← All TWiT.tv Shows (Audio)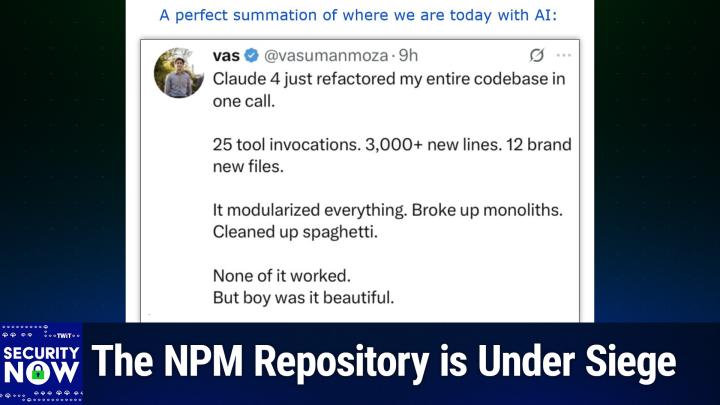
All TWiT.tv Shows (Audio)
Security Now 1030: Internet Foreground Radiation
02:48:29
The NPM Repository is Under Siege
Loading summary
Transcript228 lines
- [00:00]
Leo Laporte
It's time for Security now. Steve Gibson is here. Apple denies it, but there's clearly an exploited iOS message vulnerability. A good reason not to use Telegram ever, ever, ever. And Steve's evolving opinion of Microsoft security. I think you can guess which direction it's headed. All that more coming up next on Security Now.
- [00:28]
Steve Gibson
Podcasts you love from people you.
- [00:32]
Leo Laporte
This is Twit. This is Security now with Steve Gibson. Episode 1030, recorded Tuesday, June 17, 2025. Internet foreground radiation. It's time for Security now. I know you wait all week for Tuesday to come around. Steve Gibson is here, the man in charge of security now, our expert. I shall give you the Klingon salute.
- [01:01]
Steve Gibson
Oh, that's good.
- [01:02]
Leo Laporte
Yesterday I went our wonderful little coffee shop in town, which has really become a community center. Good friend of mine runs it, has a game night on Monday nights. And I brought my chess set down. I thought, oh, this will be fun. Maybe somebody will play chess with me. I set it all up, put the clock there. Nobody was playing. But there was a guy across from me setting up his Star Trek 3D holo chess that plugs in and the things light up and stuff. And I said, I came over, I said, hey, I gotta play some. He said, well, I don't know the rules and I seem to have lost the booklet. So I asked ChatGPT. ChatGPT knew the rules. Fortunately, the proprietor had also saved the booklet. What chatgpt said is, since there are no canonical Star Trek rules for hollow chess, you people have made them up over time.
- [01:59]
Steve Gibson
I was gonna ask whether, you know, did I miss that episode? Because, you know, they always were moving them around.
- [02:04]
Leo Laporte
Yeah. You knew they were playing.
- [02:06]
Steve Gibson
Yeah.
- [02:07]
Leo Laporte
But here is, here's the photo of, of Chris and Peggy and me playing.
- [02:14]
Steve Gibson
Oh, good.
- [02:15]
Leo Laporte
Star Trek Hollow chess. And it had, it has, it has sound effects and then the pieces light up and stuff. And the rules are so complicated that you get a card that you hold. So, you know, there's a piece called the. I guess that's how you pronounce. G, H, H, H, K. Anyway, it was a lot of fun. We played to a draw.
- [02:43]
Steve Gibson
I think Klingon was actually a fully realized language, wasn't it?
- [02:46]
Leo Laporte
I think there's some Klingon names in this.
- [02:49]
Steve Gibson
You can actually speak Klingon?
- [02:51]
Leo Laporte
Oh, yeah, there's people. Yeah.
- [02:53]
Steve Gibson
Apparently Shakespeare has been translated fully realized language, so. Yeah. Yes. Because before computers we didn't have enough to keep us busy.
- [03:05]
Leo Laporte
Anyway, it was a lot of fun. And there's a name for it too, which I Can't remember off the top.
- [03:12]
Steve Gibson
It's not girl.
- [03:14]
Leo Laporte
No, it's something almost equally silly, like Gajeet or something. But anyway.
- [03:20]
Steve Gibson
And as a. An accomplished chess player, Leo, was it actually a useful game or just.
- [03:28]
Leo Laporte
No, no. Chess is so much better. If I could have just gotten anybody to play chess with me, I would have been. It's called De Jaric. It's not. Did I say Star Trek? It's Star Wars. This is not.
- [03:40]
Steve Gibson
And that does look like the.
- [03:43]
Leo Laporte
Yes. This is the one they were playing on the Millennium Falcon. I apologize. I apologize.
- [03:47]
Steve Gibson
Yeah.
- [03:48]
Leo Laporte
Okay. I get them confused.
- [03:50]
Steve Gibson
No, no, you don't.
- [03:51]
Leo Laporte
I do. And that's not good.
- [03:53]
Steve Gibson
No.
- [03:53]
Leo Laporte
Yeah.
- [03:54]
Steve Gibson
You can't do podcasts if you can confuse Star Trek.
- [03:58]
Leo Laporte
Star wars credentials. That's.
- [04:00]
Steve Gibson
I'm sorry, that's not.
- [04:01]
Leo Laporte
Okay. What's coming up on Security now.
- [04:04]
Steve Gibson
So we're going to talk about. I had fun with the title because I've. For 20 years, I've been talking about a term that I coined. Internet background radiation.
- [04:15]
Leo Laporte
Yes.
- [04:17]
Steve Gibson
Today's podcast is titled Internet Foreground Radiation. What? And we're going to find out what that's all about. But we're also going to look at an exploited iOS iMessage vulnerability, which Apple is denying. Do we trust them? Are they saving face? We don't know. The NPM repository is under siege with no apparent end in sight. Two pieces of news there. Not good. Were Comcast and Digital Realty compromised? They, you know, don't ask them. They say, no, not here. But evidence and even some serious agencies suggest otherwise. Matthew Green has agreed that X Chat does not offer true security. We touched on that last week. I said I might dig deeper into it. I don't have to because Matthew did for us. We may know how Russia is convicting users of Telegram, and it's not by decrypting their messages. Interestingly enough, Microsoft finally decides to block two insane Outlook file types and I'm going to deliberately control my language because we have young listeners of this podcast.
- [05:41]
Leo Laporte
Good boy.
- [05:43]
Steve Gibson
Wow.
- [05:44]
Leo Laporte
I know you want to.
- [05:47]
Steve Gibson
It turns out, just as we were doing the podcast last week, Leo, you ran across the news that 40,000 video cameras were online on the Internet. I've got the details to follow that up and interestingly enough, where they are and who owns them. Also, the. There was a question about running Spinrite on encrypted drives that I'm going to cover briefly. And then. Oh. A listener also sent their. The result of their dumping all of Elaine's transcripts into an LLM and then asking it how my opinion of Microsoft Security has evolved over time.
- [06:33]
Leo Laporte
Oh boy.
- [06:35]
Steve Gibson
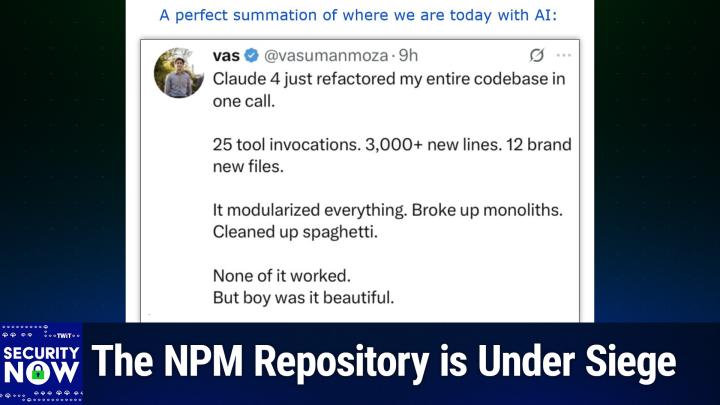
And what do we know about the bots that are scanning the Internet to create Internet foreground radiation? So. And oh, a picture of the week, that is. I sent the show notes out about 24 hours ago. Yesterday afternoon, this one generated more LOLs than is common. I am going to have to describe before we explain this what it means to refactor code, because I know that. Well, I know you do and I, I also have had to do so from time to time.
- [07:14]
Leo Laporte
Yes.
- [07:15]
Steve Gibson
But anyway, we have a great picture of the week.
- [07:17]
Leo Laporte
Can't wait. I have not looked at it. We will see it together in just a minute or two on this episode of Security now. Can't wait. Always look forward to this. Go ahead, have a little sip of java. There's a lot of work ahead of you, Steve, while I Now our sponsor for this segment is Delete Me. And if ever you thought you needed to delete your data from data brokers, there is a real reason to do it. Now I know people have been watching the news about what happened in Minnesota. They recovered the suspects notebooks and he had a list in the notebooks of all the places you can go online to get personal information about people, including their home addresses from those data brokers. If you've ever gone online and did a search for your name, you know, you see these people, they call them people searches, but they're data brokers. They're people online sites, companies that collect your personal information and then sell it to anybody who comes along. Your name, your contact info. I was stunned to know it's legal to sell my Social Security number and your home address, even information about your family members, all being compiled completely legally. There's no law against it. There really needs to be by data brokers and sold online. Anyone on the web can buy your private details. This can lead to identity theft, phishing attempts, doxing harassment, and now we know much worse. But now you can protect your privacy with Delete me. Look, I, I live in the public. I, I share my opinions online. I make people mad because I confuse Star wars and Star Trek. Obviously. Obviously I'm in trouble, right? It's really important to everybody though to keep your personal information private. That's why we use at TWIT for our management, our managers and we recommend Delete me. We did it when Lisa started getting there were phishing texts being sent to our employees to Lisa's direct reports impersonating Lisa. And how did they know what her phone number was and who her direct reports were. Those darn data brokers. We immediately went to Delete Me. It's a subscription service that removes your personal info from data brokers, hundreds of them. You sign up, you give Delete me the details about what information you want deleted because you fully control that and their experts take it from there. Now here's the neat thing. Just the other day, Lisa got an email from Deleteme about what the status is, about where her name is showing up and what they've done to delete it. DeleteMe will continually do this. They'll send you regular personalized privacy reports showing what info they found, where they found it and what they removed. It's not just a one time service. It's always working for you. Constantly monitoring and removing the personal information you don't want on the Internet. You know you need this. We all do. It's sad, but until there's a law against it, thank goodness there's Delete Me. Delete Me does all the hard work of wiping you, your family, your company, your employees, personal information from data broker websites. They've got plans for businesses, families, individuals. Take control of your data. Keep your private life private by signing up for Delete Me. We've got a special discount for individuals today. 20% off your delete me plan. When you go to JoinDeleteMe.com TWIT and you use the promo code TWITTITCHECKOUT. But the only way to get 20% off is to go to JoinDeleteMe.com twit Enter the code TWIT at checkout JoinDeleteMe.com TWIT offer code TWIT at checkout. I hate to bring, you know, these terrible stories in, but honestly, if ever there were a need for Delete me, it's now. Joinedeleteme.com TWiT use the offer code TWiT. Sometimes the world intrudes on our nice little space here. All right, I'm ready for the picture of the week. Set me up.
- [11:34]
Steve Gibson
Okay. If you're willing to wait for our listeners. I was going to say you could go, you could jump ahead if you didn't read it out loud. Okay, so I'll wait. Okay. So what I need to explain for those who are not coders is what this, what the process of refactoring a code base is and it really comes from. It came from math where, for example, if you have the number 30, there are a bunch of factors. Right, 30, 30, right. You know, 2, 2 times 5 times 3, 15, 30. So the point is, there's different ways to break that 30 down into its factors. One of the things that happens with code is you start off with kind of an idea of what you're going to do, and you say, okay, I'm going to put these things in this file and the things that. With the user interface, they're going to go over here and things for the database go in the database file. And everything sort of starts off right. And then, you know, reality hits. You know, it's time for version 1.5 and some guy says, well, but AI now we need an AI. It's like, oh, crap, where do I put that? So you kind of stick it in somewhere just to get it working, because the boss says, you got to ship this yesterday. What's taking you so long? And a few years go by. And the point is that code notoriously does not evolve well. It just kind of. It gets stuff hung on it like barnacles and strange fungus and, you know, just. It's not good. And so it gets to a point typically where you say, okay. Some. At some point you say, okay, wait, we're having a hard time maintaining this because it just doesn't make any sense anymore. And so we need to refactor it. It basically means sort of just saying, okay, hold on, this thing over here should really go over there. And this one function ended up with so many arguments that nobody knows what it does anymore. So let's break this up into multiple smaller pieces, each which has a clearer task. I mean, sort of. It's like a rethinking of something big and. And complex. Okay, so with that background, I. The title I gave, this perfect snippet from Twitter or X was a perfect summation of where we are today with AI.
- [14:14]
Leo Laporte
All right, now, I have not seen this. I'm going to scroll up here and.
- [14:17]
Steve Gibson
You should read it to yourself.
- [14:19]
Leo Laporte
Claude just refactored my entire code base in one call. 25 tool invocations. 3,000 plus new lines, 12 brand new files. It modularized everything, broke up monoliths, cleaned up spaghetti. None of it worked, but, boy, was it beautiful. Yeah. Yeah, I've seen that happen, actually.
- [14:40]
Steve Gibson
Oh, yeah, this is just great. So anyway, so this guy Vaz is his handle on Twitter or his name, his actual handle is a lot longer. He dumped some massive code base into Claude 4 and said, Fix this. And oh, it was so impressive. Of course, it broke his code completely. Yes, he says, but oh my God, this is so pretty now. Yeah, doesn't work doesn't work, but wow, if it did, that would be great. Anyway, yes, where we are today with our AI. Okay, so the mobile threat hunting security firm Iverify posted the news of their discovery under their headline iverify uncovers evidence of zero click, which you know is the worst kind mobile exploitation in the US and at that point it's like, okay, that seems kind of generic. It could be whatever. Then we find out. They wrote throughout late 2024. So quite recently and early 2025, I verify detected anomalous activity on iPhones belonging to individuals affiliated with political campaigns, media organizations, AI companies and governments operating in the United States and the European Union. Specifically, we detected exceedingly rare crashes typically associated with sophisticated zero click attacks via iMessage, an exploitation technique previously unobserved in any systematic way in the United States. Subsequent forensic examination of several of these devices ultimately revealed a previously unknown vulnerability in the imagent image, the imagent process, you know, image agent, so they crunch it together process which owing to its relative position in the operating system and its functionality, would provide attackers a primitive for further exploitation. This vulnerability was patched by Apple in iOS 18.3. We've dubbed this vulnerability nickname because that's it's. It's taking advantage of a apparent flaw in imessage's nickname functionality, they said. In the course of our investigation, we discovered evidence suggesting but not definitively proving this vulnerability was exploited in targeted attacks as recently as March of this year. Specifically, we learned that Apple sent threat notifications to at least one device belonging to a senior government official in the EU on which we saw the highly anomalous crashes. So some correlation there we don't know about. Causation. Likewise, one device demonstrated behavior frequently associated with successful exploitation, specifically the creation and deletion of imessage attachments in bulk within a matter of seconds on several occasions after an anomalous crash. Again, that's not normal. We only observed these crashes on devices belonging to extremely high value targets. And These crashes constituted only 0.0001% of the crash log telemetry taken from a sample across 50,000 iPhones. They said while this evidence does not definitively prove exploitation, it is nonetheless difficult to ignore and merits a public discussion, particularly in light of signal gate. Our findings suggest it doesn't matter what channel is being used to communicate if the device itself is compromised. And of course that's what we've been saying all along, right? You know, you may have even with with signal, if you've got a compromise in the device, it's before it's encrypted and after it's decrypted on the device. Our findings suggest it doesn't matter what channel is being used to communicate that the device itself is compromised. Attackers have access to all conversations, regardless of whether those happen over signal, Gmail or any secure application.
- [19:32]
Leo Laporte
Excuse me.
- [19:33]
Steve Gibson
This is why it's crucial that organizations on the front lines of digital conflict, including the US Government, adapt their mobile security models to face modern threats. Our findings have been vetted by multiple independent third parties, including iOS security experts such as Patrick Wardle from the Objective by the Sea foundation, who have confidently evidence in our conclusion that mobile compromise is real, not academic or hypothetical, and that it's happening here in the United States. So what exactly are those findings? So far we've observed six devices total that we believe were targeted for exploitation by this threat actor, four of which demonstrated clear signatures associated with nickname and two which demonstrated clear signs of successful exploitation. Interestingly, all of the victims had either previously been targeted by the Chinese Communist Party, the ccp, meaning they were confirmed to have also been targeted by Salt Typhoon. They were engaging in business pursuits counter to or of particular interest to the CCP or or they had engaged in some sort of activism against the ccp. We don't have enough evidence they wrote to make clear attribution or a full view of an exploit chain, but the circumstantial evidence could indicate the ccp. So how does it work? IPhones allow you to set a nickname or avatar for numbers in your contact list. The vulnerability is likely triggered by by sending repeated rapid fire nickname updates to imessage which results in a use after free memory corruption. And of course we just in the last few months we've extensively looked at the idea of, well, of what is use after free and how a race condition could cause something you know that has been freed to get used before the access to it has completely disappeared, they wrote. This makes nickname a good candidate for a primitive to pivot off of as part of a longer exploit chain. We believe this vulnerability correlates with successful iPhone exploitation due to four concurrent factors. First, the extreme rarity of these specific crash patterns, less than 0.001% of all crash logs. Second, their exclusive appearance on devices belonging to high value targets. Third, similarity to crash patterns seen in previously known spyware attacks and finally, evidence of successful exploitation including the receipt of at least one Apple threat notification proximal to the observed behavior and evidence of cleaning behavior. So is it still active? Differential analysis reveals the vulnerability was patched in the iOS 3.2.18 release. However, nickname could be one link in a larger exploit chain. It's possible that there are other elements of the exploit chain that are still active, which is why we're only speaking about the link in the chain that has definitively been patched. We provide a full technical analysis and look forward to sharing any additional material findings when our investigation concludes. I've got a link in our in the show notes to their full technical report, which is extremely thorough and it's important to disclose that Apple is is actively contesting this. Although boy, I mean the evidence surely does point at this Axios reported Apple has fixed the flaw which was present in iOS versions through 8.1.1, but disputes that it was ever used to hack devices. Ivan Krztick, head of Apple Security Engineering and Architecture, said in a statement, we've thoroughly analyzed the information provided by Iverify and strongly disagree with the claims of a targeted attack against our users. Krstick added Apple confirmed the underlying nickname bug, but said its own field data from iPhones points to it being a conventional software bug that we identified and fixed in iOS 18.3. He said iverify has not responded with meaningful technical evidence supporting their claims and we are not currently aware of any credible indication that the bug points to an exploitation attempt or active attack. We are constantly working to stay ahead of new and emerging threats and will continue to work tirelessly to protect our users. Okay, so the results are at best ambiguous. On the Iverify side, you know, if it walks like a duck and quacks like a duck, you know, which this flaw certainly did, then it really would be reasonable to conclude that it's probably a duck. But as we have observed and talked about long ago, back when Kaspersky discovered some of their iPhones containing very similar malware, the very fact that iPhones have been so tightly locked down actively thwarts the type of post exploitation forensic analysis that would allow third parties like Iverify to, you know, to be able to dig more deeply and to help put pressure on and, you know, kind of keep Apple honest if indeed they were not already being, you know, I mean Apple certainly doesn't want this to be true. Boy, but the circumstantial evidence, which you know is circumstantial because it's the only evidence you can get because these iPhones are so well protected. The trouble is that they know the stakes in all this have, as we know, have been raised to such a high level. I verify referred to Signal Gate in their posting, reminding US of the threat that high level classified military operations planning was now known to have been conducted on non secured civilian smartphone hardware. They didn't identify who these people were that were attacked, but they did. They were explicit about saying individuals in the US very high value targets in the United States. They ended their disclosure with an important reminder. Iverify did, they wrote. Iverify recommends that high risk users keep their phones updated and turn on Apple's lockdown mode which is designed to guard against spyware. Iverify COO Rocky Cole said that it's likely that lockdown mode would have prevented these potential infections. And so that's just a reminder about that given, you know, that all the evidence continues to show. You know, just consider last month's PWN to own competition against fully patched systems that we do not still do not currently have the technology or capability to perfectly secure our devices. You know, so having a bifurcated feature set where fewer features can be offered optionally to obtain greater security makes all kinds of sense. It's like Microsoft disabling their Edge browser's JIT, their just in time JavaScript compiler after observing that 80% of of their Chromium based browsers security problems were being discovered in the Just In Time compiler. And with computers having become so fast today that the Just in Time compiler optimization is way less necessary than it once was. So you know, as we recall they did some experiments where they experimentally turned it off in Edge and nobody noticed. And so they thought well let's just just leave it off because we have a much more secure browser with it that way. So anyway, no one's ever going to know. There was some reporting, I think it was last week or the week before where somebody that, that I was referring to had made the comment that while we don't get details from Apple, they do keep fixing things and rebooting our phones. And oh, it was about the whole jailbreak, the evolution in jailbreaking and how it was now much less feasible to like, certainly not as a hobby, you know, offering jailbreaking services. Those days are gone. But the point being, you know, Apple is still releasing super critical important updates. They don't tell us why or how or what, but they're happening. So it feels like also if you.
- [29:28]
Leo Laporte
Really are a high risk subject, you shouldn't be using a consumer grade smartphone to begin with. Right?
- [29:35]
Steve Gibson
Yes. Yeah, yeah. As we covered at the time, it was, I think it was Obama who was very upset that that they took away his BlackBerry BlackBerry away like hey.
- [29:48]
Leo Laporte
But that's what, you know, that's what our security agencies do is they create hardened devices for this.
- [29:56]
Steve Gibson
Yeah. And they're much less fun to use. Yeah, sure, yeah, you know they are. Yeah. It's just they don't have all the bells and whistles and goodies because every extra goodie is one more opportunity for exploitation, as we well know. Okay, so I've got two quick bits that should serve to remind us, and that's just why I'm doing this, that the open source library system is more or less under constant attack, which is leo, where we say why we can't have nice things because really, gosh. Okay, so the node JavaScript Package Manager npm, the facility. Its facility description reads, just to remind everybody. Relied upon by more than 17 million developers worldwide, NPM is committed to making JavaScript development elegant, productive and safe. The free NPM Registry has become the center of JavaScript code sharing and with more than 2 million packages, the largest software registry in the world. Our other tools and services take the registry and the work you do around it to the next level. Great.
- [31:21]
Leo Laporte
And of course Claude code is installed, as are many tools through npm.
- [31:28]
Steve Gibson
Right.
- [31:28]
Leo Laporte
So if you're doing vibe coding, you probably use an NPM and I mean.
- [31:33]
Steve Gibson
The concept of a huge repository of, of useful libraries where you can say, oh, I need a regex parser, grab it from here. Oh, I need a background log writer. Oh, grab it from there. And you piece together a package using the well intentioned and hopefully proven work of many other authors in order to glue together solutions much more easily. Unfortunately, its openness is also its challenge. The first piece of news that caused me to pause here was 84 malicious npm packages were discovered and taken down last week, the advisory said. Check out the GitHub Security Advisory portal for more details. This also includes two packages spotted by Socket that would wipe production systems almost.
- [32:36]
Leo Laporte
As well as an AI can.
- [32:38]
Steve Gibson
Nasty. Yeah, almost as bad as asking AI to refactor our code. Please. It used to work. I hope there's an undo on this. The second piece of news was A threat actor has compromised 16 npm libraries from the Gluestack UI framework. The attacker compromised a Gluestack Admins account, adding a remote access Trojan to the libraries and pushed updates on Friday. The affected packages are extremely popular and have almost one. Get this, Leo. One million weekly downloads.
- [33:18]
Leo Laporte
Oh, geez.
- [33:19]
Steve Gibson
Aikido Security says the attacker is the same threat actor behind another supply chain attack on the RAND user agent package last month.
- [33:29]
Leo Laporte
Oh, we talked about that.
- [33:30]
Steve Gibson
Yeah, yeah. And I have a snippet from Keto securities posting in the show notes they note active NPM supply chain attack 1 million weekly downloads. They wrote. Today we uncovered a rapidly evolving supply chain attack targeting glue stack packages on npm. More than 15 packages compromised so far. Nearly again 1 million weekly downloads. Malware includes a full featured Remote Access Remote Access Trojan. Lovely abbreviation is rat. Of course the latest package was compromised just one hour ago before their one hour previous, you know, before their posting.
- [34:17]
Leo Laporte
Wow.
- [34:17]
Steve Gibson
The same threat actor behind the RAND user agent attack is now targeting UI focused packages like EACT native area button and gluestack UIutils and more. The malware gives attackers the ability to run shell commands, upload files, persist across even after update. I'm sorry, persist access even after updates. This could have a massive impact, particularly for mobile developers using React native. So developers check your dependencies. Now security teams review access logs for anything suspicious. They said they finished. We're tracking this live so we will give updates. So this is another psa. In this case it's a programmer service announcement reminding and cautioning all of our listeners who may be availing themselves of the true value. I mean this is the problem is this stuff is really valuable. So there's a strong interest in going there and using it. This true value of shared open libraries to nonetheless always remain vigilant and aware that not everyone who places code there is motivated by altruism.
- [35:43]
Leo Laporte
Are there silly question libraries like this for assembly language? Any assembly language Package repositories in the old.
- [35:54]
Steve Gibson
It's funny because there's never been a market believe it or not there, there were in the early days there were a couple assembly language libraries like macro libraries or something. Yeah and some book and you know the floppy disk and later a CD bound into the back cover, you know, so and it was like, you know, it was like some, some well meaning programmer sat down and wrote a toolkit. Here's a bunch of things to put text on the screen. Here's a bunch of sorting routines. Here's a, you know, this, this and that. Just sort of a hodgepodge. But after selling two copies the publisher decided by them both.
- [36:37]
Leo Laporte
Okay, you know, that's one of the reasons I like Common Lisp. There's nobody messing with the, with the Common Lisp package libraries. There's a good one called Quick Lisp. There's a new one called ultralisp, but I don't think attack. It's not a target rich environment, shall we say?
- [36:54]
Steve Gibson
No, it's why I kept my realtor on Windows 98 for so long.
- [36:59]
Leo Laporte
Yeah.
- [37:00]
Steve Gibson
Because she was worried about viruses. And I said, judy, you have different DNA in your computer. Viruses don't know. They look at that, go, what? Where am I?
- [37:09]
Leo Laporte
They don't care. It's like, I don't want this person.
- [37:17]
Steve Gibson
Time for a break. I'm gonna wet my whistle. And then we're gonna look at what happened with Comcast and Digital Realty. I didn't realize, I didn't know about Digital Realty. They are a massive data center provider. Like, like it turns out that AWS and Google and those guys, they subcontract.
- [37:36]
Leo Laporte
Yeah.
- [37:37]
Steve Gibson
Their space.
- [37:37]
Leo Laporte
That's a good business, Ed. Think about it.
- [37:40]
Steve Gibson
Yeah.
- [37:41]
Leo Laporte
You want to make money? Don't be a gold miner. Be the guys that make the picks and shovels. Yeah, we'll get to that in just a second. But first, a word from Bitwarden. You know, I love talking about Bitwarden, the trusted leader and password management. Yes. But of course we got to include passkeys now. All my passkeys are in Bitwarden. I am so thrilled more and more sites are using passkeys. It makes me so happy. They're also good for secrets management. If you're a developer, you know, you have a lot of API keys and secrets and stuff. And gosh, how, how close have you come to committing it in public to GitHub? Right. I know you have because so many people do and you stopped. But if you storm in Bitwarden, you don't have to Worry about it. SSH keys too. Bitwarden is consistently ranked number one in user satisfaction by G2 and software reviews more than 10 million users across 180 countries. And, and this is something maybe you didn't know. Of course we know. Bit Warden is great for individuals. 50,000 businesses too. It's great in business. Oh, and if you're traveling, Bit Warden password manager can make your travels safer and easier. Do what I do. Add your passport to your vault for easy access to, I don't know, tax free shopping. Secretly share your hotel or locker code with your travel partner. There's a lot of stuff as you're traveling around you'd want to keep on your phone. You want to keep with you, but you don't want just anybody to see it. I got my driver's license, my Social Security, my passport. It's all in Bit Warden. Let's say you're at an airport or hotel and you want to use the WiFi. Take proactive steps to secure your data. Encrypt it right with Bit Warden, protect against cyber threats. And by the way, only connect to the official Airport WI FI network. Okay? And if you're using Bit Warden, turn on Autofill for credentials because then you don't have to worry about automatically filling a phishing site with your password. That's a very nice feature. Prevent your device from automatically reconnecting the public WI Fi, but forgetting the network in your device's settings. This is just good advice after use. Avoid downloading files or clicking unfamiliar links or accessing sensitive personal or work accounts while connected to public WI Fi. It has nothing to do with Bit Warden. But you know what? They care about you. They want to keep you safe. Students are now mostly online, right? They spend learning, homework, but also socializing and gaming. I think kids nowadays, 90% of their time's online. And with all this comes, of course, many accounts, many passwords, and you know, you may have a smart student in your family or in your friend group. Even if the student knows the security risks, a lot of times convenience takes precedent. Kids, you know, they feel invulnerable. Make sure the young people in your life have a password manager like Bit Warden. It generates unique, strong passwords that are only used once on every site. Students can use them, access them from any device. And by the way, Bitwarden is free for individuals because it's open source. Now. Steve and I, I think pay the $10 a year for the, for the, you know, supporter badge, but it's free forever for individuals. Unlimited passwords, pass keys, hardware keys, all of the features I just talked about. And by the way, tell the kids this is going to help your job prospects when you get out of school. Cybersecurity skills are in high demand. Potential employers will appreciate employees with a solid understanding of password management. You know, if I were an employer, I'd put that on the interview. Do you use a password manager? I would certainly want to know that before I hired anybody. And good news in business and anywhere, Bit Warden setup only takes a few minutes. You can import from most password management solutions automatically. And as I always hammer in, I think anytime you use cryptography, it should be open source. Bit Warden is fully open source, GPL licensed. The code's on GitHub, anyone can look at it. And of course they always, every year bring in third party experts to assure you that it's exactly as safe as they can make it. They meet SoC2 Type 2 GDPR, HIPAA, CCPA compliance, ISO 2700-12002 certs. Get started today with Bitwarden's free trial of a team or enterprise planner. Get started for free across all devices and individual user. Get those students, the young people, an account. Do them a favor. Tell them it'll help you get hired. Bidwarden.com twit in your business. If somebody, if an employee, future employee, prospective employee, says I use bit warden, you know they're good. Bitwarden.com Twitter we thank them so much for their support of the good works that Steve does here at Security Now.
- [42:40]
Steve Gibson
Okay, so I was scanning reports of a possible undisclosed breach of Comcast and the major data center enterprise Digital Realty when I encountered this comment quote Inside two major US Telecom operators incident response staff Leo, are you sitting down? Incident response staff have been instructed by outside counsel not to look for signs of Salt Typhoon.
- [43:15]
Leo Laporte
As a Comcast user, we're using it right now. I'm a little disturbed, perturbed.
- [43:21]
Steve Gibson
Inside two major US Telecom operators incident response staff have been instructed by outside counsel not to look for signs of Salt Typhoon, said one of the people declining to name the firms because the.
- [43:36]
Leo Laporte
Matter is sensitive because he wouldn't want to find it.
- [43:39]
Steve Gibson
Gee, you think so? That's what has evolved from the intersection of big business cybersecurity and legal accountability. The reporting is from nextgov's Cybersecurity Reporter. The headline of the story was US Agencies assessed Chinese Telecom hackers Likely hit Data center and Residential Internet Providers. Now this headline teases us with the phrase US Agencies, which begs the question which US Agencies made this assessment? To that end, the reporting says two US Security agencies listed mass media provider Comcast and data center giant Digital realty among companies likely ensnared by a Chinese hacking group previously found inside major US and global telecom operators, according to three people familiar with the matter. So triple sourced reporting. And guess who those two U.S. security agencies are? The National Security Agency? Yes, our NSA, they wrote, made the determination that Comcast had likely been impacted by the group known as Salt Typhoon. According to two of the three people, the Cybersecurity and Infrastructure Security Agency, our illustrious cisa cataloged digital realty as being potentially compromised, the third person said. The people spoke on the condition of anonymity to discuss the matter's sensitivity. Salt Typhoon breached major telecom carriers in a global multi year espionage campaign uncovered last year. Over time, news trickled out about the scope and scale of the incident, which was first reported by the Wall Street Journal. The hacking unit is part of a broader syndicate of state backed groups tied to different military and intelligence arms of China's central government. The Typhoon moniker comes from a Microsoft naming convention for Beijing linked cyber actors. Such intrusions, especially into a data center environment, could give the hackers a potentially far deeper foothold in into infrastructure supporting the world's information service providers than previously known. This was what was really creepy about this. I hadn't really considered that data centers offer a different view than telecom providers, they wrote. The agency's assessments have not been previously reported. There's uncertainty among officials about who was impacted by salt typhoon. Various agencies across the US Government are in possession of lists of confirmed or potential victims, but it's not clear if the tallies are consistent with each other, adding to confusion about who may have been accessed, targeted or marked for investigation. Cisa, for instance, is in possession of a list of both telecom and information technology companies, but an FBI tabulation shows different entities and here it comes, they wrote. Making investigations into the breach more complicated is that multiple telecom providers have invoked legal strategies to protect themselves from from disclosing compromise by the hackers. And here's the this is what I quoted that caught me there, just brought me up short Inside two major US telecom operators incident response staff have been instructed by outside counsel not to look for signs of salt typhoon, said one of the people declining to name the firms because the matter is sensitive. Yeah, I bet it's so yes, now we have deliberate and internally formalized heads buried in the sand strategies in place because employees after all may be deposed under oath. I hope that any cross examining council has the presence of mind to ask oh, whether they were ever instructed by anyone to avoid looking for signs of external intrusion, not just are they aware of any signs of external intrusion. The article continues. One of the sources said that having been assessed as likely victims oh, and I should just mention it might be that the external council knows that counsel, that cross examining counsel might ask them just that were you ever instructed not to look? And that when you think about it, saying yes I was instructed not to look is probably less damaging than looking and finding that is it's like better to say yeah, my boss has told me don't look. So oops, I don't know. It's probably better not to know. I mean even to admit that you were told not to look than it is to be able to, you know, than if you did look and then had to say yeah and I did find evidence that we were compromised that think about it, that's probably more damaging. So what a world. One of the sources they wrote said that having been assessed as Likely victims. CISA representatives should have contacted Digital Realty and Comcast multiple times since December. It's not clear whether consistent back and forth communications were established. CISA tends to initiate outreach to potential victims when it's believed their networks are compromised, according to another person familiar with the Cyber Defense Agency's notification process. Now, of course, a new concern this year is that CISA has recently suffered a significant and controversial reduction in personnel as a result of the job cuts enacted by doge. In the same way that it's impossible to prove a negative, it can be challenging to justify the presence of staff whose job is to prevent the trouble. Right? It's like, well, they're here to prevent trouble. You know, this is, of course, this is the problem. This is a familiar problem. It's one that corporate CISOs also face. But on a government agency scale, in the case of cisa, you know, someone challenges, what are all those people doing over there? To which the reply is, well, they're keeping an eye on things. Which is then followed by the difficult to defend challenge. So why do we need so many of them?
- [51:09]
Leo Laporte
Right?
- [51:10]
Steve Gibson
You know, I don't know. So, as all of our listeners will appreciate, sissa, as we've often said on this podcast, has been doing a surprisingly tremendous job since it really got rolling a few years ago. I've often commented that I've been surprised by how proactive and effective it has been, especially considering that it's a government agency. So I hope, I sincerely hope these cutbacks will not compromise that. It's probably impossible to accurately gauge since we cannot know how things would have been with a significantly smaller cisa. We'll just need to watch and see the reporting continues. Writing a Comcast spokesperson told nextgov, quote, we've worked with law enforcement and government agencies and have closely monitored our network. So this is Comcast speaking. We have found no evidence that Salt Typhoon has impacted our enterprise network, unquote. An intrusion into either provider could carry significant national security risks. Comcast, they write, facilitates Internet access for millions of users and businesses, while Digital Realty hosts troves of physical infrastructure used by telecom operators, cloud providers and governments to route global Web traffic. A CISA spokesperson said, quote, as a policy, we do not comment on individual entities. The nsa, for their part, declined to comment, and the FBI did not respond to a request for comment. Digital Realty did not return multiple requests for comment. Nextgov reported in December that hundreds of organizations were notified. Hundreds of organizations were notified of potential Salt Typhoon compromise. Last month, cyberscoop reported that CISA and the FBI devised a coordinated notification campaign to alert affected companies and help them deter the hacks, sometimes providing new data to them on an hourly basis. The FBI concurred with other agency assessments that the SALT typhoon attacks, broadly speaking, are the most egregious national security breach in US history by a nation state hacking group. Mark Rogers, a seasoned telecommunications cybersecurity expert said, quote, a breach of Comcast and Digital Realty would confirm what many of us in the cybersecurity industry already suspected, that the SALT campaign was broader than just telcos and we have low confidence the attackers have been evicted. Nextgov obtained an internal CISA list of communications sector hardware and software products found to have been exploited by the China linked hacking groups of several listed. One of those vulnerabilities first discovered in 2018 was found in Micro Tickets routers and some of the software flaws exploited by SALT Typhoon were first disclosed in 2018, same year as the Mikrotik router flaws. Mark Rogers said something that isn't being talked about enough is that the initial way in which these attackers used were simple flaws like 8 year old vulnerabilities and credential theft. Instead of talking about ripping and replacing, we should be looking at why we aren't simply patching and maintaining our existing critical infrastructure. Eric Hanselman, the chief technology, media and telecommunications research analyst at S and P Global Market Intelligence, explained that Chinese access into data center and colocation firms would provide the hackers with a different target set compared to messaging services operated by traditional carriers. This is him speaking. The additional risk created would be they're gaining the ability to monitor intra service and intra application communications traffic that does not normally traverse the Internet backbone. That could include storage traffic moving from colocation environments into cloud or traffic moving from hosted environments into on premises infrastructure. That traffic might have less robust protections as it's not traversing the open Internet. In other words, it might all be behind firewalls. So where we trust everybody inside behind the firewall? Digital Realty writes NextGov has over 300 data centers. This is, this was surprised me. Digital Realty has over 300 data centers across 25 countries and 50 metropolitan areas including to a company marketing webpage. They list Amazon Web Services, Google Cloud, IBM, Microsoft and Nvidia among their clients. The company is considered one of the largest data center colocation providers in the world, housing the physical systems where cloud and telecom networks exchange data and they're believed to have been compromised. Eric Hanselman said we can reasonably assume that these attackers are already have sufficient access into Internet infrastructure and are looking to expand the depth with which they can monitor other activities that are taking place within Data center environments. Comcast's broadband and data and cable customer base is around 51 million, while its total wireless customer count totals around 8.1 million, according to recent earnings data. It's widely believed that Salt Typhoon has still not been excised from telecom systems, despite public statements from companies saying otherwise. On the other hand, they've been told not to look too closely. On Thursday they write well known Republican Senator Josh Hawley said in a Senate Homeland Security Committee hearing that the hackers are still inside. He said, quote, if a foreign actor chose to concentrate on any member of the audience here, we were told behind closed doors, of course, but what we were told is that foreign actors basically have unlimited access to our voice messages and our telephone calls. President Donald Trump, Vice President J.D. vance and a range of U.S. officials had their calls and texts directly targeted by Salt Typhoon hacks. The cyber spies accessed providers lawful intercept systems used to comply with government orders requiring access to communications metadata for law enforcement investigations. Wow. And remember that as we previously saw, Salt Typhoon's apparent way into these major telecom backbone providers was not rocket science nor advanced PWN to own style elite hacking. It was simply that someone somewhere within telecom's sprawling and largely out of control infrastructure, somewhere, somewhere there were older, unpatched systems still online with known vulnerabilities, the reporting says. A spokesperson for the House China Select Committee said in an email, if these reports are accurate, they point to yet another serious and deeply concerning example of the Chinese Communist Party targeting America's digital infrastructure, and noted that, quote, the panel has repeatedly warned about the CCP's efforts to exploit access points into our communications networks and this apparent breach reinforces the urgent need to harden our defenses. In March, the House's Homeland Security Committee Chair Chair Republican Representative Mark Green of Tennessee sent a request to DHS asking the agency to transmit internal documents about Salt Typhoon and another Chinese hacking unit, Volt Typhoon, Greene said in a statement to nextgov, quote, every new detail that emerges surrounding the Salt Typhoon intrusions to teaches us the lengths Chinese backed hackers will go to undermine the integrity of our critical infrastructure, our US Sovereignty and the privacy of Americans, Green said. This is in reference to recent testimony from DHS Secretary Kristi Noem saying CISA is lacking detailed information about the telecom hacks. Okay. It's difficult not to wonder whether some additional manpower at CISA might help, green added. My colleagues and I on the committee share this concern, which is why we sent a letter in March to examine the previous administration's response to the Volt and Salt typhoon intrusions. Now, I was about to comment on that, that is that they were sending a letter about the previous administration's responses when I saw that nextgov's reporting had already done so, they wrote The Cyber Safety Review Board, a DHS body that was dismissed at the start of the Trump administration, was in the middle of investigating the Chinese telecom hacks. Lawmakers have called for it to be reinstated. CISA has also been mired in budget plans to slash significant parts of its workforce and operations. So I hope that CISA will be able to recover and rebuild whatever effectiveness it may have lost. It seems pretty clear that unfortunately, private industry is unwilling to to expend the cost and effort required to fully secure its own business operations. You know, they'd rather have their attorneys say, oh don't you know, don't tell anybody, but we'd like you not to look too closely because you, you could be put under oath and cross examined and we would rather have you say we were told not to look than we looked and found evidence of Chinese intrusion into our enterprise. When the public depends upon the security of those operations, there is clearly a legitimate need for oversight, for regulation, which can only come from the government, and for accountability that apparently needs to be imposed by the government. So hope we get that. Matthew Green, our illustrious cryptographer, says. Well, he concurs. I mentioned briefly in passing last week that someone named Matthew Garrett had looked at the encryption mechanisms underlying X's supposedly new all new, remember, rewritten in rust, end to end, encrypted X chat dm, you know, direct message facility and had decided that it was no better than the old one. He shared Elon's declaration about how it was written in Rust and unfortunately it turns out it's still written in C and C. Since then, Matthew Garrett's posting came to the attention of another Matthew. This Matthew was none other than the renowned Johns Hopkins University cryptographer Matthew Green. This Matthew is well known to this podcast. So this Matthew's posting last week titled A Bit More on Twitter X's new encrypted messaging is of interest. Matthews post is longer than we need and I've included a link to the entire thing in the show notes. So I'm just going to share his relatively short, bullet pointed introduction and summary. It'll really tell us as much as we need. So he wrote. Matthew Green posted. Matthew Garrett has a nice post about Twitter X's new end to end encryption messaging protocol, which is now called X Chat. The TLDR of Matthew's post is that from a cryptographic perspective, X Chat is not great. The details are all contained within Matthew's post, Matthew Green writes. But here's a quick TLDR from Matthew Green. First, there's no forward secrecy. Unlike Signal protocol, which uses a double ratchet to continuously update the user's secret keys, the Xchat cryptography just encrypts each message under a recipient's long term public key. The actual encryption mechanism is based on an encryption scheme from Libsodium. Second user Again, here it is. User private keys are stored at x.xchat stores user private keys at its own servers. To obtain your private keys, you first log into X's key storage system using a passwords such as a pin. This is needed to support stateless clients like web browsers. And in fairness, he writes, it's not dissimilar to what Meta has done with its encryption for Facebook messenger and Instagram. Of course those services use hardware security modules. And third, he says X's key storage is based on Juice Box. To implement their Secret storage system, XChat uses a protocol called Juicebox. Juicebox shards your key material across three servers so that in principle the loss or compromise of any one server won't hurt you. Okay so and we've talked about key sharing schemes in the past where a key is broken up into pieces so that no one person has the entire key and you see you need some some number of individuals to all come together in order to reassemble the original key. This sounds like what Juice Box is doing. So our Matthew Green writes. Matthew's post correctly identifies that the major vulnerability in X's system is this key storage approach. If decryption keys live in 3 non HSM servers that that are all under X's control, then X could probably obtain anyone's key and decrypt their messages. X could do this for their own internal purposes, for example, because there he writes, their famously chill owner got angry at some user. Or they could do it because a warrant or subpoena compels them to. If we judge X Chat as an end to end encryption scheme, this seems like a pretty game over type of vulnerability. And he says so in a sense everything comes down to the security of Juicebox and the specific deployment choices that X made. Since Matthew wrote his post, writes Matthew Green, I've learned a bit more about both of these in this post. I'd like to go on a slightly deeper dive into the juice box portion of X's system. This will hopefully shed some light on what X is up to and why you should not use X chat. So the bottom line is that Matthew Green concurs with Matthew Garrett, which is to say that no one should consider any encrypted messaging system to be securely end to end encrypted when such a system externally stores on its user's behalf their private keys. Now a perfect example is Apple's currently controversial Advanced Data Protection. What it explicitly does is give its users discretionary control over whether or not a copy of their private key is also retained by Apple. Allowing that enables additional features, but it also enables Apple to similarly respond to court ordered subpoenas in the case of Advanced data protection. If that's not what you want, or if you're and if you're not in the United Kingdom and all of your devices are running Apple OSs that support ADP, you know, iOS or iPadOS 16.2 or later in the case of iPhone and iPad, then you can turn that on and a new private key Apple has never seen will be created and shared only among your idevices. So no one should confuse Apple's state of the art encryption technology and for that matter signals with what Elon is peddling. I'm not suggesting that anyone necessarily needs end to end encrypted DMS on X, but everyone should be aware that they're not really available there to the same degree they are elsewhere. Nor for that matter are they available on Facebook, messenger or Instagram, which, as Matthew Green notes, similarly stores its users private keys in their own data centers in order to enable the features that are necessary. Leo, we're at an hour in. I want to talk about what we learned about Telegram. Let's take our third break.
- [71:35]
Leo Laporte
Indeed we shall. Thank you Steve. This is a good time to mention that this portion of security now is brought to you by material. Because you know what, when it comes to security, you need security in your email, don't you? Material is the multi layered detection and response toolkit for email. Nowadays we all, you know, have a cloud office, right? We use Google workspace, maybe use Microsoft's 365. It's the heart of your business. But the problem is traditional security tools don't really know about that. They treat email and documents as kind of afterthoughts, which means your most critical assets are exposed. Material transforms cloud workspace protection with a revolutionary approach. It goes beyond traditional security paradigms. Dedicated security for modern workspaces ensures purpose built protection specifically designed for Google Workspace and Microsoft 365. You get complete protection across the entire security life cycle. That means defending your organization before, during and even after potential incidents, not just attempting to block them or prevent them. Material allows you to scale security without scaling your team. Because your team is now using intelligent automation to multiply their impact. It's a force multiplier. They provide security that respects how people work, eliminates the impossible choice between robust protection and productivity. And it's all very cleverly done. Turns out Google Workspace and Microsoft 365 have very robust APIs that allow material to protect you without having you send your data through Material. Material delivers comprehensive threat defense through four critical capabilities. Phishing protection. They have AI power detection that identifies sophisticated attacks. Again, API based. They also help you with data loss prevention. They have intelligent content protection and sensitive data management. They will help you with your posture management, identifying misconfigurations and risky user behaviors. And of course identity protection. Comprehensive control. We were just talking about it over access and verification. You know who uses Material? Figma. I love this. The head of security of figma. They're a design firm, right? He said, quote, it's rare to find modern security tools with a pleasant usable ui. Being at Figma, we're obviously attracted to well designed interfaces and Material's interface was just so smooth and so slick. And that's because of their secret sauce. This API based protection. From automatic threat investigation to custom detection workflows. Material converts manual security tasks into streamlined intelligent processes. It provides visibility across your entire digital workspace. Which means your security team can focus on strategic initiatives instead of endless, pointless, sometimes alert triage. Protect your digital workspace. Empower your team, secure your future with material. Go to Material Security. You can learn more and book a demo. That's Material Security. This is a modern way to protect yourself and very, very effective in this modern time when we're all kind of living in the cloud. Material Security. Thank you Material for supporting Steve Gibson back to the show.
- [75:09]
Steve Gibson
I'm so jealous of that top level domain.
- [75:11]
Leo Laporte
But isn't that great? Dot Security.
- [75:14]
Steve Gibson
How much? Insanely expensive.
- [75:16]
Leo Laporte
Yeah, of course.
- [75:17]
Steve Gibson
I think it was like $25,000 a year.
- [75:19]
Leo Laporte
Oh, that's nothing. Dude.
- [75:20]
Steve Gibson
Crazy.
- [75:23]
Leo Laporte
What would you do? GRC Security.
- [75:25]
Steve Gibson
I don't know. I know I don't really want it. I love GRC.com is pretty darn good. Yeah.
- [75:29]
Leo Laporte
You know those three letter TLDS are. Are even more expensive.
- [75:33]
Steve Gibson
Yeah. Oh, I get offers all the time.
- [75:35]
Leo Laporte
Sure. Yeah.
- [75:38]
Steve Gibson
Okay. So I also recently mentioned that Telegram's encrypted privacy had recently been called into some question when Russian citizens were who were supporting Ukraine. Oh, naughty Russians were being arrested and convicted by Russia's fsb. It turns out that the culprit might not be any weakness in Telegram's. It's a little questionable encryption, but it's probably good enough. It could instead be a compromise of its network infrastructure. In other words, there may be some leakage of messaging metadata. And we've talked about metadata a lot. We know that it can be notoriously difficult to prevent metadata leakage. You know, it's why we've gone to all the lengths of creating the Tor network. You know, and when you turns out, you couple that with the fact that Telegram's network infrastructure appears to be directly under Russia's control, that's a problem for privacy. So this could explain how people are getting in trouble for who they contact without needing to see inside their messages. I don't, I'm not going to spend any more time on this because, you know, this brings us to another of those, you know, I wouldn't use Telegram in any event, if you really care about privacy. But apparently it is worth noting that Telegram's networking infrastructure is entirely under the control of at least Russia sympathizers. I've got a link to extremely detailed coverage of this in the show Notes for anyone who wants more. The report is titled Telegram, the FSB and the man in the Middle. The technical infrastructure that underpins Telegram is controlled by a man whose companies have collaborated with Russian intelligence services. So again, who you connect with can be just as damning as what you say during that connection. Especially if you're in Russia and you're connecting to a Telegram contact that supports the Ukraine, apparently. So don't do that. Okay, Leo, here's where I need to control my, my, my language. Bleeping Computer.
- [78:11]
Leo Laporte
I want to hear what this AI figured out about your opinion about Microsoft.
- [78:16]
Steve Gibson
Oh, yeah, we're going to get there in a second. Yeah. Bleeping Computer brings us the news that starting in July. So next month. Starting next month. Sometime next month, Microsoft Outlook will be blocking two additional file types, Bleeping Computer reported. Microsoft announced it will expand the list of blocked attachments in Outlook Web and the new Outlook for Windows starting next month. The company said In a Microsoft 365 Message center update that Outlook will block Library Ms. And Search Ms. File types beginning in July, Microsoft said as part of our ongoing efforts to enhance security in Outlook Web and the new Outlook For Windows, we're updating the default list of blocked file types in OWA Mailbox Policy. Starting in early July 2025, the Library Ms. And Search Ms. File types will be added to the blocked file types list. Windows Library Files Library ms, which define virtual collections of folders and files in the Windows file system, were used earlier this year in phishing attacks targeting government entities and private companies to exploit A Windows vulnerability CVE2025 24054 that exposes NT Land Manager hashes okay, now let me just pause here for a moment to say that if, if I didn't know that we have many young people listening to this podcast with their parents while they're on their way to school in the morning, as well as many other settings, and that those parents have grown to trust me to keep the colorfulness of my language under control for those young ears. At this point, I would loudly expand upon the well known abbreviation wtf. Why in the world Microsoft would have ever, by default, ever considered allowing any email client, which inherently, think about it, inherently presents as large an attack surface as any web browser, and which is being constantly bombarded with unwanted and potentially malicious content, to handle Library Ms. Files, which we are now told define virtual collections of folders and files. I've been in this business, as have you Leo, since long before it was a business, and I've never seen a dot Library Ms. File. How is it that this is a file type that all Outlook users clients should have ever been able to open? And how can that possibly be addressing the need that anyone has in email? It's just utterly unbelievable to me, as it should be equally unbelievable to anyone trained in the practice of cybersecurity. How many times have we talked about the security benefit that flows from first blocking everything by default and then only allowing selected, known, safe and needed content through any security perimeter? Email is a security perimeter. This is unbelievable. I'm so surprised by this, because any rational security aware design would never be permitting the reception and handling of by default any wacky file type somebody at Microsoft might come up with in the future, which is apparently what happened here, because that file type didn't exist in the past.
- [82:56]
Leo Laporte
That's why they didn't block it.
- [82:57]
Steve Gibson
Okay, but they shouldn't be. They shouldn't be. Unless we know it's bad, we're going to let it through.
- [83:04]
Leo Laporte
You're saying it should be a white list, not a blacklist?
- [83:07]
Steve Gibson
Yes, it's a security perimeter. Email is getting bombarded with all kinds of crap. Okay, take a deep Breath Steve. So what about this other file type? Bleeping computer tells us the cert the dot Search Ms. URI protocol handler has also been exploited in phishing and malware attacks. Get this. Since at least June of 2022. Oh, when Hacker House.
- [83:41]
Leo Laporte
That's three years.
- [83:42]
Steve Gibson
Yes, when Hacker House co founder and security researcher Matthew Hickey found that it could be used to automatically launch Windows Search Windows on recipients devices to trick them into launching malware when chained with a Windows support diagnostic tool. That's MSDT Remote Code Execution Vulnerability CVE 20223190 well isn't that just beachy. What year was that? Oh yeah, 2022. So it only took Microsoft what, three years to finally announce that next month? Not this month. No. Next month they plan to start blocking this other unneeded and clearly abuse prone file extension. Bleeping Computer reports that in Microsoft's announcement Microsoft wrote quote the newly blocked file types are rarely used though, except by hackers and malware and bad guys who just love using them. So most organizations, they say will not be affected by the change. However, if your users are sending and receiving affected attachments. Yeah, like when did anyone ever get a dot Search Ms. Attachment? In email they will report that they're no longer able to open or download them. And Outlook Web or the new Outlook for Windows? Apparently the old Outlook for Windows is screwed. You're still going to get those. No action is required if your organization does not rely on these file types. If your organization does rely on these file types, you got a different set of problems. The update will automatically apply to all OWA mailbox policies in your organization. If your organization needs to allow these files, you can add them back to the allowed file types property of your user's OWA Mailbox policy objects before the rollout. Why not just have that? Have it always been that way? If your organization needs one of these wacky no one has ever heard of them file types, then turn them on for you know your people and good luck to you rather than exposing the rest of the world to this nonsense. Bleeping computer then explains you can find the complete list of blocked Outlook attachments. It's apparently very short list on Microsoft's documentation website. Enterprise users with a Microsoft Exchange server account can ask to Exchange server administrators to adjust security settings for their mailboxes to accept attachments blocked by Outlook if they can't be shared as an archive using a different Extension or using OneDrive or SharePoint. This move is part of a much broader effort, apparently, which Microsoft has just initiated to remove or secure and turn off Office and Windows features that have been abused and exploited to infect Microsoft customers with malware. Wow. What a concept. I'm shocked. We'll see what AI thinks about this rant. It started in 2018 when Microsoft expanded support for its anti malware scan interface AMC to Office 365 client apps. Apparently they haven't had anybody looking at this ever since 2018. Somebody woke up and said, oh look, let's add some more stuff to the AMC to block access using Office WBA macros. Since then, the company began blocking VBA Office macros by default. Another great jump, a leap for security disabled Excel 4.0 XLM macros. I remember covering that. Yay. Introduced XLM macro protection. We even gave it a nice name and started blocking untrusted XLL add ins by default. Because what could an untrusted LLM do? Wow. Microsoft also announced in May 2024 that it would so a year ago it would kill off VBScript and disabled all ActiveX controls in Windows versions. Boy, you know, I don't know. Oh again, it is truly, I mean really inexplicable that Microsoft has been so utterly lame about the security of their email clients on the desktop and in the cloud. The only rational explanation is this was all originally put in place by engineers who had zero training in security. Hubris is the only explanation for a policy of allow everything to run by default. It is the exact equivalent of how we have of having an allow all firewall policy and believing that it could ever be secure to only block the dangerous ports. Nobody does that. Haven't for a long time. Microsoft's just beginning to wake up to this and say, oh look, three years ago people began exploiting the DOT Search Ms. Extension which nobody has ever needed or uses, but which Microsoft says, oh look, let's open that. My God. Okay, as we were.
- [89:50]
Leo Laporte
Deep breath. I mean, yeah, I can't think of any reason. I mean, one thing would be that engineers say, well, you should just be able to send anything you want. Why wouldn't.
- [90:01]
Steve Gibson
Yeah, what could possibly go wrong? All of our code is perfect. We never have any flaws. Just ignore those 125 critical updates that we had last month and the next 150 that we've got planned for this coming month. Really, those are just exceptions. Besides, none of those were DOT Search Ms. So you know, you know, wouldn't have been would this wouldn't have helped anyway. It's unbelievable. I mean again, that all should be turned off. And if by some bizarre. For some bizarre reason, some enterprise has to send. I don't even virtual folders and directories through email. What?
- [90:42]
Leo Laporte
Not through email? Never.
- [90:43]
Steve Gibson
No, I mean that's what this does. Whatever that was. It's unbelievable. I'm just. I'm looking forward, Leo, to October when they stop messing with Windows 10 and just will leave it alone. And then it can. It'll have a chance to settle down and then we can just keep using that. That'll be good. Okay. I don't need any more coffee, that's for sure. As we were recording last week's podcast, Leo, you encountered the news of 40,000 40000 cameras having been found online. Now this raised a bunch of questions, the first of which was probably what sort of exploit might have been needed to hack into and compromise such a huge inventory of Internet connected cameras. And the answer, it turns out, is none. All 40,000 of these video cameras are simply online and wide open, viewable by anyone, anywhere, anytime. The news of this came from Bitsite, an Internet scanning company that offers to keep an eye on the IPs and ports of its own clients to let them know when anything like this might be happening to them. In BitSite's report, they wrote, welcome to 2025, where Microsoft is still getting around. No, welcome to 2025, where thousands of Internet connected cameras meant to protect us are actually putting us at risk. In our latest research at Bitsite Trace, we found over 40,000 exposed cameras streaming live on the Internet. No passwords, no protections, just out there. We first raised the alarm in 2023, and based on this latest study, the situation has not gotten any better. These cameras, intended for security or convenience, have inadvertently become public windows into sensitive spaces, often without their owner's knowledge. No matter the reason why one individual or organization needs this kind of device, the fact that anyone can buy one, plug it in and start streaming with minimal setup is likely why this is still an ongoing threat. And it doesn't take elite hacking to access these cameras. In most cases, a regular web browser and a curious mind are all it takes. Meaning that 40,000 figure is probably just the tip of the iceberg. Okay, for their key takeaways, they wrote, bit site trace has found more than 40,000 security cameras openly accessible on the Internet, allowing anyone to view their live footage. The United States and Japan rank first and second for camera exposure. Most times, all that an attacker needs to spy on homes or even large organizations is just a web browser and the right IP address. We detected conversations on the Dark Web where bad actors are discussing exposed cameras, we scanned the entire Internet for exposed HTTP based and RTSP based cameras. The United States leads the charge with roughly 14,000 exposed online cameras, followed by Japan, Austria, Chechiya and South Korea. Given the high prevalence of exposed cameras in the United States, we also analyzed their distribution across each state. I grabbed the heat map both of the world and of the US and what's curious is that the US map is not at all uniform. It shows that a huge preponderance of open cameras are located in California and in Texas, like way more than any other two states. You know, it would be interesting actually to determine why I have no idea. As I said, the distribution is extremely non uniform. Bitsite noted that not all cameras are bad. Some people stream beaches or bird houses on purpose, but here's where things get problematic, they said. Residential cameras watching front doors, backyards and living rooms. Office cameras disclosing whiteboards and screens full of confidential information. Factory cameras showing manufacturing secrets. Even public transportation cameras streaming passengers movements. By leveraging the intelligence gathered by our awesome Cyber Threat Intelligence colleagues, we dug into dark forums where people openly discuss tools and tactics to find and abuse the content being exposed by these cameras. Even are some even some even sell access, they said. This isn't hypothetical. It's happening right now. Then they finished their synopsis with a section titled what should I do to protect myself or my Company? Their advice is what any longtime listener of this podcast would echo. They wrote. If you have a security camera at home or manage surveillance cameras for your company, then taking the right precautions can make the difference between keeping your footage private and unintentionally broadcasting it to the world. Here are some simple but essential guidelines to ensure your cameras are secured. First, check if your camera is accessible from the Internet. Try accessing it from a device outside your home network. If you can reach it remotely without logging in through a secure app or vpn, it's exposed. Second, change default usernames and passwords. Many cameras come with weak or publicly known default credentials. Set a strong unique password. Third, disable remote access if you do not need it. If you only use your camera on your home network, there's no reason to allow outside connections. Fourth, keep its firmware up to date. Manufacturers often release security updates that fix known vulnerabilities. Regularly check for updates and install them. Additionally, they wrote, if you manage security cameras in your organization, restrict access with firewalls and VPNs. Ensure that only authorized personnel can access camera feeds using a VPN or Firewall rules that block access from untrusted sources, and finally, monitor for unusual activity, set up alerts for unexpected login attempts. It really would be interesting, I think, to follow up and track down a, you know, a large set of those cameras to determine whether they are likely being deliberately shared publicly or may be inadvertently exposing parts to the physical, you know, like, views of the physical world to a global audience that should not have access to it. The idea, you know, like of a corporate camera aimed at a conference room's whiteboard is terrifying. You know, I mean, maybe they just think it's a security camera and don't realize that some, some configuration misstep, you know, allowed this thing to go out over the Internet. But clearly the consequences could be devastating. Leo, we're an hour and a half in. Let's take a break. And then I'm going to talk briefly about using spin, right, on an encrypted drive, share some feedback, and then we're going to start talking about Internet foreground radiation.
- [99:42]
Leo Laporte
All right. I hope you're enjoying the show so far. I certainly am. And we thank Steve for doing such a good job putting this all together. And we thank our sponsors who make it all possible. This episode of Security now brought to you by Drata. If you're leading risk and compliance at your company, you have our deepest sympathy. But you're probably wearing 10 hats at once, right? You're managing security risks, compliance demands, budget constraints, and it's hard to say one's more important than the other, right? And you're then all the while trying not to be seen as the roadblock that slows the business down. But GRC isn't just about checking boxes. It's a revenue driver that builds trust, accelerates deals, and strengthens security. That's why modern GRC leaders turn to Drata, a trust management platform that automates tedious tasks so you can focus on reducing risk, proving compliance, and scaling your program. With Drata, you can automate security questionnaires, automate evidence collection, automate compliance tracking gives you more time to do whatever you want. You could stay audit ready with real time monitoring. I mean, this just takes a huge load off your shoulders. It also will help you simplify security reviews. Auditors love Drata's trust center, and you'll get AI powered questionnaire assistance that makes it a snap to fill those questionnaires out instead of spending hours proving trust. Build it faster with Drata. Are you ready to modernize your GRC program? Visit drata.comsecuritynow to learn more. R-A-T-A drata.com Security now this is the premier name in in automating compliance and man, you deserve it. That's all I could say. You deserve the help draw Tocom slash Security. Now thank them for support and security now when you talk to them.
- [101:42]
Steve Gibson
All right, Steve, on with my tech support guy. Greg forwarded an interesting question about spinrite which bears sharing because its answer is not always intuitive and sometimes results in some confusion, as it did when it was recently posted over in GRC's web forums. Lee Garrison sent the email through Greg hi Steve, I need to run Spinrite 6.1 on a 3 terabyte partition which is encrypted with VeraCrypt for the purpose of locating and fixing bad sectors on this encrypted partition. The drive is a Western Digital 4 terabyte hard disk drive, meaning a spinner which also has the rest of the drive space occupied with an unencrypted partition. My question is, should I first decrypt this partition with VeraCrypt before running Spinrite on it, or should I leave it encrypted while running Spin right on it? We've been discussing this problem over on your GRC forums under the running SpinWrite topic, but with varying degree, varying opinions persisting. Yes, Leo? Leo's raising his hand. Yes, I don't have your audio.
- [103:02]
Leo Laporte
I didn't turn on my microphone, so you didn't hear my. Oh, oh, Mr. Gibson. Oh, it doesn't matter. Am I right? It doesn't matter.
- [103:13]
Steve Gibson
Correct.
- [103:14]
Leo Laporte
All right.
- [103:14]
Steve Gibson
I went over to the forum to see what the dialogue had been over there since he referred to that, and it was as Lee had asked. The answer, as you said, Leo, is that spinrite has no problem running on drives that have been encrypted with Veracrypt, TrueCrypt, BitLocker, or any other form of encryption. Since Spinrite 6.1 is seeing the drive as nothing more than opaque blocks of data, it doesn't care whether the data might be encrypted or not. Now, what's interesting is that spinrite has this real time monitor screen which presents a cool window that allows its user to see the data that's passing by as spinrite is working on it. And one of the cool things that SpinWrite users notice is that they often see their own recognizable data flashing past that window while spinrite is running on their drive. But that's an example of what encryption would change when spinwright is running on an encrypted drive or partition. That real time monitor window will never reveal any of its users recognizable data. Everything will just look like monitor static. It will be digital noise because as we know, the result of high quality encryption is data that is indistinguishable from completely random noise. So by all means Lee, run Spinwright over that encrypted partition and any damaged sectors that SpinWrite is able to recover will result in recovered files once that encrypted partition is remounted and viewed through its decryption. Okay, some other feedback Jason Egan wrote Steve, I wanted to send along my thanks to you for reminding me of the Tower of Hanoi puzzle. I had forgotten how much I'd enjoyed it as a child. I picked one up for my children who are 8 and 10 for Father's Day and Leo is showing it to us on camera and they are hooked. He said. Makes, he said. It makes me proud. Yeah, he said thanks for not only bringing us timely and informative security news, but also for interesting and fun things like this. I appreciate what you do every week, Jason.
- [105:46]
Leo Laporte
I did this because I told you I grew up with one of these and I just couldn't resist going out and buying one. They're expensive and they're a lot of fun.
- [105:54]
Steve Gibson
Yeah. And that's, that's a nice one. Different colored wood disc so you kind.
- [105:59]
Leo Laporte
Of know the even and odd. It makes it a little easier to. Yeah. To spot it and it all folds up and goes into this.
- [106:05]
Steve Gibson
Yeah, very cool.
- [106:07]
Leo Laporte
Put it away.
- [106:08]
Steve Gibson
I was wondering if the pegs like are like attached to the lid enough so that you're able to move the discs around.
- [106:15]
Leo Laporte
Yeah, you have to really jam them in so they don't. But they do come out so you can put it all in the box.
- [106:21]
Steve Gibson
Nice.
- [106:22]
Leo Laporte
Yeah, I love this. It was nothing. It was on Amazon. It was nothing. And yeah, it's just a great memory.
- [106:27]
Steve Gibson
As I said last week, there are pages of.
- [106:30]
Leo Laporte
Oh yeah.
- [106:30]
Steve Gibson
And many of them are those really nice looking blue ones with their own little box. So Jason, thank you for your note. I very much appreciate it and all the feedback our listeners take the time to send every week. And it's interesting a surprising number of our listeners mention that the podcast also makes them laugh. I assume that's mostly thanks to the picture of the week, not our silliness. Yeah, we do encounter things in the security space that are so absurd as to be ridiculous and funny. So anyway, when it. When it is occasionally impossible to both inform and entertain, well, that's a win. Brian Tillman wrote what I'm Curious about is how a newspaper can claim that it's LLMs users. Although he's referring to an article we talked about last week. How a newspaper can claim, I think was New York Times that was leading a group of. Of newspapers that were suing. I don't remember who it was, that an LLMs users are reading data that's supposed to be behind a paywall. If there's a paywall in place, how are the LLMs gaining access to that material?
- [107:44]
Leo Laporte
Same way.
- [107:45]
Steve Gibson
Doesn't seem like a very good paywall to me.
- [107:47]
Leo Laporte
No, it's not.
- [107:48]
Steve Gibson
And I think that's a really good point.
- [107:49]
Leo Laporte
You just turn off JavaScript.
- [107:52]
Steve Gibson
Yeah. Many sites like coding forums will have huge historical depth of code that could be plumbed once. So once an LLM got in there and sucked out all of its content, you know, it's game over for that site. The information has escaped. But the point of a news site is that it's news. So to Brian's point, although it may not have been clear several Years ago, today's LLMs have learned that they must legally abide by robots exclusion rules and not traverse into any sites that have explicitly banned their entry or put up a paywall.
- [108:37]
Leo Laporte
That's key. I want.
- [108:39]
Steve Gibson
And I would be pretty sure that's no longer happening.
- [108:41]
Leo Laporte
Yeah, well, it depends on the LLM. Some, some of them are very aggressive.
- [108:46]
Steve Gibson
And ignorant and I did just see something. I haven't had a chance to follow it up. I mean, it was like literally during one of our commercial breaks, someone sent something about how LLMs are getting clever about like being. LLMs are being used by hackers to get around these things. Yeah, Cloud.
- [109:02]
Leo Laporte
Cloudflare complained of that. They said, you know, then most, many, many of these spiders don't adhere to robots. Txt. But I think more and more that's going to make them liable in courts. Right. That's going to be the real problem.
- [109:17]
Steve Gibson
Right. If, if you put up a clear specification saying, you know, llai not welcome here.
- [109:25]
Leo Laporte
Right.
- [109:25]
Steve Gibson
And then there is evidence that AI got trained here. That's got a good case.
- [109:30]
Leo Laporte
Yeah.
- [109:31]
Steve Gibson
Yep. Okay. So Z ev said. Hi, Steven Leo. My name is Z ev. Yeah, Z E apostrophe ev. So I'll go with. Actually, I think you think it's what Ziv.
- [109:43]
Leo Laporte
Yeah.
- [109:44]
Steve Gibson
Okay.
- [109:44]
Leo Laporte
Well, unless he's Hawaiian. Oh, that's where he's from.
- [109:48]
Steve Gibson
And I'm a longtime listener of the Security now podcast. Your show is fantastic and I'm glad to hear that it's that there's no definitive end date in sight. Yay, he said. Recently, like many others, I become interested in AI as part of a hackathon at work. I explored the Llama Index Python library, which can be used, among other things, to easily create a retrieval augmented generation, which he calls a rag system. That immediately made me think of the incredible podcast transcripts that Elaine Ferris has created for your show. I realized it might be an interesting opportunity to use AI to gain insights from this amazing trove of data. I ended up writing a simple python program around 130 lines of code that lets you run a query or prompt to get an answer based on the transcripts.
- [110:46]
Leo Laporte
Awesome.
- [110:47]
Steve Gibson
After some experimentation, I found that indexing and querying the transcripts by year yields the best results, he said. Below are a few examples of prompts I tried and the responses I got from the LLM. He also said the code is available on GitHub here and he gives us a link I've got it in the show notes for anyone who wants to go there GitHub.com zeevin B SN and he said thank you for all the work you put into the podcast. It's been an invaluable source of knowledge and entertainment over the years. Best regards, Zev.
- [111:31]
Leo Laporte
This is cool. Now you could do this also with a Notebook LLM. If you have all the transcripts downloaded, just give them to Google's Notebook LLM and do the same thing. In fact, I did it with just a handful of them, a few months worth and made a little show and it sounds just like our show, except it's two very nice AI voices.
- [111:50]
Steve Gibson
So Ziv shared his query and the LLMs reply about our most recommended science fiction reading material and our most recommended television shows. But his third query, as I mentioned at the top and the LLMs response was the most interesting to me and I figured would be the most interesting to our listeners. What Ziv asked his transcript trained LLM was quote, how has Steve's opinion on Microsoft security changed over the years? And the LLM's reply was Steve's opinion of Microsoft Security has evolved significantly over the years, reflecting a complex interplay of recognition of improvements, growing skepticism, and critical concerns that about the company's practices. In the early years, particularly around 2015, Steve acknowledged Microsoft's efforts in managing security, noting that the company had developed defenses against constant attacks and was not frequently in the news for major breaches. He appreciated the improvements in security, but remained cautious about privacy implications, especially with Windows 10's new Windows 10's design. By 2016, his perspective began to shift toward a more critical stance, particularly regarding Microsoft's handling of updates and the promotion of Windows 10. He expressed concerns about the alignment of Microsoft's interests with those of its users and highlighted issues such as the lack of transparency in updates and and potential security risks associated with third party antivirus software. In subsequent years, Steve recognized improvements in built in security measures, particularly with Windows Defender, but he also emphasized the ongoing challenges in cybersecurity landscape. By 2018, he began to advocate for the use of built in security solutions over third party options, acknowledging the complexities of maintaining security in a rapidly evolving environment. However, as time progressed, his concerns deepened. By 2019 and into 2020, he expressed frustration with Microsoft's inconsistent handling of vulnerabilities and updates, particularly regarding support for older operating systems. He highlighted the need for users to be proactive about security and criticized Microsoft's approach to updates, which he felt often led to significant vulnerabilities. By 2021 and 2022, Steve's skepticism intensified as he noted a perceived negligence on Microsoft's part in addressing known security issues promptly. He pointed out that the company seemed to prioritize other aspects over security, leading to a growing concern about the effectiveness of their measures. In 2023, his criticism became more pronounced, focusing on Microsoft's reliance on updates and the prevalence of known vulnerabilities in their products. He expressed frustration with the company's failure to address these issues proactively and question the ethics of their approach to forcing upgrades. By 2024, Steve's opinion had crystallized into a broader skepticism about Microsoft's commitment to security, particularly in light of high profile security failures and a corporate culture that seemed to deprioritize security investments. He criticized the company's reactive approach to vulnerabilities and argued for the inclusion of essential security features in base products rather than as a paid add on. As of 2025, Steve's view reflects a recognition of the inherent complexities in securing Microsoft systems, acknowledging that while improvements have been made, the legacy nature of their software creates ongoing vulnerabilities. He advocates for additional protective measures when using their products, emphasizing the need for caution and accountability in Microsoft security practices. Overall, Steve's evolving opinion illustrates a journey from cautious optimism to critical skepticism, highlighting the need for significant changes in how Microsoft approaches security to better protect its users.
- [116:42]
Leo Laporte
I think that was fairly accurate. Do you think?
- [116:44]
Steve Gibson
Yes. I mean, you know, it has that kind of vanilla feel.
- [116:49]
Leo Laporte
Yeah, that AI thing, that AI gives things.
- [116:52]
Steve Gibson
But you cannot argue that to give something a just a bunch of text And I mean, we are living through a truly astonishing revolution where we're witnessing the emergence of a technology that's able to take transcripts of 20 years of my rambling and turn them into that. Which while, yeah, a little pablum ish still, you know, it's, it's amazing that it even is able to say this. I'm. I'm. I'm astonished.
- [117:35]
Leo Laporte
Yeah, yeah, it is amazing. Notebook LM would do the same thing. In fact, we're going to talk to the folks from Notebook LM on IM tomorrow. Yeah. Oh, you know more than I do.
- [117:48]
Steve Gibson
Cool. Yeah, cool.
- [117:50]
Leo Laporte
Yeah.
- [117:50]
Steve Gibson
Okay. Just for the sake of not breaking up this final piece. Okay, Foreground Radiation. Let's take our last break and then we're going to look at what is going on with proactive bot scanning in the foreground across the Internet. And, and it is very rare that we encounter something fundamental that we have never Talked about in 20 years of this podcast.
- [118:21]
Leo Laporte
Well, I am in the Neil Sedaka camp on this one. Breaking up is hard to do. So let's get the ad out of the way. And then Internet foreground radiation with Mr. Stephen Tiberius Gibson, who apparently knows the difference between Star Trek holo chess and Star wars holo chess. Even though as far as I could tell, they do look the same. Am I wrong? I think they do look the same.
- [118:47]
Steve Gibson
Star Trek's actually. They had three dimensional.
- [118:50]
Leo Laporte
Oh, that's right, it was three dimensional.
- [118:51]
Steve Gibson
And they had weird little three by three and four by four boards and Spock would move things around and. Yeah, no one ever explained it.
- [119:00]
Leo Laporte
Yeah, there is and there are. You can get those chessboards too and make up your own rules. All right, our show, the last advertiser for this particular episode of security now is BigID. They're the next generation AI powered data security and compliance solution. BigID is the first and only leading data security and compliance solution to uncover dark data through AI classification, to identify and manage risk and to remediate the way you want. You can also use it to map and monitor access controls, scale your data security strategy and it's got great unmatched coverage for cloud and on prem data sources. In fact, they work with anything. BigID also seamlessly integrates with your existing tech stack so you can coordinate security and remediation workflows, take action on data risks to protect against breaches, annotate data, delete quarantine more based on the data, all while maintaining an audit trail, which is very handy. As I said, it works with everything you work with partners include ServiceNow, Palo Alto Networks, Microsoft, Google, AWS and more. With BigID's advanced AI models, you can reduce risk, you can accelerate time to insight, you can gain visibility and control over all your data. If you think about it, if you're using AI, if you're doing what we just talked about with Steve Rag retrieval, augmented generation, you want to make sure that you're not feeding AI proprietary secret information. Stuff you don't want to incorporate into the models. But to do that, you need to be able to see and control your data. That's what BigID does. Intuit named it the number one platform for data classification and that's in accuracy, speed and scalability. Who has, who has the most dark data, do you think in the world? Big Ide equipped the U.S. army?
- [120:59]
Steve Gibson
Yes.
- [120:59]
Leo Laporte
250 years of dark data to illuminate the dark data, to accelerate this ongoing process of cloud migration, to minimize redundancy, to automate data retention. All of these are high priorities. And what a great quote Big ID guy from US Army Training and Doctrine Commander. This is the quote. The first wow moment with BigID came with being able to have that single interface that inventories a variety of data holdings, including structured and unstructured Data across emails, zip files, SharePoint databases and more. To see that mass and to be able to correlate across all of them. Completely novel. They go on to say. I've never seen a capability that brings us together like Big ID does. That's the US Army Training and Doctrine Command. But that's not all. Cnbc recognized Big ID as one of the top 25 startups for the enterprise. They were named to the Inc 5000 and the Deloitte 500 not once, but for four years in a row. The publisher of Cyber Defense magazine says BigID embodies three major features we judges look for to become winners. Understanding tomorrow's threats today, providing a cost effective solution and innovating in unexpected ways that can help mitigate cyber risk and get one step ahead of the next breach. Start protecting your sensitive data wherever your data lives. @bigid.com SecurityNow Get a free demo to see how BigID can help your organization reduce data risk and accelerate the safe adoption of generative AI. Again, that's bigid.com securitynow oh, when you get there, there's a free white paper that provides valuable insights for a new framework. It's AI Trism T R I S M Trust, Risk and Security Management. To help you harness the full potential of AI responsibly. You'll find that and everything else@bigid.com security now big id.com security now big id. We thank him so much. Two thumbs up for big id. We thank them so much for their support of security. Now I can never get to do it when I want to, but it always does it when I don't want it to. All right, let's talk about foreground radiation. You're the. You're the guy, at least as far as I know, coined Internet background radiation.
- [123:21]
Steve Gibson
That's my term. Yep. Okay, so as I mentioned at the top of the show, today's podcast title, Internet Foreground Radiation, is a play on the term Internet background radiation, which I coined 26 years ago back in 1999. Develop while developing GRC's Shields up facility, which, by the way, Paul Thurrott was the first person to discover and and write about.
- [123:49]
Leo Laporte
Really? Oh, that's awesome. That was small world, isn't it?
- [123:53]
Steve Gibson
And that came because I was observing all the random packet crap and noise that would occasionally flow into any Internet IP address. Now, Wikipedia reminds us that, quote, cosmic background radiation is an electromagnetic radiation that fills all space. The origin of this radiation depends on the region of the spectrum that's observed. One component is the cosmic microwave background. This component is redshifted photons that have freely streamed from an epoch when the universe became transparent for the first time to radiation. Its discovery and detailed observations of its properties are considered one of the major confirmations of the Big Bang. Now, fortunately, unlike the cosmic background radiation, which will presumably never die, the original designers of the Internet had the foresight to place a time to live counter into every single packet that moves across the Internet. And the very first thing that every Internet router does when it receives an incoming packet is to decrement that packet's remaining time to live. If the packet's time to live was one and is decremented to zero, that signals that the packet has been alive long enough and that if it was ever going to reach its destination, it should have by now. And that for the sake of the greater good of the Internet, it must now be put to rest. Sorry, packet. When this occurs, well behaved Internet routers will see where that packet came from from its source IP address and will send back an ICMP time exceeded message to inform its sender that the packet it sent to whatever destination IP never, for whatever reason, reached its destination. My point here is that unlike true cosmic background radiation, Internet packets are strictly not allowed to wander around the Internet forever aimlessly. And what this in turn means Is that all Internet background radiation has a deliberate source somewhere, and that at any time a packet is received, someone somewhere deliberately formed it and dropped it onto the Internet. Now, that said that someone somewhere could be some cranky old and forgotten NT server in a locked and forgotten closet that became infected with Code Red or Nimda worms back in 2001. Those were the good old days, where Code Red, for example, was a flash worm that successfully infected more than 350,000 Microsoft IIS Web servers within a few hours of its launch onto the Internet. So if any skeptics might be wondering whether things have actually gotten better through the intervening years, the answer is certainly yes. We do seem to be well past the point of flash worms taking down the Internet.
- [127:34]
Leo Laporte
Thank God.
- [127:35]
Steve Gibson
Yeah.
- [127:35]
Leo Laporte
Geez, I forgot all about that.
- [127:38]
Steve Gibson
Yeah, but the presence. Still the presence of any monoculture should always make a prudent person nervous, since mistakes can always happen. My point is that even today, even though Internet packets will never persist on the Internet, true Internet background radiation being emitted from dusty servers in lonely locked closets may still exist. So the reason I named today's podcast Internet Foreground Radiation is that there's something else going on that an Internet security firm has been observing. The distinction I wanted to make is that whereas Internet background radiation, much like the cosmic background radiation, lacks deliberate intention, there is now separate Internet foreground radiation, behind which a great deal of deliberate intention lies. So who's generating that radiation and why? Last week, the firm Human Security posted the results of their long running research under the heading Opportunity makes the thief How Web scanner bots target new websites for cyber attacks. And I have in the show notes a link to their their full research paper. Since what they found is not something that I think has ever been known before or appreciated before, I thought it would be worth sharing and taking a closer look at. They introduced the subject by writing, when a new website goes live, it's not people who visit first, it's bots. Automated tools probe new domains within minutes, long before any customer or legitimate user arrives. These bots vary widely in intent. Some are benign search engine crawlers indexing your pages, or commercial security scanners checking for vulnerability with permission. But many are malicious. Among the most pernicious are web scanner bots, which quickly examine websites for weaknesses and exploit them immediately, turning reconnaissance and attack into a single automated sequence carried out at scale. Human Security's Satori Threat Intelligence team monitors bot activity across our customer network and in dedicated research environments. One such environment is a honeypot, a web server we intentionally set up to attract only bot traffic. By observing the requests hitting this fresh, otherwise unpublicized website, we're able to gain insight into the types of bots that that target a website from its inception onwards. One early finding in this experiment was that web scanners consistently dominate early traffic to new sites and continued to probe the sites day after day, long after other bot types began to appear. This persistence underscores why scanner activity is a security concern for the full lifespan of any web property. This blog post examines the threat of these web scanner bots and shares our recent research findings on several active scanner campaigns, including the Mosai A botnet, a Mirai variant called Jaws, and the Romanian Distillery scanner Web scanner bots are an escalating cyber threat These bots are often the very first visitors to any new website, probing for security weaknesses long before any human users arrive on a newly launched site. Observed by human security scanners made up an average of 70% of all bot traffic in the first days, meaning web scanners scanning the entire site and on some days 100% of detected bot visitors were from scanners. Bot driven scanning operations are growing more complex. The Romanian distillery operation is a prime example. Once focused solely on harvesting SMTP credentials, it now probes for PHP services, env files, and misconfigurations across a distributed 24 subnet. Its scan patterns follow doubling revisit intervals and reveal a coordinated infrastructure designed for scale. In some cases, such scanners don't stop at discovery. They attempt SQL injection or deploy malware immediately after identifying a weakness. Traditional defenses struggle to catch web scanners. Many of these scanner bots evade simple security measures. They may rotate through networks of infected devices using other botnets to distribute their scans, hide their true identity by omitting or faking their user agent strings, and rapidly change tactics to avoid signature based detection. Legacy security tools that rely on known malicious IP lists or obvious signatures often miss these these stealthy probes Web scanners, also know as Known as website vulnerability scanners are automated tools designed to identify security weaknesses in web applications, websites, and APIs. They systematically probe and inspect websites for misconfigurations, exposed files, default credentials, or known vulnerable software. If a new website is still being configured or or lapse proper protections, scanners will attempt to find and exploit any flaw they can before the site's owners have a chance to secure it. Okay, so the first and crucial takeaway would be to never assume that any security can be added after any portion of a new site goes live. Never assume that since it hasn't been advertised or announced in any way publicly that it might be at all safe to place anything online that hasn't already been fully hardened. Essentially, the entire Internet has become a loaded and cocked mousetrap, ready to shut, spring and capture at the slightest provocation. This is where my favorite of all tricks, IP based filtering, can come in handy. It is so simple and is so absolutely robust as a security solution. If you wish to create some some, you know, true external exposure, simply first block all all access, then selectively allow the IPs through that you know you can trust. But never open the floodgates until you are fully prepared to be deeply attacked because that will immediately happen, they wrote. Not all scanners are bad, though. There are good scanners run by security companies or researchers to help site owners by identifying vulnerabilities so they can be fixed before the bad scanners can get to them. But both good and bad scanners impose load on your site, and the bad ones, if not blocked, will certainly attempt to leverage any weaknesses they find. Scanners don't visit just once. They constantly and persistently re scan sites over time, since new vulnerabilities might appear with site updates or or as new exploits are discovered. Okay, so it's it's always fun to run across, as I said, something we've never touched on or talked about on this podcast. Given that this is our 1030th podcast, we've logged many thousands of hours discussing and covering pretty much anything and everything that's happened over the past 20 years. So it's not often that we encounter something we've never discussed before. But today is one such rare day because the ubiquitous shift to TLS website connections, which increasingly require the use of sni, which we were just talking about. Server name indication to be specified and provided by the connecting client in its first TLS handshake packet, means that knowing the IP address of a site or having a site's IP address simply by scanning them all is no longer sufficient to successfully establish a completed handshake to a site's sample servers. That's new. We've never mentioned this before. Think about that for a second. From the birth of the Internet, it has been possible to simply scan the Internet's 32 bit IPv4 space for web servers and to establish connections to them. But that all changed once the likes of Cloudflare and other CDNs came along as a result of IPv4 space depletion and the economic fact that IP sharing is inherently far less expensive, since it also allows for infrastructure sharing today. More than 90% 9,0% of today's websites are now sharing IP addresses, leaving fewer than 10% of all sites sitting on a single dedicated IP address. This means that more than 90% of the Internet's websites have migrated behind proxies that are only able to disambiguate website destinations by examining the incoming client's SNI extension field in the TLS handshake the client hello packet. This even applies to a modest facility like mine. GRC's SC shortcut server, our mail dev squirrel, GitLab servers and others all share the same ip, so it's not possible to reach any of them simply by their ip. Because we don't know where which server to send it to, it's necessary for anyone who wishes to connect to any server behind that IP to somehow also first know which domain name they expect to find at which IP address. So as I said, that's not an observation that's ever come from this podcast before. The bad news is I wish this presented a bigger problem for web scanners than it does. The guys at Human Security explain that scanner's response to this has been to solve it, they wrote to ensure that their scanners managed to get first in line for any new website. Threat actors take advantage of feeds and services that that announce new websites or domains coming online. For example, threat actors monitor newly registered domain NRD feeds which are lists of recently registered updated or dropped domains such as who is databases and domain drop lists. Such NRD feeds are repurposed from policy feeds intended to increase corporate security to threat intelligence and monitoring feeds against the websites themselves. Threat actors also monitor certificate transparency logs such as certstream which publicly log new TLS certificates. For scanners, a new domain registration or certificate issuance indicates a new website that could be scanned. Once the large scale SEO crawlers index the new website, scanners may also monitor the search engines new listings and the scale of scanners will increase even further. One thing that hadn't occurred to me until just now as I was as I was reading this and paying attention to it is that wild card certs are an interesting hack here. If a wild card cert is issued that just says for example star.grc.com that doesn't indicate what the sites host names are and there's no indication of that from a wild card certificate. So there's a little bit of obscurity there. I wouldn't rely on it, but still it's there. So for the purposes of these, of this research, these Guys are interested in identifying and where possible, disambiguating and classifying the range of bots that are probing their honey pots. We know this doesn't matter for the sake of security, since for security it's necessary to simply be equally secure for anyone who might come knocking. But what these guys found was intriguing and revealing. Under the heading of identifying web scanner bot traffic, they wrote, some scanners openly identify themselves in the user agent string. Which, which, okay, that's interesting. Which is the part of an HTTP request that might say, for example, Mozilla/5.0 parens compatible semicolon scanner XYZ forward/1.0 and then it goes on. So this is identifying itself as a scanner. And they, and they say security teams can easily filter or block those known scanners. But many malicious scanners naturally deliberately mask their identity for use misleading user agents. I'm sorry? Or use misleading user agents to obfuscate their true nature. In these cases, identifying them requires analyzing their behavior and deploying anti bot mechanisms to intercept their activity. You know, like maybe a ridiculous number of of page requests per second. You could say, wait a minute, this is not a person. On the other hand, you wouldn't want to block a search engine and this thing might be declaring itself to be Google, you know, a Google spider. So there you'd have to know if it corresponded if the source IP corresponded with with a legitimate known Google IP address. Anyway, they wrote. Some user agents we observed suggest the presence of outdated or anachronistic systems, including the BOS legacy Linux kernels and even Windows 3.1 Internet Explorer versions. Obviously no real users are surfing the web on Windows 3.1 today. So this was a dead giveaway of automated activity and not very smart activity. These impossibly old user agents likely came from a public user agent database that the attackers grabbed for obfuscation purposes. A fun and benign find that should never hit any of your web servers if you have a decent bot mitigation solution deployed. And Leo, you put that on the screen a second ago and they show some of these ridiculous user agent strings. I particularly like the Mozilla/1.1 compatible MSIE 5.01 Palm OS 3.0, I remember that. Eudora Web 2.1, yes, Palm OS 3.0 now my refrigerator could use that, but nothing else. And then Eudora Web 2.1, wow. Anyway, so I would be inclined to agree with their assumption about the likely source of those bogus bot user agent strings. You know, where else are you going to get them? From some old historical list somewhere.
- [145:35]
Leo Laporte
Yeah.
- [145:36]
Steve Gibson
Under the heading of reconnaissance and probing the target, they explain what these scanners tend to do once they locate a new, new candidate target. They write. Before scanners are even deployed, operators conduct manual reconnaissance to identify likely entry points, directories, configuration files, endpoints and services that may exist at newly launched sites. They then craft scanners. So they're talking about the operators who design what the behavior of the bots will be. So they design this behavior, then they turn the bots loose. So they said. They then craft scanners with predefined paths and exploitation logic tuned to probe and attack if those elements are present and identified. Once launched against a site, the scanner rapidly tests for these known targets. It attempts to enumerate directories, pages, API endpoints and exposed resources, executing preset payloads or exploits where applicable. One of the most common methods to launch scanners is using Durbust, a dictionary based attack against web servers that automates the process of discovering hidden files and directories on a website. This tool scans through predefined lists of potential directory and file names, you know, slash admin,/config, php,/upup, zip, etc. In hopes of getting lucky in finding unprotected sensitive files or admin interfaces. Now here again, having been a website admin myself for the past 25 years, it can sometimes be tempting to imagine that it might be possible to to just briefly do something that's not entirely secure under the assumption that, you know, just for a few minutes, nobody will notice. All I can say is that on today's Internet, doing anything like that is risky at best. I've always had better things to do than wonder and worry about what percentage of GRC's inbound connection traffic has malicious intent. But for example, I have seen ample evidence of tools like that Durbust they mention in the logs that I sometimes briefly enable when I'm trying to track down some specific behavior. The only way to be safe is to assume that everything is malicious and be prepared for that. GRC's servers do not log website activity specifically because the signal to noise ratio is so low that there's virtually no signal among all of the noise. That's the reality of today's web. For sites that have been around for the last 25 years, it really has become a nasty jungle out there. It's sad it's happened, but it has, they wrote using the scanner traffic. From our research, we mapped the most targeted path types targeted by scanners. This mapping shows that scanners have particular favorites when it comes to these initial probes, the two most targeted types of files by far were environment configuration, ENV files and repositories for code secrets. In fact, about one third of all scanning attempts in our study were after dot ENV files and another one third were looking for git repository data such as git folders or or leftover export files. They wrote this as no surprise environment. ENV files often contain API keys, database passwords and other secrets that would be a jackpot for an attacker. And git related files might expose source code or credentials that enable a deeper compromise. The potential exploitation from each of these path types is listed in the table below and the most targeted paths are shown in the chart. And I've got a big bar, a big pie chart here. It is rather astonishing mostly to see how again, non uniform this stuff is. So I mean, here's a hint. If you wanted to immediately increase the security of your website and you don't use.env files or, or git secret files, simply set up a trap so that any query to those file extensions on your site blacklists that source IP for some length of time there. I mean again, no legitimate user who is clicking on a URL to access a page on your site for a site that doesn't use those file types is going to query that. So you're better off without them going any further. So astonishingly, fully 33.6% of web server file type requests which they observed were for env files. 33.6%. Wow. And equally the. The equally the. The effectively equal 33.5% were for git secrets.
- [151:49]
Leo Laporte
So these are clearly malicious spiders. Yes.
- [151:52]
Steve Gibson
No, there's no other reason, no other reason for anything to probe that, you know, period. So there's 2/3 of the probes right off the bat you're able to identify as malicious intent. Next up at 23.4% were common PHP files. So collectively just those three account for a whopping 90.5% of all website probes. This leaves 4.3% for unprotected config files, 2.9% for YML files and 1.1% for Python mail sender files. They offered a table that explained why different file types were being searched for. As I mentioned, the ENV files typically store API secrets, tokens and other sensitive information that can be used by attackers to pivot and attack. The git secrets are used to gain access to victims repositories, leading to cross organization compromise. Of course, common php if you, if you left Your PHP config out that might allow them to do recon identify versions of PHP and other installed frameworks. Even WordPress popular PHP CMS files. You know, as we know, WordPress has a long history of vulnerabilities. Attackers try to find fresh versions that are still using default credentials or endpoints that provide additional fingerprinting such as, you know, plugin versions. So these can be further than scanned for vulnerabilities and exploited if they're found lacking the latest security patches. So you know a wealth of information just from, you know, scouring and looking for things. And we know, we know how many unintentionally exposed files exist on the Internet that make this sort of scanning worth doing. I mean that unfortunately there is a payoff. You just don't want it to pay off on your site. They wrap up the topic of reconnaissance and probing by adding beyond those. Scanners also commonly seek out various configuration and backup files. For example, yml or YAML configs, old back or zip backups of the site, or files like config PHP that might reveal database connection information. Oh, that's true. They probe for known software specific files. For instance, requesting a URL ending in wp config php could indicate the site uses WordPress and reveals its config if it's not secured. Or hitting server status on a web server could reveal internal information if that page is not locked down. Scanners will even check for well known vulnerable services. One example is scanning for Outlook Web access and Exchange server paths on sites. Since unpatched exchange servers are high value targets, that could lead to a broader organizational breach. Essentially, during the probing phase, scanner bots test the site against a predefined list of files, directories and endpoints that should never be exposed. Every directory, listing, config file or version disclosure it files finds constitutes loot that can be used in the next phase of the attack. This process is highly automated and aggressive. The scanner might attempt Hundreds of different URLs on your site in rapid succession. Far more exhaustive and faster than any human could manage. That behavior pattern is often a telltale sign that the traffic is a scanner bot. So when you stop to think about it, there's only one reason any of this exists. And any of this is worth the time and trouble on the part of the attackers. All of this technology we're using today contains a very long legacy of being insecure by default. That's what this is about, right? It's you. You have to take, you have to be proactive you have to take measures not to expose these things. I mean, it is really a sad state of affairs that, that we have developed a world in a world which is insecure by default. You know, although this characteristic is beginning to disappear, historically it has been entirely possible, and was even once acceptable, to choose not to use any password at all when setting up a new operating system or a device. Unix and Linux once allowed the root user's password to be null. You know, today we all recognize this as beyond bad, but we all probably also remember a time when perhaps we did that ourselves. In the future, the option to skip a password won't exist. No one will believe it was even ever possible. And they'll understand, and they'll understand that doing so in the future would be insane. So once upon a time, though, it was not so insane. But that, you know, that has been. That approach of having no or low security has been now entirely upended thanks to the Internet's steadily growing foreground radiation.
- [158:00]
Leo Laporte
I remember a time when no one locked their doors and children would play out in the street with absolutely no fear at all.
- [158:09]
Steve Gibson
Times change. Steve used to be a friendly neighborhood.
- [158:12]
Leo Laporte
Used to be a nice place back here, no? Yeah. Gotta have a password for your root user. Gotta. It just seems sensible. Also, you got to listen to this show every Tuesday. My God, you miss an episode, you miss a mountain of information that is, I'm sure, useful to you in your work and then at home and keeping things secure. This is the show. We do this every Tuesday right after a Mac break weekly. So that's about 1:30 Pacific, 4:30 Eastern, 20:30 UTC. You can watch us during the show recording if you want to get the freshest version. Fresh usually means there's some, you know, unbaked parts, but most of the time it's pretty good. If you are watching live, you can chat with us. So that's the advantage. Club members get behind the velvet rope. Access in our club, Twit Discord. Love to see you there. If you're not yet a club member, please join it. We'd love to have you ad free versions of all the shows and a lot of special programming just for the club, including, by the way, all those keynotes we did last week and the week before from Apple and Microsoft and Google and all that stuff. That's all club only. Now the live streams for everything we do not only are in Discord, but open to the public at YouTube.com, twitch, TikTokX.com, facebook, LinkedIn and Kik pick One of those you can watch live. Chat with us live after the fact. Of course you can download a copy. Now. Steve has some unique versions of the show. In fact, every version Steve has is unique, different. There's a 16 kilobit audio version for the bandwidth impaired. It's a little scratchy, but it is small. Has that virtue. He has a normal 64 kilobit audio version. We don't make those anymore. So that's the place to get that. He also has those great transcripts that Elaine Ferris does. Takes a couple of days to get those out. So come back maybe in Friday or Saturday and it should be there. What else? He's got the Show Notes there and if you want to get those ahead of time, you can subscribe to the Show Notes newsletter. In fact, the best thing to do if you want to correspond with Steve in any way is to go to GRC.comemail and sign up to get whitelisted. Basically he'll vet your address to make sure that it's okay. You're not a spammer. You can send him emails. Great way to submit pictures of the week or comments, that kind of thing. He's also great forums there, which may be even a better place to do the comments. Anyway, when you're going there grc.comemail you'll see two checkboxes unchecked by default. One for the weekly show notes and one for a much less common email. When Steve has something to announce like the forthcoming version of his DNS Benchmark Pro. And there's lots of other great stuff that's free forever, like his famous shields up where this whole background radiation thing started. He's got all sorts of information about vitamin D and just a variety of stuff. Grc.com now our unique versions are a 128 kilobit audio version. Don't know why, but that's what we do. I'm told it has something to do with the way Apple re encodes this stuff that if you don't have a higher bitrate, Apple munches it up anyway. That's what you can get in audio. We also have a video version if you want to see Steve's mustache at work. It's basically got a life of its own. That's all at Twit TV S and I'm teasing. That's only in my imagination. Twitter TV SN There's a YouTube channel dedicated to securing now that I recommend if you want to share clips. I know often when you're listening you go oh my boss has got to hear this or my co worker, my friend, my, my. My spouse, whatever. Go to the website GRC.com SN there's a link there to the dedicated YouTube channel with all the videos. Makes it very easy to clip it. Best thing to do, if you ask me, is subscribe. Because it's a podcast. I know it's old fashioned, but we still make these as RSS feeds so you can subscribe and you'll get a notification the minute new one comes out. You can even set your podcatcher to automatically download it so it's there ready and waiting for you to watch or listen whenever you're in the mood. If you do that though, many of these apps have directories and have a review capability. Leave us a good review, would you? Because it really helps build the audience. When shows get long in the tooth like this one, we don't get much on the charts because there's not a whole bunch of new subscribers at any given time. It's just a steady hum. So the reviews are really what makes the difference. Leave us 5 stars if you would. We'd appreciate that. If you're not a member of the Club Twit TV Club Twit. 10 bucks a month and you get all those great benefits. I think that does it for me. Steve, we'll be back here next Tuesday for 10:31.
- [162:59]
Steve Gibson
Yes, we will see you then, my friend. Oh boy. Bye.
- [163:04]
Leo Laporte
Nice.
- [163:07]
Steve Gibson
Yes.
- [163:08]
Leo Laporte
Noise, noise, noise.
- [163:10]
Steve Gibson
So I heard you say before that you become a fan of GL1 GLP1 Agonist.
- [163:20]
Leo Laporte
I asked my doctor for Tirzepatide, which is the dual GLP1 and GIP agonist, and he said, I can give it to you. It's more expensive. I have to. We have to jump through some hoops, send you an endocrinologist. But I've been on Ozempic for three weeks. I love it. My. My A1C. Well, I don't know my A1C yet, but my blood sugar is down. It was, it was averaging 154 when I started. It's now down 125 average.
- [163:45]
Steve Gibson
Well, and you said you're really seeing a change in appetite, like.
- [163:49]
Leo Laporte
Yeah, I'm not interested in. I don't have those. And by the way, I don't want to do an ad for this. I'm not, I'm not recommending this for anybody. I know.
- [163:57]
Steve Gibson
I wanted to wait till we were off the podcast.
- [164:01]
Leo Laporte
We're not on the podcast. We're still streaming. So if you're, if you're hearing this. Yeah. I'm not hiding it because I think it's really interesting. No, for me. No side effects. A lot of my friends have a lot of nausea and stuff, but I haven't. And I'm on the lowest dose, which means it's amazing that it's even working at all. I mean, the doctor said don't expect much in the first month. It's working. It's amazing. Lost five pounds already. I mean, I just.
- [164:26]
Steve Gibson
And you said you went from your typical four slices of pizza to.
- [164:30]
Leo Laporte
Yes. So if there's a pizza sitting on the counter, it's really hard for me to have one. I didn't even finish a piece. Yeah, it was fine. I was happy. It probably takes a lot of the edge off, you know, like, oh, this tastes so good.
- [164:46]
Steve Gibson
That's all right, actually, I. I'm sure it does.
- [164:50]
Leo Laporte
Yeah.
- [164:50]
Steve Gibson
I'm, you know.
- [164:51]
Leo Laporte
Yeah.
- [164:51]
Steve Gibson
But. But if. So if you're a foodie, then, you know, you have to give that up a little bit. But for longevity, yeah, it's worth it.
- [164:58]
Leo Laporte
I was. I scared myself. My blood sugar was just getting too high. So. Yeah, it's been. This has been great. What? It really just. I mean, you feel full most of the time. You always have a full feeling because you're stuck.
- [165:09]
Steve Gibson
You're not thinking about food.
- [165:11]
Leo Laporte
That's the main thing. I don't have these, like, oh, God, I can't wait to eat something. I fast until one o' clock every. I don't eat. I eat it last meals at like 6 or 7, and then I don't eat again until after, you know, about one o' clock.
- [165:25]
Steve Gibson
Good.
- [165:25]
Leo Laporte
That's fine.
- [165:26]
Steve Gibson
Yeah.
- [165:26]
Leo Laporte
Yep. Yep. So I only have two meals a day. I don't eat all those snacks. I would eat in the evening. It's nice. Big difference. I'm nice. I feel good, too. I feel much healthier. Yeah. Yay. Thank you. Thank you.
- [165:39]
Steve Gibson
Okay, buddy.
- [165:39]
Leo Laporte
Yeah. Have a good one. Mr. Gibson.
- [165:42]
Steve Gibson
See you next week.
- [165:43]
Leo Laporte
My love to Lori. We'll see you next week.
- [165:45]
Steve Gibson
Will do. Bye. Oh.
- [165:55]
Leo Laporte
I don't want to be an ad for that drug. I don't. But it, it, it's. But I. I have to say, it's kind of amazing.
- [166:03]
Steve Gibson
You need to learn the disclosure spiel at the end of it.
- [166:05]
Leo Laporte
Like, you may cause sausage fingers and weird hallucinations. You may not be able to poop for a week, but you'll lose weight.
- [166:15]
Steve Gibson
Side effects include instant death.
- [166:16]
Leo Laporte
Instant death. I have. I haven't had any side effects, which is great because will Will Harris said he would get terribly nauseous. I know a number of people just say I get so sick every time I have my dose. But it's worth it is what they all say.
- [166:30]
Steve Gibson
Well, all drugs are like that, right? It's very specific to the person.
- [166:33]
Leo Laporte
I, you know, I never have a reaction to vaccines, to medicines of any kind. I'm. I'm pretty insensitive, I guess would be the word. Oh, and I do my tai chi like crazy. I love my tai chi. I am now up to. So there's 108 poses in the yang that we do, the Yang style that we do. I'm now up to 38. I could do about a third of the total. But I have to say I love tai chi. Sometime I'll do you a little tai chi demo. It's so much fun. And I do it as slow as I can. So I had class yesterday and I, I love it. Lisa and I are both doing it. It's really good. We have a nice sensei. He is a. He is a black belt and Kenpo, he's like a super black belt. He's like a. He's very high level Kenpo master. But he all. He knows every many other disciplines, but studied Tai chi for many decades. He's about my age since. Since his twenties, so forty or fifty years. But he has his own flavor. You know, I look at the videos on YouTube and stuff and I'm doing a little. It's a little different, but so. So I really love it. And I exercise every day. I usually row for half an hour every morning. And then I. Now I'm in the habit of taking a couple mile walk after dinner every night because that helps also with the blood sugar. So I'm getting good habits. Yeah, I feel. And I have been feeling much better. So thank you for asking. Except you didn't. But there you go. You're gonna hear it anyway.
- [168:22]
Steve Gibson
Security now. Hi, Zoe Saldana. Welcome to T Mobile. Here's your new iPhone 16 Pro on us. Thanks. And here's my old phone to trade in. You don't need to trade in. When you switch to T Mobile. We'll give you a new iPhone 16 Pro. Plus we'll help you pay off your old Phone up to 800 bucks and you still get to keep it. There's always a trade in. Not right now. @ TM. I feel like I have to give you something in return for karma. That's okay. I don't really have much in my purse. Oh, let's see. Hand Sanitizer it's lavender. I'm good. Seriously. Let me check this pocket. Oh, mints. Really, I'm fine. Oh, I have raisins. I'm a mom. Wait, wait one sec. I've got cupcakes in the car. It's our best iPhone offer ever. Switch to T Mobile, get a new.
- [169:09]
Leo Laporte
Iphone 16 Pro with Apple Intelligence on us. No trade in needed.
- [169:13]
Steve Gibson
We'll even even pay off your phone. Up to 800 bucks with 24 monthly bill credits. New line, $100 plus a month on.
- [169:19]
Leo Laporte
Experience beyond finance agreement 99999 and qualifying.
- [169:22]
Steve Gibson
Forwarded for well qualified, plus tax and $10 connection charge. Pay off via virtual prepaid card.
- [169:26]
Leo Laporte
Allow 15 days credits end and balance.
- [169:28]
Steve Gibson
Due if you pay off early or cancel ctmobile. Com.