end of the phone call who this time had her camera on. She explained that the hand waving was to prevent any sort of green screen from being used in order to spoof this validation. So I, you know, and finally after a lot of jumping through hoops my organization was re qualified for extended validation. So you know, it is a huge annoyance which I am glad I will probably no longer do again. There's no point for having EV certificates, there's no point for having EV code signing. All of that is sort of drained out of the system. And I'm hoping that when I when this next b the next this a year from now, when this be me certificate expires or whenever my EV qualification expires with Digicert that I'm just going to go without it. By then I hope that GRC will have established itself as a well known enough email provider that I can just go BB free. And I mean I understand the motivation behind it. I get it that the industry wants the use of BIMI to actually mean something but having it on every single piece of GRC's email from the start, which I did, did not apparently earn GRC any you know, useful get out of jail free card. I still needed to battle the spam gods and and establish GRC separately. So anyway, returning to Rick's original point where he wrote but Many other public CAs including DigiCert all offer ACME based service to automatically obtain a certificate that chains up to one of their routes. Again, absolutely right. As I said, you are not in business as a certificate authority moving forward if you don't support certificate automation because it's just it's coming down to three weeks eventually of of of certificate life. But it appears to me that let's encrypt and now I understand Google are in the unique position of having a business model in the case of let's encrypt always free. In the case of Google they're able to give anything they want to away for free because they're Google and they have the network that they have. Those two entities have business models that allow them to offer hassle free automatically issued and reissued TLS web certificates. And frankly I don't see any reason given what the CA browser forum has done for anyone paying for encryption and domain level authentication on the Internet. We've solved this problem. We just need now to keep it online and available and free. So as I said, once I start using let's Encrypt certs I plan to be sending them some money as I do Wikipedia, because I think it's, you know, really a service that is worth something.
- [113:51]
Leo Laporte
Yeah.
- [113:53]
Steve Gibson
So thank you Rick, for a really terrific discussion point. Jason Townsend reminds us of an old saying that sadly less and less true today. He said, back in the 90s in the UK computer magazine, there was a picture of a dog using a computer. I have it in the show notes. Actually, the caption was, the best thing about the Internet is that no one knows that you are really a dog. And he said, sadly, it's getting more and more difficult to be a dog or a kangaroo on the Internet and the days of anonymity are fading fast. And so Jason, of course is referring to the famous New York New Yorker magazine cartoon which was published on July 5, 1993. And it, it shows a dog sitting in front of a computer talking to another one who's, who's standing on the floor looking up at him. And it says, on the Internet nobody knows you're a dog. So I got a kick out of that because as Jason says, that was.
- [114:55]
Leo Laporte
An innocent time, wasn't it? 1990.
- [114:57]
Steve Gibson
It was 1993. Yep. Jeff Root said, steve, Australia has done us a service and that we now have great discussions about an important topic. Your piece was great and got even better when Leo weighed in. But I think your insistence that age verification be privacy protecting is wrongheaded. Assume Apple and Google solve this problem perfectly. Now you go to a website, maybe an online liquor store, and they use the age verification system which reveals the nothing other than you are above a certain age. Now what? Now you are led into a website which is chock full of Google Analytics, Cloudflare analytics, probably fronted by Cloudflare and containing JavaScript code from 30 to 50 other random sites. Security now has long reported on how easily ISPs and data brokers can de anonymize users. So where's the privacy? And how has that effort to produce a 100% private age verification system made it harder for sites and brokers and data brokers to identify you? His point is it hasn't. He said, I would suggest that Leo was right. The answer is not an Apple app. The answer is regulation and enforcement. Data brokers should be tightly regulated. Sites should should be required to collect only such information as is necessary to render their pages or transact their business. What we need is a fully private and anonymous Internet, not yet another app which gives the illusion of privacy. Just my opinion. Keep up the good work. Jeff Root in San Diego, California.
- [116:44]
Leo Laporte
Yeah, you mentioned this on Sunday on Twitter. I remember.
- [116:46]
Steve Gibson
Yeah, yep. I think Jeff makes a very valid and an ironic point about the idea of preserving privacy. Absolutely. While gaining entry to a website where forces that are often far beyond any visitor's control are all about tracking and profiling and doing everything possible to dissolve whatever privacy its users may imagine they have. And as for websites not collecting in any information beyond that which is required to render their pages, the only way I can see that happening would be if the EU were to make that a requirement, much as they did with the cookie disclosure and permission pop ups that they've made the entire world endure. They really did manage to change website behavior. That happened to be for the worse. But I doubt we'll be seeing the the EU enforcing website privacy since remember it was the European advertising and tracking companies that are profiling just as much as companies everywhere else. And they were the ones who caused the EU to kill Google's hopes for the privacy sandbox initiative that would have allowed interest profiling without cookies or tracking. So I have a feeling we're pretty much stuck with the current business model that we have today.
- [118:13]
Leo Laporte
I think you're right.
- [118:15]
Steve Gibson
And Leo, our last break.
- [118:17]
Leo Laporte
Yes.
- [118:17]
Steve Gibson
And then we're gonna look at a naughty little png.
- [118:23]
Leo Laporte
This is a wild story. You're watching Security Now. All the stories are wild in Security now every Tuesday. I hope you'll join us. We're gonna take a break next week. As I mentioned, it's our Best of Episode, a 2009 episode about vitamin D. After that, we come back to work on January 6th and every Tuesday thereafter right about right after Mac break weekly. So that's about 1:30 Pacific, 4:30 Eastern, 23rd, 21:30 UTC. You can watch us do the show live if you're in the club. In the club. Twit Discord. Everybody can watch though, if they want. If they want to watch the live version on YouTube, Twitch, X.com, facebook, LinkedIn and Kik. You can chat with us too. I'm watching the chats from all of the above. This show, I think more than any other show we do, I think it's the largest live audience. I might be wrong, but I feel like this is the biggest live audience of the week. So welcome to you all. You don't have to watch live, of course. We have on demand versions of this show at our website, TWIT TV sn. Steve's got it at his website. Actually, Steve has some unique versions. A 16 kilobit audio version, 120 or sorry, 64 kilobit audio version. He has the show Notes, which we refer to often, which you can download there. And he also has a transcript written by an actual human being, Elaine Ferris. She does a great job. So all that's@grc.com while you're there, you can sign up for Steve's email whitelist so that you can send him email grc.com email and there are two check.
- [120:00]
Steve Gibson
Feedback from our listeners.
- [120:01]
Leo Laporte
Oh, good. I bet. Yeah, it's a great way to get feedback. I think he also has forums that are very active, so you can go there. There's. There's really a lot of ways to interact with the show. I hope you will, and I hope you will listen on a regular basis. If you can't listen live, download a copy. You can also just do it in your favorite podcast client. Subscribe, Steve.
- [120:22]
Steve Gibson
And if we do have archives available for everything else, you end up, you know, thinking, yeah, what am I, well, what am I going to listen to today then?
- [120:32]
Leo Laporte
That's a good idea. Kind of get you. I know there are people who get extended education credits and so forth by listening to Security Now. It's a really, it's educational show. It's a good use of your time.
- [120:43]
Steve Gibson
Yeah, it, it does qualify for the, the ongoing security credits. And we. Somewhere we have a semi truck driver who is consuming 70 hours a week of this podcast and catching up rather quickly.
- [120:58]
Leo Laporte
We're kind of watching along with amazement as he, as he listens to the show. Steve, let's go. Okay with the show. I want to know about this ping thing.
- [121:09]
Steve Gibson
The KOI is the name of the company K O I, who fashioned themselves an Endpoint Security company. Last Tuesday they published a nice descriptive piece that I just, I was well written, I liked it, I wanted to share it. About their recent discovery, which as I said it immediately caught my eye and imagination as I imagine it might catch our listeners under the headline, their headline, inside Ghost poster How a PNG, you know, ping icon infected 50,000 Firefox users. They explained every extension, meaning a browser extension, Firefox extension. In this case, every extension has a logo, a tiny image sitting in your toolbar, a visual shorthand for trust. You glance at it, you recognize it, and you move on. You probably never think about what's actually inside that file. The authors of Ghost Poster are counting on that. Our Risk Engine wings flagged anomalous behavior in a Firefox extension called Free VPN Forever. And I'll just interrupt to say it should come as no surprise that malicious Free VPN offerings are beginning to crawl out of the Woodwork as the uk, the eu, Australia and various US states such as Texas and Mississippi begin limiting who can access their services based on their location. So beware, you know the free VPN Coy continues writing the Firefox extension was reading its own logo file standard behavior, but then doing something unusual with the raw bytes. When we dug into the code, we found a hidden extraction routine. The extension wasn't just displaying the logo, it was searching through the logo's image data, looking for a marker that shouldn't be there. There's actually three equal signs, they said, inside that friendly little planet icon. Past where the image data ends. We found malware embedded in the bytes of the PNG image file itself, waiting to be extracted and executed. Free VPN Forever has been on the Firefox Add Ons marketplace since September of 2025, with over 16,000 downloads and installations. It's still live as of this writing. And it's not alone. The campaign spans 17 Firefox extensions, with over 50,000 combined downloads and installations. Extensions promising free VPNs, translation tools, weather forecasts, ad blocking, the usual lures. What they actually deliver is a multi stage malware payload that monitors everything you browse, strips away your browser's security protections, and opens a back door for remote code execution. Okay, so clearly since PNG images are defined to contain non executable image data, the authors of this malware must have assumed, apparently correctly, that the files of type PNG would not be closely scrutinized by anti malware scanners and would be allowed to pass. And you're not expected to understand what's in an image, especially a png, because they are encrypted bitmaps, which makes them very efficient. They are they they don't blur the way JPEG does, so they they you wouldn't expect to understand what's there. Coy continues writing the Free VPN Forever load when when Free VPN Forever loads, it fetches its own logo file. Logo PNG standard behavior for any extension. But then something unusual happens. The code starts searching through the raw bytes of the image, looking for a marker. Three equal signs, nothing. After that marker is image Data. It's malicious JavaScript hidden in plain sight. The technique is called steganography, hiding information inside something that looks completely innocent. Security scanners examining the extension's JavaScript files won't find the payload code. Reviewers won't see it. The logo displays normally in your toolbar. Nothing looks wrong. But every time the extension loads, it extracts the hidden code and runs it. The code pulled from the logo isn't actual malware. It's a loader, a small program whose only job is to fetch the real payload from a remote server. The loader reaches out to www.liveupdt.com. if that fails, it tries the backup www.dealctr. like deal counter.com the request includes a signature parameter so the attackers can track which infected extensions are checking in. But the loader doesn't phone home every time it waits 48 hours between check ins, and even then it only actually fetches the payload to 10% of the time randomly. The other 90% it just doesn't. Random chance this is deliberate. Security researchers monitoring network traffic might watch an infected extension for hours and see nothing that looks suspicious. The malware is patient. It knows that inconsistent behavior is much harder to catch than consistent behavior. When the payload does arrive from the command and control server, it's not readable. JavaScript it's been transformed using a custom encoding scheme. The decoding algorithm is almost playful in its simplicity. Swap all lowercase characters to uppercase and vice versa. Swap all eights with nines and vice versa. Base 64 decode the result. The decoded payload gets XOR encrypted using a key derived from the extension's unique runtime id, then stored in local browser storage. Persistence achieved. And now it gets interesting. The final payload pulled from the command and control server, decoded and executed, is a comprehensive toolkit for monetizing your browser without your knowledge. Using affiliate link hijacking, the malware watches for visits to major e commerce platforms. When you click an affiliate link on Taobao or JD.com, the extension intercepts it. The original affiliate, whoever was supposed to earn a commission from your purchase gets nothing. The malware operators get paid instead. It's invisible to the user. You still end up on the product page. You still make your purchase. The only difference is who gets the commission. And then there's the tracking injection. The malware injects Google Analytics tracking into every page you visit. Tracking ID is UA 601-449-338. It collects your extension, installation date, how many days you've been infected, which merchant networks you visit, and a unique identifier tied to your browser. Hidden HTML div elements that get injected into pages with with IDs like X wiggle bit and XD way show kissed. These elements contain tracking attributes, installation days, signatures, merchant network data that can read that can be read by scripts on the page or by the extension itself. You're being profiled and you'd never know it. Then there's the security header stripping. The malware actively removes security headers from HTTP responses. Content Security policy Gone X frame options Gone these headers exist to protect you from click jacking and cross site scripting attacks. The extension strips them from every response on every site you visit. Your browser's security model is quietly dismantled. And then there's the captcha bypass. The malware includes multiple methods for bypassing captcha challenges. One method creates an invisible overlay that simulates user interaction. Another loads an external captcha solver from ref euficn.gov GitHub IO a third checks if you're logged into Baidu and uses your account status as verification. Why would malware need to bypass CAPTCHAs? Because some of its operations, like the hidden iframe injections, trigger bot detection. The malware needs to be able to prove it's human to keep operating. What was about? What was. What was that about? Hidden iframe injection the extension injects invisible iframes into pages, loading URLs from attacker controlled servers. These iframes enable ad fraud, click fraud, and additional tracking. They're created, used, and deleted, leaving no visible trace. Referrer policy gets manipulated to hide the traffic source. The iframes disappear after 15 seconds. Forensic analysis would need to catch them even in the act. What makes Ghost Poster effective isn't any single technique. It's how they're layered together. Steganography hides the initial payload where scanners won't look. Stage uploading means the actual malware never exists in a file it's fetched at runtime. Custom per browser encoding defeats pattern matching. Random delays and probability checks make behavior inconsistent and harder to observe. Time delays prevent the malware from activating until six plus days after its installation, long after most security researchers and reviews would have concluded. XOR encryption protects stored data from casual inspection. Each layer isn't particularly sophisticated on its own. Combined, they create something genuinely difficult to detect. Free VPN forever is not alone. We found 16 other Firefox extensions communicating with the same command and control infrastructure. Liveupdt.com and dealcounter.com different extensions, different lures, same backend. Some use the PNG steganography technique. Others download JavaScript directly and inject it into every page you visit. Others use hidden eval calls with the command and control domains encoded using custom ciphers. Same attacker, same servers, different delivery mechanisms. This looks like experimentation, testing which approach evades detection the longest, which gets the most installs, which generates the most revenue Collectively, these extensions have been installed over 50,000 times. And ghost Poster isn't the first time we've seen free VPN extensions turning malicious. It's becoming a pattern. Earlier this week we exposed Urban VP Proxy, a Google Featured extension with 8 million users that was secretly harvesting AI conversations from ChatGPT, Claude and Gemini and selling them to data brokers. Before that, FreeVPN1, another featured verified extension with 100,000 plus installs was silently capturing screenshots of everything users browsed, including bank accounts, private photos and sensitive documents. Free VPNs promise privacy, but nothing in life comes free. Again and again they deliver surveillance instead. What makes Ghost Poster dangerous isn't any single technique. It's the access. These extensions strip your browser's security headers on every site you visit. They inject code into every page you view. They maintain a persistent connection to attacker controlled servers waiting for instructions. The payload can be updated at any time. What runs in your browser tomorrow is entirely up to them. The steganography is clever. The layered evasion techniques show operational maturity. But the real threat is simpler. 50,000 users installed extensions that gave attackers full control over their browsers. And these extensions are still live on the Firefox Add ons marketplace. So to give everyone an idea of these sort of extensions, they list the names of the actual ones they found. We've got free VPN forever Screenshot saved Easy weather Best Forecast CRX Mouse Gesture Cache Fast Site Loader Free MP3 Downloader Google Translate Right Clicks Google Trade Dr. ESP Worldwide VPN Dark Reader for FF Translator GBBD I like Weather Google Translate Pro Extension Lib Light Liber tv watch free videos, add stop and rightclick Google Translate. You know, needless to say, when you know what this stuff is doing, nobody wants this sort of crap lurking inside their browser. And tremendously reducing its native security guarantees by removing all incoming website security measures which prevent all manner of other hijinks. We've seen that movie. It doesn't end well. There's not really anything anyone can do. You know these things snuck past the observers trying to keep the store clean. Google has featured VPNs with 8 plus million downloads that are malicious. The original admonishment that we gave is still operative and still applies. Don't just rummage around adding every random browser add on that presents itself and looks like it might be fun. Do everything you can to limit your usage to those only that you really need. Remove any that you downloaded thinking you would use it and then haven't. Get rid of it just, you know, practice, you know, safe hygiene of. Of. Of Internet use with your browser.
- [137:12]
Leo Laporte
The.
- [137:13]
Steve Gibson
As we have said, the browser is the window to the Internet. You know, keeping it secure is really important. These things destroy that.
- [137:20]
Leo Laporte
It's just a natural attack vector, too. I mean, that's the place you want to be if you're going to attack somebody's machine so much that they would. Yeah, yeah. That's just. It's really interesting to see how clever and determined these guys are.
- [137:37]
Steve Gibson
Yeah.
- [137:37]
Leo Laporte
And all the little ins and outs, the funny names that give their functions and.
- [137:42]
Steve Gibson
Yeah, we're, you know, we're just not equipped to. To deal with due to the nature of security and the human factor on, on our end, that the amount of effort that North Koreans are willing to expend to penetrate, they got just to do. Yes, exactly.
- [138:04]
Leo Laporte
It's amazing. It really is. Yeah. They're much more devoted attacking us than we are defending ourselves.
- [138:10]
Steve Gibson
And I mean, and. And a lesson we learn about, you know, humanity is somebody who really wants something really bad, who just keeps pushing for it. Often gets it often. Yeah, yeah. Other people are like, well, yeah, okay, fine, okay, you know, that's what you want.
- [138:27]
Leo Laporte
I don't have the energy, you know. Well, I know you have the energy. You're like the Energizer Bunny. All year long you've been crying, cranking them out. We thought. You thought you'd be done last year at 9.99, but no, a whole year has come and gone and you've delivered us some wonderful shows. Thank you, Steve Gibson.
- [138:45]
Steve Gibson
That's my pleasure. I like doing it. I like having listeners. I like the feedback. I like writing code, and I appreciate the support of people buying my stuff. It keeps it going.
- [138:55]
Leo Laporte
You're living in heaven right now.
- [138:58]
Steve Gibson
Couldn't be any better.
- [138:59]
Leo Laporte
GRC.com's the place. That's where you get a copy of Spinrite, the world's best mass storage, maintenance and recovery utility. His brand new tool, the DNS Benchmark Pro. Only $10, $9.95.
- [139:10]
Steve Gibson
Pardon me.
- [139:11]
Leo Laporte
Save a nickel. Both of those are available there right now. He puts a lot of thought into everything he writes. It's always good stuff. Just browse around@grc.com you'll find lots of goodies. We'll be back next week with our best of a 2009 classic, the story of Vitamin D. Kind of a little off the beaten path, but I thought it'd be fun to bring that back. As cold and flu season encroaches upon.
- [139:38]
Steve Gibson
Us, a different way of having something that's good for your health, not security, but immune system support.
- [139:44]
Leo Laporte
Corporeal security is important, too. You've got to do that, too. Thank you, everybody, for joining us. Have a wonderful holiday. If we don't see you again, happy New Year. We will see you in two weeks on January 6th for the next Security now in 2026.
- [140:03]
Steve Gibson
Wow.
- [140:03]
Leo Laporte
Have a great, great couple of weeks.
- [140:06]
Steve Gibson
Have a great holidays and see everybody next year. Bye.