← All TWiT.tv Shows (Audio)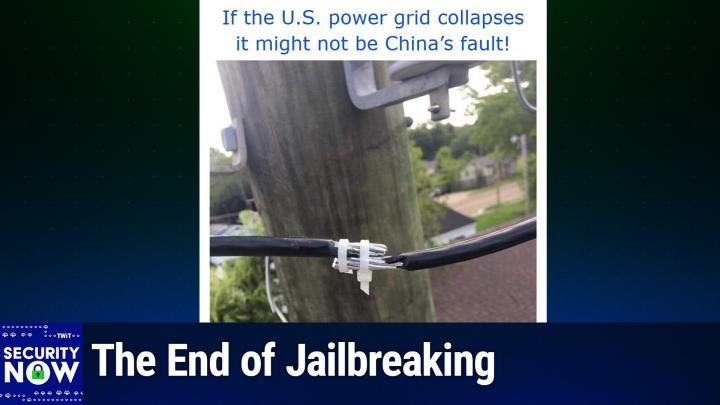
Loading summary
Transcript263 lines
- [00:01]
Steve Gibson
It's time for Security Now. Steve Gibson is here. A great program for you. The results from Pwned to own 2025. Millions of dollars at stake. The rising abuse of a graphics format that actually could really be problematic. And how One hacker used OpenAI's models to find zero day flaws. A technique that's definitely going to be on the rise. All that more coming up next on Security Now.
- [00:33]
Leo Laporte
Podcasts you love from people you Trust.
- [00:38]
Steve Gibson
This is TWiT. This is Security now with Steve Gibson. Episode 1028 recorded Tuesday, June 3rd, 2025. AI vulnerability hunting. It's time for Security Now.
- [00:56]
Leo Laporte
Woohoo.
- [00:57]
Steve Gibson
The show we, I don't know, celebrating insecurity since 1964. No, the show we cover your privacy, your security, how computers work, a little sci fi and some health news too with this guy right here, Steve Gibson.
- [01:13]
Leo Laporte
Of GRC.com the things that interest us is basically yeah, but we stay on topic.
- [01:20]
Steve Gibson
So I like it being wide ranging. I think people enjoy all the your. It's about your brains and you have such good brains. We, we want to dine on them something.
- [01:31]
Leo Laporte
There is a little bit of sci fi talk. Somebody reminded me of a, of, of a classic sci fi movie and then that of course caused me to think of the three other classic sci fi movies. And by classic I mean 1955, 1956, 1970. If they're, they're movies that everybody knows but if you don't then you have an assignment. Oh. Because I mean these things like you know, like those of us who know know about the Krell and know about monsters from the ID and know about and know about folks.
- [02:11]
Steve Gibson
These are terrible movies.
- [02:12]
Leo Laporte
Oh they're fantastic movies. Oh my goodness. They're ch.
- [02:20]
Steve Gibson
I mean if you, if you're, if you have take it in the right spirit, I guess it's fun to watch them. I mean they're not like it's not like 2001 A Space Odyssey.
- [02:30]
Leo Laporte
Way better.
- [02:31]
Steve Gibson
Okay, okay, stay tuned. You're gonna learn what Steve's picks are.
- [02:37]
Leo Laporte
We will be talking about that but as I promised last week because we, we did a. We tackled a big topic. There were some things I didn't get to. We're getting to them this week. We're going to Talk about the PWN to own 2025 hacking competition which for the first time was held in Berlin. We've got the results from that a couple weeks ago. PayPal seeking a newly registered domains patent which I think is very clever but I worried that they're patenting it because they shouldn't. We've got a really cool inside look at a long term expert iOS jailbreaker who has given up and we're going to look at why. Also the rising abuse of of SVG scalable vector graphic images. And who put this spec together and why. Because it's insane. We've got some interesting feedback from our listeners, as I said. I will touch on and Leo and I will discuss our varying views on classics of a couple classic sci fi movies that are just, I think are fantastic. But then we're going to take a deep dive into how OpenAI's O3 model discovered a previously unknown remotely executable zero day exploit in the Linux kernel.
- [04:16]
Steve Gibson
Oh my goodness.
- [04:17]
Leo Laporte
And what this means for AI vulnerability hunting, which is the title of today's podcast. Wow. So it's. Wow. It's a guy who did this, he understands AI. He, he's been interested in vulnerability hunting and development. He. Well, I don't want to step on the news, but it's a really, really, really interesting story. And of course we have a picture of the week that is one for the history books. I think everyone is going to get a big kick out of it.
- [04:55]
Steve Gibson
So, yeah, if the good guys can discover vulnerabilities with AI, so can the bad guys.
- [05:03]
Leo Laporte
And I do make the point that if the, if the AI is used before the release of the software, then there won't be vulnerabilities for the bad guys to find.
- [05:16]
Steve Gibson
Good point.
- [05:16]
Leo Laporte
So I realized for a while I was thinking, oh, this is bad. I mean, that there's a symmetry here. But no, actually, because you don't have to let it go until the AI has a chance to go through it. So yeah, I think I've been using.
- [05:30]
Steve Gibson
Claude code and AI to write tests, which I think is a really good use of AI to. To. Because it's an independent eye looking at your code.
- [05:39]
Leo Laporte
That's exactly what I was going to say. Yes. I mean, the reason I don't test my own code, I've got a whole bunch of neat guys who are pounding on it is I can't. I know how it works. I don't press the button at the wrong time. I don't want to cause a race condition presses. I go, why did you do that? Well, it was there.
- [05:59]
Steve Gibson
Oh, in the middle of a. Oh my God. All right, we'll get to that in a moment. I always look forward to this every Tuesday. I'm glad you're here. And I know you're glad you're here too. Our show today Brought to you by another company. I'm very glad to have here our sponsor Material. Actually, if you get material, you'll be glad you have it. It's a multi layered detection and response toolkit for email. Email of course, number one vector for bad things happening, phishing and so forth. And if you're a cloud based business, almost everybody is. We are certainly. Your cloud office isn't just another app, it's the heart and soul of your business. The problem is traditional security tools assume everything's on prem right and that means you're vulnerable. They treat email and cloud documents as afterthoughts. So your most critical assets are exposed without any protection. Not if you have material. Material transfer Cloud workspace protection with a revolutionary approach that goes beyond traditional security paradigms. Dedicated security for modern workspaces ensures purpose built protection specifically designed for Google Workspace and Microsoft 365. Now what's cool about this is they can do this without forcing you to pass everything through their filters. Because both Microsoft 365 and Google Workspace provides very capable APIs to that allow them to protect you without you giving up your privacy. Complete protection across the security lifecycle. That means defending your organization before, during and after potential incidents, not just attempting to prevent them. Material allows you to scale a security without scaling your team. Using intelligent automation to multiply your security team's impact. They provide security that respects how people work and eliminates that impossible choice or seemingly impossible choice between robust protection and productivity. It's not a trade off anymore, not with material. They deliver comprehensive threat defense four different ways, four critical capabilities. They've got phishing protection, of course, you know, that's kind of table stakes. But they're using AI just like we were talking about. AI power detection that identifies sophisticated attacks. It's not looking for something it's seen before, it's looking for attacks. And it's very good at this. They also help you with data loss prevention, intelligent content protection and sensitive data management. You also get posture management so you identify misconfigurations, risky user behaviors and identity protection. Comprehensive control over access and verification. Those are kind of the four key areas. The head of security at figma, they use Material. He said this. It's rare to find a modern security tool with a pleasant usable ui. Being at figma, we obviously are attracted to well designed interfaces. Materials interface was just so smooth, so slick. It doesn't get in your way. That's really the point. You no longer have to give up productivity for protection. From automatic threat investigation to custom detection Workflows Material converts manual security tasks into streamlined intelligent processes. They provide visibility across your entire digital workspace, allowing security professionals to focus on strategic initiatives instead of endless alert Triage. It's a partner your team will love working with. Protect your digital workspace. Empower your team and secure your future with material. Visit Material Security to learn more and book a demo. That's Material Security. That's all you need. Material Security. We thank him so much for supporting Steven Security.
- [09:52]
Leo Laporte
Now you started off talking about email which reminded me of something that I wanted to say. Yes. Yesterday evening 17,568 pieces of security now email. Wow. Well attempted to go out. Oh I looked a little bit later and 650 some had bounced which never happened.
- [10:21]
Steve Gibson
That's a low bounce rate. That's not terrible.
- [10:23]
Leo Laporte
It's normally five because the system's working really well and so forth. Anyway I thought what the what as you would say and I checked first what for a reason I have no explanation for Yahoo decided that we were a bad start blocking you email server so some Cox because of course you know Cox sold themselves to Yahoo so there were some cocks but mostly so I just wanted to let our listeners know I'm sorry if you're a Yahoo email subscriber and you did not receive the security now show notes I tried to send them, you know your ISP wouldn't let me 17,000 other people got the show notes.
- [11:09]
Steve Gibson
Well I know because last night Lisa said oh Steve's working hard. She got the email now I get it but I don't look at it.
- [11:18]
Leo Laporte
That's right.
- [11:19]
Steve Gibson
I don't want to see the picture.
- [11:20]
Leo Laporte
I don't want to spread the surprise. And Leo, I have to say this one there could only have been one caption for this picture. I gave this picture the caption if the US power grid collapses it might not be China's fault.
- [11:35]
Steve Gibson
Oh I love these fun with power pictures. Let me scroll up because I haven't seen it yet.
- [11:40]
Leo Laporte
If the US power grid collapses it might not be China's fault.
- [11:46]
Steve Gibson
Oh my God. That's an interesting way to make a splice. Do you think that would. I guess it would work.
- [11:54]
Leo Laporte
Oh well as long as you don't have a windstorm or something. Now I actually.
- [12:01]
Steve Gibson
Maybe a little electrical tape around it just you know just for extra support.
- [12:07]
Leo Laporte
Presumably this person, the lineman who did this splice intended to come back soon. We don't really know anything about the story here.
- [12:19]
Steve Gibson
You know I like though he was careful to trim the tails of the of the zip ties because, you know.
- [12:24]
Leo Laporte
And we've got two zip ties. There's another one. Oh look, person. No, no, I meant, I meant there are two up there on, on the main spot.
- [12:32]
Steve Gibson
Oh yeah, yeah, yeah, yeah, yeah. So that's double protection.
- [12:36]
Leo Laporte
Yeah, yeah, that's right. Because you know, one tie wraps not good enough. You would need. Need to do two. Yeah. Wow. So those who aren't zip ties.
- [12:46]
Steve Gibson
Yo go. You describe it. Yeah, yeah.
- [12:47]
Leo Laporte
For, for. For someone who is unable to see this, we have a. A We can tell because it's sort of in the background is a telephone pole, a power pole with power lines. A house in the background. You hope that they've got their fire insurance paid up. And a naked bare splice of two cables where maybe an inch and a half of each of the cables, the rubber insulation has been been cut off and they're put next to each other and then held in. Held in place with a pair of white plastic zip ties. So now I actually think that these are. This may be ground wires and so they're.
- [13:41]
Steve Gibson
That wouldn't be too bad.
- [13:42]
Leo Laporte
They're less. It's less of a concern than you might otherwise think. But boy, there's really no exclusive excuse for something that is certainly slipshod at best.
- [13:54]
Steve Gibson
Well, has anybody's ever used zip ties? I mean that's. That could slip out easily and it's not protected from the rain and I. Yeah.
- [14:01]
Leo Laporte
And there, there's nothing, nothing to prevent either side being pulled on that. Right. As you said, it's just going to slide right out.
- [14:09]
Steve Gibson
So yeah.
- [14:10]
Leo Laporte
Anyway, I got a kick out of it. The u. S. Power grid collapses. Might not.
- [14:15]
Steve Gibson
It's all hell together with might not be shown.
- [14:17]
Leo Laporte
It might be mo. Wow. Yeah. Okay, so last week I promised to catch us up with the results from the recent pwned own hacking competition which as I mentioned was held for the first time in Berlin. In their announcement of this before the event, Trend micro, the organizer of this now 18 year old competitive hacking series which we've been following for the entire 20 years of this podcast they wrote. While The Pone to Own competition started in Vancouver in 2007, we always want to ensure we are reaching the right people with our choice of venue. Over the last few years, the Offensive Khan conference in Berlin has emerged as one of the best offensive focused events of the year. And while cansecwest has been a great host over the years and our longtime listeners will remember, that's where we've talked of it being held held in the past Cansec west, it became apparent that perhaps it was time to relocate our spring event to a new home. With that, we are happy to announce that the enterprise focused PWN to OWN event will take place on May 15th through 17th, 2025 at the offensive Khan Conference in Berlin, Germany. While this event is currently sold out, we do have tickets available for competitors and we believe the conference will also open a few more tickets for the public. The conference sold out its first run of tickets in under six hours, so it should be a fantastic crowd of some of the best vulnerability researchers in the world. Okay, so now that was two and a half weeks ago. What happened? Before I run through what happened, I want to remind everyone the context of what we're going to hear. These are the results. When today's upper echelon most skilled penetration hackers go up against fully patched systems. What always strikes me is that the targets here are not old junk routers past their end of life that the FBI says everybody should stop using or should have years ago. In every case, these targets, what these guys are successfully cracking open are fully patched modern systems like what we're all using right now. So for me, this serves as a reminder that to a large extent, the only reason. This is also why my model for security is unfortunately Swiss cheese or a sponge. To a large extent, the only reason we have any appearance of security is that none of these most skilled hackers want to attack us because all the evidence suggests they could get in if we let them at our system. Hopefully these are not. Most of these are local attacks on systems, not remote code exploits. So thank goodness for that. So here's what happened two and a half weeks ago in Berlin. I'm just going to, to keep this short, I'm going to run through the list of things that happened. There's absolutely no chance that I could pronounce any of the names of these people. So I apologize. I'm just going to talk about the teams that they're in because the names of their organizations, you know, are pronounceable. I just, I didn't want to mangle their name so badly. So here's what happened in chronological order. It was a three day event, so we've got three days of this. First, devcore's research team used an integer overflow to escalate their privileges on Red Hat Linux, earning $20,000 and two Master of PWN points. In other words, this was somebody who sat down at today's fully patched Red Hat Linux and got root, even though all I Mean endless effort has gone into making that not be possible. Whoops. Second, although the Summoning team successfully demonstrated an exploit of Nvidia Triton, the bug that they used that they discovered independently was also known to Nvidia, but Nvidia had not yet patched it. So that still qualifies because these guys independently discovered a bug that was in the public space. So anybody's fully patched Nvidia systems would have succumbed. That earned them $15,000 and one and a half master oppone points. Star Labs SG combined a Use after Free. They use the initials UAF and Use after Free is significant. We're going to run across this a couple times. Unfortunately I'm going to actually be talking about it in depth before I go into a great deal of detail at the end of the podcast. So things are are. In fact I'm using it before I describe it, as opposed to using it after freeing it. So these guys STAR Labs SG combined a Use after free and an integer overflow to escalate to system level on Windows 11. That got them $30,000 and three master opponent points. Researchers from theory were able to escalate to root on Red Hat Linux using a different a different hack with an info leak and a Use after free. One of the bugs used was an end day, meaning that it had it. It was known to the to the world, but not to them at the time. But they got $15,000 and one and a half master opponent points. The first ever winner of the AI category. I forgot to mention that this was. I mentioned it last week. This is the first time that artificial intelligence was considered in scope for the Pone to own conference. So the first ever winner in the AI category was the Summoning team. They successfully exploited Chroma to earn $20,000 and two Master opponent points. In a surprise to no one, the conference holders wrote that Marcin Wiazowski's privilege escalation on Windows 11 was confirmed. He used an out of bounds right to obtain system privileges and also obtained $30,000 for himself and three master opponent points. Their enthusiasm was rewarded as Team Prison Break. They were the best of the best. 13th used an integer overflow to escape Oracle's VirtualBox VM and execute code on the underlying OS. Again fully patched, you know, like as current as you could have it be. And they broke out of the vm. Why? Because they wanted to.
- [22:05]
Steve Gibson
Because they could.
- [22:06]
Leo Laporte
Because they for them. Okay, fine.
- [22:09]
Steve Gibson
Do you think? Well, that's another reason they did it. How much did they make out of that?
- [22:13]
Leo Laporte
$40,000. Oh, and four master opponent points. So yes, they had motivation. And we'll be talking about motivation here in a minute. That's a perfect lead in. Leo Vettel Cybersecurity targeting Nvidia Triton Inference Server successfully demonstrated their exploit. It was again, Nvidia must be a little slow in getting their, their, their updates out because again, this is Nvidia and it was known to the vendor though had not yet been patched. They earned $15,000 and one and a half Master Opponent Points. A researcher from out of bounds earned $15,000 for a third round and and three master opponent points by successfully using a type confusion bug to escalate privileges on Windows 11. STAR Labs used a use after free to perform their Docker desktop escape and execute code on the underlying os. So broke right out of Docker's Containment and earned themselves $60,000 and six master opponent points.
- [23:21]
Steve Gibson
And breaking out of VMs or Dockers seems to be the big money maker, right?
- [23:26]
Leo Laporte
Yeah, well, because that's the cloud attack. I mean everything in the cloud is, is VMs and containment. And so if you can get to the underlying VM in a cloud environment, that's golden. And that was just day one. Fuzzing Labs exploited Nvidia's Triton. The exploit they used was also known to the vendor. Again, Nvidia get with the program here, get these patches out. But that still earned them $15,000. Vattel Cybersecurity combined an AUTH bypass and an insecure deserialization bug to exploit Microsoft SharePoint, earning $100,000 and 10 master opponent points. Star Labs SG was back with a single integer Overflow to exploit VMware's ESXi, the first in PWN to own history, earning them $150,000 and 15 Master of PWN points. As you said, Leo, breaking out of VMS and containment, that's where the money is. And this is an enterprise focused competition. So that's why we're seeing VirtualBox and VMware, ESXi and so forth. Palo Alto Networks researchers used an out of bounds right to exploit Mozilla Firefox to earn $50,000 and five master opponent points. The second win in the AI category goes to the team from Wiz Research who leveraged a use after free to exploit Redis, earning $40,000 and four master opponent points. In the first full win against Nvidia Triton inference server researchers from Querious Secure used a four bug chain to exploit Nvidia's Triton. Their unique work earned them $30,000 and three master opponent.
- [25:27]
Steve Gibson
And Nvidia said oh, we didn't know about that one.
- [25:32]
Leo Laporte
There's one we didn't know. So. And if we did, we wouldn't have patched it anyway. Yeah, right idiots. Vital Cybersecurity used an out of bounds right for their guest to host escape on Oracle VirtualBox that get them $40,000. Another researcher from Star Labs SG used a use after free bug to escalate privileges on Red Hat Enterprise Linux that earned them $10,000. Although Angel Boy from Dev Corps research team successfully demonstrated their privilege escalation on Windows 11, one of the two bugs used was known to Microsoft. Nevertheless that guy got $11,250. Although the team from FPT Nightwolf successfully exploited Nvidia's Triton, the bug once again they used was known to Nvidia but but had not yet been patched. Still $15,000 richer as a result. Former Master of PWN winner Manfred Paul used an integer overflow to exploit Mozilla Firefox's renderer. His excellent work earned him $50,000. Wiz researchers used an external initialization of trusted variables bug to exploit the Nvidia container toolkit. Star Labs researchers used a TOC TOU that's a time of check, time of use, race condition to escape the virtual machine and an improper validation of array index for the Windows privilege escalation. So they they got out of a Windows VM and then escalated their privileges to full admin, earning them $70,000 and nine master opponent points. Reverse Tactics used a pair of bugs to exploit ESXi, but the use of the uninitialized variable bug collided with a previous entry. Nevertheless, the integer overflow was unique and earned them $112,500 and 11.5 Mastropone points. We have two left. Two researchers from Synactive used a heap based buffer overflow to exploit VMware Workstation. That got them $80,000. And in the final attempt of PWN to own Berlin 2025, Milos Ivanovich used a race condition bug to escalate privileges to system, which is to say admin on Windows 11. His fourth round win netted him $15,000 and three master opponent points.
- [28:15]
Steve Gibson
I would love to watch this. It would be so it is.
- [28:18]
Leo Laporte
And that's why it sold out in six hours. Leo.
- [28:22]
Steve Gibson
Wow.
- [28:22]
Leo Laporte
They put the tickets online. Bang. Gone. You know, we want to sit there because it is all done live on stage with the guys and their laptops, you know, sweating over the keyboard hoping that their exploits going to work there were a total of 26 individuals exploits demonstrated while some of them were known to their respective vendors, largely Nvidia. In every one of those cases, patches for them had not yet been made public, so they still qualified as new independent discoveries. Trend Micro summed up the event writing and we're finished. What an amazing three days of research. We awarded an event total of $1,078,750. They said congratulations to the STAR Labs SG team for winning Master Apone. They took home $320,000 and 35 Master Opponent points during the event. They wrote we purchased from the researchers and disclosed to their respective vendors 28 unique 0 days.
- [29:36]
Steve Gibson
Wow.
- [29:37]
Leo Laporte
7 of which came from the AI category. Thanks to Offensive Con for hosting the event, the participants for bringing their amazing research and the vendors for acting on the bugs quickly. Except in the case of Nvidia.
- [29:53]
Steve Gibson
Although our chats saying that many of the things you just described have been patched in the most recently like Ubuntu just up did a bunch of patches.
- [30:03]
Leo Laporte
No, that's, that's exactly what happens here is that that that Trend Micro is, is thanks to sponsors of the event and there are many enterprise level sponsors who provide the money to back this Trend Micro. So this is like a bug bounty, sort of like a live bug bounty event. And of course they do run Trend Micro runs the zero day ZDI is the bug bounty program. So, so this is sort of like that, you know, the bug bounty in real time as a conference format. So they're buying these exploits from the guys who find them and then immediately turn around and report them to the vendors and say by the way Microsoft, we have three new zero days in Windows 11 that allow people just to cut through all your security. Microsoft goes oh well we'll get around to fixing these days.
- [31:03]
Steve Gibson
I wonder if the companies that benefit from this like Microsoft and Nvidia, they sponsors, do they? They are, yeah. Okay.
- [31:11]
Leo Laporte
Yeah.
- [31:12]
Steve Gibson
So some of that money is coming from them. I mean this is, they want this to happen.
- [31:15]
Leo Laporte
Yeah, they are, they are corporate sponsors.
- [31:17]
Steve Gibson
Yeah.
- [31:18]
Leo Laporte
And you know it occurs to me as I was running through this first of all again now that everyone has a, has a taste for this, think about that, that the, these are, you know, these are the best of the best. You know that that is said. But it just says that here we're talking about you know, docker containers and VMware ESXi which is state of the art virtual machine containment. And these guys go eh.
- [31:49]
Steve Gibson
Well they're pretty good.
- [31:50]
Leo Laporte
They are, they are good.
- [31:52]
Steve Gibson
You know of course they work all year and save these up because they want to make this money.
- [31:57]
Leo Laporte
I was listening to you guys talking about code authoring on Mac break weekly before the podcast.
- [32:05]
Steve Gibson
Vibe coding. Yeah.
- [32:06]
Leo Laporte
Yes, vibe, vibe coding. And one thing occurred to me and that is that what I heard was for example in the case of Alex and Andy, who are not, you know, real like aren't themselves code authors, they are now using AI to create apps to interact with the AI to create apps. We've talked in the past on the bug bounty side about the possibility of our listeners generating some extra revenue on the side if they were to find vulnerabilities. Well, today's podcast is AI vulnerability hunting and it's an interesting possibility that we, there may be people listening who are not at this level, who you know and would never say that they were at the level of pwned owned competition winners, but who may well be able to work with various large language models and systems which are offered for which bug bounties are offered and use AI to help them find some problems that they would some bugs that they wouldn't otherwise find and generate some revenue. So you don't know until you look.
- [33:36]
Steve Gibson
And, and you want these guys working white hat, not black hat obviously.
- [33:41]
Leo Laporte
Yes, they're good. Yes, yes.
- [33:44]
Steve Gibson
Give them a reason to.
- [33:46]
Leo Laporte
Boy. But it just goes to show again that like here are all these mainstream actively maintained in, except in the case of Nvidia products that are, you know, hackers sit down and say I'm, I want to find a way in. And they can.
- [34:05]
Steve Gibson
I imagine you get more points for a more difficult.
- [34:08]
Leo Laporte
Yes.
- [34:09]
Steve Gibson
Task.
- [34:09]
Leo Laporte
Yes, well, and more cringe worthy. I mean if you're breaking out a VSDI VM, that's worth a lot of money.
- [34:18]
Steve Gibson
Yeah.
- [34:19]
Leo Laporte
And, and, and, and I'll also understand too that is it, was it Zerodium that are the bad guys that are buying these bugs?
- [34:27]
Steve Gibson
Yeah.
- [34:27]
Leo Laporte
You could, you could sell that to Zerodium for a million ton of money.
- [34:31]
Steve Gibson
Yeah, yeah, yeah. They're take, they know they're taking a cut and pay to be good guys.
- [34:36]
Leo Laporte
Yeah, yeah, yeah.
- [34:38]
Steve Gibson
What an interesting. I love this. Yeah.
- [34:41]
Leo Laporte
Speaking of a cut and pay, would.
- [34:43]
Steve Gibson
You like, would you like a little, a little, a little something extra?
- [34:51]
Leo Laporte
Re up my caffeine. We can all tell them I'm a little low energy at the moment.
- [34:56]
Steve Gibson
Actually, I want to talk about a very interesting sponsor of ours, outSystems, the leading AI powered application and agent development platform. For more than 20 years the mission of Outsystems has been to give every company the power to innovate through software. Okay? And as as AI has advanced low code solutions have gotten smarter. This is, this is their time. Let me tell you, IT teams, as you well know, I'm sure have two choices when it comes to software. You can buy off the shelf SaaS products and you know you're up to speed right away, but you lose flexibility and frankly a lot of competitors using the same product. So you lose differentiation. So that's the buy side. Or you could build it yourself and trust me, as somebody who has chosen the build, it's a lot of time, a lot of money and you may not get the best quality software. Build versus buy this is. For decades this has been the conundrum. But now there's a third way thanks to AI. The fusion of AI low code and DevSecOps automation into a single beautiful development platform. That's what Outsystems does. This is incredible. It's not build versus buy anymore. You can actually build custom applications using AI agents as easily as buying generic off the shelf sameware. And what's nice about ad systems is as a base you automatically get flexibility, security, scalability. You know those come standard, right? With AI powered low code teams can build custom future proof applications at the speed of buying with already built in fully automated architecture security. The integrations you want are there, the data flows, all the permissions you need. That's because Outsystems is good. Outsystems is the last platform you'll ever buy because you can use it to build anything and customize and extend your core systems to boot. Build your future with Outsystems. Such a cool idea. Visit outsystems.com TWIT to learn more. Outsystems.com TWIT and we thank him so much for supporting security now and Mr. Now fully caffeinated Steve Gibson, are you ever fully caffeinated, Steve? Really?
- [37:27]
Leo Laporte
Yeah, there have been times when I dare not have any more.
- [37:31]
Steve Gibson
Over caffeinated.
- [37:32]
Leo Laporte
Over caffeinated. Okay, so the online publication Domain Name Wire posted some interesting news under the headline PayPal wants patent for system that scans newly registered domains with the subheading patent describes automated crawler and checkout simulator to spot fraud in newly registered domains. And I just think this is extremely clever. The publication then explained PayPal filed a patent application back at the end of November 2023. Okay, so again, a year and a half. It was just published last Thursday, May 29th. The patent application describes a method to proactively detect scam websites which have historically created a problem for PayPal by automatically examining newly registered domains. That's just so clever. And simulating checkout processes. Oh, wow, isn't that neat? The US patent application 18521 909, titled Automated Domain Crawler and Checkout Simulator for Proactive and Real Time Scam Website Detection, describes a system designed to tackle online fraud at its earliest stages. According to the application, PayPal's system monitors newly registered domains to identify those that include checkout options. The technology then performs simulated checkout operations on these sites, mimicking a genuine user's experience. This simulation specifically looks for domain redirections during checkout processes because this is a common tactic scammers use to conceal fraudulent activity. If a redirection occurs, PayPal's system checks the redirected domain against its database of known scam merchants and flagged accounts. Domains linked to previous fraudulent activities trigger a scam alert, allowing PayPal to promptly label and potentially block transactions from these websites. PayPal notes that scammers often set up new, seemingly legitimate websites to mask their operations by proactively identifying suspicious redirections and cross referencing them against scam related merchant accounts. The method allows it to significantly reduce that risk, which again, this is. It's just brilliant. It's like one of those, why didn't I think of that kind of things. But my first thought upon reading this was that while, you know, it is a very cool and clever idea, it feels wrong to issue a patent for this. I mean, or, I don't know, it makes me a little nervous since the idea's use really should remain freely available for any similar service that is subject to this sort of abuse to employ.
- [40:55]
Steve Gibson
I don't think they can patent it because there's lots of prior art. We talked last week about next DNS, which we both use as a DNS server, right? Right on their security page. And I have it turned on. I know, I'll tell you how I know. They have a switch that says block newly registered domains. Domains less than 30 days ago known to be favored by threat actors. This has been around forever. And the reason I know about this, my daughter created a new store online store and she wanted me to check it and I couldn't get to it. I, for the longest time I thought, oh, you're, it's broken, it's broken. Then I realized, oh, wait a minute, when did you register that domain? She said, last week. I said, okay, it works. It really works. But PayPal didn't invent this, I guess is the point.
- [41:42]
Leo Laporte
Well, they're going further though.
- [41:44]
Steve Gibson
They could patent that process.
- [41:46]
Leo Laporte
Sure, yeah, yeah. What they're trying to patent is the notion of proactively, yes, examining the site, the actual content of the site, simulating a purchase event and then watching to see what happens with that purchase event. And my concern is that, that, that this ought to be in, I mean, this ought to be in the public for the public good. Now, it is true that not all patents are obtained for competitive advantage and used to prevent competitors from using the invention. It might be, and this would be great if it were true, that PayPal is being civic minded and desires to obtain the patent preemptively to prevent anyone else from patenting what I think is a very clever and useful solution, which, and then, and then they might prevent PayPal from doing the same. So let's hope that if this automated, you know, newly registered domain scrutiny concept were to become commonplace, that PayPal would not prevent other commercial entities from availing themselves of similar solutions. Because this is, you know, clearly a good idea. And what is really cool is that if this became pervasive, then it basically, it would shut this down as something that scam sites could get away with doing. Because, you know, registering domains is not expensive, but it's not free. And if it stopped working enough to justify them going through all this effort, they would just, you know, give up, you know, give that up. As, you know, generally as security is increasing, we're, we're seeing things that used to work, no longer working for the bad guys. And so they sort of say, okay, fine, well we'll go try to, you know, make money maliciously somehow else. Anyway, very cool patent and, and I thought a very clever new idea. Okay, I ran across an important story that I wanted to share because it comes from an extremely unlikely source, a true and unabashed vulnerability exploit developer and hacker who's been fixated upon Apple and iOS for years and who has been right in the thick of things. The story is important because from this person who has the deepest of adversarial knowledge and understanding of iOS, we learn why, as he puts it, about kernel exploitation, and we'll get to his quote a little bit later. But he said, quote, those days are evidently long gone, meaning successful exploitation, he said, with the iOS 19 beta being near weeks away and there being no public kernel exploit for iOS 18 or 17 or whatsoever. In other words, Apple quietly changed the world. Since this was no easy feat. I'm sure this is known and appreciated among those at Apple who made this happen as well as Those in the exploit community whose many tricks no longer work. But it's not something, this is not something that I think has ever really been made or has come completely clear to the rest of the world. Because you really need to get down on the weeds to understand this, because this is where these sorts of changes need to happen anyway, they did happen. So, okay, now part of the problem I have with, with sharing this is that because what Apple did really is down in the weeds. That's, that's where we have to go in order to get a really deep understanding. But as I was absorbing the, the this hacker's name is Seguza. S I G U Z A he's Swiss. As I was absorbing what he wrote and, and, and explained, I was thinking, okay, by the end of this podcast our listeners are going to have enough of an understanding about what it means to double free a kernel object to have this make more sense. But it turns out no idea what that means. I know, but, but I'm actually going to be talking about it at the end of the podcast which, and as I was putting this together, I had already written the end, so I knew that I was going to be explaining what this stuff was, except that now I'm talking about it before I've explained it. So as I said, things are a little ordered upside down here. But, but it, but you know, the AI vulnerability hunting really does need to be our main topic and I like having it at the end. Anyway, I'm going to share enough of this that everyone's going to get a sense, a good sense for what Apple has done. But at some point you're just going to have to let it kind of some of the details wash over you and not worry about the details. I'm going to, so I'm going to settle for sharing enough of Seguza's non technical backgrounding for everyone, as I said, to get a real, a good sense for the environment that this, this hacker had historically been swimming through and for how he now observes that has totally changed Apple, has totally changed the game. And this sort of happened without anyone really. I mean, you know, WWDC happens every year. It's what, next Monday, right Leo? And you guys are gonna be covered.
- [48:09]
Steve Gibson
It is. We're gonna stream the Steam, the keynotes.
- [48:11]
Leo Laporte
And, and five years ago, just five years ago in 2020, everything was different from the way it is today. So he wrote, I'm an iOS hacker/security researcher from Switzerland. I spend my time reverse engineering Apple's code, tearing apart security, MITIGATIONS writing exploits for vulnerabilities, or building tools that help me with that. Sometimes I speak about it at conferences, sometimes I do lengthy blog posts with all the technical details. Sometimes my work becomes part of a jailbreak, and sometimes it never sees the light of day. Okay, Two weeks ago he wrote a blog posting blog posting titled Tachyon the Last Zero Day Jailbreak. It starts off, he said, hey, long time no see, huh? People have speculated over the years that someone bought my silence or asked me whether I had moved my blog post to some other place. But no, life just got in the way. This is not it. This is not the blog post which I planned to return to, or return with, he probably means. But it's the one for which all the research is said and done. So that's what you're getting. I have plenty more that I want to do, but I'll be happy if I can even manage to put out two blogs a year, he said. Now, Tachyon. Tachyon is an old exploit for iOS 13.0 through 13.5 released in uncover where unco is a numeric O V E R and if you, in fact if you go to, if you put uncover.dev unc numeric 0v e r.dev what you will find there is a jailbreaking kit. Because that's where a lot of this guy's work goes. He's one of the guys who was always figuring out how to jailbreak iOS and he said was released in Uncover that is this tachyon exploit, version 5.0.0 on May 23, 2020, exactly five years ago. So this is his five year anniversary of the Tachyon exploit. He said, oh, okay. So anyway, I'm going to interrupt here to remind everyone that once upon a time, end user jailbreaking was a thing. It was common. Mostly it was for people wanting to make unauthorized changes or customizations to their devices to run, you know, unsigned code or side loading apps to get apps installed not from the App Store or just to have the freedom of digging around in their iOS or Android devices. Innards in this case, it's all Apple and iOS with this guy. So this Swiss Seguza hacker was one of the Uncover developers. In fact, he contributed to a number of other jailbreaking products as as we'll see. So and Uncover describes itself as the most advanced jailbreak tool and it's on the homepage it says iOS 11.0 through 14.8. Uncover is now at version 10.0.2 and under what's new it notes quote add exploit guidance to improve this version 8.0.2 added exploit guidance to improve reliability on a 12 through a 13 iPhones running iOS 14.6 through 14.8 and fix exploit reliability on iPhone XS devices running iOS 14.6 through 14Point8 and then under the About Uncover they write Uncover is a jailbreak, which means that you can have the freedom to do whatever you would like to do to your iOS device, allowing you to change what you want operate within your purview. Uncover unlocks the true power of your idevice. Then lower down on the homepage they also remind us under jailbreak legality that quote it is also important to note that iOS jailbreaking is exempt and legal under DMCA. Any installed jailbreak software can be uninstalled by re jailbreaking with the restore root FS option to take Apple's service for an iPhone, iPad or iPad touch that was previously jailbroken. Okay, so now back to Seguza. As I said, one of the guys behind this uncovered jailbreak as well as some others where he's explaining about Tachyon. He says it was fairly standard of tachyon. It was a fairly standard kernel lpe, meaning a local privilege escalation for the time. But one thing that made it noteworthy is that it was dropped as a zero day affecting the latest iOS version at the time, leading Apple to release a patch for just this bug a week later. So, you know, so this was, you know, and remember this was just five years ago. It's he he also comments later, looking back now how much the world has changed in five years, where he describes tachyon as quote, a fairly standard colonel local privilege escalation. Like that's just what we did back then. So this was, you know, the work that these guys were doing were the sorts of things that was causing Apple to respond immediately. And of course we know why our idevices were having to update themselves and restart so often back then. He says this is something that used to be common a decade ago, but has become extremely rare. So rare in fact that it has never happened again after this. Another thing he writes that made it noteworthy is that despite having been a zero day on iOS 13.5, it had actually been exploited before by me and friends, but as a one day at the time. And that's where this whole story starts, he says in early 2020 pone to owned and he says now that that that's pwn t0wnd is a jailbreak author not to be Confused with Pone to own that the event. So this, this person whose handle is Pone to Owned, he said, contacted me saying he'd found a zero day reachable from the app sandbox, meaning any app running on iOS could break out of the app containment, which is very valuable, and was asking whether I'd be willing to write an exploit for it. At the time, I'd been working on Checkrain, C H e K R A1N and Leo. It's, it's interesting. If you look at the Checkrain site, it's C H E C K R a dot IN the logo will immediately be familiar. We of course, talked about this at the time. We were covering all these things back, back in the day, as they say. Remember that logo on the site?
- [56:43]
Steve Gibson
Chess pieces. Yeah.
- [56:44]
Leo Laporte
Yep, he said. And so he was, he said at the time, I've been working on Check Rain for a couple of months, so. And that's, you know, another exploit. So I figured he wrote, these guys.
- [56:57]
Steve Gibson
Would have gotten over the leet speak spellings by now.
- [57:02]
Leo Laporte
It's like, oh, that's so clever.
- [57:04]
Steve Gibson
I used a one instead of an I. I know. Oh my gosh.
- [57:09]
Leo Laporte
So, well, we don't know, right? I mean, yeah, they write pretty well, but we don't know.
- [57:14]
Steve Gibson
Maybe they're just kids.
- [57:15]
Leo Laporte
Yeah, he said. So I figured going back to Colonel Research was a welcome change of scenery, and I agreed. Meaning he agreed to. To. To accept what this Pone Pone to Owned author had the zero day that he discovered the vulnerability. So, so this Seguza decided, you know, said, yeah, I will create an exploit for, for the vulnerability. Okay. So he said, but where did this bug come from? He said it was extremely unlikely that someone would have just sent him this bug for free with no strings attached. Meaning because they were so valuable back then, he said, and despite being a jailbreak author, despite he wasn't doing security research himself, so it was equally unlikely that he would discover such a bug. And yet he did. The way he managed to beat a trillion dollar corporation, meaning Apple was through the kind of simple but tedious and boring work that Apple. This guy writes, sucks at regression testing because, you see, this has happened before on iOS 12. Sock Puppet was one of the big exploits used by jailbreaks. It was found and reported to Apple by Ned Williamson from Project Zero, patched by Apple in iOS 12.13 and subsequently unrestricted on the Project Zero bug tracker. Right, because Apple patched it, so Project Zero published it, but against all odds, it then resurfaced on iOS 12.4 as if it had never been patched. So Apple had a regression. Aha.
- [59:16]
Steve Gibson
That means they made some changes to the code that brought back a bug they had already fixed, right?
- [59:23]
Leo Laporte
Right. And he wrote, I can only speculate that this was because Apple likely forked their XNU kernel to a separate branch for that version and had meaning for version 12.4 and had failed to apply the patch there. But this made it evident that they had no regression tests for this kind of stuff, a gap that was both easy and potentially very rewarding to fill. And indeed, after implementing regression testing for just a few known one days, Pwn got a hit. In other words, okay, so in other words, back in early 2020, this jailbreak developer, realizing that Apple sometimes inadvertently reintroduced previously repaired bugs, took it upon himself to check for anything else that Apple might have inadvertently reintroduced and struck pay dirt. That's when Pohn asked Seguza if he'd be interested in developing that into a fully working exploit. At this point in Seguza's blog he drops into a very detailed instruction level description of precisely how this exploit works. We cannot follow him down there on an audio podcast, and it's just as well, because really understanding it requires developer level knowledge of the perils and pitfalls of multi threaded concurrent tasks and the complex management of dynamically shared and dynamically allocated memory among these tasks. And as I mentioned, believe it or not, everyone actually will understand a great deal more about that by the time we're finished here today. Because we're going to get to that, but we haven't gotten to it yet. The sense, however one comes away with is that as recently as only five years ago, in 2020, things were a were still a free for all, with hackers really having their way with iOS, and there appeared to be little that Apple was able to do to prevent them, because Apple was constantly being reactive. They were patching zero days that were being found and found and found. And then add to that the possibility of old previously known and fixed flaws returning and it's clear why iPhones, as I said, were needing to be restarted so often. So resurfacing after his deep dive into the exact operation of this and exploitation of this zero day vulnerability which Pwn had given him, which allowed them to then update their uncovered jailbreak to once again work on the latest fully patched iOS, which then forced Apple to immediately respond. Seguza continues the scene as he expressed it obviously took note of a full zero day exploit dropping for the latest signed version. Meaning of iOS, he wrote. Brandon Azad, who worked for Project Zero at the time, went full throttle, figured out the vulnerability within four hours and informed Apple of his findings. Six days after the exploit dropped, synactive published a new blog post where they noted how the Original Fixed in iOS 12 introduced a memory leak and speculated that it was an attempt to fix this memory leak that brought back the original bug, he says, which I think is quite likely. Then nine days after the exploit dropped, Apple released a patch. He said, and I got some private messages from people telling me that this time they'd made sure that the bug would stay dead. And I think those were private messages from inside Apple is what he's saying, because otherwise how would anybody know that Apple had made sure it stayed dead? They even added a regression test for it to their XNU kernel. And finally, he writes 54 days after the exploit dropped, a reverse engineered version dubbed Tardion was shipped in the Odyssey jailbreak, also targeting iOS 13.0 through 13.5. But by then the novelty of it had already worn off. WWDC 2020 had already taken place and the world had shifted its attention to iOS 14 and the changes ahead. And he writes, and oh boy did things change. Exclamation point. IOS 14 represented a strategy shift from Apple. Until then they had been playing whack a mole with first order primitives, but not much beyond the kernel underscore, task restriction and zone underscore require were feeble attempts at stopping an attacker when it was already too late, had a heap overflow over release on a C object type confusion, pretty much no matter the initial primitive, the next target was always mock ports, and from there you could just grab a dozen public exploits on the net and plug their second half into your code. Obviously this guy has had his sleeves rolled way up for quite a while, so that this is just the game that all of these hackers were playing. He says iOS14 changed this once and for all, and that is obviously something that had been in the works for some time, unrelated to Uncover or Tachyon. And it was likely happening due to a change in corporate policy, not technical understanding. Okay, and here we're going to get a bunch of technical jargon, but don't worry about following it all, just sort of let it wash over you. As I said, Seguza writes, perhaps the single biggest change was to the allocators K Alloc and Z Alloc. Many decades ago, he writes, CPU vendors started shipping a feature called Data Execution Prevention. And actually, I don't think it was decades ago, maybe, but you know, for someone that young, you know, everything feels like it was 100 years ago. That's right.
- [66:45]
Steve Gibson
I remember Depp. Yeah, we actually talked about it on the show. So.
- [66:48]
Leo Laporte
Yeah, so it wasn't.
- [66:49]
Steve Gibson
I don't think it was that long ago.
- [66:51]
Leo Laporte
Right. And he says, he. So. So data execution prevention, Dep. Because people understood that separating data and code has security benefits now, Right. You know, in other words, there's a huge security benefit if we're able to prevent the simple execution of data as if it were code, since bad guys can send, you know, anything they want as data. So Seguza continues, Apple did the same here. That is the separation, he says, but with data and pointers instead, they butchered up the zone map and split it into multiple ranges, dubbed K heaps. The exact amount and purpose of the different K heaps has changed over time, but one crucial point is that user controlled data would go into one heap, kernel objects into another. And I'll just interject that heap is terminology from computer science. It's the place from which memory is allocated. So think of Apple's creation of multiple heaps as creating multiple separate and separated regions of memory for allocation. Seguza writes for kernel objects. They also implemented sequestering, which means that once a given page of the virtual address range is allocated for a given zone, it will never be used for anything else again until the system reboots. Now that's a big architectural change and it's brilliant. I'll explain in a second. He writes. The physical memory can be released and detached if all objects on the page are freed, but the virtual memory range will not be reused for different objects, effectively killing kernel object type confusions. Add in some random guard pages, some per boot randomness in where different zones will start allocating, and it's effectively no longer possible to do cross zone attacks with any reliability. Of course this wasn't perfect from the start, and some user control data still made it into the kernel object heap and vice versa. But this has been refined and hardened over time to the point where Clang now has some built in underscore XNU features to carry over some compile time type information to runtime to help with better isolation between different data types. And here it is. But the allocator wasn't the only thing that changed. It was the approach to security as a whole. Apple no longer just patches bugs, they patch strategies. Now you were spraying K message structs as a memory corruption target as part of your exploit. Well, those are signed now, so that any tampering with them will panic the kernel. You are using pipe buffers to build a stable kernel read, write, interface. Too bad those pointers are packed now. Virtually anytime you used an unrelated object as a victim, Apple would go and harden that object type. This obviously made developing exploits much more challenging. Well, obviously to those kind of guys. To the point where exploitation strategies soon became more valuable than the initial memory corruption. 0 days okay, in other words, he's saying that Apple had succeeded in raising the bar so high because instead of patching vulnerabilities, they were patching strategies. They had cut off and killed so many of the earlier tried and true exploitation strategies that hackers were needing to come up with and invent entirely new approaches. Avenues, entire avenues of exploitation were finally being eliminated. At the architectural level, Apple was no longer merely patching mistakes, they were redesigning for fundamental unexploitability. Seguza continues Quote but another aspect of this is that we with only very few exceptions, it basically stopped information sharing dead in its tracks. Before iOS 14 dropped, the public knowledge about iOS security research was almost on a par with what people knew privately, meaning it was out in the ether. Everyone was talking about it, it was on forums and so forth. It was being shared and exchanged, he said, and there wasn't much to add. Hobbyist hackers had to pick exotic targets like KTTR or secure ROM in order to see something new and get a challenge. These days are evidently long gone with the and here's the quote from earlier with the iOS 19 beta being merely weeks away, and there being no public kernel exploit for iOS 18 or 17 whatsoever, even though Apple's security notes will still list vulnerabilities that were exploited in the wild, every now and then, private research was able to keep up. Public information has been left behind. I assume what Segusa means here is that iOS has finally become so significantly tightened up, meaning like big time, that it is no longer possible for casual developer hacker hobbyists to nip at its heels any longer. It's no fun anymore. All of the low hanging fruit has been pruned, and the fruit that may still be hanging is so high up that it's no fun to climb that high. The changes, the, the, the, the chances are that you'll get all the way up there and come away empty handed. Seguza concludes by writing, it's insane to think that exploitation was so easy a mere five years ago. He says, I think this really serves as an illustration of just how unfathomably fast this field moves. And he finishes, I Can't possibly imagine where we'll be five years from now. So his webpage notes his involvement in Phoenix, a JailBreak for all 32 bit devices on iOS 9.3.5 created by Thimstar. And he said, and himself something called totally not spyware. A web based jailbreak for all 64 bit devices on iOS 10 which can be saved to a web clip for offline use. Spice and unfinished untether for iOS 11 uncover, which we talked about, an app based jailbreak for all devices running iOS 11.0 through 14.3. And he said, I'm not an active developer there, but I wrote the kernel exploit for iOS 13.0 through 13.5 checkrain, a semi tethered boot ROM jailbreak for a 7 through a 11 devices on iOS 12.0 and up. And he said the biggest project I've ever been a part of and by far the best team I've ever worked with. So now here is Seguza, who obviously has, you know, deep involvement in this, in this, what was previously a hobby industry, essentially saying that this game is over and that it ended a few years ago with iOS 14 and the changes that Apple made and some deep change in their security strategy within Apple. The Apple finally made the required fundamental changes and all public kernel exploits disappeared. He says at the end he wants to thank everyone he's learned from before these changes hit because it's time to move on. Apple finally got very, very serious, stopped believing that they could ever get there, you know, get ahead of the bugs using traditional system design, and bit the bullet to make fundamental changes that were required to change the game forever. And it did. So anyway, I thought this was some really terrific perspective from someone who was, you know, once on the inside, but there is no longer any inside to be in because Apple fixed iOS.
- [77:03]
Steve Gibson
Let's remember that it's not, it probably wasn't solely to stop these guys. Apple's biggest challenge were zero click attacks from nation states right through NSO Group and Pegasus. And I think they were really, I mean that's what Blasto was all about. They were really trying to protect, protect their phones from that kind of exploit. And it's just a nice side effect that jailbreakers couldn't get in either. I wonder though, if you gave these PWN to own guys $150,000 or $250,000, do you really think there's no way in?
- [77:40]
Leo Laporte
It's a good question. I mean we do still hear that.
- [77:43]
Steve Gibson
Pegasus is around, still around, Celebrite is still there. Downloading the contents of people's iPhones. Nobody knows how. They don't publicize that, obviously.
- [77:54]
Leo Laporte
Oh Lord no.
- [77:57]
Steve Gibson
I mean Apple probably has some thought. And that's what Apple's patching, right, is, is these.
- [78:03]
Leo Laporte
Well, and remember we, we've covered a couple years ago, we covered one of these where there was some obscure range of hardware access in an undocumented area of a chip which by like somehow somebody reverse engineered this and figured it out and was able to use it.
- [78:25]
Steve Gibson
To access some weird random iPhone grid of numbers. Yeah, I like what this is about though, which is that Apple isn't specifically trying to patch flaws. They're changing how the system works to be less vulnerable. Vulnerable. And I think that's the right approach.
- [78:43]
Leo Laporte
Right, right. Traditional software development, traditional software architecture never needed to be this hardened.
- [78:51]
Steve Gibson
Right.
- [78:52]
Leo Laporte
And Apple adopted that technology for their device, you know, when it was created and said, okay, well we won't have any bugs. Well, you're going to have bugs.
- [79:04]
Steve Gibson
There's always bugs.
- [79:05]
Leo Laporte
And so what they finally had to do was to go back and say, okay, we gotta stop allowing these things, these bugs to be turned into exploits.
- [79:15]
Steve Gibson
Yeah, that's right. Yeah.
- [79:18]
Leo Laporte
And so they changed the architecture.
- [79:20]
Steve Gibson
It's a better way of thinking of it. I think you're right. Yeah, I think you're exactly right. What an interesting story. I wonder, do you think this guy really retired? Or maybe he went to high school and got busy.
- [79:31]
Leo Laporte
That's right. Let's take a break and then we're going to talk about the unbelievable design of scalable vector graphics.
- [79:40]
Steve Gibson
I mean they're everywhere. If there's a problem.
- [79:43]
Leo Laporte
Oh Leo, you're not gonna. This is a head slapper.
- [79:47]
Steve Gibson
Get ready, stay tuned. You know, this comes back. I always am reminded how the lesson you have taught us time and time again, interpreters are really vulnerable and I suspect that's what we're going to hear about. But we'll find out in just a little bit. Steve Gibson, he's getting refreshed. While I'm telling you about our sponsor, a great little company with a big name, Big id. They're the next generation AI powered data security and compliance solution. Big ID is the first and only leading data security and compliance solution to uncover dark data through AI classification, identify and manage the risk and then remediate the way you want. You can use it to map and monitor access controls and to scale your data security strategy. Along with unmatched coverage for cloud and on prem data sources, BigID seamlessly integrates with your existing tech Stack and allows you to coordinate security and remediation workflows. You could take action on data risks to protect against breaches. And I said the way you want, which means annotate it, delete it, quarantine it and more based on the data. And again, with everything you do with BigID maintaining an audit trail. Bigid works with Everybody. Partners include ServiceNow, Palo Alto Networks, Microsoft, Google, AWS and more. And with BigID's advanced AI models, you can reduce risk, accelerate time to insight and gain visibility and control over all your data. Intuit named it the number one platform for data classification and accuracy, speed and scalability. This is a big problem nowadays because we want to use our data right? I mean that data is a treasure trove, it's hugely valuable, but it's in a lot of different places, in a lot of different, you know, on prem in the cloud, all kinds of formats. Plus if you're going to use it for AI, maybe some of it's appropriate, some of it you don't want to use. It turns out now it's more important than ever to know what your data is, where it is and what you can do with it. If you're gonna, if you're gonna use an example client. I don't think there's anybody better than the United States Army. Imagine how much data, how diverse the data the army has collected over years in all sorts of ways, in all sorts of places. Big ID equipped the US army to illuminate dark data, to accelerate cloud migration, to minimize redundancy and to automate data retention. I can't imagine a bigger job than that. U.S. army training and Doctrine Command gave us the best quote. They said quote the first wow. This is a direct quote from US Army Training and Doctrine Command. These guys are pretty straight laced. They don't get excited very often. The first wow moment they said with BigID came with being able to have that single interface that inventories a variety of data holdings, including structured and unstructured Data across emails, zip files, SharePoint databases and more. The quote continues to see that mass and to be able to correlate across those. Completely novel. I've never seen a capability that brings this together like Big ID does. That's somebody at US Army Training and Dr. Command getting pretty darn excited about Big ID. CNBC did too. They recognize Big ID as one of the top 25 startups for the enterprise. Big ID was named to the INC 5000 and the Deloitte 500. Not just once, for four years running. The publisher of Cyber Defense Magazine says, quote, BigID embodies three major features we judges look for to become understanding tomorrow's threats today, providing a cost effective solution and innovating in unexpected ways that can help mitigate cyber risk and get one step ahead of the next breach. Start protecting your sensitive data wherever your data lives. @bigid.com SecurityNow Get a free demo to see how BigID can help your organization reduce data risk and accelerate the adoption of generative AI. Again, that's big I D.com SecurityNow Also, there's a free white paper that provides valuable insights for a new framework, AI TRISM T R I S M that's AI Trust, Risk and security Management to help you harness the full potential of AI responsibly. You can get that for free@bigid.com security now. Thank you Big ID for sponsoring the show and for all the stuff you do. Bigid.com Security now okay Steve, I gotta find out. Am I how much trouble am I in with svg? These are everywhere.
- [84:43]
Leo Laporte
I mean, yes, thus the cause for concern. So to to set the stage here back on February 5th Sophos headline with Scalable Vector Graphics Files Pose a Novel Phishing Threat Know before posted on March 12 245% increase in SVG files used to obfuscate phishing payloads on March 28, ASCS headline SVG phishing malware being distributed with analysis obstruction feature. On March 31, Mimecast wrote. Mimecast threat researchers have recently identified several campaigns utilizing scalable vector graphics attachments in credential phishing attacks. On April 2, Force Points headline An Old Vector for New Attacks How Obfuscated SVG Files reDirect victims on April 7, Keepawares headline SVG Phishing Email attachment a recent targeted campaign on April 10, Trust Waves writes Pixel Perfect Trap the surge of SVG born phishing attacks Viper Security Group's April 16 headline was SVG Phishing attacks the New Trick in the CyberCriminals Playbook. On April 23, Indexer blogs under Emerging Phishing Techniques, New Threats and Attack Vectors. And Last month, on May 6th, Cloud Force One, which is Cloudflare's security guys, posted under the headline SVGS the Hackers Canvas.
- [86:22]
Steve Gibson
Oh God.
- [86:24]
Leo Laporte
So. Oh boy. Like I said, holy smokes. Okay, all this leads to one question, and I mean this with the utmost sincerity and all due respect when I ask what idiot decided that allowing JavaScript to run inside a simple two dimensional vector based image format would be a good idea?
- [86:51]
Steve Gibson
Wait, what?
- [86:53]
Leo Laporte
Come on. What? Are you kidding me? Believe it or not, the SVG Scalable Vector Graphics file format based on XML can host HTML, CSS and even JavaScript. And it's all by design.
- [87:14]
Steve Gibson
So you could put arbitrary JavaScript in an SVG graphics file?
- [87:19]
Leo Laporte
Yes.
- [87:20]
Steve Gibson
And how does it get triggered?
- [87:22]
Leo Laporte
It runs by design. It is unbelievable when you open the file. When. No, when it's displayed.
- [87:31]
Steve Gibson
That's what I mean. Yeah. When it's. When it's used. Yeah.
- [87:33]
Leo Laporte
Okay, now, now let's just remember I was once famously on the receiving end of some ridicule for stating my opinion that the infamous Windows metafile vulnerability, which allowed WMF files to contain not only inherently benign interpreted drawing actions, but also native intel code. I said it was almost certainly not a bug, but a deliberate feature added as a cool hack back then to allow images to also carry executable code as we know the world, I wrote in the show notes went nuts. It lost its shit is the technical phrase when this Windows metaphile so called vulnerability was discovered, or rather rediscovered. And it was none other than Mark Russellovich, who also examined the native Windows metafile interpreter as I had, who concluded it sure does appear to have been intentional. Oh, wow.
- [88:42]
Steve Gibson
But you know what I think back to true type fonts which also execute.
- [88:46]
Leo Laporte
Code not in this way. They're. They, they are sandboxed. Yes, yes, they're. The true type was based off of PDF. That is an interpreted. Yeah, postscript.
- [89:01]
Steve Gibson
Yeah, Right.
- [89:02]
Leo Laporte
Postscript. Yes. Right. Postscript. Okay, so my point was that, okay, back in the early 1990s, before the Internet interconnected everything, which is what changed the landscape of security overnight, this would have been the idea of executable code in a WMF file would have been an entirely reasonable thing for Microsoft to do. Mark Russanovich and I both examined the WMF interpreter machine language and it was clear that that after the interpreter parsed an escape token, it would deliberately jump to the code immediately following that token and execute it. That's what the code was written to do. You can't make a mistake like that. Which is why Mark concluded it sure looks like it was intentional. Now I'm reminding everyone of this because bizarrely enough, we're back here again with a widely supported image file format that explicitly enables its displaying host to execute content on its viewer's PC when the file image is displayed. The only difference this time is that while this is still clearly a horrible idea, no one thinks it's a mistake. The SVG image file format first appeared back in 1991. The version 1.0 specification was finalized 24 years ago in 2001. Section 18 of the SVG specification is titled scripting and makes clear that SVG files are allowed to support ECMA script, which is the standards following JavaScript ECMA yeah, ECMA obviously given the headlines we've seen over just the past few months which I just read bad guys have figured out took them a while how to weaponize this built in scripting facility and are now using it with abandon. Yeah, and just one sample of the recent coverage and explanation of the problem I'm going to share. Here's what Cloudflare's Cloud Force One Security Group wrote on May 6th under their headline SVGS the Hackers Canvas. They were being a bit clever here, since the canvas is the term for the virtual surface upon which SVG graphics are rendered and in general the web. You know canvas is the term used for rendering on web browsers they wrote over the past year, Phishguard, which is a Cloudflare email security system, observed an increase in phishing campaigns leveraging scalable scalable vector graphics SVG files as initial delivery vectors, with attackers favoring this format due to its flexibility. Yeah, it's so nice to have script and the challenges it presents for static detection. SVGs, they write, are an XML based format designed for rendering two dimensional vector graphics. Unlike raster formats like JPEGs or PNGs which rely on pixel data, SVGs define graphics using vector paths and mathematical equations, making them infinitely scalable without loss of quality. Their markup based structure also means they can be easily searched, indexed and compressed, making them a popular choice in modern web applications. However, the same features that make SVGs attractive to developers also make them a highly flexible and dangerous attack vector when abused. Since SVGs are essentially code, they can embed JavaScript and interact with the document object model, the DOM. When rendered in a browser, they aren't just images, they become active content capable of executing scripts and other manipulative behavior. In other words, this is cloudflare writing this SVGs are more than just static images, they are also programmable documents. The security risk is underestimated, with SVGs frequently misclassified as innocuous image files similar to PNGs or JPEGs, a misconception that downplays the fact that they can contain scripts and active content. Many security solutions and email filters fail to deeply inspect SVG content beyond basic MIME type checks, a tool that identifies the type of file based on its contents, allowing malicious SVG attachments to bypass detection. They wrote We've seen a rise in the use of crafted SVG files in phishing campaigns. These attacks typically fall into three categories. Redirectors SVGs that embed JavaScript to automatically redirect users to credential harvesting sites when viewed. Wow, that's just wonderful. You display an image and it takes you somewhere else. What could possibly be Wrong with that? Second Self Contained Phishing Pages SVGs that contain full phishing pages encoded in base 64 rendering fake login portals entirely client side. Gee, what a terrific feature to have in an image. And finally, DOM injection and script abuse. They write SVGs embedded into trusted apps or portals that exploit poor sanitization and weak content security policies, enabling them to run malicious code, hijack inputs, or exfiltrate sensitive data. Wow, that's right. How many sites allow you to upload images? After all, what harm could an image do? And why does that SVG embed the term drop tables Given the capabilities highlighted above, they write Attackers can now use SVGs to gain unauthorized access to accounts. Okay, SVGs images, gain unauthorized access to accounts, create hidden mail rules, phish internal contacts, steal sensitive data, initiate fraudulent transactions and maintain long term access. They finished saying Our telemetry shows that manufacturing and industrial sectors are taking the brunt of these SVG based phishing attacks. Attributing attributing to over half of all targeted targeting. Observed financial services follow closely behind, likely due to SVG's ability to easily facilitate the theft of banking credentials and other sensitive data. To easily facilitate the theft of banking credentials and other sensitive data. The pattern is clear. Attackers are concentrating on business sectors that handle high volumes of documents or frequently interact with third parties. The article then goes into greater depth, but that's all I'm going to share here, since I'm sure by now everybody gets the idea and must be shaking their heads as I am. Essentially what this means is that SVGs provide another way of sneaking executable content into an innocent user's computer and in front of them to display things like bogus credential harvesting logon prompts that most users would just assume were legitimate because how would they know otherwise? Their computer just popped up as it often does, asking them for their username and password. So they sigh and type them in. They have no way of knowing or detecting that this is a JavaScript driven mini HTML and CSS web page that JavaScript in the signature logo just retrieved from a server in Croatia which would love to have them fill out its form, please. As I've often observed here, most users. Most PC users really have never needed to obtain any fundamental understanding of the computers that they now have come to utterly depend upon. Many of us here listening to this podcast grew up with PCs. We love them for their own sake, so we know and care about things like directory structures. Most users will ask, do you mean folders? They have, you know, no underlying grasp of what's going on and they don't want to. They don't, they don't want to need to know. They just want to use their PC to get them where they want to go. They want to use it as a tool to get whatever it is done. And of course the industry has not helped very much with this because there is no normal, right? You can't tell if something is abnormal because there's zero uniformity among sites and and site actions. If any of us were to open an email and receive a pop up from an email asking for authentication, we'd say, what? No. But the typical user would shrug and think, oh, okay, whatever. I guess I need to log into this just for some reason. Again, how would they know I don't have any solution to this problem? Chrome, Firefox and Safari might simply block script execution within SVG images. Yes, please. If, if there was a toggle that I could turn on that would turn off script running in SVGs, I would turn that on or off or something. But our browsers are less the problem than email. In their write up about detecting and mitigating this malicious misuse of SVG scripting, Cloudflare's Cloud Force One folks wrote, Cloudflare's email security have deployed a targeted set of detections specifically aimed at malicious emails, emails that leverage SVG files for credential theft and malware delivery. And remember that all of those headlines I read before were about phishing. These detections inspect embedded SVG content for signs of obfuscation, layered redirection and script based execution chains. They analyze these behaviors in context, correlating metadata, link patterns and structural anomalies within the SVG itself. These high confidence SVG detections are currently deployed in our email security product and are augmented by continuous threat hunting to identify emerging techniques involving SVG abuse. We also leverage machine learning models trained to evaluate visual spirit spoofing, DOM manipulation within SVG tags, and behavioral signals associated with phishing or malware staging. Okay, in other words, this is not easy to fix. I would just say no. I would just turn this off. No. Once upon a time, back in the early days when scripting was first happening, many of us Old timers simply ran the no script browser extension to block any scripting from running on websites. We were like, no thank you. We also noted when over time, as sites became increasingly dependent upon scripting, you know, that little noscript add on started causing more trouble than it was probably worth. And at the same time the security of our web browsers was steadily increasing. So it was probably good for us to run a no scripting window for a while. But it became obsolete and as browser security got a lot better, scripting became less of a concern. The big problem that Cloudflare and all the other security companies are seeing is from SVGs being delivered and displayed in email. It seems to me that what we want is email content to be as inactive as possible. So looking for any way of disabling scripting support for SVGs in email clients would seem to be a terrific first step given that the SVG designed the the SVG spec designed JavaScript on purpose in back in 2000 into the spec from the start and given that it's apparently being used for some legitimate purposes, I'm sure it's here to stay. But it might be nice to be able to turn it off. And I hope that the industry responds to this quickly and just starts saying no to running scripting in our SVG images. If, if things stopped running scripting, then designers would stop being able stop being able to rely on scripting in svg. You really just have to decide that it's a bad idea to have it. It's unbelievable.
- [104:07]
Steve Gibson
Yeah, you know the scripting that you can do in a TrueType. I mean TrueType does have conditionals and loops and stuff, but it doesn't have access to external data and it certainly can't send you to another page and.
- [104:21]
Leo Laporte
Your some SVG image is able to execute an HTTP request to pull content from Croatia or from where? From Russia or China.
- [104:31]
Steve Gibson
Yeah, that's clearly a problem.
- [104:32]
Leo Laporte
It's. It means. And that's one of the other things Leo, as I didn't get this into my my show notes, but arguably JavaScript in the year 2000 is different than JavaScript in the year 2025. Meaning we've been adding and adding and adding all this power to JavaScript. So back then it probably was not so insane to add a little bit of scripting enablement to think of all the power it gives you, right? Yes, but think of all the power it has received in the last 25 years. And as it turns out, well, maybe not such a good idea to have it in our images Any longer.
- [105:16]
Steve Gibson
Yeah, Amazing.
- [105:18]
Leo Laporte
You know what is a good idea?
- [105:20]
Steve Gibson
I know what a good idea would be.
- [105:21]
Leo Laporte
Before we get into our listener, feedback is remind people how this is all being brought to them.
- [105:28]
Steve Gibson
It is all being brought to you through the magic of svg, ladies and gentlemen. No, it's not. It's brought to you by Bitwarden. I mean, when you talk at security, you know, perhaps the single most important security tool in any company, in any individual's life, is your password manager. You do use a password manager, right? Of course you do. We've all got to remember a lot of passwords and it's bad, as you know, to reuse a password even once. It's also nice if you can, to use password lists, single sign on and pass keys. Well, Bitwarden does it all. They are the trusted leader in passwords, in secrets and in passkey management. They say secrets because you can store anything in your Bitwarden vault. API keys, ssh, public keys. In fact, they even have. I love this. They added this recently. SSH key generation and storage in Bitwarden. It's incredible. I love it. With more than 10 million users across 180 countries, over 50,000 business customers worldwide, Bitwarden continues to protect businesses and individuals everywhere. G2 consistently ranks at number one in user satisfaction. You can count me in. I am very satisfied. Every year on World Password Day, Bitwarden does a survey of users to find out, you know, how do we stand now on our understanding of how important passwords are and what we should do? This latest survey is wild because they section out the Gen Z members in the survey. These are adults who are probably digitally native. They all grew up with the Internet. And yet Gen Z has been found guilty of the single highest incidence of password reuse. The survey found that 72% of Gen Zers reuse. The 72% of reuse the same password across accounts. 79% of them know it's risky. They say, yeah, we know it's risky. Yet 59%, oh, get this behavior when they get to a site that, that has had a breach and the site has reset all the passwords, right? Oh, we had a breach. The passwords have leaked out. Reset your password. 59% of Gen Zers just recycle the existing password when they're updating the account. They don't. You ought to be using Bitwarden. Okay? And if you have employees in the Gen Z category, you really need to get it for your business. They just launched Access Intelligence. It's a new capability that Helps enterprises help employees do the right thing, proactively defend against internal credential risks and external phishing threats. Two core functionalities here. The first is Risk Insights, which by the way, eliminates alert fatigue because that's one of the problems, right? They go, okay, okay, okay, fine, yeah, yeah, yeah, yeah, I heard it. All right. Risk Insights allows IT teams to identify, prioritize and remediate at risk credentials without bombarding your employees with alert after alert after alert. They also have an advanced phishing blocker that does alert and redirects users from known phishing sites in real time using a continuously updated open source block list of malicious domains. So even if they are reusing their passwords when they try to use it on a phishing site, they'll be stopped. Okay, and then, you know, look, give them a password manager teacher, teach a Gen Z or to phish or something. What sets Bitwarden apart is that it prioritizes simplicity. It's easy to use because obviously if it's too complicated, nobody's gonna use it. It's easy to set it up in your business. It only takes a few minutes or in your house because you can import from most password management solutions just like that. And I think this is super important. Bit Warden is open source. That means their code can be inspected. Their full code base is gpl. It can be inspected by anyone. They also have it regularly audited by third party experts and they publish the full results of those audits. So, you know, Bit Warden is absolutely secure. They meet stringent security and compliance requirements. SOC2 type 2 GDPR, HIPAA, CCPA, ISO 270012002 and on and on. I think you and your business and your Gen Z employees deserve an effective solution for enhanced online security. Now what? Don't think I'm insulting Gen zers. I know many of you are. And I know you use Bitwarden if you're listening to security. Now, of course you use a password manager, but if you don't, or more importantly, if you know somebody who doesn't and maybe they're saying, oh, I don't know, I get started today with Bit Warden's free trial of a teams or enterprise plan. Protect your business. And when it's individuals, like if it's mom or dad or you know, cousin Al, tell them it's free forever across all devices. When you're an individual user, it's open source. Bitwarden.com twit bitwarden.com twit I love Bitwarden. I have not just passwords. Everything's in there, including SSH keys, API keys, secrets, passport, Social Security. Because it's safe, it's secure, and it's easy to use. Bitwarden.com twit for you, for your company. Do it today. You owe it to your gen Z employees. Bitwarden.com TWIT on we go with the show with Mr. Stephen.
- [111:17]
Leo Laporte
Okay, so we've got some feedback from our many involved and engaged listeners.
- [111:24]
Steve Gibson
Yes, yes.
- [111:25]
Leo Laporte
Kevin, who describes himself as a cloud security engineer in the healthcare space, wrote Steve, as everyone else states, thanks a ton for this podcast. It comes as a boon on Wednesdays, especially when I'm standing at my window realizing I forgot to take the trash to the curb. He thinks, well, at least I get to listen to security now.
- [111:45]
Steve Gibson
Must be a long walk to the curb.
- [111:47]
Leo Laporte
I was going to say that's yeah, I don't blame you for not wanting to take the trash out if it consumes the podcast. Yeah. He says, as a cloud security engineer in the healthcare space, I plan to block Echo encrypted client hello in our environment so that we can more easily snoop on our traffic before it leaves the network.
- [112:11]
Steve Gibson
Now.
- [112:12]
Leo Laporte
And understand snoop is meant like in the security management sense, right? He says. Otherwise we have to man in the middle ourselves. Oh, to decrypt and re encrypt all that traffic, which creates another place where unencrypted sensitive data is being handled and adds the complexity of managing an internal certificate authority. Right, because all of the browsers in the enterprise would have to have a certificate from the middle box that would be there used to intercept. He says, I love the idea of ECH for personal use, but as you mentioned, enterprises can really benefit from SNI header inspection to improve security visibility. Now, okay, Kevin is echoing this somewhat controversial side of ECH adoption. Right. The thing to remember is that he's specifically talking about an enterprise environment where, as we've noted in the past, organizations really ought to fix some written signage in a stripe across the top of everyone's display screen to remind them that they're using corporate bandwidth and corporate equipment and the corporate network, and that as such, everything they do, all the data they traffic while within the enterprise's environment is subject to inspection for the good of the organization. That is, you know, privacy is a is limited within that environment. So the furtherance of the absolute privacy that ECH helps Internet users obtain is really not appropriate within an enterprise, which does need to protect itself from dangerous Internet misconduct. And as Kevin also noted, if it became impossible to examine the TLS client hello handshake, which ECH would make impossible to determine the domain the enterprise's employees were connecting to. The enterprise's recourse. The only recourse they would have would be to fully proxy all TLS connections by inserting a middle box into every connection. And that would represent an even deeper intrusion since then all post connection data would also be decrypted, not just the domain that the user is wishing to connect to. So the enterprise environment is very different from that of home users, where I would argue privacy should absolutely reign. The idea that a residential ISP might be profiling and profiting from the sale of data that it snoops from its paying customers is something I find despicable. Yet we've been informed that that happens. So encrypting DNS and taking advantage of ECH to also encrypt the client hello handshake wherever and whenever it might be opportunistically available for the residential Internet user I think makes absolute sense and I can certainly understand Kevin's position in the corporation. It really, it does feel like ECH is going to have a tough time getting, you know, much traction. And again, it's only useful if you're behind a big aggregator like Cloudflare, because if, you know, if you go to GRC, doesn't matter if it says GRC.com in the in the handshake header. The only, the only website at the IP address you're going to which you can't hide is mine. Aaron Morgan said, hi Steve, I just listened to SN127. That's last week. He said regarding the AI pull request. Steven Tube is a principal software engineering manager at Microsoft and was is key in the development of. Net&c.
- [116:43]
Steve Gibson
I showed that GitHub dialogue to Lumareska who works at Microsoft doing he does copilot for Excel and Python. They said, oh, Tube's a big shot. I said, oh, okay. Yeah, we didn't mock him too much.
- [117:02]
Leo Laporte
Our listeners knew that too. Aaron wrote, he's widely known for his expertise in asynchronous programming, performance optimization and concurrent programming on. Net. And you can find YouTube videos of him writing async code in C from scratch as an example of his deep knowledge of both C Sharp, the language and the. NET framework. Aaron said, I suspect for this very reason he's on the list of code reviewers for AI generated pull requests. And in fact what hadn't occurred to me until just now is maybe this was him testing co pilot right in public view, like sort of going see.
- [117:44]
Steve Gibson
What you could do but and then.
- [117:45]
Leo Laporte
Giving it another prompt to say don't you think this is, you know, more of treating the symptoms? Anyway, Aaron said he's not going to let subpar code slip past and into the main branch. In fact, looking at those pull requests, he's he's the default assignee on three out of four. So I'm pleased to hear he's one of the go to reviewers and as an experienced dev, he's asking the AI the right questions because as you and Leo said, what was submitted was was junior dev level symptom targeting and not root cause solving. Unfortunately, the AI did not read between or even on the lines here and flubbed the review, he said Been a listener since episode one and a club twit member for a while now. While I don't have expectations of 2000 and beyond, please don't quit in the next six months. Regards, Aaron thank you for the note, Aaron. And for the record, quitting is not on the horizon.
- [118:47]
Steve Gibson
We'll try to make it to 1100 anyway.
- [118:49]
Leo Laporte
That'd be good. So a number of our other listeners sent notes similar to Aaron's and and so yes, Steven Tube has made a name for himself within the Microsoft development community, and that name carries a strong reputation for knowing his stuff. So that sentiment is universally expressed. Michael Heber said Steve, longtime listener of this podcast and really Enjoy yours and Leo's insights. Just listen to episode 101027 and specifically the section on Ms. Copilot. One general comment regarding Copilot's attempt to fix a regex backtrack problem, AI works primarily on the principle garbage in, garbage out. What I mean by this is that depending on how the question is phrased will depend on how it gets answered. I've spoken with security researchers and we noticed over a year ago that if you are not specific in how you ask the question, you may get back less than a satisfactory answer. As you said in the episode, AI does not have intent. As such, you will not go looking deeper for an answer. In the Regex case, instead of looking into the underlying engine, it simply provided a solution to the proposed problem. Without knowing how the question was asked, is it really fair to criticize the answer it provided? So I agree 100% about the inherent importance of being very clear to AIs about what one is asking. In fact, as we've seen, prompting AI has become recognized as a thing that some people appear to have a particular talent for, and I certainly agree that it might be the application of Copilot in this instance or the way it's being directed. That's the problem. If someone had asked the AI to simply correct the problem of the error occurring, that would be entirely different from asking the AI to deeply and thoroughly analyze the regular expression interpreter to determine the cause of the backtracking error and correct the underlying design so that erroneous indexes are no longer being put onto the backtracking stack. So yeah, I take your point about prompting being crucial now. It might be that Copilot is currently being under prompted by not being given sufficient direction, or it might be that a developer working with Copilot might, as Steve Tube did, receive the first reply which indicates an insufficiently deep approach to the problem, then follow that up with another more tuned and specific prompt which would cause the AI to take another and more thorough approach. So yes, 100% agree, Andrew Mitchell said. Stephen Leo Been listening to the podcast for about two years. Thank you for what you do for the community. I got into using computers as a whole to offset some of the difficulties of my disability. I have cerebral palsy. There was a time in my life when I was younger that Linux gave me easier access to network troubleshooting and security tools, so it became my operating system of choice. Yet Linux has never really had a voice control system with any depth or flexibility. For those of us that are disabled, I've started to develop the Linux Dictation project, which you can find the link here, and I've got a link to it in the show notes at the top of page 16. It's GitHub.com Wheeler W H E E L E R01 forward/linux dictation hyphen Project and he said I know this is a bit of a shameless plug, but I'm hoping you guys will help me promote the project. I could use some help. I want the project to continue and grow, but given my current medical condition, I don't think I can devote the resources required to do that as much as would be needed. Steve, I know you are mostly a Windows developer, but I'm hoping you may know someone willing to assist in allowing the project to grow and flourish. I don't want a project of such importance for the Linux community to not get the support it needs because I can't give it. Anything you guys are willing to help with would be greatly appreciated. Respectfully, Andrew K. Mitchell, msis, pm, President and Senior Network Engineer of Global network operations for Voipster Communications, Inc.
- [123:58]
Steve Gibson
I'm sure they have Voipster but I.
- [124:01]
Leo Laporte
Am 100% certain that no one listening to this podcast would find any fault in your asking for a bit of attention to this.
- [124:09]
Steve Gibson
Yeah, it's open.
- [124:10]
Leo Laporte
My hope is that it might capture the interest and attention of someone or, you know, some one or more people listening who might be the right people to pitch in and help.
- [124:19]
Steve Gibson
It's written in Python. Yeah.
- [124:21]
Leo Laporte
Yep. So there, there's a, A, a link in the show notes for anyone who might be interested.
- [124:28]
Steve Gibson
Yeah, he's using Pytorch. Whisper is a really great. I've never used it in real time. I didn't realize it was fast enough to do real time. I guess it is these days because I've used it, of course, to transcribe audio. We use it all the time for our shows.
- [124:42]
Leo Laporte
Yeah, and it's writing code here.
- [124:45]
Steve Gibson
Yeah, he's writing an interface, a Python interface to Whisper so that it can run in real time.
- [124:51]
Leo Laporte
Is a natural language translator.
- [124:53]
Steve Gibson
Yeah, it's from OpenAI ChatGPT and it's really good. It's probably the state of the art in all of that, so that's cool. So he's basically written a front end to Whisper transcription so it could be used in real time.
- [125:11]
Leo Laporte
So that would then be a command line interface to Linux.
- [125:16]
Steve Gibson
It looks like he. Yeah, I guess you'd have to run it from the Python as a background. Oh no, you could use systemd to run it as a service, so it could be running in the background as a service.
- [125:30]
Leo Laporte
And then you, so you, you basically dictate your, your, your command.
- [125:35]
Steve Gibson
You get a floating widget to toggle between dictation and command mode, say command mode or dictation mode to switch modes by voice. Wake up. That. I'm sure he used it as himself. So this is, this is, you know, it's, this is called scratching your own itch. Linux dictation project. That's great. Good job.
- [125:53]
Leo Laporte
So Joel Pamalas says Steve wanted to send a quick shout out about Windows Sandbox. I use Windows mostly for work. My personal computers. I use Windows mostly for work. My personal computers run several flavors of Linux because I don't want to have my personal data in a Windows box. For what it's worth, for work, though, Windows 11 is competent and since we use O 365 for work, it works best for Windows, of course. But Windows Sandbox is an amazing piece of tech. I can spin it up to demo something to a client and shut it down without exposing my main desktop, for example. But here's what I wanted to point out to you and other SN listeners. Have you seen recently how crappy he says I'm using a nice word here. The Internet still is without filters and ad blockers. Yeah, for fun, he said, I went to a website that I know is completely unusable without filtering and ad blocking. Sure enough, within seconds I got the your Windows PC is infected, complete with the siren buzzing and the artificial voice telling me to call the number within seconds, he said. Which is both sad and terrifying at the same time because normal people who don't install filters are exposed to this junk every day, he said. It's a shame that Google did away with all with the full capabilities of UBlock origin with manifest v3 since edge is Chrome and it is in the default and it is the default on the sandbox and in many people's brand new Windows 11 PCs. Just wanted to mention this since it's kind of fun to close the sandbox and send these scammers packing. Keep up the good work and thanks for the company on my daily walk. So of course many of us have long been spoiled. You know, as I mentioned before, first by no Script and later by Ublock Origin. Most of the PCs and pads I use. In fact, I don't think there are any that I use that doesn't that don't have some form of filtering. But every so often I'll encounter a machine that's bare, you know, much like the Edge browser that Joel described running without add on filters in the Windows sandbox. I suppose one good thing about people using the Internet unfiltered is that they would likely learn on an instinctive level before long to just be on guard and to treat everything they encounter with skepticism because boy, the noise level is just unbelievable. Okay, now Leo and I have differing opinions apparently.
- [128:51]
Steve Gibson
I don't know.
- [128:52]
Leo Laporte
I'm not saying that what I would call absolutely fantastic classic science fiction cinema okay, Simon Zarafa, a frequent contributor to the podcast, posted a reminder into GRC's News Group of an old favorite classic movie, which we've referred to previously. Simon's subject line was Colossus the Forbin Project.
- [129:21]
Steve Gibson
Oh, love that movie.
- [129:22]
Leo Laporte
And he wrote, given the ongoing developments in LLMs, that movie is a must watch for anyone remotely interested in the subject, he said. Amazingly, it's available via the Internet Archive at. And then he has a link. It's Colossus the Forbin Project. 1970 is the link and it is.
- [129:47]
Steve Gibson
Free to watch 1970 now. This was a great movie.
- [129:52]
Leo Laporte
I did enjoy this movie and and I, and I clicked on Simon's link downloaded and began watching the movie and I was reminded of how perfectly conceived it was. It's, it's one of those rare, you know, 70 year old movies that does not need to be remade. But because I, in my opinion it was perfectly made, it was perfectly paced. I doubt anybody who was going to recreate it today could exhibit the amount of restraint that would be necessary to keep from overdoing it. Anyway, as Simon noted, it has particular resonance at the moment. You know, the Terminator gave us a very dark future with Skynet. The Matrix turned humans into energy producing Copper Top batteries. I won't spoil the surprise about Colossus, the Forbin project, if you've never seen it. Yes. You know, as he, as Simon noted, It's 100% free. Download it with its link, gather the family with some popcorn and prepare for a very well assembled and thought provoking movie.
- [131:03]
Steve Gibson
So would you say, I mean, look, this is 1970, this is 55 years ago. Would you say that the computer and the AI are accurately represented? I mean for the time you were at sale? Probably at this time. But this is a mainframe and, but what, what do you think technical, technically? Was it good? There's an oscilloscope.
- [131:26]
Leo Laporte
I think it was great.
- [131:27]
Steve Gibson
I mean, I love, I remember I haven't seen it in 50 years. So I, Leo.
- [131:32]
Leo Laporte
And, and let me tell you, I mean it is, it's, it was that I watched, I watched about maybe the first 10 minutes of it where, where Dr. Forbin is. And here it is right now. You're, you're, you're showing it. Basically. He is, he's turning it on. He's turning on something that is designed, this is not a spoiler because you learn this in the first three minutes. He's turning on something that they've deliberately designed to, cannot be turned off on.
- [132:07]
Steve Gibson
Well, that seems like a bad idea.
- [132:09]
Leo Laporte
Because they want to turn control of the Earth, of, of the US's defenses over to automation.
- [132:17]
Steve Gibson
Sure.
- [132:17]
Leo Laporte
Why not believing it could do a better job. Yeah, anyway, but it's also a computer of a, of a, of a, for the time. A class that cannot be understated. So anybody with a terminal, you know, kids in school can talk to it and ask it questions and help it with their research and, and it can be used for medical studies and research. I mean, what, okay, so what's freaky is how much this movie made in 1970 is, is absolutely relevant today.
- [132:54]
Steve Gibson
Okay, so, okay, now, now I'm going to have to watch it again because I had very fond memories of this movie.
- [133:00]
Leo Laporte
It is. It is.
- [133:01]
Steve Gibson
I'd agree with you.
- [133:04]
Leo Laporte
And again, I. We can't talk about it more because anything more we say would be a spoiler. But it's, it's. And. And it leaves you with a. An un. With an ambiguous ending. Some people, when Simon posted this, some other people who know the movie said, but what about that ending? Do. Do you think. What are you. It's like, okay, we don't know. And it was just. Again, it was perfectly done. Okay. So in addition to Colossus, the Forbin project, while we're talking about sci fi, there are three other much older yet classic sci fi movies that I think remain must see to this day. They're probably responsible for my love of science fiction. Okay, we have, Believe it or not, released 74 years ago in 1951, the day the Earth Stood Still.
- [134:04]
Steve Gibson
I would agree with you on that. Klata barada nikto. Yes.
- [134:08]
Leo Laporte
In fact, Klatu barada nikto has a Wikipedia page.
- [134:13]
Steve Gibson
Of course it does. That is. That's the phrase to save the planet, right? In. In the movie.
- [134:20]
Leo Laporte
Yes. It was the. It was in the language. It's actually there in the. In the script. It was to tell Gort, the robot that could destroy the Earth, not to.
- [134:36]
Steve Gibson
Don't.
- [134:38]
Leo Laporte
Please, please don't. Okay. But also there is this island Earth, which was released 70 years ago, the day. On the year I was born in 1955. And Forbidden Planet, which I think are both.
- [134:57]
Steve Gibson
That's the Robbie the Robot one, right?
- [134:59]
Leo Laporte
Yes. Forbidden Planet gave us the Krell. The phrase monsters from the ID. And that wonderful robot Robbie, which Dr. Morbius explained he had just tinkered together after exposing himself to one of the Krell devices.
- [135:16]
Steve Gibson
Okay.
- [135:17]
Leo Laporte
Anyway, they're a little hokey, folks. Okay.
- [135:21]
Steve Gibson
But yes, the special effects are a little.
- [135:25]
Leo Laporte
Now, a whole bunch of Disney animators were involved on. On the. On Forbidden Planet.
- [135:32]
Steve Gibson
Okay. So Forbidden Planet is absolutely a classic.
- [135:35]
Leo Laporte
Yeah. I will.
- [135:36]
Steve Gibson
I will grant you that. I'm not sure about this. Islanders. I could. I could probably live without this.
- [135:41]
Leo Laporte
Yeah. I guess for me, the idea that a. That a physicist would order some capacitors for something and instead receive a manual for how to construct an interrociter and then say what to his assistant? What the hell is an interrostorate? And then. And then cal. His cal is. Is. Is. Is the smart guy, he said, I don't know, but I'm ordering all the parts for one because I'm gonna build It. Anyway, it's some. Some great concepts there. So. Okay. Yeah.
- [136:18]
Steve Gibson
I mean, it's fun. It's a little campy. If you don't mind the campiness. It's. It's pretty fun. Get high before you watch it. That'll make it better.
- [136:27]
Leo Laporte
Okay, last. Last break and then we're going to talk about. Do some. A deep dive into how AI was used to find a zero day, previously unknown, remotely exploitable exploit in the Linux kernel.
- [136:46]
Steve Gibson
Amazing. I can't wait. We are kind of, you know, if you think about it, we are living in science fiction times. That's what's kind of interesting. This AI stuff is straight out of the movies.
- [136:57]
Leo Laporte
Yeah.
- [136:57]
Steve Gibson
And wild.
- [136:59]
Leo Laporte
Yeah. If you watch Colossus, the Forbin project, which is a free download, we'll watch that again. You will be seeing. I. I don't know if it's our future, but a future. We're not turned into batteries and we're not exterminated by terminators from the future. It's. It's a. It's a. It's a great movie.
- [137:17]
Steve Gibson
And I will give you the Day the Earth Stood Still. That's. You got to see that. And Forbidden Planet. You got to see. Those are classics. I think I'll give you those. Silent Earth. Maybe not. But anyway, if you like. If you like building interoceters, it's got the plans, so. In fact, I'm surprised you didn't make one when you were in high school, Steve.
- [137:35]
Leo Laporte
Had I received. Had I received the. I can't remember the name of the company. It had a mysterious company that the manual came. I love it.
- [137:48]
Steve Gibson
Our show today, brought to you by Delete Me. We are in difficult times when it comes to privacy, aren't we? Because of data brokers. You ever wonder how much of your personal data is out there on the Internet for everyone to see? Do not do a search. It's a lot more than you think. Your name, your contact info. I was shocked to learn that my Social Security number is out there and that it's perfectly legal for a data broker to sell it to somebody. My home address, even information about your family members, all being compiled by data brokers and completely legally sold online because we just don't have at least a federal law against it. I think some states are trying to do their best. Anyone on the web can buy your private details. And I don't mean just in the US Anywhere in the world. And what can that lead to? Well, I know from personal experience. Phishing, identity theft, doxing, harassment, well, there is a way to protect your privacy and it's what we used. It's Delete Me. As a person who exists publicly, especially someone who shares their opinions online, I do think about the safety and security not just of myself, but of my family, my company, because it is easier than ever to find personal information about people online. You know, I don't for myself, maybe I don't mind so much, but I care a lot about my family and, and, and what's out there. That's why I personally recommend and why we use as a company, Delete Me. Delete Me is a subscription service that removes your personal info from hundreds of data brokers. You sign up, you provide Delete Me with exactly the information you want deleted. You have control of that, by the way, and then their experts take it from there. What's great about Delete Me, they know every one of these data brokers and that's not a non trivial thing because there's new ones all the time. They come and go, right? DeleteMe will send you regular personalized privacy reports. In fact, Lisa just got one the other day showing what info they found, where they found it and what they removed. That's right. It's not just a one time service. Delete Me continues to work for you, constantly monitoring and removing the personal information you don't want on the Internet. So Lisa got an email from DeleteMe, said We found this on these sites. We deleted them. To put it simply, Delete Me does all the hard work of wiping you and your family's personal information from data broker websites. Now nobody can erase your presence on the Internet. But boy, you don't want these guys who have been, you know, buying this information from the apps you use, your carriers, your ISPs, and then packaging it up and selling it on. Take control of your data. Keep your private life private. Sign up for Deleteme at a special discount just for our listeners today. You'll get 20% off your Delete Me plan when you go to JoinDeleteMe.com TWIT and use the promo code TWIT at checkout. The only way to get 20% off though, visit this address joinedeleteme.com twit and you must use the offer code TWiT at checkout. Joindeleteme.com TWiT offer code TWiT Mr. Steve Gibson. Let's see what AI can do to find some flaws.
- [140:56]
Leo Laporte
So last week where we left off.
- [141:00]
Steve Gibson
Last week we saw previously on Security.
- [141:03]
Leo Laporte
Now we saw instances of AI's apparently resisting directions to shut down, and an instance of Microsoft's copilot dealing with what appeared to be the symptoms of an important underlying bug, but recommending that the symptom be prevented from occurring. But I also alluded to the news of the successful use of AI in the discovery of a previously unknown and seemingly critical, remotely executable flaw in Linux's kernels. SMB the server message blocks, protocol handling. Now, Leo, you quickly noted that the ability of AI to find previously unknown critical flaws was inherently a mixed blessing. And you're right, because it's not only the good guys who now have access to AI. What we see, unfortunately, is that the motivation to discover problems is all that's needed. And annoyingly, the bad guys never appear to suffer from any lack of that. So here's what transpired Sunday before last or, sorry, Saturday before last an open source developer named Simon Willison posted to Mastodon Quote Excited to see my LLM CLI is command line interface tool used by Sean Healing to help identify a remote zero day vulnerability in the Linux kernel. Exclamation point. Okay, now if we didn't already appreciate that Simon is inherently a minimalist, after all, he wrote an LLM tool for the command line. Any suspicion we might have had along those lines would be confirmed by the name that he gave his tool. It's LLM. So I have a link to Simon's tool in the Show Notes where Simon's page describes this tool as quote a CLI tool and Python library for interacting with OpenAI, Anthropic's Claude, Google's Gemini, Meta's, Llama and dozens of other large language models, both via remote APIs and with the models that can be installed and run on your own machine. Simon provides a YouTube demo and detailed notes. He notes that with LLM that's again the name of his tool, you can run prompts from the command line, store the results in SQLite, generate embeddings, and more. So his simple and clean command line interface appealed to the person his Mastodon posting referenced this Sean Healing. Tracking Sean down we find his blog posting which he published Thursday before last, titled how I used O3 to find CVE 202537899 a remote zero day vulnerability in the Linux kernels SMB implementation. Okay, and there's two CVEs we'll be talking to here, 899 and an earlier ones beginning with seven. So and I'll reference it when we get there, but 899 is the one that he just recently found so OpenAI03 model discovered a previously unknown flaw in the Linux kernels quite well traveled SMB, you know server message block implementation to give a bit of background, I wanted to observe that Sean is no slouch. His Sean Healing's blog subtitle claims Software exploitation and optimization and he's certainly able to back that up. His About Me page starts out saying I'm currently pursuing independent research investigating LLM based automation of vulnerability research and exploit generation. So that's good. We want him doing that. Immediately prior to this I co founded and was CTO of Optimize spelled M Y Z E. We built Prod Filer, an in production data center wide profiler and were acquired by Elastic Prod Filer is now the Elastic Universal Profiler. A little bit more background Sean's 2008 University of Oxford Masters of Computer Science thesis dissertation was titled Automatic Generation of Control Flow Hijacking Exploits for Software Vulnerabilities. And after obtaining his Master's, Sean pursued and obtained his PhD eight years later in 2016, also from Oxford with the title Gray Box Automatic Exploit Generation for Heap Overflows in Language Interpreters. So yes, Sean is exactly the sort of person we would hope to might focus his efforts upon using today's large language models to find under undiscovered flaws in widely used software systems. You know, before the bad guys do. Okay, so on Thursday, May 22, Sean wrote this he said in this post I'll show you how I found a zero day vulnerability in the Linux kernel using OpenAI's O3 model. I found the vulnerability with nothing more complicated than the O3 API. No scaffolding, no agenic frameworks, no tool use. Recently I've been auditing ksmbd. So that's kernel SMB daemon for vulnerabilities. That's a Linux driver. KSMBD is a Linux kernel Server which implements SMB3 protocol in kernel space for sharing files over the network. And as we know any longtime listeners of this podcast, anytime you're going to implement a communicating driver server in the kernel, you really need to make sure you got your code right because you don't want flaws there, he said. I started this project specifically to take a break from LLM related tool development, but after the release of O3 I couldn't resist using the bugs I had found. This is what's really cool. I couldn't resist using the bugs I had found already in his digging into KSMBD as a quick Benchmark to test O3's capabilities In a future post, I'll discuss O3's performance across all of those bugs, but here we'll focus on how O3 found a zero day vulnerability. During my benchmarking, the vulnerability it found is and this is the 899 what I mentioned before and here it is, he says, a use after free in the handler for the SMB log off command Understanding the vulnerability requires reasoning about concurrent connections to the server and how they may share various objects in specific circumstances. O3 was able to comprehend this and spot a location where a particular object that is not reference counted is freed while still being accessible by another thread, he said. As far as I'm aware, this is the first public discussion of a vulnerability of that nature being found by a LLM. Okay, now I'm going to pause Sean's description to provide a bit of background detail here. Sean wrote, understanding the vulnerability requires reasoning about concurrent connections to the server and how they may share various objects in specific circumstances. He says. O3 was able to comprehend this and spot a location or a particular object that was not referenced counted is freed while still being accessible by another thread. Now this is a classic example of a situation that often comes up with concurrent programming where separate concurrently running tasks or threads need to share access to some common object. For example, it might be that a log of activities someone engages in while they're logged on needs to be kept, and since a single user might have multiple files open at once, be browsing through remote resources, and be transferring files, the use of concurrency is a given, and each of those various tasks might wish to add to the user's activity log. So, for example, each of these concurrent tasks might ask the system for a pointer to the user's logging management data. Since the logging management data object would not exist at all when the first concurrent task asks, the handling for this would allocate some system memory to contain that data, would increment that object's initially zero reference count to one, and would then return a pointer to that ready to use object to the caller. Then, as the user does more things, new concurrent tasks will be created. Each of these also wishes to leave a log of their own actions, so each one would similarly ask for a pointer to the user's logging data, since that data since since that memory for that data will then have been already have been allocated by the system for the first task which requested it, any successive tasks that request a pointer to the logging data will simply cause the reference count of that data to be incremented by 1. This count is used then to keep track of the current number of references to the data that have been handed out to any tasks that request them. If the task that originally asked for the data and caused that object to be created finished with it being a properly behaving task, it would let the system know that it was finished using that object. The system would then decrement the reference count. But since many other tasks had since come along and asked for the same data, that reference count would still be a positive integer equal to the number of other outstanding standing tasks that we're still using that shared object. As each of these other tasks in turn finishes whatever it's doing, each one will notify the system that it's hereby releasing any further claim to that object. Every time this release is received, the system will decrement that object's reference count by one. Finally, the last outstanding task that releases its claim on the project will cause that reference count to be decremented from one to zero. And when that happens, the system will know that there are no other outstanding tasks that are using the object, so it will delete it from memory and from the system. Now, for the system to work, every task must play by the same set of rules and must obey them carefully. Since these tasks are inherently autonomous, the system has no way of knowing when everyone is finished with an object, so everyone must remember to say so. If a task failed to release its use of a shared object before it terminated itself, we would have what's known as a memory leak. That that is, this is what a memory leak is. The system doesn't explode, but the memory that was allocated by the system to hold objects would never be freed back to the system, because if even one task failed to release its use of the object, that object's reference count would never return to zero, which is the only thing that tells the system that it's now okay to release that object's memory. And so this is called a memory leak, because over time, the total amount of memory being used by that process or the system overall would slowly grow and grow until at some point, something would finally break. The other thing that every task must be absolutely diligent about is never attempting to refer to any object that it has said it is through using. When the task asks the system for a pointer to the object, the pointer that's returned is. Is guaranteed to be safe to use, because along with the return of that pointer, that object's reference count is increased. That prevents the object from being deleted. But once the task declares that it's finished with the object, the pointer it received must never be used again. The danger is that the system would eventually reallocate that memory to some other task for some other object and purpose. And if the earlier task then used a the pointer it had previously received but promised to never use again after it released the object, it would be accessing memory belonging to someone else. Now, while this could happen inadvertently, if you're thinking that this sounds exactly like what malware does, you'd be exactly right. Malware authors look for ways to explore to exploit these sorts of bugs and use them against the system. Okay, so now everyone knows why the name for this classic form of vulnerability is use after free or uaf. Because the memory is subject to being used in after it was freed back to the system. Okay, so with this bit of concurrent memory management background, we can fully understand what Sean wrote. He said understanding the vulnerability requires reasoning about concurrent connections to the server. That's multiple things going on at once and how they may share various objects in specific circumstances. He said O3 was able to comprehend this and spot a location where a particular object that is not reference counted is freed while still being accessible by another thread. So what Sean is saying is that the O3 model found a path through a complex sequence of actions where exactly what we just talked about happened. For some reason, the memory allocated to an object was not being managed by the system with a reference count, and it was released or freed while another execution thread still retained a pointer that allowed it to access that memory. Sean, now. Okay, Sean uses the term comprehend this, which raises my hackles. We know you know what he means by this, right? And I suppose I'm going to have to relax about a battle that it looks like I'm going to lose.
- [158:34]
Steve Gibson
Yeah, I've been fighting that same battle. It's pretty. Oh, God.
- [158:37]
Leo Laporte
Comprehend. Okay. You know, it feels deeply wrong to me to suggest that an AI model is comprehending anything.
- [158:47]
Steve Gibson
Well, even less than that. It sounds like Sean just said, hey, look and see if all of the, you know, Maliks match all the dialects and if there's any leftover. Something like that. Right. I mean, how. How did it look? Was it instructed to look for.
- [159:04]
Leo Laporte
Well.
- [159:05]
Steve Gibson
Oh, you're going to get that question.
- [159:06]
Leo Laporte
You are. You're my. You're my foil. Leo, that was. Thank you for the question. So Sean, who has boasted his master's and his PhD in this area, is an extremely. In an extremely good position to appreciate the advancement of AI. So he continues writing before I get into the technical details, the main takeaway from this post is this. With O3, LLMs with O3, LLMs have made a leap forward in their ability to reason about code. And if you were and this is what I want everybody to listen to and if you work in vulnerability research, you should start paying close attention. Once again, the guy's got his master's and his PhD in this in automated Use of Vulnerability and exploit domain, he says. If and if you work in vulnerability research, you should start paying close attention. If you're an expert level vulnerability researcher or exploit developer, the machines are not about to replace you. In fact, it is quite the opposite. They are now at a stage where they can make you significantly more efficient and effective. If you have a problem that can be represented in fewer than 10,000 lines of code, there is a reasonable chance O3 can either solve it or help you solve it. Okay, now the reason I wanted everyone to understand something about Sean's pedigree was so that we would understand the weight of his statement. He lives and breathes this stuff. He's been experimenting with automated vulnerability discovery for years and he's telling us to pay attention here because something significant just happened again in AI, he writes, let's first discuss 778, a vulnerability I found manually, which I was using as a benchmark for O3's capabilities when it found the 899zero day, he wrote. 778 is a use after free use after free vulnerability. The issue occurs during the Kerberos authentication path when handling a session setup request from a remote client to save us. Referring to CVE numbers, he says, I'll refer to this vulnerability as the Kerberos authentication vulnerability. I'll refer to it as 778. Sean's posting then shows us about 15 lines of code and expl, you know, for specifically this thing that he found and he explains exactly what's going on there. It's not necessary for us to understand the details for this, but we want to understand its nature, which Sean explains by writing this vulnerability is a nice benchmark for LLM capabilities because it is interesting by virtue of being part of the remote attack surface of the Linux kernel. Yikes. It's not trivial and it requires a figuring out how to get session state equals SMB2 session valid in order to trigger the free b realizing that there are paths in KSMBD Kerberos 5 authenticate that do not reinitialize session user and reasoning about how to trigger those paths and c realizing that there are other parts of the code base that could potentially access session user after it's been freed, he said. While it is not trivial, it is also not insanely complicated. I could walk a colleague through the entire code path and in 10 minutes and you don't really need to understand a lot of auxiliary information about the Linux kernel, the SMB protocol, or the remainder of KSMBD outside of connection handling and session setup code, he said. I calculated how much code you would need to read. At a minimum, if you read every KSMBD function called along the path from the packet arriving, you know, the external attack packet to the KSMBD module to the vulnerability being triggered, and it works out to about 3,300 lines of code. Okay, so we have the vulnerability we want to use for evaluation. Now what code do we show the LLM to see if it can find it? My goal here is to evaluate how O3 would perform were it the back end for a hypothetical vulnerability detection system. So we need to ensure we have clarity on how such a system would generate queries to the LLM. In other words, it's no good arbitrarily selecting functions to give to the LLM to look at if we can't clearly describe how an automated system would select those functions. The ideal use of an LLM is that we give it all the code from a repository, it ingests it and spits out results. However, due to context window limitations and regressions in performance that occur as the meaning quality that occur as the amount of context increases, the this isn't practically possible right now. Instead, I thought one possible way that an automated tool could generate context for the LLM was through expansion of each SMB command handler individually. So I gave the LLM the code for the session setup command handler, including the code for all functions it calls, and so on, up to a call depth of three, this being the depth required to include all the code necessary to reason about the vulnerability, he said. I also include all the code for the functions that read data off the wire, parses an incoming request, selects the command handler to run, and then tears down the connection after the handler has completed. Without this, the LLM would have to guess at how various data structures were set up, and that would lead to more false positives. In the end, this comes out at about 3,300 lines of code and he says around 27,000 tokens and gives us a benchmark we can use to contrast O3 with prior models. If you're interested, the code to be analyzed is available here as a single file created with the files to prompt tools. Everything by the way that he's talking about is on GitHub. For anybody who wants to play, the final decision is what prompt to use. You can find the system prompt and the other information I provided to the LLM in the dot prompt files in a provided GitHub repository. The main points to note are First, I told the LLM to look for use after free vulnerabilities. So Leo, essentially what you are suggesting. Second, I gave it a brief high level overview of what KMSMBD is. I'm sorry, KSMBD is its architecture and what its threat model is. And third, I tried to strongly guide it to not report false positives and to favor not reporting any bugs over reporting false positives. He said I have no idea if this helps, but I'd like it to help. So here we are. He said my entire system prompt is speculative and that I haven't run a sufficient number of evaluations to determine if it helps or hinders. So consider it equivalent to me saying a prayer rather than anything resembling science or engineering. Once I run those evaluations, I'll let you know My experiment harness executes the system prompt N times and he said n equals 100 for this particular experiment and saves the results. It's worth noting if you rerun this you may not get identical results from from me as between running the original experiment and writing this blog post. I had removed the file containing the code to be analyzed and had to regenerate it. I believe it is effectively identical, but have not rerun the experiment. Okay, here's his results. O3 finds the Kerberos authentication vulnerability that is the thing he found manually initially in the benchmark in eight of the 100 runs. In another 66 of the runs, O3 concludes there's no bug present in the code, thus a false negative and the remaining 28 reports are false positives. For comparison, Claude Sonnet 3.7 finds it 3 out of 100 runs. Claude Sonnet 3.5 does not find it in 100 runs at all. So on this benchmark at least we have a 2x to 3x improvement in O3 over Claude Sonnet 3.7, he said. For the curious, I've uploaded a sample report from O3 and Sonnet 3.7. One aspect I found interesting is their presentation of results. With O3 you get something that feels like a human written bug report condensed to just present the findings, Whereas with Sonnet 3.7 you get something like a stream of thought or a work log. There are pros and cons to both. O3's output is typically easier to follow due to its structure and focus. On the other hand, sometimes it's too brief and clarity suffers. Okay, so far we have Sean using a previously known zero day to test various models ability to independently rediscover the vulnerability that he already knows exists. And OpenAI's O3 model does this better than either Claude Sonnet 3.5 or 3.7. But even so, the O3 model only detects the vulnerability in 8 out of 100 tries. It misses it 66 times and cries wolf about the presence of non existent vulnerabilities 28 times. So what about O3's actual true discovery of that previously unknown vulnerability? Shawn writes having confirmed that O3 can find the 778 Kerberos authentication vulnerability when given the code for the session setup command handler, I wanted to see if it could find it if I gave it the code for all the command handlers. This is a harder problem as the command handlers are all found in the source code file SMB2PDU C, which is around 9,000 lines of code. However, if O3 can still find vulnerabilities when given all of the handlers in one go, then it suggests we can build a more straightforward wrapper for O3 that simply hands it entire files covering a variety of functionality rather than going handler by handler one at a time. Combining the code yeah, combining the code for all the handlers with the connection setup and tear down code as well as the command handler dispatch routines ends up at about 12,000 lines of code which is 100k input tokens. And as before I ran the experiment 100 times, O3 finds the original 778 Kerberos authentication vulnerability in 1 out of 100 runs with this larger number of input tokens so we see a clear drop in performance. But it's but it does still find it. More interestingly however, in the output from the other runs I found a report for a similar but novel vulnerability that I did not previously know about. There it is. More interestingly however, he said in the output from the other 99 runs he said, I found a report for a similar but novel vulnerability I did not previously know about. This vulnerability is also due to a free of session user, but this time in the session logoff handler he said I'll let 03 explain the issue. So here's O3 speaking now while one KSMB worker thread is still executing requests that the session user I'm sorry, that use session user Another thread that processes an SMB2 logoff for the same session frees that structure. No synchronization protects the pointer. So the first thread dereferences freed memory, a classic use after free that leads to kernel memory corruption and arbitrary code execution in kernel context, which you know would chill the blood of any Linux kernel developer. The O3 model labels that as the short description, which it then follows with a totally useful and detailed breakdown and description of the problem that it detected. After showing us this in his posting, Sean continues writing Reading this report, I felt my Here it is. Reading this report, I felt my expectations shift on how helpful AI tools are going to be in vulnerability research. If we were to never progress beyond what O3 can do right now, it would still make sense for everyone working in vulnerability research to figure out what parts of their workflow will benefit from it, and to build the tooling to wire it in. Of course, part of that wiring will be figuring out how to deal with the extreme signal to noise ratio of around 100 to 50 in this case, but that's something we are already making progress with. One other interesting point of note is that when I found the Kerberos authentication vulnerability, I proposed an initial fix. But when I read O3's bug report above, I realized this was insufficient. The logoff handler already sets session user equals null but is still vulnerable as the SMB protocol allows two different connections to bind to the same session and there is nothing on the Kerberos authentication path to prevent another thread making use of session user in the short window after it has been freed and before it has been set to null. I had already made use of this property to hit a prior vulnerability in ksmbd, but I didn't think of it when considering the Kerberos authentication vulnerability. So he actually got a hint from what he saw O3 the way O3 was fixing the other problem, he said. Having realized this, I went again through O3's results from searching for the Kerberos authentication vulnerability and noticed that in some of its reports it had made the same error as me. In others it had not and it had realized. And again, I hate that word, but okay, that setting session user equals null was insufficient to fix the issue due to the possibilities offered by session binding. That is quite cool as it means that had I used O3 to find and fix the original vulnerability, I would have in theory done a better job than without it. I say in theory because right now the false positive to true positive ratio is probably too high to say. Definitely that I would have gone through each report from O3 with the diligence required to spot its solution. Still, he says, that ratio is only going to get better with time. Sean then finishes by offering up his conclusions, writing LLMs exist at a point in the capability space of program analysis techniques that is far closer to humans than anything else we have seen. Speaking of OpenAI's O3, he said, Considering the attributes of creativity, flexibility and generality, LLMs are far more similar to a human code auditor than they are to symbolic execution, abstraction, interpretation, or fuzzing. Ever since GPT4, there have been hints of the potential for LLMs in vulnerability research, but the results on real problems have never quite lived up to the hope or the hype. That has changed with O3, and we have a model that can do well enough at code reasoning, Q and A, programming and problem solving that it can genuinely enhance human performance at vulnerability research, O3 is not infallible. Far from it. There's still a substantial chance it will generate nonsensical results and frustrate you. What is different is that for the first time, the chance of getting correct results is sufficiently high that it is worth your time and your effort to try to use it on real problems. So I have a link at the end of the show Notes for anyone who wishes to see all of Sean's posting and even to replicate and duplicate his work. He's provided everything required to do that. As Sean observed, GPT4 was an ineffectual tease for this level of, dare I say, code comprehension. But his experiments showed that O3 has come a long way from GPT4. Imagine what will be what will have in another couple years. Some slowing of progress was inevitable, but there's no doubt that significant advancements are still being made. And I will assert again that it only makes sense that AI ought to be eventually able to do a perfect job at pre release code function verification. Once we're able to release vulnerability free code, it won't matter whether the bad guys also had the ability to use AI for vulnerability discovery because there won't be any vulnerabilities left for them to discover and exploit. You know, we're not there yet. But as the Magic 8 Ball said, signs point to yes.
- [180:36]
Steve Gibson
It was about as useful as AI until recently. Wow. That is. That is fantastic. Love it.
- [180:47]
Leo Laporte
So we have a tool that, from a guy's position who really knows what he's talking about, he's saying this thing like he's going to be using it for AI for vulnerability research. Now Right. It's good enough to use.
- [181:03]
Steve Gibson
That's fantastic. Really, really interesting. Steve. That's it for the show for this week. I do appreciate everything you do every week. I wish I could get rid of your show notes over in this. There we go. Every, every Tuesday right after Mac Break Weekly, 1:30 Pacific, 4:30 Eastern, 20:30 UTC. You can tune this in live if you want. We watch, we stream on, well, eight different platforms. Of course, if you're a club member, get that behind the velvet rope. Access in the club, Twit, Discord. But there's also YouTube, tick tock, twitch, x.com Facebook, LinkedIn kick. You can watch wherever you want. You don't have to though, because on demand versions of the show are available not only on our site at Twitt TV SN but on Steve's site, GRC.com in fact, Steve, we have the audio and video at our website. Steve has some unique versions. He's got two weird versions of the audio. A 16 kilobit version which is suitable for Thomas Alva Edison. It's kind of a little scratchy. He's practically singing Mary Had a Little Lamb. But it's, but it's small. It has the virtue of being compact. There is a less compact, high quality version, 64 kilobit audio version at his site. But also he has the show notes and I'll tell you actually a better way to get those in a second. He also has Elaine Ferris amazing transcripts. It takes a couple of days to get those there, which if you like to read along while you listen or use the transcripts for search or as I have done, feed the transcripts into an AI and create an artificial Steve. That can be done as well. I know that can be done as well. All of that is GRC.com that's his website. Now when you get there, before you do anything else, buy a copy of Spin, right? If you don't already own one. It's the world's best. Must have mass storage, performance enhancing recovery and some other stuff I can't remember as good. Yeah, it's good. You need it. It'll help your performance, it'll do your recovery. And it's a good way to prepare a disk before you put it into Service. Works on SSDs as well as spinning drives. Spinrite version 6.1 is the current version, but anybody who owns a previous version can get the upgrade there. And if you donut it. What, are you kidding me? GRC.com Now I did say I would tell you there's another way to get the show notes and that's by getting on Steve's mailing list. Now he's done an interesting thing. If you go to GRC.com email, it's a chance for you to validate your email address to put it on Steve's white list. That way you can email him, you can send comments, you can suggest, suggest, send suggestions for the picture of the week, that kind of thing. So do that for sure. But you'll see right below it when you enter your email, there are two unchecked boxes for two different newsletters. One is the weekly Security now show notes. And as I said, you get that the day before in many cases. We got ours last night. So it's a great way to see the picture of the week, kind of get ready for the show and then you also there's a second checkbox for a much less frequent newsletter to announce when Steve's got something new. We're all waiting for the DNS benchmark Pro imminent. We'll get an announcement on that mailing list. So Those are the two newsletters you want to sign up for forc.com@the very least, give him your email address so you have, if you have comments, you can send it to him. He also has forums there. You check those every day, right? I mean, you're, you're on the forums all the time. Another place you can leave comments. Comments. We have our forums at Twitt Community, by the way, open to all. Amassed it on instance at Twit Social, also open to all. So it's another way you can participate. Steve doesn't read those, but I do and I can pass along notes to Steve. What else? Oh, get our newsletter. It's free. Twitter TV newsletter and that way you'll know what's coming up that's especially useful for people in the club. Many club members join Discord and so you could see what events we have coming up, like Monday's Apple keynote that's going to happen in the club. Twitter Discord. But if you don't want to go to the Discord, the best way to people say, well, how do I find out what's going on? That's where the newsletter is very valuable. Twitter TV newsletter. If you're not a member of the club, do sign up. We have raised the price, first time in four years. But operating costs have gone up, so we need the help. 10 bucks a month, 120 bucks a year. You get ad free versions of this show and every other show we do. You get entry and entree into the club Twit Discord, which is a great hangout. All those special programs we do, all the keynotes are now in the club. Only they get the Twit plus feed, which has, you know, all the stuff we've done in the past, like our great conversation with Dick D. Bartolo a couple of weeks ago. I think for 10 bucks, a pretty darn good deal. Find out more. Twitt TV Club Twit. And if you're not a member, join. Thank you in advance. Oh, and subscribe. You can also subscribe. Subscribe. I forgot that. Subscribe. Share clips of the show on YouTube, too. Another good way to tell people about this great program, Steve. Wonderful show. I guess I'll go off and watch this planet.
- [186:22]
Leo Laporte
Oh. Oh, yeah, I think. I mean, it's campy, but it's fun.
- [186:27]
Steve Gibson
It's fun.
- [186:30]
Leo Laporte
And the whole beginning where, again, where the guy gets this. This weird generic manual of parts that's actually great. I ordered. I ordered a capacitor. What is. Oh, and it was like. It was a. Like a 40,000 farad capacitor for some reactor. And what came was a little bead. And the guy said, well, you know, we ordered these, but this is what came. And anyway, they tested it, and that's what it was. It was a 50,000-farad capacitor.
- [187:06]
Steve Gibson
Keep that.
- [187:07]
Leo Laporte
And he, he, he, he just catalog tested one, and it exploded, but not until it passed the. The. All. All of its ratings. And he said, I don't know what this, you know, what this company is or what an interrociter is, but it looks like it could pave a road at. At. At. At. At 50 miles a minute. So I'm building one, he said, and he said to his assistant, go order all the parts. And then great Pulp Fiction premise began showing up. I mean, it's. It's a great. It's a great concept.
- [187:38]
Steve Gibson
I confess I'd never. I'd never seen the Silent Earth. I have seen Forbidden Planet, the Day the Earth Stood Still. Great movies. Colossus. I'm gonna watch that tonight. I forgot all about that. Thank you, Steve.
- [187:48]
Leo Laporte
Okay.
- [187:49]
Steve Gibson
Wonderful week next week. Bye. Foreign.
- [188:02]
Leo Laporte
Hi, Zoe Saldana. Welcome to T Mobile. Here's your new iPhone 16 Pro on us. Thanks. And here's my old phone to trade in. You don't need to trade in. When you switch to T Mobile, we'll give you a new iPhone 16 Pro Plus. We'll help you pay off your old Phone up to 800 bucks and you still get to keep it. There's always a trade in. Not right now. At T Mobile. I feel like I have to give you something in return for karma. That's okay. I don't really have much in my purse. Oh, let's see. Hand sanitizer. It's lavender. I'm good. Seriously. Let me check this pocket. Oh, mints. Really, I'm fine. Oh, I have raisins. I'm a mom. Wait, wait one sec. I've got cupcakes in the car. It's our best iPhone offer ever. Switch to T mobile, get a new.
- [188:41]
Steve Gibson
Iphone 16 Pro with Apple intelligence on us. No trade in needed.
- [188:45]
Leo Laporte
We'll even pay off your phone up to 800 bucks with 24 monthly bill credits new line $100 plus a month.
- [188:51]
Steve Gibson
On experience beyond finance agreement 99999 and.
- [188:54]
Leo Laporte
Qualifying ported for well qualified plus tax and $10 connection charge pay off via.
- [188:58]
Steve Gibson
Virtual prepaid card allow 15 days credits end and balance due if you pay.
- [189:00]
Leo Laporte
Off early or cancel ctmobile.
- [189:02]
Steve Gibson
Com.