← All TWiT.tv Shows (Audio)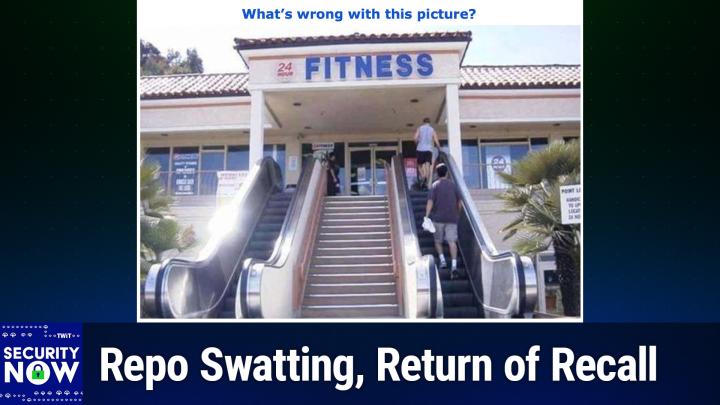
All TWiT.tv Shows (Audio)
Security Now 1002: Disconnected Experiences
02:32:04
'Nearest Neighbor' Attack, Repo Swatting, the Return of Recall
Loading summary
Transcript277 lines
- [00:00]
Leo Laporte
It's time for Security Now. Steve Gibson is here. He's in love with these Chinese cranes that they use at container ports. But he says there's a problem. Apparently there's a Chinese back door. Oh, no. We'll also talk about the nearest neighbor attack and a warning about a new feature of Microsoft Windows they call Connected Experiences. Steve says it's a recipe for disaster. All of that and more coming up next on Security Now.
- [00:32]
Steve Gibson
Podcasts you love from people you trust.
- [00:36]
Leo Laporte
This is Twit. This is Security now with Steve Gibson. Episode 1002, recorded Tuesday, November 26, 2024. Disconnected experiences. It's Time for Security now. The show where we talk about your security, your privacy, how the Internet works, how computers work, a little bit of sci fi thrown in, maybe some vitamin D. And it's all because of this guy, the man in charge, our very own Steve Gibson. Hi, Steve.
- [01:10]
Steve Gibson
Hey, Leo. You know when you're saying security now.
- [01:14]
Leo Laporte
You'Re leaning back and it gives you.
- [01:16]
Steve Gibson
Kind of a nice. Like the mic. That's right. A little Doppler shift effect there.
- [01:21]
Leo Laporte
I learned that from Adele. It's so funny because I realize now we'd had a photo meetup in New York City.
- [01:29]
Steve Gibson
Yeah. A couple months ago.
- [01:30]
Leo Laporte
A couple months ago September. And I would look back at the pictures and there were a bunch of people doing the Live long and Prosper sign. And I realized that has become not just the Security now thing, but everybody now it's our twin hand sign.
- [01:45]
Steve Gibson
That's very cool.
- [01:47]
Leo Laporte
Thanks to you.
- [01:48]
Steve Gibson
That's good.
- [01:48]
Leo Laporte
What's going on?
- [01:49]
Steve Gibson
No, not everybody could do it.
- [01:51]
Leo Laporte
No, I know, I know. Didn't they have to tape Leonard Nimoy's fingers because he, in fact, could not do it.
- [01:58]
Steve Gibson
Interesting.
- [01:58]
Leo Laporte
And they had it. I believe there's an anecdote of how do they. When they first. He was the guy who came up with it, but he couldn't do it. Maybe that. Maybe it was somebody else who couldn't do it. But I. But, yeah. Anyway, I'll go find that anecdote.
- [02:13]
Steve Gibson
As I was saying to you, I was saying to you before we began recording, every time I look at these four digit episode numbers, I'm thinking, whoa. I mean, that really does seem like an accomplishment.
- [02:26]
Leo Laporte
It is, yeah. You should be very proud. Yeah.
- [02:28]
Steve Gibson
Well, we're at 102. 102, 1002.
- [02:33]
Leo Laporte
See, there's the problem right there. Even his brain can only do three digits.
- [02:37]
Steve Gibson
We're at 1002 and the software didn't collapse. I did spend some time updating GRC systems so that it also would not freak out when four digits were presented to it and that all that experience was smooth. Emailing continues to go well. It was 13,219 subscribers received the show notes, the picture of the week, various links and things yesterday evening. So that's turned out great and we're going to have lots of feedback because there was also lots of news. But my discussion of what I titled disconnected experiences wasn't half of the podcast, as some of our main topics have been in the past. I have something like 3,800 pieces of feedback from our listeners, so I have plenty to choose from. I feel a little bit badly that I'm getting so much feedback that I can't even begin to put a dent in it. But thank you everybody for sending me your thoughts. And as I said, the quality of the feedback has a very different flavor since we were able to switch to email and people didn't have to try to squeeze something into 280 characters. So big benefit. We're going to talk about at the end of this something that Microsoft calls their connected experience, which is an interesting turn of phrase. We'll understand what it is, why they sort of slipped it in under the covers, and why it may not be what everyone wants and if so how you can turn it off, thus disconnecting your experience from Microsoft. And it's not what it sounds like either because I mean it's not at all that. But we're first going to talk about something known actually, and this was probably the most sent to me topic for the show and it happens that it's what I had chosen myself already by the time I saw that the nearest neighbor attack. And wow, it just sort of goes to show you how clever bad guys can be whether we like it or not. We also have let's Encrypt Just turning 10. We're going to take a little bit of a retrospective look at the changes that it has wrought. Also now the Coast Guard is worried about Chinese built ship to shore cranes. Turns out 80% of the big cranes that we use for offloading containers are made by China and what could possibly go wrong there? Also Pakistan becomes the first country to block Blue sky going to talk about that. There's also a new way to get git repos swatted and removed from their repositories. I know. Again, it just just incredible how clever bad guys can be. Who's to blame for Palo Alto Network's serious new zero day vulnerabilities? And if you have Any of six specific older D link VPN routers. The advice would be to unplug them immediately. We'll see why. Turns out that speaking of VPNs, they are against Sharia law, so says some legislators in Pakistan. So we'll touch on that. Also we have the return of Windows recall. What are we learning from that? And how many of today's systems remain vulnerable to last year's most popular exploits. So after sharing then a bunch of feedback from our listeners, we're going to talk about disconnecting your experiences from Microsoft. So I think another interesting podcast for our pre Thanksgiving listeners.
- [06:31]
Leo Laporte
Yeah, Shatner. According to pac, Patrick Dillahandy was unable to do the salute. So he would have to put his fingers in position and then he would hold it up or he would hold it up behind.
- [06:46]
Steve Gibson
And did he actually do it often? Obviously Spock was the original. Was that it was a Vulcan hand sign.
- [06:53]
Leo Laporte
It was a Jewish hand sign that Leonard Neiman had seen in his childhood. That meant roughly it was a Jewish benediction and it wasn't in the script. But Nimoy thought, well, you know. And he asked the director, is it okay if I do this? And the director said yeah, that'll work real well. And it became of course a trademark. Shatner joked that it took years of diligent practice and self denial for him when he was on Conan to be able to do it because he could not do the live long and there.
- [07:28]
Steve Gibson
Are people who can't. The best man at my wedding was unable to do it.
- [07:33]
Leo Laporte
Wait a minute. You, you had this at your wedding?
- [07:37]
Steve Gibson
Of course.
- [07:40]
Leo Laporte
At what point did you do live long and prosper? Was this. Instead of kissing the bride, what did you.
- [07:44]
Steve Gibson
Gary got up for the best Mads toast and said to, you know, was holding the microphone and said now Gibson made me promise that I would not do anything to embarrass him. Oh. So I'm just going to say. And then he held his hand up and said live long and that's beautiful. But he had two. He had two orthodonture braces bands around his fingers because he also was unable to do that.
- [08:13]
Leo Laporte
I can't do it with my left hand. I can only do it with the.
- [08:15]
Steve Gibson
Right hand without some assistance.
- [08:17]
Leo Laporte
Yeah, well you'd expect you didn't like the sound effects, but I will play one more. Live long and prosper and continue on now with the show.
- [08:25]
Steve Gibson
Thanked Gary for keeping his toast quite quick and to the point.
- [08:28]
Leo Laporte
That's a perfect toast. It says it all.
- [08:31]
Steve Gibson
Yes, yes.
- [08:32]
Leo Laporte
All right. We're going to get to the picture of the week in just a moment, but first a word from our first sponsor, Mr. Gibson. Today it's Experts Exchange. You listen to this show because you've got a real live expert who talks about the things you care about the most on the show. Well, imagine having that kind of expertise available to you anytime, day or night. That's what Experts Exchange has been doing for, I think it's almost 20 years now. I know I started using them early on when I needed an answer and I couldn't find it anywhere else. Network Experts Exchange is a network of trustworthy and talented tech professionals. You can go to them to get industry insights, to get advice. And it's not just advice from some stranger on the street. It's from somebody who's actually using the products in your stack. That sure beats paying for expensive enterprise level tech support as the tech community. For people tired of the AI sellout, Experts Exchange is ready to help carry the fight for the future of human intelligence. Now you might say, well, there's got to be a future. But remember, AI is starting to creep into all of these, you know, intelligence things. There's these question and answer sites. Worse, it's using the answers humans give on these sites, scraping them and then adding it to their own LLMs body of knowledge. Not at Experts Exchange. Experts Exchange is about human intelligence. Experts Exchange gives you access to professionals in over 400 different fields. We're talking coding, Microsoft Azure, AWS, DevOps and more. And unlike some of these other places, there's no snark. Duplicate questions are encouraged. There are no dumb questions. You don't get the snarky, oh well, I wouldn't do it that way kind of an answer. You get real help because the contributors are serious tech enthusiasts who love graciously answering all questions. In fact, I would go even a step further to say these are experts who believe that the best thing that can happen, the best way to celebrate your expertise, is to graciously share it with others, to help other people, to pay it forward. That's what Experts Exchange is all about. So let's talk a little bit about it. One member said, I've never had ChatGPT stop and ask me a question before, but that happens on EE all the time. It's a dialogue, it's a conversation. Experts Exchange is proudly committed to fostering a community where human collaboration is fundamental. Their Experts Directory is full of experts to help you find what you need. One of them is listening right now. Rodney. Hello, Rodney Barnhart. He's a VMware expert and a Security now fan. There are people like Edward von Biljohn. Maybe you've seen Edward's YouTube videos. He's a Microsoft MVP and an ethical hacker who really knows his stuff. He's on Experts Exchange plus Cisco design professionals, executive IT directors. Yes, you can get management questions answered and a lot more. But here's the most important thing. Other platforms betray their contributors by selling the content on the platform to train AI models. LinkedIn does it. They just announced that Reddit does it. So many sites do it. But you know what? At Experts Exchange, your privacy is not for sale. They stand against the betrayals of contributors worldwide. And they have never and will never sell your data, your content, your likeness. They block and strictly prohibit AI companies from scraping content from their sites to train their LLMs. And the moderators on Experts Exchange strictly forbid the direct use of LLM content in their threads. Really, it's humans talking to humans. And that's the best kind of expertise, the best kind of conversation. Experts deserve a place where they can confidently share their knowledge without worrying about some company stealing it. To increase shareholder value, humanity deserves a safe haven from AI. And you, you deserve answers, real answers, useful answers to your questions. Now, they are so confident you're going to appreciate Experts Exchange and love it and get value at it, they're offering you 90 days free. No credit card required, just three months, free to try it out. So at the very least, I want you to go to e-e.com Twitter sign up. You don't have to give them a credit card. Try it for three months. If you don't get anything out of it, no harm, no foul. But I have a feeling you're going to really appreciate the community that Experts Exchange has built. Really amazing e-e.com TWIT the tech Q and A for people tired of the AI sellout. Real humans with real answers to real questions. Thank you, Experts Exchange, for supporting this real human Steve Gibson in his ever, never ending quest to make the world a safer place. All right, I have the picture of the week. Shall I look at it? Yeah, I'm going to scroll up here.
- [13:30]
Steve Gibson
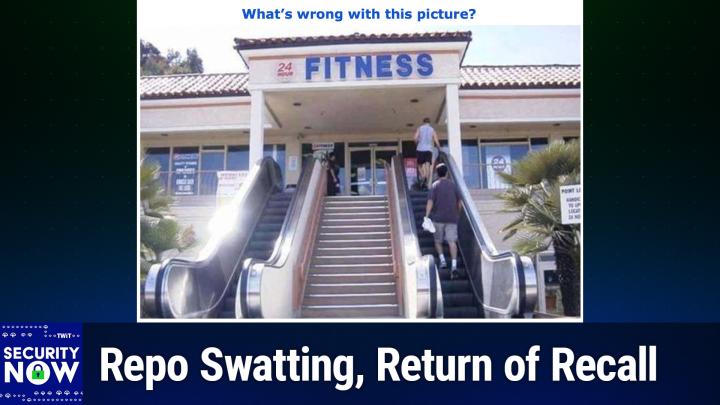
I gave this the caption. What's wrong with this picture?
- [13:36]
Leo Laporte
Oh, I love it.
- [13:37]
Steve Gibson
I do. Okay, so for those who aren't seeing it, we have the entry to a facility where there's a big staircase sort of front and center in the middle. And you can imagine the parking lot is on a lower level. So these stairs are leading up to the entrance to this facility. And to make things easier for the people who wish to come and go at the extremes, the far left and the far right of the staircase are escalators. One, you know, an up escalator and the other the down escalator, which would all be fine. But the sort of. The non sequitur of this whole thing is that the facility is 24 Hour Fitness and nobody's on the stairs and the people are taking the escalators.
- [14:31]
Leo Laporte
I have to go on a StairMaster. I can't just climb stairs.
- [14:35]
Steve Gibson
So. And of course, the show notes went out yesterday evening. And so I've already had feedback from saying, how do you know they're not going up the down escalator, which is actually giving them extra exercise rather than if the stairs were fixed. And there is that. Or what about for people who are there for physical therapy, you know, pt. And so they're not able to climb the stairs. You know, they need to be gentle on the. I saw. Well, yes, of course. Thank you very much. We have to be accessible those alternative possibilities. Anyway, I always. We. I think we showed this once before. I know I've seen it before and I just always get a kick out of just sort of the like, okay, we're. We're going the 24 Hour Fitness, but we're not ready to start working out just yet. We're going to take the escalator up rather than taking the stairs.
- [15:26]
Leo Laporte
Well, that's the equivalent of searching for the closest parking space too, right? Why walk?
- [15:30]
Steve Gibson
Yes. In fact. Yes. Somebody El also wrote to me using exactly that analogy. How many times, in fact, at. At his gym, he's seen people circling, waiting to get a close parking place rather than walking from.
- [15:45]
Leo Laporte
There's exercise and there's just. Then there's just work, you know.
- [15:49]
Steve Gibson
Okay, so. Wow. Last Friday on the 22nd, the security firm Velocity published the details of a somewhat astonishing and successful attack. Being several years old, predating Russia's invasion of Ukraine, this story is not about a threat any of us will ever face, at least almost certainly not. But I wanted to share it since it presents a perfect example of my porosity theory of security, where the security of today's systems is best viewed as being porous to varying degrees. I like this model of a porous system, which I think fits best, because while the amount of effort an attacker may need to exert to obtain access to any specific system may vary, most systems. And look at systems in the broadest sense, most systems can ultimately be breached by a sufficiently motivated and determined attacker. Okay. Now that might mean, you know, arranging to install a subverted employee into the organization playing the long game, or it might mean subjecting employees to phishing attacks of increasing complexity until you finally make it happen. The point is, our systems are not infinitely secure. They're kind of secure where it kind of varies. So the term absolute security is more of a concept than a reality today. Okay, so here's how Valexity opened their disclosure of this astonishing attack, which they're now able to talk about. They wrote in early February of 2022, notably just ahead of the Russian invasion of Ukraine. And that ends up being significant, as we'll see. Velexity made a discovery that led to one of the most fascinating and complex incident investigations we'd ever worked. The investigation began when an alert from a customer detection signature Velexity had deployed at a customer site. And they said, we'll refer to them as Organization A because they're still going to be anonymous even today, indicated a threat actor had compromised a server on that customer's network, they said. While Valexity quickly investigated the threat activity, more questions were raised than answers due to a very motivated and skilled advanced persistent threat APT actor who was using a novel attack vector Velexity had not previously encountered. At the end of the investigation, Valexity would tie the breach to a Russian threat actor it tracks as Gruesome Larch, publicly known as and by many names. One is best known. I like Apt 28. There's also Forest, Blizzard, Sofasi, Fancy Bear, and among other names, in other words, the Russians. They said Velexity further determined the that Gruesome Larch was actively targeting organization A in order to collect data from individuals with expertise on and projects actively involving Ukraine. Okay, so what did Flexity's investigation uncover? Strange as it might at first seem, despite being thousands of miles away in Russia, this well known APT28 group of Russian state sponsored actors breached an unnamed US company, this organization A, by gaining access through its enterprise WiFi network. But wait, we're thousands of miles away in Russia. How's that possible? If I told you that the attack had been dubbed the nearest neighbor attack, you'd start to get the idea. That's right. APT28 pivoted to their ultimate target after first compromising an organization in a nearby building that was in WI fi range of their target. APT28 has this level of expertise. They're part of Russia's military unit 26165 in the General Staff Main Intelligence Directorate, the GRU. And they're known to have been conducting offensive cyber operations dating as far back as 2004. So for the past 20 years, APT28 initially obtained the credentials to the target's enterprise WI FI network through password spraying attacks targeting a victim's public facing service. But the presence of multifactor authentication prevented the use of those credentials over the public web. So they couldn't use the web. Although connecting through the enterprise WI fi did not require multi factor authentication, as Velexity phrased it, being thousands of miles away and an ocean apart from the victim presented a problem. So the hackers got creative and started looking at organizations in buildings nearby that could serve as a pivot to the target wireless network. The idea was to compromise another organization and search its network for a wired accessible device containing a wireless adapter. So a dual home, both wired and wireless. Such a device, whether it be a laptop, a router or an access point, would theoretically allow the hackers to use its wireless adapter to connect to the targets. Organization A, the targeted organization's enterprise WiFi. Flexity wrote this. They said Flexity now determined the attacker was connecting to the network via wireless credentials they had brute forced from an Internet facing service. However, it was not clear where the attacker was physically that allowed them to connect to the enterprise WI fi to begin with. Further analysis of data available from Organization A's wireless controller showed which specific wireless access points the attacker was connecting to. After overlaying them on a map, a physical map that had a layout of the building and specific floors, Felixity could see the attacker was connecting to the same three wireless access points that were in a conference room at the far end of the building, near windows along the street. This gave Velexity the first evidence that, as they put it, the call was not coming from inside the building. Could this be an attacker conducting a close access operation from the street outside? Nothing was ruled out, but Velocity was not too far off from discovering the real answer. Okay, so what they discovered was that APT28 had compromised multiple organizations as part of this attack. They daisy chained their connection using valid access credentials. Ultimately, they gained access to a device containing a WiFi radio that was able to connect to those three access points near the windows of the victim's conference room. Then, using a remote desktop connection RDP from an unprivileged account, the threat actor was able to move laterally within the target network to search for systems of interest and to exfiltrate the data which had been their target all along. The attackers generally used living off the Land techniques as they're now referred to, which rely mostly on already present native Windows tools in order to minimize their footprint and thus reduce the chance of being detected. And one of the things that's happened in Windows through the years is the number of already present built in utilities. Things you just don't even realize are there have really expanded. So for attackers who have full knowledge of just how much available utility is in Windows for them to repurpose, there's a lot they're able to use. Even with all their research, Flexity was working from forensic data and was unable to trace the attacks back to the original attackers. Attribution at that point was still impossible, but a Microsoft report just this last April provided them with the missing clues. Flexity saw clear overlap in indicators of compromise, as we call them IOCs, that clearly matched and pointed to the Russian Advanced Persistent Threat Group. Based on details in Microsoft's report, it's very likely that APT28 was able to escalate privileges before running critical payloads by exploiting a zero day vulnerability back in 2022. CVE 202238028 that existed in the Windows Print spooler service. Remember we talked about that a lot a couple years ago within the victims network. So our unsettling takeaway from this is that close access operations as they're known, that typically require proximity to the target, such as from an adjacent parking lot, sometimes is used can also be conducted from great distances by compromising something nearby you know, that makes an otherwise impossible attack possible and has the benefit of eliminating all the risk to the attacker of being physically identified and caught on site. Nobody can get them. The other and this is the most significant takeaway I think for our listeners is that everything should be logged. The mantra should be log everything. It's crucial to appreciate that it is inherently impossible to know which logs will be needed after the fact. And nothing brings an investigation to a grinding halt more quickly than running up against the oh we don't have logs of that. Today's storage is so inexpensive that it's no longer a factor. Logs don't take up much space. They contain so much redundant information and formatting, which is repetitive, that they compress down to nothing. And they serve as a form of time machine that later allow forensics investigators to venture far back into the past to view what happened when and to retrace the previously unseen footsteps of unknown network users. And logs are not only useful for tracking Russians, large corporations cannot be certain about the changing motivations and loyalties of their own employees. So an IT culture of logging and letting it be widely known within the enterprise that everything within an organization is being logged is a bit like planting a sign on the front lawn to let would be burglars know that the premises is being monitored by such and such a company. It could be an ounce of prevention.
- [28:53]
Leo Laporte
It reminds me of the warning that I always get when I do an su due and mistype the administrator password and then it says or give the wrong name and says, you are not allowed to do this. Your presence will be logged. They back in the day they knew this stuff. You know the other lesson though is also important, which is that we are not operating on our own, that we are in a community and our security impacts other people's security. Right? Yeah. This is not just our machine that we're securing or not securing. We could be a vulnerability happening to our neighbor.
- [29:32]
Steve Gibson
Yeah, well, and in fact, you know, oftentimes now you go and look at the available WiFi access points within range.
- [29:42]
Leo Laporte
Oh man.
- [29:43]
Steve Gibson
It's astonishing, really.
- [29:45]
Leo Laporte
Yes. We're living in a community and we all have a responsibility.
- [29:53]
Steve Gibson
It is the case that one WI fi network is able to see another one and if the hackers are good, they can get near you and then use that WI FI link to jump across the air gap. So, wow, the world we live in today. Let's Encrypt has turned 10, Leo. And you and I have been here the entire time.
- [30:19]
Leo Laporte
Yep.
- [30:20]
Steve Gibson
Watching it happen.
- [30:21]
Leo Laporte
You did a show when it first came out, right?
- [30:23]
Steve Gibson
Oh yeah. Last Tuesday was the 10th anniversary of let's Encrypt and its statistics page shows that its certificates are now being used to encrypt the connections of, get this, 500 million domains. Half a billion domains. Wow. And the rate of certificate issuance. I have that chart. And the rate of certificate issuance both in the show notes for anyone who is interested. The rate of certificate issuance tells a story. This shows that the number of certificates issued per day has now touched 6 million. Now that's of course because these certificates have. Are short lived, right? They're 90 days. So that's one of the things that let's Encrypt has been able to do is to reduce certificate life by automating the process. Twenty years ago, when we began this podcast, most websites used unencrypted and unauthenticated HTTP. Those sites which needed to obtain private and confidential information from their users, even if it was only their username and password to log in, would typically switch to an HTTPs connection. Only during the transmission of that information and then would switch back. We later learned the problem with that, because during that that secure negotiation of username and password, the browser would be given a cookie. But then when the browser switched back to HTTP non secured, non encrypted connections, that cookie would be transmitted in the clear, which we had a lot of fun with under the name Fire Sheep, which was a means of very easily capturing that credential from an unsecured WiFi network and immediately impersonating a logged in user. The good news is those days are gone. But as the world began to grow ever more dependent upon the Internet for everything, it became clear that this original trust by default model was not going to take us where we needed to go in the future. The industry needed a future where the privacy provided by encryption could be available to everyone, not just those who were willing to pay to purchase a certificate. Because the trouble was that encryption required certificates, and certificate authorities had made a lucrative business out of verifying the identity of website owners and signing their certificates, which attested to that verification having been performed. And since performing this verification did require significant work, certificates carrying those attestations were not free. The isrg, the Internet Security Research Group, was formed to solve this problem. Two engineers from Mozilla, a guy from the EFF and one from the University of Michigan, incorporated the ISRG and set about solving the problem. The group decided that the inherently expensive and scaling resistant verification of domain ownership could simply be bypassed in favor of reducing the test to anonymous domain control. And if that was done, web and DNS servers would be able to verify the domains they were serving and the entire process of certificate issuance and maintenance could be automated. Thus, the ACME Automated Certificate Management Environment protocol was born. And today, half a billion domains later, by any measure, this has been a huge success thanks to let's Encrypt. Any website that wishes can now have every connection encrypted for privacy for free. Have let's Encrypts free certificates been abused? Of course they have. That's what happens on the Internet when anything is free. Look at email, spam and today's social media. You know it's abuse frenzy. Both are an utter catastrophe because both are free. But this was not the problem let's Encrypt was trying to solve or prevent. Their clearly stated goal was to offer equal opportunity privacy through encryption for all bad guys. And phishing sites were every bit as welcome to have let's Encrypt certificates as anyone else. At least the communications of the people they were scamming would now also be private and encrypted. And that really was all that the ISRG intended to provide. So 10 years and thanks to these guys. You know, as we've seen, we had a pie chart, remember a couple months ago that showed they'd just taken over. Yeah. You know why?
- [36:10]
Leo Laporte
Everybody uses them. Yeah, we did just. Patrick Delahanny has sent me the link. This is our episode almost exactly 10 years ago, November 25, 2014, where you introduced. Let's Encrypt to the world security now. 483. And Grayson Petty, who is very sharp eyed, pointed out that you had at the time three PDPs holding. Still do. What happened to the other one?
- [36:36]
Steve Gibson
Maybe I moved them up. There is one.
- [36:38]
Leo Laporte
Oh, okay. Above the angle of the shot change. That's all, Grayson. No PDPs have died in the making of this program.
- [36:48]
Steve Gibson
Okay, Leo, let's take a break. Then we're going to talk about, oh, the latest concern of stuff coming from China and a little bit of a sticky wicket in this case. And. Oh, Leo, I want one of these cranes. Oh, wait till you see. I have a picture of one.
- [37:05]
Leo Laporte
What would you do with a crane, Steve?
- [37:08]
Steve Gibson
Oh, wait till you see. You just have to have one.
- [37:12]
Leo Laporte
You take your offload, your hard drives or something. I don't know. Well, if you lived in a container, you could use the crane to move your house around every once in a while.
- [37:21]
Steve Gibson
That's true.
- [37:22]
Leo Laporte
Yeah, that would work well. All right, we'll come right back. I want to find out about these hackable cranes. But first, a word from our sponsor, Bit Warden. And if you listen to this show, you know, you know without any question in your mind that you need to have a password manager. Unfortunately, there are lots of places that don't know that maybe your business does not yet have a password manager. Or maybe your friends and family. In fact, this would be a great thing to talk about around the turkey on Thursday. Bitwarden, the only password manager I recommend and trust because it's open source, it is also trusted by thousands of businesses. Yes, they have a business plan. Of course. What Bit Warden does, you know perfectly well, is generate an autofill. Strong, unique logins. You don't have to remember them, so you don't have to make them easy to remember, and that means they're harder to crack. Bit Warden takes care of all of that. But the important word in there is autofill, and I think we don't maybe emphasize this enough. If you're using the Bitwarden extension and you go to a site and you fill in the password. Bitwarden is protecting you in more ways than you might know. For instance, it will not autofill that password on a spoofed site. If you go to TV, it's not going to fill in your twitter.com password, right? Actually, that made a problem for me when it changed its name to x.com, i had to change my password to x.com but that is a great thing. It means autofill only works on the legitimate sites. And autofill is not just for passwords. It's also for credit cards, for identities, it's even for passkeys. And that is really nice to have that in the inline autofill menu so you don't leave the page. And it will also protect you if it's not the page you think it is. Bit Warden is really great for business. It works with all the tools you already use. They continue to expand their integration ecosystem across key platforms to support seamless operations and elevated security. They just, this is so cool. They just integrated with Microsoft's Intune. You know that Intune is their, is their, you know, service to keep your Windows machine safe. Now with Bit Warden in Intune, it enhances device security and user identity management. It enables secure Bitwarden app deployment on any Intune managed endpoint. That's great for the IT department, including desktops and mobile devices. The HR tool rippling simplifies employee onboarding and off boarding by integrating with Bit Warden, which means the IT team can assign or revoke access as employees join or leave. It's built in. Here's another one. Vanta longtime sponsor here. Vanta combines Vanta compliance audit and reporting with secure password management, which helps your organization meet SOC2 and ISO 27001 and other standards. Rapid7 ensures improved threat detection and response by oh, this is so clever. Correlating credential usage with security events. You were talking about logging earlier, Steve. Automatic logging, right? That lets you know, hey, you had a security event and look who was logged in where. This really helps you strengthen your proactive monitoring and your intelligence for enterprise security teams. And it's automatic. But those are just a few of the many, many integrations Bit Warden can do in your business. These integrations increase flexibility to centralize security management across existing technology stacks and employee devices. And it helps you maintain control over sensitive information. I think it's really. We talk about Bitwarden a lot as being a great tool for individuals and it is free Forever for individuals, which is great, it's open source. But it's really important to remember that Bitwarden has a great enterprise story as well. Bitwarden users can seamlessly connect tools for IT management, for compliance, for security, which helps you improve and standardize the deployment of enterprise credential management throughout your organization. It's not just saying to your employees, here, this is our password manager, use it. It's so much more than that. Your business deserves a cost effective solution that can dramatically improve its chances of staying safe online, and that's Bitwarden. It's easy to set it up. They support importing from most password management solutions. So it should just take a few minutes. And of course I emphasize this. I think it's so important. Any crypto tool should be open source so that you or an expert can verify there are no back doors. It does what it says it does. It's using good, strong encryption. It's not using out of date technologies and all of that. Bitwarden is open source. It's as we talked about last week, it's, or maybe it was two weeks ago. It's gpl. It's true open source. It can be inspected by anyone. It's right there on GitHub. And they regularly get audited by third party experts. But even more importantly, they publish the results of those audits without fear of favor. They guarantee they're going to put them online. So you know you're always using a password manager you can trust. I can go on and on. I'm a big fan. As you can tell, I'm maybe a little bit of a Bitwarden nerd. Get started today with Bitwarden's free trial of a teams or enterprise plan. And if you're an individual or you're sitting across the table at Thanksgiving with a member of your family, says, oh no, I don't worry about passwords. I just use my kitty cat's name and my birthday and my mother's maiden name. And I'm so clever about how I smush those together. No one will ever guess that. You need to tell them about Bit Warden. And if they say, well, I don't want to pay for a password manager, you tell them Bitwarden is free for individuals forever. Bitwarden.com TWIT Now I happen to pay $10 a year, $10 a year for the premium plan because I want to support him, but you don't have to. And if, and if Uncle Joe says I don't want to pay for it, you tell Him. Hey, don't worry Joe. It's free. And Leo says it's the best bitwarden.com TWIT we thank him so much for supporting the fine work Steve does to protect you and Uncle Joe on security. Now, Steve.
- [43:38]
Steve Gibson
Okay, so last Wednesday's report in Gov info security was titled Coast Guard warns of continued risks in Chinese port cranes. Oh boy. This becomes an issue actually when it's accompanied by the news. Get this, Leo. 80% of all heavy lift gantry cranes used to load and unload container ships at American ports were manufactured by a single company, ZPMC, a state owned company in China. 80% of these cranes, and I know why. Oh my God, they are just the most lovely things you've ever seen. They're gone.
- [44:25]
Leo Laporte
This is the problem. They're the best in the business, right?
- [44:28]
Steve Gibson
Like the DJI drones, which are the best drones there are.
- [44:32]
Leo Laporte
Right? Right.
- [44:32]
Steve Gibson
Yes. So, okay, the report explains that the US Coast Guard is warning that Chinese made, as they're called, ship to shore STS cranes come with, and this is unspecified, but that said with quote, built in vulnerabilities, unquote, like back doors. Well, yeah, okay. Enabling remote access and control. Consequently, the Coast Guard has begun urging operators across the country to adopt enhanced security protocols.
- [45:09]
Leo Laporte
Okay, are these the cranes you're talking about?
- [45:12]
Steve Gibson
Oh, I've got one in the show notes. Scroll down another page or two. It's just, just the most gorgeous thing you've ever seen. Oh, so that. So in their notice that the Coast Guard wrote, additional measures are necessary to prevent a transportation security incident, unquote. And the Coast Guard cited, quote, threat intelligence related to the PRC's interest in disrupting US critical infrastructure. Now the notice instructs owners and operators of Chinese made STs, you know, shipped to shore cranes to obtain a copy of the official directive from their local Coast Guard officials stating that the materials contain sensitive security information. In other words, we're not telling you what we know in this public notice. Get this. Get the official directive from your local Coast Guard. They'll tell you more. A congressional report published in September warned a Chinese company with a major share of the global market of STS port cranes posed, quote, significant cybersecurity and national security vulnerabilities for the United States. According to the report, the Chinese state owned company ZPMC supplies 80% of all shipped ashore cranes in the US market and has significant involvement in militarizing the South China Sea. Lawmakers warned that the company and its cranes could serve as a Trojan horse, allowing Beijing to exploit and manipulate U.S. maritime equipment and technology at their request. What remains unclear is what measures the Coast Guard could implement to restrict the remote functionality of ship to shore cranes, which are integral to port operations nationwide. Okay, so here we add another example, a new example to the Chinese made DJI drones and Chinese made security cameras, which those in the US have been blithely purchasing and plugging in everywhere for years. Because as you said, Leo, they're the best. The answer to the question of what are we to do about these cranes is the same as for the DJI drones and cameras. I think in theory we could purchase the hardware and independently source the firmware or software for these devices. But nothing prevents firmware buried deeply within the hardware from being similarly compromised. So it's not just flash memory in obvious firmware. So the real truth is in any instance where we've seriously and firmly determined that we cannot trust the supplier of equipment, that equipment cannot be used anywhere. Its physical or cyber compromise might lead to other damage. And imagine if Beijing could do nothing more than cause, and I say nothing more than cause, 80% of all US ship to shore port cranes to self destruct. It would instantly and irreversibly cripple all major U.S. ports. And at the bottom here of page six, I have a picture of this thing. Oh my God, look at that thing. It looks like something out of Star Wars. You know, you definitely don't want to have that thing walking in your direction.
- [49:07]
Leo Laporte
Well, it doesn't walk. It does roll back and forth. One of the things I love about going on cruises, which we do a lot of, is you get to see these ports and you get to see these cranes in operation.
- [49:19]
Steve Gibson
Well, it's beautiful. But then, then to give you a sense of scale, look at the itty bitty size of the standardized containers.
- [49:27]
Leo Laporte
Yeah.
- [49:27]
Steve Gibson
Next to it, I mean, it's. My God, it's just amazing.
- [49:32]
Leo Laporte
Yeah.
- [49:33]
Steve Gibson
So anyway, it is a beautiful machine and it's a pity that we apparently, we can't trust it. I mean, we don't know what, what is known that, you know, says, what was it? Pre installed vulnerabilities? What does that mean? Yeah, I mean, like have they discovered, have they reverse engineered the firmware and actually found back doors that China knows are there?
- [49:59]
Leo Laporte
That would be a remainder service. There's probably a back door, right?
- [50:04]
Steve Gibson
I mean, well, or it ought to be a documented front door. Right? I mean, we're like. ZPMC is able to update the software in order to handle the new type of shipping container which is 30% bigger.
- [50:23]
Leo Laporte
This is a universal issue. We've talked about how the Chinese, what do they call this attack? They're in the phone systems, they're listening to phone calls. They're taking advantage of the legitimate wiretapping capabilities that law enforcement put in 20 years ago to listen to. I mean, they're in our power grid. We know that they are. They're just sitting there, they're not doing anything. But honestly, it sounds as if the Chinese government has infiltrated pretty much all of our infrastructure and has full access.
- [50:55]
Steve Gibson
We're buying all of our stuff from China. It's. They didn't have to even try, right? I mean, we, we said, oh, we like those cameras. Yeah, we'll take a million of them.
- [51:07]
Leo Laporte
But they're taking advantage of flaws in SS7 that's been there since 30, 40 years ago. Right. So, Right.
- [51:14]
Steve Gibson
So they're on the one hand there are vulnerabilities in the technologies that we're using. But on the flip side, I mean, we don't know that. There's no evidence, for example, that DJI actually was ever used in a covert surveillance effort. We just know it could happen. And we know that they are a Chinese based company. So everyone is now, and now we're looking at these cranes saying, oh my God, what if, you know, no crane has ever gone crazy and done anything wrong.
- [51:50]
Leo Laporte
Is there any reason the crane is online? Should that crane not be air gapped?
- [51:56]
Steve Gibson
My switches are online, my plugs are online, your blender is online, the microwave is online, the coffee maker is online, everything is online.
- [52:06]
Leo Laporte
Yeah, we're out of luck.
- [52:07]
Steve Gibson
I mean, that's really what has happened is we've gone online happy, right? And so you betcha, you know, I mean, who knows how those cranes even get installed. I'm sure a whole bunch of people who are experts in installing them, you know, erect them and then you've got to install the software because again, it's going to all be software controlled. Once upon a time there was a guy sitting in a cab with big levers.
- [52:32]
Leo Laporte
Oh, there still is now, now you.
- [52:34]
Steve Gibson
Got a game controller that runs the whole thing.
- [52:37]
Leo Laporte
Yeah, that's one of my favorite series seasons of the Wire. Did you ever watch the Wire?
- [52:43]
Steve Gibson
Oh, Leo, one of the best shows ever produced.
- [52:47]
Leo Laporte
Absolutely. And one of, and one of the seasons, they're down at the shipyards talking to the guys who operate those big cranes and they have lots of scenes of them in there and how fast they can move them and so forth. It's pretty cool. But that was, that was a Long time ago. I'm sure it's even cooler now.
- [53:02]
Steve Gibson
Yeah.
- [53:03]
Leo Laporte
And Chinese infiltrated.
- [53:04]
Steve Gibson
So I, I, I know, I, I feel really mixed about this. I know we have a lot of Chinese listeners. I love them. I, there's, you know, nothing against them. And we don't know that China has, has ever misbehaved. We do know that there are, that we're being attacked. We, you know, that we know. But commercial companies, there's no evidence that I'm aware of, of misbehavior yet. Because it's possible, you know, I don't know.
- [53:35]
Leo Laporte
I'm going to throw this out here. I think this narrative is a little disturbing to me because where it leads is, well, you just don't have anything that's made or from China which probably still wouldn't secure you. Right. Because. Correct. We still are using SS7. So, yeah, I've ripped and replaced all the Huawei equipment in my network, but I still have software that's got massive holes in it and I'm not willing to replace that. But let's say that's the road we go down. Let's get rid of all the Chinese stuff. I think that makes us more vulnerable because China no longer is economically dependent on us, is no longer intertwined with us. I think we're less vulnerable if we trade with our enemies.
- [54:16]
Steve Gibson
I know.
- [54:16]
Leo Laporte
And they're economically tied. Their fate and our fates are economically linked. That to me is a better strategy for keeping the peace than putting up a big wall and saying, oh, we're not going to buy any Chinese stuff. Well, then it doesn't matter then. They have no dog in this hunt.
- [54:32]
Steve Gibson
Right. They have no economic incentive for keeping their number one customer.
- [54:38]
Leo Laporte
Right. So I don't have as, I mean, look, by the way, we are infiltrating their stuff. We know this from the Edward Snowden leaks. The NSA has plenty of tools to do the same thing back. And they buy American stuff. Probably not as much American stuff as we buy Chinese stuff. But I think it makes me nervous to think of the direction we seem to be heading with these reports that, well, let's just not have anything from China at all because that could be a prelude.
- [55:07]
Steve Gibson
It would be better if we just all got along.
- [55:10]
Leo Laporte
Yeah. Which, and you know, what we've got there is, by the way, there is this mutually assured destruction, because we do have stuff in their gear as well. And there is, there, in fact, these were, they even Bill Clinton even made the, and Obama made these agreements with China. Okay, you're going to have your stuff in there, but we're going to have our stuff in your stuff. And we'll only go so far in this espionage game. And these are the rules. And, you know, that's. I don't know how good a way to do that. That's a very good way to do things, but that is kind of where it is right now. So I'm just nervous about the idea of, oh, let's cut off all Chinese stuff. No, no, no Chinese stuff. Maybe the other direction would be safer.
- [55:53]
Steve Gibson
And look at the crane. It's gorgeous.
- [55:55]
Leo Laporte
And they make good stuff. Oh, I mean, probably it's also cheaper than the American made or the German made cranes. I don't know German. I'm sure Germany makes equally good cranes.
- [56:06]
Steve Gibson
I bet, I bet. And who's to say though that if we start we switch to those? There wouldn't be some vulnerabilities even, even if Germany didn't intend to.
- [56:15]
Leo Laporte
That's the problem.
- [56:16]
Steve Gibson
There'd still be vulnerabilities that the Chinese cyber ops could get into.
- [56:21]
Leo Laporte
There's still supply chain issues, there's still software vulnerabilities. I don't. Is perfect security possible?
- [56:28]
Steve Gibson
No. I wonder what the German cranes look like. I might be in love.
- [56:33]
Leo Laporte
Where are you going to put this crane? Have you talked to Lori about your crane loss?
- [56:37]
Steve Gibson
It a little model. I want a model.
- [56:39]
Leo Laporte
A model would be okay.
- [56:41]
Steve Gibson
Yeah.
- [56:41]
Leo Laporte
And you can have, you can have little model containers and little model ships and you could go.
- [56:47]
Steve Gibson
One of the best things about my wife is she loves trains, like model trains. I could have model trains running around the house.
- [56:55]
Leo Laporte
Well, there's a very small difference between a model train and a model crane.
- [56:58]
Steve Gibson
That's what I'm saying. That's what I'm saying. I think this would probably work.
- [57:02]
Leo Laporte
I love it.
- [57:03]
Steve Gibson
Okay, so after a phenomenal surgeon in new users, BlueSky has received its first country level block. And the winner is Pakistan.
- [57:17]
Leo Laporte
Congratulations.
- [57:18]
Steve Gibson
For those who don't know, bluesky was originally conceived as a project with Twitter. Back in the Twitter days at Twitter by Jack Dorsey. It was designed to create an open, decentralized standard for social media and it was launched in 2021 as an independent entity. After that, BlueSky quickly evolved into a strong competitor to X, offering a more customizable and transparent UI, you know, user experience UX. BlueSky's overall popularity has been soaring recently and in Pakistan specifically, this is being driven by increasingly or increasing accessibility issues with X. Due to government restrictions and the growing need for a VPN to access X, many Pakistani Users have turned to using bluesky as an alternative. Unfortunately, now it appears that within Pakistan, bluesky is quickly hitting the same barriers as X. I should mention that I've received Twitter DMS from our listeners asking when I'll be moving to Blue Sky. I'm not moving anywhere. For me, X is being, you know, just kind of slowly allowed to fade. I'm still posting the weekly show notes to X because I've been doing so for years and some of our listeners who hang out there continue to appreciate that. But, you know, a nicer presentation of today's show notes was, as I said earlier, emailed to more than 13 and a quarter thousand of our listeners yesterday. And every one of those listeners is able to email directly back to me@securitynowrc.com and all of that works, even for our listeners in Pakistan. There you go. Anyway, mail works.
- [59:16]
Leo Laporte
When I was in China, I used mail to post to my blog and Facebook and Twitter because I could email it. Yeah.
- [59:21]
Steve Gibson
Yep.
- [59:22]
Leo Laporte
By the way, I got something for you, Steve. Actually, should I send a link to Lori? It's the Lego City seaside harbor with cargo ship, toy, model container, crane and boat with eight minifigures. Steve, this is what you want.
- [59:38]
Steve Gibson
You know, we don't need a train running around the Christmas tree.
- [59:43]
Leo Laporte
You need a crane.
- [59:44]
Steve Gibson
We can set this puppy up. Wonderful.
- [59:49]
Leo Laporte
This is yours. Man, that's great.
- [59:53]
Steve Gibson
Rise before Christmas.
- [59:55]
Leo Laporte
Thank you to Chocolate Milk Mini Sip. As you know, I'm Paul Holder in our chat for providing us with that.
- [60:02]
Steve Gibson
So under the section of what will they think of next? We now have what's being called repo swatting attacks. Reino Repo is of course short for repository, which is the unit of organization employed by GitHub and GitLab. So get a load of this. Threat actors have been abusing a hidden feature to cause GitHub and GitLab accounts to be taken down. The technique allows. This will really strike home for you, Leo, with the problems Twit has with anything, you know, copyrighted. The technique allows users to open issues against a targeted repo, upload a malicious file and then abandon the issue without publishing it. On both GitHub and GitLab, the file remains attached to a victim's account. Then the pesky threat actor reports the hidden non public file for for breaking the services terms of service, which forces the repo to be removed for hosting malware. Good lord. Apparently this is just one more reason why we can't have nice things.
- [61:24]
Leo Laporte
We do that the administrator. This is the problem with DMCA takes downs you're right on YouTube is that the process is so efficient, works so fast you have no virtually no time to defend yourself. Right? One would hope that both get both GitHub and GitLab would start to understand this attack and figure out this is what's going on.
- [61:42]
Steve Gibson
Not so quick. Yeah yeah. A couple of weeks ago I touched on two recently announced zero day flaws that had been discovered to affect Palo Alto Network's enterprise firewalls. That led to my quite predictable rant about the proven impossibility of protecting any form of remote management access to Internet facing services. Even firms like Palo Alto Networks whose business is security and security appliances still don't know how to do that as this you know two recent zero day flaws demonstrate. In this case to say that Palo Alto's internal architecture seems somewhat wanting would be an understatement. An analysis by Watchtower Labs that's spelled T O W R they've dropped the E reveals that this vulnerable appliance, and it's actually a family of them, is implemented in what they declare with tongue in cheek to be the absolutely stellar PHP language which is served by Apache fronted by an NGINX reverse proxy. They then note that the system implements its authentication layer by using a PHP feature known as auto prepend file, which Prepends the file UIENV as an environment. UIE environment setup php to anything php loads, which is just such poor design I can't even begin. Okay, this is implemented by the line autoprepenfile equals UIENV setup php and php's.ini file which they preface by saying quote take a look at this gem of a hack in the php.ini file and I could not agree more. They introduce its use by noting we guess auto prepend file actually has legitimate uses besides writing PHP exploits. I mean, it's just the bottom line is that this is all quite dispiriting. I don't know why I always imagined that Palo Alto Networks would be doing things right. I suppose I wanted to give them the benefit of the doubt. The UIE environment PHP text file which provides front end authentication by redirecting pre authenticated access to the login page actually contains the comment. This is their own source code. Their own PHP code contains the comment quote these are horrible hacks. This whole code should be removed and only made available to a few pages main comment, debug comment, et cetera. In other words, their own coders know this was awful.
- [65:04]
Leo Laporte
That's exactly what you'd expect some engineer to write Looking at this code just to put in the comment, this is a hack. This is terrible. Please don't.
- [65:12]
Steve Gibson
I don't know why I'm doing this. It's late.
- [65:14]
Leo Laporte
Don't make me.
- [65:15]
Steve Gibson
I'm hungry. Or they just delivered pizzas to the conference room.
- [65:20]
Leo Laporte
Oh, my God.
- [65:21]
Steve Gibson
Anyway, I couldn't agree with the. With the quota's own comment. And I would never say that Palo Alto Networks deserves to have been hit by these vulnerabilities, especially since it's their customers who will be taking the hit for this. But a design that is this slipshod can only be called asking for it. It's unconscionable that this is the utter crap they're shipping. And in order to see any of this, because it's not out for public display, the Watchtower guys needed to first jailbreak this Palo Alto Network's appliance, which they did. But this means that this extremely poor design is locked away out of sight, so that it's only visible to intrepid researchers who go to the effort to create a jailbreak. But even if it cannot be seen, every Palo Alto network's customer remains reliant upon it. We all know the rigid line I draw between bad policies which are deliberate and true mistakes which anyone could make. None of this is an example of a mistake anyone could make. You know, these are policies. There are developers inside Palo Alto Networks who know this is what they are shipping. Those people should be looking for a new job, far away from anything having to do with security. And so today we have the news from the Shadow Server foundation of evidence that at least 2000 of these palo Alto Networks firewalls have been compromised. Using those two recently disclosed zero days, 2000 of Palo Alto Network's enterprise customers have been penetrated. As a result, once they've been compromised, the firewalls contain a PHP webshell, which allows attackers to return later at their leisure. The presence of this web shell is one indicator of compromise. The Shadow Server foundation said that their number was a conservative estimate, since it relies upon a limited set of IOCs released by Palo Alto Networks last week. Now, to their credit, Palo Alto Networks had warned of a possible zero day earlier this month, which is what I talked, which is when I talked about it back then. And their communication throughout this has been stellar. So there's much to commend Palo Alto Networks about their response to this trouble. Unfortunately, this stands in stark contrast to whomever is developing their devices.
- [68:21]
Leo Laporte
Did they fix it?
- [68:24]
Steve Gibson
They probably patched it, and it's probably largely the same?
- [68:28]
Leo Laporte
Not.
- [68:29]
Steve Gibson
Yeah, maybe if a bright enough light is shined on this, they'll say, wow, is what Gibson just said true? Is what? Is what?
- [68:40]
Leo Laporte
Wait a minute, does anybody know? Is that true? Oh man, I know you know. And don't blame PHP because you can code securely in php, but the problem is it makes it very easy to code insecurely. It has.
- [68:57]
Steve Gibson
Thank you for finishing the sentence I was about to rebut with. It doesn't.
- [69:03]
Leo Laporte
It doesn't exactly get in your way, I guess.
- [69:06]
Steve Gibson
Yeah. If they had developed it in Interpreted Basic, you would wonder about the level of the programmer expertise that chose the basic language to do the work. And PHP is similar. It's a very nice language. We know what PHP the initial stands for, right?
- [69:27]
Leo Laporte
Yeah. Personal page. Do not write your security plants front ends in Personal home page.
- [69:34]
Steve Gibson
No, exactly right.
- [69:37]
Leo Laporte
Wow.
- [69:38]
Steve Gibson
Okay, so a responsible security researcher going by the handle Del Sploit, who reportedly answers email at del sploit@gmail.com has privately and responsibly disclosed their discovery of a terminally serious stack buffer overflow vulnerability across D Link's past VPN routers. I characterize this as being terminally serious because this now known to exist vulnerability allows unauthenticated users, also frequently referred to as anyone, anywhere, to remotely and at their whim, execute their remote code on the victim's targeted D Link VPN router. The concerns are that D Link's announcement of this sobering reality last Monday contains a field for Link to Public Disclosure, which is currently filled in with the abbreviation TBD as in to be determined, which strongly suggests that this Delsploit character is being responsible with his or her knowledge and is giving D Link some time to respond. But there's a problem with that. All six of these venerable and vulnerable D Link VPN routers have gone well past their end of life. They're no longer being supported by D Link and thus will not now and not ever be receiving updates to correct this most critical vulnerability. No CVS tracking designation will be assigned to track this vulnerability because it's never going to be fixed. And if a CVS were to be assigned, it would be carrying a flashing red CVSS score of 9.8, perhaps, or maybe even the rarest of 10.0s. Okay, now this vulnerability is as bad as they come because this otherwise lovely family of routers offers a standard SSL VPN which runs a simple web server at the standard HTTPs port 443. I have a screenshot in the show notes of what you get when you use your HTTP browser to connect to this thing's port 443. It looks like a web page asking you for your username and password. From the standpoint of almost actively soliciting attackers, this could not be any worse. The page that's displayed to any Device connecting to port 443 of an of an affected router prominently displays the device's model number and both the hardware and firmware version numbers. This thing effectively shouts please exploit me so you know where they are on the Internet will never be any mystery, and I have no doubts that the lists of their IP addresses have long ago been assembled okay, so now everyone knows the situation. The two oldest affected routers are the DSR 500n and the 1000n, which both went end of life nine years ago back in September of 2015. The more recent four VPN routers are the DSR 150, 150n, 250 and 250n. All four of those went end of life just a few months back in May of this year. But as the saying goes, close only counts in horseshoes and hand grenades, meaning in this case that end of life is end of life and that D Link formerly states in their disclosure that these now known to be seriously vulnerable D Link VPN routers will never receive updates Longtime listeners of this podcast know what will come next as sure as the sun rises every morning. Many tens of thousands of these devices are currently sitting on the public Internet. Number may be around 60,000 6, 000. I haven't seen an exact count, but I'm sure that either Shodan or Census would have that number and be able to provide their IP addresses, since every one of them, as I said, proudly presents its logon page to any passerby. There's been no public disclosure of the details of the vulnerability that Del Sploit found, but D Link has confirmed it, and at some point Delsploit is going to want to have their day in the sun and bragging writes about having discovered this vulnerability. So it's going to be published and no one can really fault Delsploit for eventually disclosing the vulnerability they discovered, because that's the way the game is played these days. You wait long enough to give the impacted parties a reasonable amount of time to respond, and after that, no matter whether or not they have, and regardless of the consequences, the entire hacking elite is then informed of exactly how to bypass the Internet facing authentication, which protects tens of thousands of networks that are Currently behind every one of these VPN routers, there's nothing any of us can do other than protect ourselves and those we have responsibility for and care for. So make absolutely double damn certain that nowhere within your spheres of influence do any of this 6D link VPN routers currently exist. Because we all know exactly what's going to happen next. In their disclosure, D Link ineffectually recommended that this hardware should be replaced. We know that most of the owners of these devices will never receive any sort of notice of this and probably wouldn't pay it the attention it deserves even if they did. We're all being so inundated by all of our software being constantly updated that it's easy to become numb to it. But if anyone is in the market for a replacement, I would now say to stay well clear of D Link. They have a long and still growing history of very serious remotely exploitable vulnerabilities being discovered after the fact in their past end of life products. This happened earlier this month with 66,000 of D League's Internet connected NAS devices. Their response was effectively, well, we're sorry, we don't make NAS any longer. And even if we did, those 66,000 Internet connected remotely exploitable network attached storage devices we once made are now past their end of life, so it wouldn't matter even if we still made them. It's true that hardware is not forever, and that it would not be unreasonable to expect an aging NAS or router that's past its end of life to be rotated out of service in favor of something new. But we all know that that doesn't happen often. Given their track record, I would be disinclined to give D Link any more commercial support if you really like the brand. Okay, you know, I get it, it is truly nice looking hardware. But you should be aware that end of life or end of support probably means end of secure service life, after which point a device, a D Link device, should be rotated out of service. And if you have any existing inventory of D Link devices, you should be very certain to have a current subscription to their security bulletins and other notifications and really pay attention when you get one.
- [78:26]
Leo Laporte
It's too bad. This used to be a good company, right? I mean, I had a lot of D Link routers in my day. Right.
- [78:32]
Steve Gibson
I did too. But you know, they're having problems and I mean, again, it's not, it's not unreasonable to say, okay, well it's, it's end of old and we're not going.
- [78:44]
Leo Laporte
To support it anymore.
- [78:44]
Steve Gibson
Yeah, yeah. I mean, all the other companies do that too. But even Microsoft has gone back and like fixed a really bad Windows 7 problem after Windows was end of life because they recognized they didn't want to hurt their own users.
- [79:03]
Leo Laporte
The problem really is that D Link was a consumer dominant consumer brand for a long time. And so there are a lot of people who aren't that sophisticated who have D Link gear and they're not paying attention. They don't listen to this show and.
- [79:15]
Steve Gibson
Right.
- [79:16]
Leo Laporte
So they'll never know that there's a problem with their router or actually it's not a router, it's. What's a nas?
- [79:24]
Steve Gibson
Well, it is a. An S. Yeah, it is. The earlier this month it was 66,000 NAS. And now we've got. We have six different models of SSL VPN routers.
- [79:41]
Leo Laporte
Routers.
- [79:41]
Steve Gibson
And so an SSL VPN router is sitting there listening for incoming SSL connections on Port 443. So I mark my words, a month or two from now we will have a count of how many systems have just been taken over as a customer.
- [80:02]
Leo Laporte
I mean, at least an SSL router is not a consumer product. That's not in grandma's hands.
- [80:07]
Steve Gibson
Well, actually, I don't know. I would say that's a bigger problem because it means that it's hooked to a more valuable network.
- [80:13]
Leo Laporte
Yeah. Something you're trying to produce.
- [80:14]
Steve Gibson
It's not on Grant Chinese lan.
- [80:16]
Leo Laporte
Right.
- [80:16]
Steve Gibson
You know, it's on, you know, some, some small businesses network that can be, you know, have all their systems encrypted and then held for ransom.
- [80:26]
Leo Laporte
Yeah. Some IT guy 12 years ago installed it in a lawyer's office and nobody's thinking about it. It just works. And security is not a concern.
- [80:35]
Steve Gibson
Except I had sort of a related story. It turns out that as many people know, Sharia is a religious law that governs some aspects of the lives of Muslims based on the teachings of Islam and the Quran. We were just talking about Pakistan being unhappy with pretty much all things Internet. I should note that Pakistan's Religious Advisory Board recently ruled that the use of VPN apps is against Sharia law, apparently, because Sharia law is whatever they want it to be. The Council of Islamic Ideology said that VPN technology was being used in Pakistan to access content prohibited according to Islamic principles or forbidden by law, including, quote, immoral and porn websites or websites that spread anarchy through disinformation. And this gave me pause to wonder, Leo, whether they might be inclined to change their minds if they Were able to get a really good deal on some used D link VPN routers.
- [81:40]
Leo Laporte
Yeah, that's the ticket. Oh, Lord.
- [81:46]
Steve Gibson
What a world, huh?
- [81:47]
Leo Laporte
What a world. Well, this is. Yeah, I mean, yeah. Yeah.
- [81:51]
Steve Gibson
So we have the return of recall. Let's take a break.
- [81:55]
Leo Laporte
Yes.
- [81:55]
Steve Gibson
And then we're going to talk about recall now being put back into Windows Insiders to begin testing.
- [82:03]
Leo Laporte
Yep. Congratulations. We talked about it on Sunday and on Twit and all four of us said, yeah, but we would love to have something like recall. In fact, my problem with recall is it should be on every device. It should be on everything. But of course, that would be a security nightmare. But we'll let you talk about that in a second. Our show today, brought to you by Threat Locker, this is the opposite of recall. This is basically zero trust. It's the opposite of what you were talking about earlier, which is, you know, kind of allow everybody and then, you know, filter out the bad guys. No, no, it's quite the opposite. If zero day exploits and supply chain attacks are keeping you up at night, and I think they probably are, if you run a business, here's a solution. You don't have to worry. You can harden your security affordably and easily with Threat Locker. I mean, worldwide companies like JetBlue Trust Threat Locker to secure their data, to keep their business operations flying high. But even small businesses can benefit with Threat Locker's easy to implement zero trust solutions. Very affordable. Imagine, and this is the kind of the nut of how it works. Taking a proactive deny by default approach to cybersecurity. Deny by default. That's what zero trust is. You don't assume just because somebody's in your network that they're good guys, that they should have access to everything. Unless. Unless you give them explicit approval. Every action is blocked, every process is blocked, every user is blocked. And it will continue to be blocked until authorized by your team. And even further than this, you were talking about logging earlier Threat Locker, which will, which will make it easy to do. This also will give you a full audit for every action fully logged. So that's great for risk management, for compliance too, right? You can demonstrate your security posture. If this is how it should be done, this is done. Right? And their 247 US based support team will fully support you getting started, getting onboarded and beyond. Stop the exploitation. This is so cool. I talk about ring. One of the things they do called ring fencing. Stop the exploitation of trusted applications within your organization. Keep your business secure, keep it protected from ransomware organizations across any industry can benefit from Threat Lockers ring fencing. That's what they call it and it's a great name for it because you're in a sense fencing stuff in you're isolating those critical and trusted applications from unintended uses from weaponization. You're eliminating attackers lateral movement within your network. Threat Lockers ring fencing works so well it was able to foil a number of attacks that were not stopped by traditional EDR, including the SolarWinds Orion attack. We've talked about it for many years. It was foiled by ring fencing because you couldn't move laterally in the network. Oh, and Threat Locker works for Macs too. Get unprecedented visibility and control of your cybersecurity quickly, easily and cost effectively. Threat Locker Zero Trust endpoint protection platform offers a unified approach to protecting users, devices and networks against the exploitation even of zero day vulnerabilities. When we first talked about these guys I went out and I looked at reviews. I was blown away. But the people who use Threat Locker love it and it really works and it's very affordable. You could get a 30 day free trial right now. Learn more how Threat Locker can help mitigate threats no one's ever heard about before and ensure compliance. Visit threatlocker visit threat locker.com that's threatlocker.com we thank him so much for supporting the good works of Mr. Stephen Tiberius Gibson and and you support us when you go to threatlocker.com and if they ask, tell them you saw it on Steve's show. That will help a lot. Okay Steve.
- [86:02]
Steve Gibson
So last Friday, yes, the Windows Insider blog announced the return of recall to Windows 11. They wrote hello Windows Insiders. Today we're releasing Windows 11 Insider Preview build 261202415 or as one of my employees would have once said, Start eight, which I thought always was funny. He said that. They said to the Dev channel with this update we welcome Windows Insiders with Snapdragon powered Copilot Plus PCs to join the Dev channel to try out Recall Preview with Click to do Preview, which is a new feature that they are that they're now going to be testing. So anyway, I have a I have a link to the lengthy rollout text in the show notes for anyone who wants more. Suffice to say that Microsoft has done exactly what they had promised to do. The setup experience, of course, promotes Recall as a wonderful and really secure feature. It's unclear from the few screenshots Microsoft provided what the user's decision tree looks like and how readily the user is able to decline to receive the recall experience. But presumably after all the backlash Microsoft received and their commitment to disable Recall until and unless its user explicitly enabled it, that's what they've done. I do know from reporting that Recall can mostly be removed from Windows through that turn Windows features on and off dialogue. One security researcher noted that a few recall related DLLs do remain under the Windows System Apps Directory, specifically Microsoft Windows Client, but this researcher noted that the core functionality is removed, so that's good. A few items of note from their blog posting were Quote Recall Preview will begin to roll out on Snapdragon powered Copilot Plus PCs with support for AMD and Intel powered Copilot PCs coming soon as we gradually roll out Recall in preview. Recall is supported on select languages including simplified Chinese, English, French, German, Japanese and Spanish. Content based and storage limitations apply. Recall is not yet available in all regions, with expanded availability coming over time. So there were anecdotal reports of researchers being able to get the first shot at recall running on PCs without any fancy AI GPU support. So it might be that Recall will be made more widely available over time, you know, and so this might also mean that for now no one without copilot plus PCs will need to worry about removing it since it may never be present and again not yet in the main channel. This is all just insider preview also of interest in the posting for their enterprise customers, they said as announced at Ignite for our enterprise customers, Recall is removed by default on PCs managed by an IT administrator for work or school, as well as enterprise versions of Windows 11. IT administrators fully control the availability of recall within their organization. Employees must choose to opt in to saving snapshots and enroll their face or fingerprint with Windows hello for snapshots to be saved, only the signed in user can access and decrypt recall data, theoretically. So although enterprises cannot access employee recall data, they can prevent recall from being used altogether and prevent any saving of specific apps or sites. So essentially they're they're saying that that you know, group policy settings that the IT admin controls can can prevent Recall's use. But if recall is allowed, then employees will it is still a one a one to one relationship between the machine and the employee that under no circumstances does the enterprise have access to the data that recall is collecting for that employee. So that's good. And of course that was not the case when this was first rolled out in that very what many people feel was a premature mode because none of the data was encrypted it was just all there in a user directory. So just for the record, Microsoft is also previewing a recall feature which they call Click to Do and they write with Click to do. In Recall you can get more done with snapshots and improve your productivity and creativity. Click to do recognizes text and images in snapshots and offers AI powered actions. You can take on these, saving you time by helping complete tasks in line and or quickly getting you to the app that can best complete the job for you. They then show that the user is able to mark and highlight to select text in an image on a recall snapshot, which is cool. And then once selected you get a context menu with Copy, open with search the web, open website and send via email. And if the user happened to right click on a recalled image as opposed to text, a block of text, then the context menu commands are copy, save as Share, open with visual, search with Bing, blur the background with photos, erase objects with photos and remove the background with paint. So some things you can actually do with images that are recalled and apparently soon with things that are not recalled. They said in this update Click to do only works within the recall experience. And by the way, we're going to have a lot of experiences with Windows apparently and Microsoft. That's their new favorite word. They said in a future update you'll be able to effortlessly engage with Click to Do by simply pressing windows logo key + mouse click windows logo key + Q through the snipping Tool menu and Print screen or searching Click to Do through the Windows search box. In other words, it'll be pervasive in Windows. They said these methods will make it easier than ever to take immediate action on whatever catches your eye on screen. We're also working on introducing more intelligent text actions to enhance your experience even further. Just like with Recall noted above, Click to Do Preview is available only on Snapdragon powered Copilot PCs. Support for intel and AMD powered Copilot PCs is coming soon. So okay, you know, for people who have those again, not yet mainstream, not yet released, but it's clearly coming. I was talking earlier about the fact that we absolutely know that very, very few of the now known to be vulnerable D Link VPN routers will be removed from the Internet as a result of D Link's announcement of their serious vulnerability. How do we know? Well, all of the history that we've talked about on this podcast shows that in this case CISA maintains a list of the most exploited security vulnerabilities by year. We know that at least 66. Zero known threat actors exploited vulnerabilities from CISA's list of the most exploited bugs last year. And we have details. According to the security firm Vuln Check V U L N check. The North Korean group Silent Kalama was the most active in this regard. They targeted nine out of 15 CVEs from CISA's list. China and Russia's groups were the most active among the 60 known threat actors, with China sponsoring 15 groups of those 60 and Russia supporting nine groups. And here's the most distressing news that gets back to why we know that few of those D link routers will be removed from service. Hopefully all of our listeners will. If there's any intersection between those D link routers and our listeners, the action will be taken. But VCheck reports that over 400,000 systems that are currently online at this moment are vulnerable to attacks. Using one of last year's Most popular vulnerabilities, 400,000 systems online now are vulnerable to at least one of 2023's most popular. And I have, you know, popular most exploited vulnerabilities. So, wow, we have to do better as an industry. We really do somehow need to do better. Okay.
- [96:19]
Leo Laporte
It just shows you how hard it is to do, though. I mean.
- [96:22]
Steve Gibson
Yeah, well. And I'm sure that notices are going out. As I said, we all just get inured to them. Essentially. We just stop paying attention to every one of them because it's like, oh my God, oh my God, oh my God. And finally it's like, oh, yeah, fine. Well, we keep hearing that. But nothing ever bad happens until something bad happens. Okay. Some great feedback from our listeners. Thomas wrote, on a recent episode, you mentioned a device that acts like a Bluetooth keyboard and connects via a dongle between a phone or other Bluetooth device and a computer or basically anything you could plug a USB keyboard into. It sounds to me like an input stick. And that's, he said, a device that I used frequently as a hardware tech when replacing HP motherboards. After you replaced the motherboard, you had to enter a setup command string that was about 30 characters long and case sensitive. Since it was entered before during bios, you could not copy it into the field from the web. It was a nightmare. Okay, right. 30 characters of upper and lowercase gibberish. Yeah, he said, but with the input stick.
- [97:54]
Leo Laporte
This is so cool.
- [97:55]
Steve Gibson
Oh, Leo. I immediately ordered one.
- [97:57]
Leo Laporte
I was about to order one myself.
- [97:59]
Steve Gibson
It is very, very cool. And the apps kind of like a.
- [98:03]
Leo Laporte
Yubikey, but you could program it to do Whatever you want.
- [98:06]
Steve Gibson
It's exactly what it is. And not only keyboard, but also mouse. Wow. So you're able to remotely control like do mouse functions. So he said. But with the input stick you could go to HP's website on the phone, copy the string, paste it into input sticks software and send it, slash, input it directly the first time. So clever, he said. Been a while since I've done that. Mostly it now works as the volume control to turn my computer down when I'm going to sleep, he said. And because they have also complete multimedia controls also, he said.
- [98:48]
Leo Laporte
As any keyboard does, of course.
- [98:50]
Steve Gibson
Yes, exactly, he said. Still one of my favorite toys though. Even though I'm no longer in the biz, I still keep up with the news via security. Now sign Thomas.
- [98:59]
Leo Laporte
Nice.
- [99:00]
Steve Gibson
So as I said, Thomas is 100% correct. The gizmo that is the gizmo that another listener mentioned, which I immediately purchased since it looks clever and interesting. I think it was $39 US plus shipping from Poland and they immediately shipped it. I got a notice of it being shipped like hours later. I'll report again once I've had a chance to play with it. Its creator appears to have done quite a lot with the capability. It's able to simulate both a keyboard and a mouse and as I said, it's able to simulate multimedia control keystrokes, it's got macro capabilities and the works. So you know, I'm constantly annoyed that despite my decades long loyalty to all things Apple, for everything other than PCs, Macs offer integration features that Apple refuses to bring to Windows. You know, I would, oh my God, would I love to have imessage for Windows. But no, no, I don't get that. And I was wondering if this would somehow allow me to bridge that gap. But it's actually, it's going in the wrong direction probably. Unless I were to, I guess I could. No, it's going in the wrong direction. So I guess at the same time if they, they brought us something that was like itunes for Windows then so I'm probably better off without it.
- [100:21]
Leo Laporte
So.
- [100:24]
Steve Gibson
You have a solution?
- [100:25]
Leo Laporte
No, I'm just, I'm trying to think of how you would use it. So your, your goal is to be.
- [100:32]
Steve Gibson
To do what I guess my goal would be. Okay, so I, it's, it's burdensome writing a long message on the horrible touch screen.
- [100:42]
Leo Laporte
Yeah, you want to do it on your keyboard.
- [100:44]
Steve Gibson
So I like to do it on my keyboard.
- [100:45]
Leo Laporte
Right.
- [100:46]
Steve Gibson
And then just send that. Yeah. And I've like, I've emailed me Myself messages and then gone to email on the iPhone, opened it, copied it, gone to messages, pasted it and said it. It's like that.
- [100:59]
Leo Laporte
What? This is how Apple keeps people in the Apple ecosystem. It's easy to do if you're an.
- [101:05]
Steve Gibson
Apple, if you're all Apple I know.
- [101:11]
Leo Laporte
Otherwise you might buy other people's computers and we can't let that happen, right?
- [101:19]
Steve Gibson
Gino Guidi, who signed his note the network Ninja earns his title, he wrote. Steve was listening to the episode where you had a listener ask about how to capture the command and control C2 traffic when it's using a hard coded IP. The solution you offered would absolutely work. I think the more elegant solution would be to just NAT the destination. I'm not entirely familiar with PF Sense or OpSense, and I use Untangle and Palo Alto at home. However, if you have firewall software that supports it, you could create a NAT rule that changes the destination from the hard coded IP to a host of your choice. You won't even need additional interfaces. If you configure the rule correctly, it will re nat it back for return traffic. The malware will have no idea that it isn't actually talking to that ip. The additional advantage is that you wouldn't have to change the IP or add additional IPs onto the machine you're sending the command and control traffic to. You could easily create as many of those NAT rules as you want, which I think would make it more robust long term. I appreciate the podcast and hope to be listening for another 1,000 episodes. Okay, hope this suggestion makes sense. Okay, so given that a router's firewall supports it, I think it's a brilliant solution that's clearly superior to the more complex approach that I propose. So I like it a lot. Okay, so let's think this through. As I understand it, it would require routing software that's able to perform NAT translation for packets traversing the router's internal LAN interface. That's different from typical consumer router nat, which is generally applied to outbound packets crossing the router's WAN interface. So this would definitely require some third party routing software, you know, higher end routing software like PF Sensor, OPN Sense. Applying NAT to the internal interface would cause any packets sent from any machine on the lan, such as the malware infected machine, which is addressed to a specific external public ip, to have its destination IP changed to another host machine on the lan, the one that's serving as the command and control server. So that packet source IP would Remain, the source IP would remain unchanged, the IP which would be the IP of the infected machine. So on its way out from the malware infected machine, the outbound packet crosses the LAN's selective NAT translation, which would give it a local destination LAN IP address. This would cause the router to send it back out the same LAN interface now addressed to the command and control server. And since that packet arriving at the command and control server would still be carrying the local source IP of the malware infected machine, the spoofed command and control server would return its replies directly to the malware infected server. So it's an elegant solution and I can't see why it wouldn't work. I haven't tried it, but it's sort of an interesting concept. I replied with this to our network ninja Gino, who sent me a follow on link that referred to this using the term hairpin nat. So this thing, it is a known technique and you can see a hairpin, right? It's like bent, it's like a, it does an immediate 180. So it's called a hairpin nat, where you NAT across your local interface, your LAN interface as opposed to the wan, in order to perform these sorts of tricks. So very cool. Thank you. ABHI Rao, a B H I Rao, driving his skids, his kids to school in Charlotte, North Carolina, wrote hi Steve, I've been listening for the past 12 years. Your podcast has been a constant on my drive to work and dropping my kids to and from school. My kids have grown up listening to your voice. Sorry about that, and more security conscious because of you. So thank you. Yeah, I guess the kids are probably on edge now. He said in your Last show, episode 1001, you mentioned Cloudflare tunnel as an option for accessing home networks. One main clarification I would like to make, which you did not mention, is that although a Cloudflare tunnel is simple to set up and use, it does not provide true end to end encryption while it encrypts traffic between your origin server and Cloudflare's network. Cloudflare can decrypt and inspect the data in transit as it terminates the TLS connection at its edge network, meaning it is not fully encrypted from start to finish. And he says what we all know for true end to end encryption. An overlay network like tailscale can be used for more detailed comparison. And he gives us a link that I haven't seen before@tailscale.com Compare Cloudflare Access. He says, I looked into Cloudflare Tunnel myself to access myself hosted bit warden running on my home Synology nas, but I decided to use Tailscale instead for this reason. Love the show to 2000 and beyond Leo which appears to be everyone's new goal for us since we did pass 999 unscathed. So Abhi we need to come up.
- [107:48]
Leo Laporte
With a hand gesture.
- [107:51]
Steve Gibson
Yeah.
- [107:54]
Leo Laporte
I don't know.
- [107:58]
Steve Gibson
He provided a link as I he provided a link which I have in the show. Notes to Tail Scales Tail scale versus Cloud Flare Tunnel side by side feature comparison and I tend to agree with AB's feelings. I think that the best way to think of it is that these two solutions Cloudflare Tunnel on one and an overlay network like Tailscale on the other. They have some overlap in their capabilities which allows either one to solve the remote access problem, but they are also very different. Cloudflare Tunnel has a large range of features that go far beyond what's needed for remote access to a user's lan. It's really aimed at secure remote access to servers, and an overlay network's true full end to end encryption is really what we want for remote network access, and it sort of tips me in its favor. Stephen Klowater reminds us of an even simpler solution, writing hey Steve, Congrats on hitting 1000 plus episodes. Thanks for all the thoughtful content you've shared. I wanted to share an observation about remote access to Home labs, he said, having tried Cloudflare Tunnels and various VPN clients. For those who don't need the features of an overlay network like Tailscale, Wireguard is worth considering. It offers simple, lightweight layer 3 connectivity, modern elliptic curve crypto, and straightforward setup. While tailscale builds on WireGuard for robust overlay features, a standalone deployment keeps things minimal and widely supported across platforms like Linux, PF Sense, and OpSense. What has kept me using Wireguard, he writes, is how it handles iOS sleep cycles, meaning the Wireguard client on iOS, he said ensuring apps can reliably access data when waking from sleep. VPNs like OpenVPN, CF, Warp, and Ikev2 often struggle with app level connection failures because their clients cannot wake up properly in the selective sleep process iOS has or renegotiate stale connections before a TCP timeout. WireGuard's small kernel footprint and fast connection renegotiation allows it to reconnect on demand without timeouts, he says. I started using Wireguard in 2020-2021 while setting up a self hosted email server. I needed a reliable way to fetch mail on my phone while keeping port exposure to a minimum. Since then, it's become a core part of my setup, enabling reliable email fetch cycles, isolating ubiquity cameras, and syncing files via sync thing on my phone. Just thought I'd share in case it's helpful to anyone exploring options best and he signed off another Steve because he's Stephen Clowater. So I'm really glad Stephen reminded us of the many benefits of just plain old wireguard. We originally discussed wireguard, which was, you know, at the time viewed as the replacement for OpenVPN, which had grown very old and stale back when it first appeared on the scene about five years ago in episode 744. I first talked about Wireguard after meeting and being very impressed by the founders of the Mulvad VPN service and learning that they were already adopting wireguard. And recall that not long after that Linus Torvalds incorporated wireguard natively into the Linux kernel, which is saying something for it, because he would never do that casually. The only downside to running, for example, WireGuard on a PF Sense or Opn Sense router is that the first thing you need to do is open a static port through the router's WAN interface to the WireGuard service running on the router, and from then on that port is open, facing the outside world and you're relying on wireguard not to have any critical vulnerability that would allow an authentication bypass. If you're okay with that, then wireguard is likely the lightest weight and most secure solution available. And I loved what Stephen shared about its compatibility with iOS. But running with a statically open port, which is never required when using any of the overlay networks, would tend to bend me away from wireguard, much as I would otherwise love to be able to use it. What I would consider as an option would be adding some sort of port knocking solution that would allow a remote IP to be authenticated so that that IP and that IP only could then connect to the wireguard VPN running in the home base router. You know, since for example an ICMP ping packet can contain plenty of payload, a simple and secure challenge response mechanism that incorporates the endpoint IP addresses and some crypto would do the trick, you know, and I would write one. I would create it. If only there were more hours in the day, but maybe somebody has or will. Enrico gave his Note the subject ep989 backdoor or incompetence? And he said happy 1000 I'm still a bit behind I'm listening to episode 989 where you talked about the Chinese RFID badge chip that was found to have a backdoor. We've heard plenty of reports about vulnerabilities found where the manufacturer left some debugging credentials in. We've also heard lots of reports about backdoors and products. I'm curious in general, how does one determine if something is a backdoor or incompetence? How can the researcher infer intent? Perhaps an internal company memo gets leaked that shows it was on purpose. It is still hard to tell if this was mandated by the government unless top secret governments get leaked. Is it just based on the country that manufactured the device and whether they're friendly to the us? I also heard about the guy that has done some back that oh that has gone back and started listening to your podcast from episode one. I wanted to do this too. However, I'm already over 10 episodes behind so I just fall even further back. Only listen to podcasts while driving. Maybe I need to plan some long road trips. Okay, so I think Enrico makes a very valid point. Controversy is inherent when attempting to ascribe intent. The question of the Windows metaphile escape which I talked about last week, is another perfect example. Why was it there? Why had it been faithfully copied and re implemented through many editions of Windows, even jumping from windows 3, 9598 and me over to the brand new Windows NT where it had to be reimplemented? Was all that an accident? The original intent of its designers has been lost to history, and we'll probably never know. And remember about 10 years ago when Cisco kept discovering hidden backdoor credentials in one appliance after another, month after month? You know, and I have discovering in quotes because you know, these were their own systems. How difficult could it be to discover an undocumented login account in software that they wrote and for which they have the source code? They just had to look. So I guess they just looked and it's like whoopsie. Anyway, since Cisco is not evil and never was, and since they were confessing over and over to what they kept finding in their own machines, I think that's a case of poor judgment and changing times. Twenty years ago, just as it may have been acceptable to design an escape hatch into Windows metafiles, it may have been acceptable for developers to just kind of lazily leave their development accounts in Cisco appliance firmware. Back then, it may have been no big deal. But as we've seen times change, as does our expectations. My feeling is that in nearly all cases it's just a mistake. For one thing, no clever developer would implement something that was meant to remain a secret by leaving a username and password in the firmware. That's way too obvious. If someone told any competent developer okay, not somebody using php, I did say competent developer to design in a back door, it would be far more well hidden. For example, it would be necessary to first bounce an ICMP ping packet off the device with a particular payload length. This would leave an insignificant trace. Then it would be done again with a different specific length, and that pair of events would prime the device to then accept anything originating from the same source IP only without requiring any authentication or something like that. My point is nothing as dumb and obvious as leaving a username and password account burned into the firmware. There are an infinite number of ways to bury a true backdoor in today's insanely complex systems. And there's something that keeps people awake at night because these things could be really difficult to find.
- [118:57]
Leo Laporte
Yeah, I guess it doesn't. The intent doesn't really matter. It's. It's the fact that it exists, period is sufficient.
- [119:03]
Steve Gibson
Yeah, right. And I guess the real point is who else knows about it, right?
- [119:10]
Leo Laporte
Everybody knows everything. Don't think you can hide anything. That's really the truth.
- [119:15]
Steve Gibson
Exactly. There are no back doors David in the US Wrote hello Steve, I'm a longtime listener but haven't reached out before. I credit you in large part for my career in infosec. I was unable to get formal education in the field, so I self taught using resources, including your podcast. It's been many years since I started my first job in the field, but I still listen regularly and learn a lot. Thank you for all your efforts. I'm sure this is an edge case, but regarding your remarks about Soho routers in SecurityNow995, I was recently treated to an experience with a new Nokia. They still exist. Soho router access point. I changed ISPs and they provided one for free with a WI FI access point ready to use. They came out and installed it for me and plugged what they thought was my computer into it, he says. Parens as if I had only one Haha he said. After they left, I plugged my entire home infrastructure into their router. As a result of your recommendations some years ago, my main firewall is Pf sense running on a Protect LI unit. You know P R O T E C T L I that I mentioned recently. He said I didn't bother to reconfigure the new Nokia box for a couple of days because I didn't consider it an important layer of security. However, I finally got around to logging into it and was stunned by what I found. For some unfathomable reason, the firewall was set to light filtering mode. Apparently it had a short self described non disruptive block list it was using to blacklist certain things. However, it was not performing NAT services for the ethernet. It was a pass through mode by default, giving my public IP address to my PF sense firewall behind it. There was an option on the Nokia device to enable nat, but it was disabled. While I would like to think that perhaps it detected the firewall behind it and switched itself off, I somehow doubt it was that smart. If I was a typical user, whatever I plugged into that ethernet port would have been immediately exposed to the Internet. The wifi did seem to be using nat, so perhaps they thought that was good enough for most users. Okay, so this was really interesting to me. The thing that occurred to me first after thinking about what David wrote was that I'll bet almost no typical Internet user today ever plugs anything into their router's wired ethernet ports. I know that many of us who listen to this podcast do, but we're far from typical Internet users. WI fi really has overtaken wired Ethernet and that's the only way I can think to explain what David experienced is that, you know, just everyone uses wifi. So that was what was set up in order to, you know, share a single IP box.
- [122:52]
Leo Laporte
Maybe that Nokia just wants to say, you know, anything you plug in is dmz and maybe that's, you know, I wonder if it even says that if you're going to hook up a web server to this, put it on the ethernet port because then it'll be dmz. It's directly connected to the Internet, right? Yeah. As you can tell, not a recommended solution.
- [123:15]
Steve Gibson
A recommended solution. I have a couple inches at the bottom of this final page before we switch to today's main topic. So I wanted to answer the many questions I received from listeners who've taken note of the fact of the remarkable pro box on the bookshelf behind me. You could see it right there over my. My left shoulder. It's right. It's there. I'm pointing at it. Dave wanted to know what I think of it. I very much wanted to love it, but I don't. I wanted to like it's. I don't. I wanted to like its support for color. It's slightly higher pixel density. It's larger size and it's reputed higher stylus tracking rate. But I don't. Its support for color feels like it's not ready for prime time. The display goes through all sorts of conniptions when using color. I mean, it's almost comical what the thing has to do with things flashing and switching back and forth and blinking. It's, you know, it's clearly not easy to pull off color and I don't think it was worth the effort. Also, the darn thing is heavy. I mean, it is really heavy. And its stylus now requires charging, which the Remarkable 2 doesn't. By comparison, its predecessor, the Remarkable 2 I really love. You know, I do wish I could get the cool cover for the Pro which much more securely captures the stylus than on the Remarkable two. But at least for the time being, it appears that that cool cover is only available for the Pro. So anyway, to answer everyone's questions, I was hoping I would like the Pro as much as I love my Remarkable Twos. I have a couple of them, but it doesn't really make the grade.
- [125:13]
Leo Laporte
You tried the Amazon Scribe, right?
- [125:15]
Steve Gibson
Yeah, well, yeah. It's only because the Remarkable is just. I mean, yeah, I don't, I don't do any reading on it. I don't do. I don't read PDFs, I just use it as a replacement for my engineering pad.
- [125:30]
Leo Laporte
Right.
- [125:31]
Steve Gibson
And a soft number two pencil.
- [125:34]
Leo Laporte
It's nice to have unlimited graph paper, isn't it?
- [125:36]
Steve Gibson
Oh, yeah. And I now have. You're able to sync three devices through to a single account. And because I purchased one in the old days, I'm grandfathered in to the no charge icloud connectivity. So if I doodle one location when I turn it on on the other, it's synchronized multiple location doodling.
- [126:04]
Leo Laporte
What more could anybody ask?
- [126:06]
Steve Gibson
I got everything I want.
- [126:09]
Leo Laporte
Yeah. The advent of code is coming up in just five days.
- [126:13]
Steve Gibson
That's right.
- [126:14]
Leo Laporte
That's one where it's very often handy to sketch out.
- [126:19]
Steve Gibson
I'm a big algorithm bits sketcher.
- [126:21]
Leo Laporte
Yeah. Yeah. Just to understand. In the advent of code, it's all about text problems. And so to even understand the geometry, sometimes you have to draw it because otherwise it's like.
- [126:32]
Steve Gibson
Yeah.
- [126:32]
Leo Laporte
In fact, there were people a couple of years ago cutting out paper and making paper cubes so they could understand the relationship from one side to another.
- [126:40]
Steve Gibson
No, I absolutely get it. The, the, the. It's all those off by one problems you want to make exactly. Sure.
- [126:47]
Leo Laporte
Yeah.
- [126:47]
Steve Gibson
That, that you mean greater than or greater than or equal.
- [126:50]
Leo Laporte
Right.
- [126:51]
Steve Gibson
And so I just, I quickly jump to a little sketching out a little simple example of a more complex problem.
- [127:01]
Leo Laporte
I do exactly the same thing. Yeah.
- [127:03]
Steve Gibson
Did we do all of our breaks?
- [127:05]
Leo Laporte
We have one more. Would you like to do one more.
- [127:07]
Steve Gibson
And talk about disconnected experience, experiences, whatever that is.
- [127:12]
Leo Laporte
We'll find out in just a moment.
- [127:14]
Steve Gibson
Why you may want to be disconnected from some of these experiences.
- [127:17]
Leo Laporte
Yes, please. Here's, you know, you listen to the show, I'm sure, because it gives you.
- [127:22]
Steve Gibson
I'm right here.
- [127:23]
Leo Laporte
No, no, you do. I'm talking to our fine audience. Yeah, I was watching the F1 race on Sunday. It was in Las Vegas. And they talked to one of the drivers, longtime F1 driver, and they said, do you ever watch your races? He says, no, I was in it. I don't need to. I don't need to watch it. I know what happened. Yes. We don't listen to our own podcasts. We were in them. But I'm talking to you, our dear listeners, our wonderful listeners who listen to this show for information. Right. They get intelligence out of it. Governments have intelligence agencies. Why don't companies? Well, now you can with Flashpoint. This episode of Security now brought to you by Flashpoint. For security leaders, this year has been insane. It's like no other year. Cyber threats matched with physical security concerns and they're both increasing. And now you've got geopolitical instability adding a new layer of risk and uncertainty. And how important is it for you and for your business to know ahead of time where the threats lie? Let's talk numbers. Last year there was a staggering 84% rise in ransomware attacks, almost doubled. A 34% jump in data breaches. That should give you chills. Nobody wants a data breach. The result, Trillions. Trillions with a T of dollars in financial losses. Threats to safety worldwide. Well, okay, that's where our sponsor, Flashpoint comes, comes in. Flashpoint empowers organizations to make those mission critical decisions that will keep their people and their assets safe. And it does it with information. That's what you need, information. By combining cutting edge technology with the expertise of world class analyst teams. And with Ignite, Flashpoint's award winning threat intelligence platform, you get access to critical data, finished intelligence, you get alerts, you get analytics, and you get it all in one place. It's a dashboard to the world out there and what's happening. It helps you maximize your existing security investments. Some Flashpoint customers say they avoid a half a billion dollars in fraud losses every year and have a 482% ROI in six months. That's probably one of the reasons Flashpoint earned Frost and Sullivan's 2024 global product leadership Award for unrivaled threat data and intelligence. Here's an example. A senior vice president of cyber operations at a big. I can't say the name, but you would know it. US Financial institution, he said, and this is the quote. Flashpoint saves us over $80 million in fraud losses every year. $80 million. Their proactive approach and sharp insights are crucial in keeping our financial institutions secure. They're not just a solution, they're a strategic partner helping us stay ahead of cyber threats. Wouldn't you like a partner like that? It's no wonder Flashpoint is trusted by both mission critical businesses and even governments worldwide, because not everybody has their own intelligence service. Well, now you do with Flashpoint. To access the industry's best threat data and intelligence, visit Flashpoint IO today. That's Flashpoint Flash, flash point, P O I N T dot and it's dot IO. Okay. Flashpoint dot I O. The best data for the best intelligence. We thank him so much for supporting security now. Really, it's a good match, right? Because we're both in the same business. And we thank you for supporting security now by telling them if they ask, oh, yeah, I heard it on Security Now. Yeah, it was. It was on Steve Show. That helps us. That way we can say, see, see, we're sending you traffic. All right, Steve, you gotta explain the title.
- [131:14]
Steve Gibson
Okay, so the way things are going, it looks like I'll be needing to set up, well, I guess what I would call a sacrificial lamb.
- [131:24]
Leo Laporte
Oh, no. Oh, I'm so sorry.
- [131:26]
Steve Gibson
Yeah, running the current. Which is to say the latest Windows. The last thing I would use for myself would be such a machine. Because Microsoft really does appear to be pushing well past the limits of what is acceptable practice for me. You know, Windows Recall was a perfect case in point. If the industry hadn't pushed back so loudly and quickly, they may have delivered that first disaster. Who knows? But it occurs to me that if this podcast is going to continue to be as relevant as it has been in the past, it's becoming clear that I'm going to need to have a machine that's running what the rest of the unwashed masses are running, which is to say, you know, the latest version of Windows. There was a time when creating a sacrificial lamp PC meant exposing the machine to the Internet without protection. As we know the half life of such machines is best is best measured in seconds, and not many of those. But the way the Windows desktop environment has been evolving today, the creation of a sacrificial Lamp PC means just exposing a machine to Microsoft. The need for such a machine became clear when I encountered the news that Microsoft has silently enabled the use of its users Microsoft Office Word and Excel document content for training its AI models. Rather than being straightforward and calling this something like I don't know, how about AI training? They obscure it behind the title Microsoft Connected Experiences. Now how the hell would anyone ever know that that means that they're training AI models connected experiences. And that's my point. This is what Windows has become. At the moment I'm reporting this blind because I have no way to verify the reporting that I've seen. At the moment I don't have a Windows 11 machine and that's going to have to change. But okay, so here's what we know in Microsoft's documentation for their so called connected experiences. Under the topic Connected experiences that analyze your content, they write Connected experiences that analyze your content are experiences that use your Office content to provide you with design recommendations, editing suggestions, data insights and similar features. The key phrases are analyze your content and connected. But connected to what and to where? That appears to mean what they're reporting on. This states, which is that the connection is to some AI which is doing the analyzing and being trained against Windows users Office document data. Now add to this the fact that it's been reportedly enabled by default, because of course it has. And I should say since this the Show Notes went out last night, I have heard back from listeners who found this stuff enabled by default. So this reporting is confirmed and they turned it off. Okay, it seems clear that just as a great many people are made uncomfortable by the idea of having Windows Recall silently collecting and analyzing everything they do on their computers, some Windows users may not be interested in having Microsoft's AI being trained on the content of their otherwise private Word and Office Excel documents. First, I'll note where this Connected Experiences setting is located, since they clearly want their Windows users to have ready access to this potentially significant privacy setting. So under File in an Office application, you choose Options. Under Options, go to Trust Center. In the Trust center, select Trust Center Settings. There you'll find Privacy options, which you need to select in order to get to the Privacy settings. And on the Privacy Settings page there's a section for optional Connected experiences where you should find a checkbox labeled Turn on optional connected experiences which all regular users will reportedly find and a bunch of our listeners have has been thoughtfully enabled for you. By default, users whose machines or Microsoft accounts are managed by their organization may not have these options showing, and Microsoft appears to confirm this on their own website where under the topic choose whether these connected experiences are available to use, they write, you can choose whether certain types of connected experiences, such as Connected Experiences that download online content, are available to use. How you make that choice depends on whether you're signed into Office with a Microsoft account, such as a personal Outlook.com email address, or with a work or school account. If you're signed in with a Microsoft account, open an Office app such as Word and go to File Account Account Privacy Manage Settings okay, now note that that's a very different path from what I had first shared from the reporting on this, it turns out, and I've heard from our listeners, both are correct. You can get to the proper setting either way, and Microsoft's is a shorter path. File Account Account Privacy Manage Settings Although maybe once you get to Manage Settings, then you go to Privacy Settings. I don't know. Anyway, if you've got it, you'll be able to find it. And they said under the Connected Experiences section, you can choose whether certain types of connected experiences, such as experiences that analyze your content, are available to use. If you don't go to Manage Settings, all connected experiences are available to you. In other words, all your content gets analyzed. So there it is. What's apparent nowhere is that Connected Experiences is a euphemism for we're going to share all of your Office documents to train an AI in the cloud in order to make Office smarter for you and of course, for themselves. So, talking about content retention, they write most connected experiences don't retain your content after performing their function, although I should tell you, there's about 50 of them to help you accomplish a task. But there are a few exceptions. In those cases, Microsoft retains the content for as long as your account exists and it's used to support, personalize, or improve that connected experience. Now, as I write this, part of me wonders whether I'm just becoming an old curmudgeon. Why not just, you know, enjoy all of the many benefits of having Microsoft watching everything I do on my PC, thus allowing me to scroll back in time and ask questions about things I did in prior years, and sending my document content to the cloud to train their AIs so that it can provide me with more relevant stories on Edge's homepage, more relevant search results in Bing, and more relevant advertising on my Windows Start menu. And of course I'm not being facetious when I say that many Windows users might actually want all of that. I get it. You know, just as they many may have been enjoying having Candy Crush, Soda Saga or whatever, all that flippy tile nonsense is under Windows 10, along with Xbox crap that refuses to be removed. I've never owned an Xbox, but it has taken up residence on my Start menu. Nevertheless, it seems clear that an alternative view of Windows is apparently an all encompassing, deeply connected entertainment portal that also has some productivity applications. And really, that's fine. It's just not for me. I mentioned a while back about the eventual move I would make to Windows 10 when I finally decide to retire this Windows 7 machine that still works great. I was briefly thinking that a server edition might allow me to avoid all of this commercial crap before I remembered that I had tried that years ago when I wanted my desktop to be running the identical code as GRC's servers, but I had encountered many instances of desktop software refusing to install on server editions. Some of our listeners have since suggested that I take a look at the Enterprise editions of Windows 10, explaining that unlike even the professional editions, the Enterprise editions are also free of Xbox and other unwanted nonsense. As I was digging around the Microsoft's documentation, I was encountering all of the places where Microsoft has been and is installing AI. Microsoft is essentially aizing every nook and cranny of Windows 11 and their office suite. I have no doubt that a memo went out a year or two ago stating that AI was coming and that it was the future, and that once it had arrived, it was here to stay. Therefore, every single Microsoft Product Manager and Product Planning team within Microsoft was hereby being tasked with figuring out anything and everything that adding AI to their offerings could do, and then to get going on implementing all of that immediately. While that will turn Windows into you know what, I have no idea. I know that it won't be any machine that I'm sitting in front of while I produce these weekly Security now podcasts, nor while I'm working on code for the DNS benchmark, the beyond recall product, or Spinrites 7, 8 and 9 and beyond. But it's also clear that I need to stay in touch with the Frontier, or as many have called it, the Bleeding Edge. For now, I want to be certain that those listeners of ours, and I know there are many of them, who may also dislike the idea of Microsoft sharing their Office content with their AIs in the Cloud. While acknowledging that this is being done by default, and that in many cases the data is being retained indefinitely, will at least be informed of this new behavior and would know that they have the option of deliberately disconnecting their Windows experiences from Microsoft before we go move.
- [143:35]
Leo Laporte
On, because I know you want to finish this up, but it's not. I think you're implying that this is being used for training LLMs for other people to use. I don't think that's what this is. No, this is asking permission, just as.
- [143:52]
Steve Gibson
A spell checker to train against your own data. Right.
- [143:55]
Leo Laporte
So that it can. So a spell checker tells you whether you've misspelled a word. In order to do that, it needs to actually look at the words you're typing. A grammar checker needs to look at the words you're typing. Well, Leo, that's what it's doing.
- [144:07]
Steve Gibson
This comes back to your original assessment of AI, right? It's just a spell checker.
- [144:12]
Leo Laporte
Well, yeah. I mean, so what Microsoft's offering you with these things is you're designing a power. It's kind of clippy on steroids. You're designing a PowerPoint and says, hey, you know, I could. I see what you're trying to do here. Would you like this image? It's that kind of thing. We'll have to check into this. I don't think it's sending it to their. You know, a lot of content is, you know, LinkedIn content is being sent to train LLMs. You know, the New York Times is being. Is suing because they say Open Eye used it to train LLMs. I don't think that's what this is. I'll have to check more in more.
- [144:47]
Steve Gibson
Detail about how much containment of the data.
- [144:51]
Leo Laporte
They say they'll retain it because that's information you've provided that you just like a cookie is that might be useful down the road.
- [144:58]
Steve Gibson
Well, all of your previous documents that have been used to train an AI model that they maintain. I guess.
- [145:06]
Leo Laporte
Yeah, but it's. But that the real question is, is it the AI model is going to be used by others, which I don't think it is because it would immediately be a problem in all businesses or is it an AI model that you will then be able to use for yourself?
- [145:18]
Steve Gibson
Yeah, probably we need to look at the terms of service and like actually read the fine print.
- [145:24]
Leo Laporte
I'll ask Paul and Rich tomorrow. But my sense is it's not, you know, going to send it out to their own LLM servers and train their own servers.
- [145:33]
Steve Gibson
Well, I.
- [145:33]
Leo Laporte
That would exfiltrate your own data. It is for for is basically for your use. Just as a spell checker or grammar checker. It's for your use.
- [145:42]
Steve Gibson
Well, they're retaining something and they're saying that they're retaining so it is being sent to them.
- [145:47]
Leo Laporte
Yeah. After performing don't they don't do it. There are after performing a function to help you accomplish a task. But there are a few exceptions. They retain your content for as long as your account exists, implying that it's attached to your account.
- [146:00]
Steve Gibson
Right.
- [146:01]
Leo Laporte
And it's used to support, personalize or improve that connected experience. Your experience, in other words, not for other people. But. But I I will check into that because I think it is an important distinction. It's like clippy it Clippy if in the day would have asked the same permissions. Hey, I'd like to keep track of everything you're doing so I can offer you suggestions. It's like that except it's on steroids. Right.
- [146:24]
Steve Gibson
Right.
- [146:25]
Leo Laporte
Anyway.
- [146:25]
Steve Gibson
Anyway, I was done. I just wanted to wish all of our listeners who celebrate Thanksgiving and I know Leo and all the Twit crew join me in wishing everyone the best holiday. And with this particular opportunity to spend time, which is precious with your family.
- [146:40]
Leo Laporte
And friends and don't argue about things.
- [146:43]
Steve Gibson
And we'll be back in December for more.
- [146:45]
Leo Laporte
And tell them to use a password.
- [146:46]
Steve Gibson
Rancher.
- [146:48]
Leo Laporte
Thanks, Steve. Have a great Thanksgiving. All our love and best wishes to you and Laurie and have a great time and we'll see you in December.
- [146:56]
Steve Gibson
Yay. Just only a week away next week.
- [146:59]
Leo Laporte
Don't get too concerned about that. We'll see you next week.
- [147:03]
Steve Gibson
Thank you, Steve.
- [147:05]
Leo Laporte
You can watch Security now as we do it live every Tuesday right after Mac break weekly. That's roughly 1:30pm Pacific, 4:30 Eastern, 21:30 UTC. And we stream live on yes, eight different channels now our club Twit members can watch and chat along with it with us in the discord. But there's also a YouTube channel dedicated to Twit Live. That's YouTube.com twit live. You can chat there too. We have chat there too. As we do on x.com as we do on facebook.com we stream live and you can chat with us live there. I see TikTok occasionally Tick Tock commenting coming through kik.com all of these have chats associated with the video and I have a unified chat that I can see all of it. Have I left anybody out? TikTok x, Kik, Facebook, LinkedIn, YouTube. Oh, Twitch TV. I left them out you can also chat there. That's if you're watching live now most people don't watch live, they like to watch after the fact. That's why we put copies of the show on our website TWIT TV SN we have audio and video. Steve also has a show on his website GRC.com he has an unusual version a quarter bandwidth 16 kilobit version for the bandwidth impaired. He also has human written transcripts are very good. Elaine Ferris does those so you can read along as you listen or Steve talked about last week you can use it to search and he has a 64 kilobit audio that's all@grc.com while you're there check out Spinrite version 6.1 the world's best mass storage performance enhancer recovery utility and maintenance utility. It does all of that and if you have a earlier copy you can get 6.1 for free. If you don't get it now because you if you've got mass storage you need need spin rate. Lots of other free stuff at this site including shields up which is a great way to test your router. I really love his new valid drive which tests USB thumb drives that you buy on Amazon to make sure they actually have the storage capacity that that is claimed surprisingly often they do not. Valid drive will do that and that's absolutely free. Plus lots of other freebies. Fun information. Steve site's really great. Grand. One more thing on our site actually two more things. One is we're doing the best of Anthony for this show. I think we are for the holidays. Yes we are. So if you have a moment on this show that you thought was from 2024 you thought was oh, we got to redo that. We're looking for little clips to put in our year end best of security. Now all you have to do is go to the website TWiT TV Best of Give us as much information as you know but don't get, don't get thrown by the form because we're asking for everything. But you don't have to give us everything. Even just say hey, that time when Steve and Leo tried to do the Vulcan salute, I remember that. That was great. Even that's a good start if you remember the day, the time of year, the climate, whatever will help us do a best of It's a lot of work but our team likes to put those together or well, we don't know if they like it. We make them put those together at the end of every year so we can give the Staff the holidays off. Help us do that. The other thing I'd like you to do is go to our Club Twit page. Twit tv Club Twit. There's some new things in Club Twit if you're not a member. We now offer a two week free trial which is a great way to see what you get for your $7 a month. You could also when you sign up, you'll be getting a code that is a reference code and every single person who signs up using your code gives you a free month. Do they get anything? They get like a discount or anything for using your code. Hey, it doesn't matter. They get the excitement, the thrill, the satisfaction, the deep rooted satisfaction of knowing they're a member of Club Twit, the best podcast network in the world. Seven bucks a month gets you ad free versions of all the shows, extra content we put anywhere else we don't put anywhere else. Cries from my cat down the actually everybody gets that. Please join the club. It helps us financially. It looks like 2025 is going to be even rockier than 2024 was. The good news is the club now pays about half of our payroll, which is fantastic. Thank you. Help us out. Twit TV Club Twit. Seven bucks a month. It's worth it for the great cut. Thanks to Anthony Nielsen who's filling in today for Benito Gonzalez who's taken some time off for the holidays. Appreciate your work Anthony. Thanks to everybody for joining us and I hope you will tune in next time next week for security now. Bye bye. Security now. Now AT T Mobile get four 5G phones on us and four lines for $25 a line per month when you switch with eligible trade ins, all on America's largest 5G network. Minimum of 4 lines for $25 per line per month with auto pay discount.
- [152:20]
Steve Gibson
Using debit or bank account.
- [152:21]
Leo Laporte
$5 more per line without autopay plus taxes and fees and $10 device connection charge phones via 24 monthly bill credits for well qualified customers. Contact contact us before canceling entire account to continue bill credits or credit stop and balance on a required finance agreement.
- [152:31]
Steve Gibson
Due bill credits end if you pay.
- [152:33]
Leo Laporte
Off devices early ctmobile combination.