← All TWiT.tv Shows (Audio)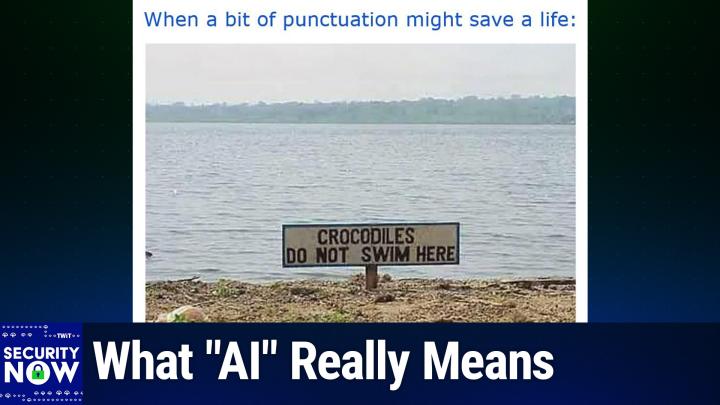
Loading summary
Transcript285 lines
- [00:00]
Leo Laporte
It's time for Security Now. Steve Gibson is here. We are going to talk about, as usual, some terrifying security issues on the Internet. Your state healthcare portal may be leaking information about you to data brokers and others. We'll talk about Facebook getting a passkey login. Apple adopting the new passkey portability, which is great. And then a deep dive into how Chinese government hackers got into our phone system. Turns out there's one American company that's at fault. Steve has the deets. Next on Security now.
- [00:38]
Steve Gibson
Podcasts you love.
- [00:40]
Leo Laporte
From people you trust. This is Twit. This is Security now with Steve Gibson. Episode 1031, recorded Tuesday, June 24, 2025. How Salt Typhoon gets in. It's time for Security Now. Oh, the show you wait for. All week long. Every Tuesday we get together with this guy right here, Mr. Steve Gibson, and we learn about all the nasty, horrible, terrible, no good, very bad things that are happening on the Internet. Hello, Steve.
- [01:16]
Steve Gibson
And ever so often, other stuff.
- [01:19]
Leo Laporte
Yeah, and all the other stuff too.
- [01:20]
Steve Gibson
That's great to be with you for episode 1031, for this last episode of. Wait, is this. No, the 31st. July.
- [01:30]
Leo Laporte
This is June 24th.
- [01:32]
Steve Gibson
Yeah.
- [01:33]
Leo Laporte
So the next one will be June 30th. No, it'll be July 1st.
- [01:37]
Steve Gibson
Right.
- [01:37]
Leo Laporte
Because 30 days, half September, April, June and November. All the rest have 31, except for February, which, which is all messy. I can never remember the rest of that rhyme.
- [01:46]
Steve Gibson
Well, you know, again, as somebody who codes things with D and times, you're dividing by 60, it's like, what's 60? Who came up with that? And 24.
- [01:57]
Leo Laporte
And the leap year every, every fourth year, except if a year ends in a 400, if it's divisible by 400, then it's not a leap year.
- [02:07]
Steve Gibson
So today we're going to talk about something that we've been skirting around. The Salt Typhoon was active for some time before and it was like, okay, another chines. Little did we know, but oh boy, these guys are in a class by themselves. Unfortunately. We were just last week talking about how they were found in digital realty, which was this major cloud provider, that sub, you know, that Amazon and Google and others buy their cloud resources from. And one other telecom I can't remember now because I've got. There's now 10 of them. Anyway, we're going to talk about how they get in because earlier this year, Cisco themselves, which is unfortunately the entry vector, their Talos group laid out the. The story. And as always, I try to do more than just recite news I try to create some context and see if there's like something that we can learn from this and I have a proposal as a consequence of this, in addition to all the other events and evidence that we see of what has to happen, what has to change and it's maybe not what people would expect. So we're going to talk about that. We're going to talk about another victim of them or two having been identified. Also the fact that state health care portals are tracking and leaking, probably to no one's surprise, but it's sad. Apple adopts Fido's passkeys and other credentials transport which is fabulous news for what's going on with pass keys. Facebook is adding passkeys. I heard you mention it was either on Sunday or just now Leo, that TikTok has been extended yet again.
- [04:25]
Leo Laporte
Yeah, another 90 days. I think you can count on that every three months.
- [04:29]
Steve Gibson
Yep. We have a Canadian telco that has acknowledged their infiltration by Salt Typhoon. This is the first known one in Canada.
- [04:39]
Leo Laporte
Interesting, huh?
- [04:40]
Steve Gibson
Microsoft has announced they're going to be removing unwanted and hopefully unneeded hardware drivers which we, we touched on before when they, when they were first talking about it. Now they have actually they're, they're moving on it. The Austrian government has legislated court warranted message decryption which I think is almost funny because you know, you, you, you, you can ask. And in something of a surprise I want to cycle back once again to a topic we've touched on a number of times, which is artificial intelligence. Because I asked ChatGPT a question on Saturday. Its answer stunned me and I'm as a consequence of that and I guess just months now of living with this, I believe I have full clarity finally, at least for myself. I'll see if it, if it transmits to our audience on what this is, what AI is and from that I would be willing to place a bet on its limits because I think I get it finally why we're confused. Why, why we've been confused why my screen just went dark. I have a Typhoon, a short duration screen blanker that I forgot to disable before I started.
- [06:16]
Leo Laporte
That's your light. You can't do that. It's your key light.
- [06:18]
Steve Gibson
Yeah, it is. Anyway, so anyway, I have something that I think that I haven't said before that resolves this for me and so this may be the last time I talk about this for a while and then we're going to take a deep dive into Salt Typhoon's operation. How they got in sadly, why they're still getting in and what I think we have to do to change this finally, I think, good to know there's.
- [06:53]
Leo Laporte
Something we could do even.
- [06:55]
Steve Gibson
There is. And I also think some of this is, some of this is as a consequence of this incredible delay that we see throughout the whole system. You know, IPv6 was finalized in 1998 and it's, I don't, you know, I don't have it, need it. GRC doesn't have any IPv6 IPs. So one of the things that's happening is that nothing changes unless it has to.
- [07:26]
Leo Laporte
There's a lot of inertia.
- [07:28]
Steve Gibson
Yes. There's so much inertia.
- [07:30]
Leo Laporte
Yeah.
- [07:32]
Steve Gibson
And now with somebody like Cloudflare being able to host a huge percentage of the Internet behind a subset of IPs, thanks to SNI server name indication, suddenly the pressure is off. It's not like we're going to run out for a while. Remember, we had the, you know, the end of IPv4 Countdown and, you know, doomsday coming and the price of IPv4 addresses was shooting up. Well, not so much anymore.
- [08:03]
Leo Laporte
Well, by the way, speaking of Cloudflare, we're going to get their cto, John Graham, coming on intelligent machines at some point because, you know, he's created a site, you know, there's a, there's a huge demand for steel that was created before the nuclear age. Right. Because it's got no radioact, radioactivity and they use it in medical devices and things.
- [08:27]
Steve Gibson
Interesting.
- [08:28]
Leo Laporte
And the only source of it is things like ships that were sunk during World War I, and they could bring them up and then there's. You reuse that steel in very careful circumstances. So he has created a website of text information that was created before the age of AI. Isn't that brilliant?
- [08:47]
Steve Gibson
That is, that is really good.
- [08:49]
Leo Laporte
Yeah. So we're going to get them on to talk about that. But I, I will also ask him a lot about Cloudflare. They've done such an amazing job with what they've done and what they offer is such a public service for free. It's kind of amazing, you know, really, I like John a lot. He's a great guy.
- [09:07]
Steve Gibson
Well, I like him. And you know, I, I, I agree with you. We're often talking about them because they do such a great job.
- [09:17]
Leo Laporte
Ah, let's do a good job for our next sponsor and then we will get to the picture of the week. What do you say? How about that? Our show today, brought to you by one password another great group. Over half of IT pros get ready for this. Over half of IT pros say securing SaaS apps is their biggest challenge. If you think about it in the enterprise, SaaS Sprawl is a growing problem and shadow it, you know, it all started with byod and it's just getting worse and worse. It's not hard to see why. Well, 1Password has an answer. It's called Trelica. Trelica by 1Password can discover and secure access to all your apps whether they're managed or not. And that's what you need these days. Trelica by 1Password inventories and every app in use in your company, every one shadow it or not, then pre populated app profiles and they cover everything by the way, assess the SaaS risks, let you manage access, optimize, spend, enforce security best practices across every app, not just the approved ones, but every app your employees use. It lets you manage shadow it. It's also helpful for securely onboarding and offboarding employees and meeting your compliance goals too because everybody has to deal with that these days. Trelica by 1Password provides a complete solution for SaaS across governance. And it's just one of the ways that 1Password's extended access management helps teams strengthen compliance and security. 1Password's award winning password manager is trusted by millions of users at over 150,000 businesses from IBM to to Slack. And now they're securing more than just passwords with this 1Password Extended Access Management. 1Password is ISO 27001 certified. Of course with regular third party audits and the industry's largest bug bounty, 1Password exceeds the standard set by various authorities. They're a leader in security. You'll be glad to have them on your team. Take the first step to better security for your team by securing credentials and protecting every application, even on managed shadow it. Learn more and@1Password.com security now that's1Password.com security now all lowercase. We thank 1Password so much for supporting the very important work that Steve does here on Security Now. 1Password.com Security Now. All right, I am ready to scroll up as we say on the picture of the week. It's been hiding on my screen all this time.
- [12:00]
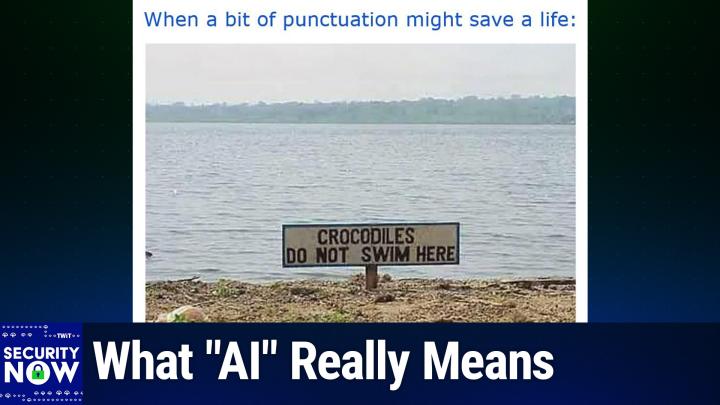
Steve Gibson
So I gave this picture the caption. When a bit of punctuation might save a life. When a bit of punctuation might save a life.
- [12:11]
Leo Laporte
All right, scrolling up here. Let me just see. It's a sign. A sign you should pay attention to.
- [12:22]
Steve Gibson
Sign has two lines. First line says crocodiles. Second line says draw. Do not swim here.
- [12:30]
Leo Laporte
So does it Henderson in our discord says, why don't we want crocodiles to swim there again?
- [12:35]
Steve Gibson
What? Yeah, well, because people should be allowed to swim there. So I think the sign is just, this might be in Florida. You never know. It might just be saying, just so. Just so you swimmers know, crocodiles don't don't swim here.
- [12:49]
Leo Laporte
No. So, no, that's not what it means for you, Steve.
- [12:53]
Steve Gibson
What?
- [12:54]
Leo Laporte
I think they're saying there are crocodiles here. Do not swim here. Or it could be a message to the crocodiles, I don't know.
- [13:02]
Steve Gibson
Oh, no.
- [13:04]
Leo Laporte
What would you put there?
- [13:06]
Steve Gibson
Should put a couple exclamation points or.
- [13:08]
Leo Laporte
Just an exclamation point. Crocodiles.
- [13:10]
Steve Gibson
Exactly. Yeah.
- [13:13]
Leo Laporte
Or maybe just say, don't stay out of the water. How about that one? Beware. That's hysterical. I love it.
- [13:21]
Steve Gibson
Yeah, I like that. Okay, so the Dark Reading outlet reports under their headline telecom giant via Stat is latest Salt Typhoon victim with a subheading. The communications company shared the discoveries of its investigation with government partners, but there's little information they can publicly disclose other than that there seems to be no impact on customers. It's like, okay, well, of course that's what. That's the story. That's the story they want to share. Okay.
- [13:56]
Leo Laporte
So yeah, unless you're the president, the national security chiefs, things like that.
- [14:01]
Steve Gibson
Well, yeah. And what does it mean? Like. Well, no one's password was exfiltrated. It's like, wait, you're a telecom provider. You're a via stat. Anyway, so Dark Reading said viastat is the latest telecom business to fall victim to tall to Salt Typhoon. Now, I should note probably more accurate to say the latest telecom business to acknowledge or to discover or to, you know, reveal whatever it's not. Well, anyway, we got a lot to talk about with Salt Typhoon today, but the article says the notorious cyber espionage threat group speaking Assault Typhoon, the breach of the satellite communications company was discovered earlier this year and has been identified as one of the threat group's targets during the 2024 presidential campaign. According to Bloomberg News, which first reported the breach, the California based company that is viastat operates a satellite fleet and various ground stations to support a global network providing high speed satellite broadband services and networking systems to both military and commercial consumers following a report of an unauthorized access through a compromised device. And again, we're going to know exactly what happened, which CVSS or well or CVE was involved. And, and we have the backstory which we're going to be getting to, as I said the company said, quote, upon completing a thorough investigation, no evidence was found to suggest any impact to customers. Due to the sensitive nature of information sharing with government partners, we're unable to provide further details Via Stat believes that the incident has been remediated and has not detected any recent activity related to this event. Again, hard to prove a negative, but okay. Salt Typhoon, they write, meanwhile, has targeted several telecom companies this year alone. In January, the group targeted Charter Communications, Consolidated Communications and Windstream. Then in February, Cisco confirmed that the group exploited a Cisco vulnerability so that it could infiltrate telecommunications providers, including T mobile, AT&T and Verizon last fall, maintaining access to the compromised environments for extended periods of time and if you can believe it, in one case, three years, they they were found to be in in networks. U.S. officials, they write, have previously raised suspicions of hackers targeting the companies to steal telephone audio intercepts and record call data. Enough attacks have occurred in the lengthy cyber espionage campaign that cisa, our cybersecurity and information security agency, was prompted to issue guidance to the telecom sector alongside the National Security Agency and FBI. In addition, the House Committee on Government Reform dedicated a hearing to Salt typhoon on April 2 to address what what actions the US could take in retaliation. Though Edward Amoroso, research professor at New York University, advised against hacking back in his testimony stating that the that the country should see these attacks as a wakeup call to shore up its defenses. And again, this all ties back to today's topic, which we'll be getting to. So we have Verizon, AT&T, T Mobile, Spectrum, Lumen, Consolidated Communications, Windstream, then as we talked about last week, Comcast and Digital Realty, and now via Stat, it's a mess. The best news about this is that we have seen over and over and over how reluctant companies are to address their own latent infrastructure security troubles. What's apparently necessary is for something as high profile as these multiple continuing Salt Typhoon attacks, or at least revelations which have successfully remained in the headlines for months and finally come to the attention of the US Congress. Maybe there's a chance that this will finally get companies to sit up, take notice and assign someone to the task of critically examining the security of their older equipment. We now know a great deal about how Salt Typhoon did what it did, and as I said, we're going to take a deep dive into the depths of that into the depths of that typhoon at the end of today's podcast. Before we leave the topic, I also want to share one what Bleeping Computer reported, since it adds some additional depth to this bleeping Computer. Of course we know them well, wrote satellite communications company ViaStat is the latest victim of China's Salt Typhoon cyber espionage group, which has previously attacked I'm sorry. Hacked into the networks of multiple other telecom providers in the US and worldwide. It's not just us here in the States, viastat provides satellite broadband services to governments worldwide and aviation, military, energy, maritime and enterprise customers. Last month, the telecom giant told shareholders that it had approximately 189,000 broadband subscribers in the U.S. the company discovered the Salt Typhoon breach earlier this year and has been working with federal authorities to investigate the attack. As Bloomberg first reported, ViaStat told Bleeping Computer via STAT and its independent third party cybersecurity partner investigated a report of unauthorized access through a compromised device. And again, we're going to know all about that upon completing a thorough investigation, they said no evidence was found to suggest any impact to customers. Via STAT engaged with government partners as part of its investigation due to the sensitive nature of information sharing. So this is a repeat from the previous article, they said. Bleeping Computer first contacted viastat. They wrote in February with questions regarding a potential breach, but received no reply at the time. Russian hackers also breached via Stats Kasat Consumer Oriented Satellite Broadband Service in February 3 years ago 2022 wiping satellite modems using Acid Rain data wiper malware roughly one hour before Russia invaded Ukraine. The 2022 cyber attack impacted tens of thousands of broadband customers in Ukraine and Europe, including modems controlling roughly 5,800 wind turbines in Germany. As the FBI and CISA confirmed in October, the Chinese Salt Typhoon state hackers had breached multiple telecom providers and they enumerate them again and other telecom companies in dozens of countries. While inside US Telecom networks, the attackers also accessed the US Law enforcement's wiretapping platform and gained access to the private communications of a limited number of US Government officials. That was again that Congress said what you know, now you're talking about us. Earlier this month, NSA and CIS officials also tagged Comcast and Digital Realty as potentially compromised in Salt Typhoon's telecom attacks. And now we know that has been confirmed. Salt Typhoon and in fact both companies have acknowledged that Salt Typhoon has been breaching government organizations and telecom companies since at least 2019 and kept actively targeting telecoms between December 2024 and January 2025. So the very end of last year and the very beginning of this year breaching more telecommunications providers worldwide via unpatched Cisco iOS XE network devices, which is where we're going to be spending a lot of time. The flaws that were once present in Cisco's it's, you know, iOS is a confusing name because of course we, we're talking about Apple stuff all the time. This, in this case it's Internet operating System and Cisco's iOS acronym predates Apple's, you know, iOS for iDevices. These XE network devices were leveraged to admit the attackers into these networks. But Cisco had found and patched those vulnerabilities long ago. As in years before, those flaws were used to gain illicit entry into these companies networks. So while Cisco was to blame for once having vulnerabilities, they fixed those flaws years before they were used which is a key factor in you know, the import of this story. I'm at a loss to know how we can ever get this behavior to change because it should have changed already. Right. I doubt we're ever going to be able to hold the purchaser and user of these products accountable. Companies purchase them. I mean like practically accountable. Sure we can say oh you're legally responsible but I mean in practice so that it's not a matter of ascribing responsibility and blame and victims licking their wounds but not having the intrusions in the first place.
- [24:39]
Leo Laporte
Well and also remember the Biden administration had an executive order which I'm sure no longer exists that companies would be liable for keeping their software and hardware reliable like the sellers as well there.
- [24:53]
Steve Gibson
Has been some rollback of, of those regulations because so, so what happens is companies purchased these devices, they didn't make them, they didn't create them. So they, you know, they see them as a drop in turnkey solution which they configure and install, wire up, plug in, power up and then forget. They just assume that they will continue working correctly until they unplug and retire the device. The problem is in a sprawling organization with thousands of routers and switches spread across this continent and others where every device is receiving periodic updates, you know, from its manufacturer, keeping practically from a practical standpoint, keeping everything updated with the risk as we know that is also there that an update might cause more trouble then the potential trouble which was unrealized. But this could be a problem. So you're being asked to update something that might break, something that's working because maybe something bad could happen if you don't. So asking the client owners of these devices to be completely responsible for them is unfortunately the best we've managed to come up with so far. And this, this salt typhoon mess clearly demonstrates that this is not Working. You know, we've talked about having devices phoning home for updates, but that's also risky since it opens the door for a failed update to break a perfectly working system, even when it might only be theoretically vulnerable. And it's interesting, we, I had an outage of my residential network about a week and a half ago, I guess, and I, and I was aware of it pretty quickly because things quickly stopped working and I thought, what the, what's going on? So I ran to the closet where that equipment is located and caught the tail end of the, of my ASUS router rebooting itself after it updated. So on one hand that was good and I gave it permission to do that and I said yes, you know, even, I mean, and I'm doing it more from a, because I'm a, you know, in the same way that Jerry Pornell used to try dumb things so that his users and listeners didn't have to. I don't need my ASUS router to reboot. It's behind a second PF sense router that is bulletproof. But I wanted to experience turning on automatic updates, which I've been preaching for routers. But here it did. It chose to update at, for some reason, not at 3am but in the early evening. And so it created a problem. It solved itself too. But still you can understand why in a, at a high end big iron telecom environment, they don't want no Cisco reaching in and updating their equipment.
- [28:20]
Leo Laporte
We got work to do here.
- [28:21]
Steve Gibson
Yeah, right.
- [28:22]
Leo Laporte
My, my Comcast business modem that we use for the shows kept dying and Russell, our MSP called them and they said, oh yeah, there's a problem with the firmware. We'll just, we're going to send you out, we're going to update the firmware and reboot it. And they did it and it fixed it. But, but you're right, I mean then that's a business device, so they didn't do it automatically. We had to call them and say there's a problem. And they said, yes, we know and we're going to fix it for you. So. Yeah, but you don't want to kind of, oh, you're down this week. Oh, right. Guess we won't have to sell widgets this week.
- [28:58]
Steve Gibson
So given, given everything we've just said, this leaves us with only one solution that I can think of, impractical though it may be. It's going to sound ludicrous, but really, I mean if you just, if you do the math, and that is for brand new Devices that are sold to never contain any exploitable vulnerabilities from the start, from day one, nor to have any introduced downstream through updates. Now, given the realities of after sales, I mean, I know how that sounds. Given the realities of after sales maintenance that we keep seeing in the real world, expecting reliable after sales patching of exploitable vulnerabilities, which is the way we're operating today, it's not reasonable. I mean, it is, it is not a reasonable thing to ask. And it doesn't happen. No. Mean even where organizations, it people kind of have this uncomfortable feeling that keeps them up at night that they really should be, you know, more on top of this, it doesn't happen. So it sort of. If that's the case, it leads to the inexorable conclusion that never deploying any insecure hardware is the only way that we're going to have security in the field. Now, of course, the world has become accustomed to the idea that it is not possible, just not possible to have flawless software. And that might be true in 2025, but it can also be a matter of degree. Recall that when we went through, remember back I was about 10 years ago, we went through a period where Cisco was apparently discovering, I'd have that in air quotes, unknown backdoor accounts that had been left in their own products. Yeah, that's not good. It's like, what?
- [31:12]
Leo Laporte
We could do better than that.
- [31:14]
Steve Gibson
It's like, you know, it should be ludicrous to imagine that any company such as Cisco would not be sufficiently aware of the contents of their own firmware to know that built in accounts might be present. How. How could they be discovering them in the field? Oh, whoa, what do you know? You know, bad guys are leveraging an account that we left in by mistake. What? You know, like you. Anyway, hopefully, as I said at the time, they actually did know that those accounts were present and, and that, you know, they were there due to a maintenance policy that had not aged well. Now, and we've often talked about policies that do not age well, inertia likely kept that policy in place until the malicious abuse of those hidden backdoor accounts indirectly exposed that policy and forced its reevaluation. Suddenly, Cisco was surprised. Oh, by the presence of those accounts. Right. But my point is things are better today, and I suspect that, that things will be even better in the future than they have been recently. You know, I think things are improving. I think we really need to keep in mind how slowly and reluctantly things change. You know, we're seeing the consequences today of decisions and policies that are a decade old with hardware and firmware. The, that was in place long before the need for much stricter and stronger security was widely appreciated. Vulnerable hardware that's not patched continues to present the significantly weaker security profile that was in use and acceptable at the time of that hardware's original design. It is still there in use and it's 10 years old. It would not be designed today the way it was designed then. But because of this refusal to update, refusal to patch, and in some cases, right, these old systems go end of life. They're still working, but. So you can't get a patch for them any longer. Their manufacturer has withdrawn support, yet the packets are still flowing.
- [34:00]
Leo Laporte
You said something though, that's pretty provocative. Is it possible to ship flawless software?
- [34:08]
Steve Gibson
We have to.
- [34:09]
Leo Laporte
How?
- [34:10]
Steve Gibson
Well, the shuttle computer famously had no bugs. It was expensive to create the software. Yeah, but it didn't have any bugs because it couldn't.
- [34:21]
Leo Laporte
It couldn't.
- [34:22]
Steve Gibson
I mean it literally could not have a bug.
- [34:24]
Leo Laporte
You can't send a repairman up or.
- [34:26]
Steve Gibson
We would have flown those guys into the sun by mistake.
- [34:29]
Leo Laporte
Right.
- [34:30]
Steve Gibson
So, so I, you know, and, and we know that like Microsoft, how many, how many tens of thousands of bugs did Windows have when it shipped? Remember? Famously. I mean, so they knew.
- [34:44]
Leo Laporte
Yeah. It was already.
- [34:45]
Steve Gibson
Yeah, they had a list.
- [34:47]
Leo Laporte
Right.
- [34:47]
Steve Gibson
And they said, well, these aren't that bad. And it only happens on Tuesday if some guy's standing on his right foot and clicks the, you know, a left handed mouse three times. I mean, okay, so we'll let that one go.
- [35:00]
Leo Laporte
Well, that's kind of the problem. I mean, Windows is a general purpose program, significantly, I think more difficult to, to make perfect than in say, a space shuttle.
- [35:11]
Steve Gibson
Well, or a router. A router.
- [35:13]
Leo Laporte
A router you could make perfect.
- [35:16]
Steve Gibson
We're coming back. I've got some very pointed to say to Cisco by the end of today's podcast because what, what was done, what was found should have never been possible. But yeah. We're going to talk about the unfortunate state of, of health care website portals after this break.
- [35:43]
Leo Laporte
Oh, that'll be fun. I can't wait for that. Oh, well, let's talk right now about Hawkshunt. All right. This is our sponsor for this segment on security. Now. I love this company. As a security leader, you get paid to protect your company against cyber attacks. Probably for a lot of you, that's why you listen to the show every week. It's not easy and it's getting harder. More cyber attacks than ever. And a lot of this, you know, comes through the over the transom with phishing emails and they're getting better because, well, the bad guys are using AI to generate them. You can't say, oh, the ungrammatical stuff, just throw it out. You need your employees to really be smart about this. But I think you probably already know those legacy one size fits all awareness programs, maybe you've been using them, they don't really stand a chance. They're out of date. They send at most 4 generic trainings a year. Most employees just ignore them. And then, you know, if somebody actually clicks, they're forced into embarrassing training programs and, and that feels like punishment. And that is not the way to get people to learn. This is why more and more organizations are trying HOX Hunt H o X Hawks Hunt. H u N T Hawks Hunt goes beyond security awareness and actually changes behavior. And it does it by gamifying rewards. Good clicks, it coaches away the bad. This is training employees. Like in fact, when I talked to the Hawks Hunt folks, they said people want more phishing emails. They say, give us more. We love this. This is like a game. It's fun, it makes it fun. Whenever an employee suspects that an email might be a scam, Hawkson will tell them instantly, giving them a nice dopamine. Rush says, this is scam. Hawkson says, good job. Gold star.
- [37:35]
Steve Gibson
Woo.
- [37:37]
Leo Laporte
You get that dopamine rush? I know it sounds silly, but it gets people to click, learn and protect your company. And people are not going to learn if they're not enjoying it. And for you, Hawkshunt is great. It makes it easy to automatically deliver phishing simulations in any way. They might come in across email slack teams. And of course, just like the bad guys, you get to use Hawkshunt's very good AI to mimic the latest real world attacks. So you can make these things very convincing even more. Simulations are personalized to each employee based on department location and more. So you know what, you're going to challenge your employees and they love it. Instant micro training solidify understanding. They're quick, they're fast and they drive lasting, safe behaviors. We know this from actual studies. You could trigger gamified security awareness training that awards employees with stars and badges and boosts completion rates, ensures compliance. There's a huge library to choose from, a customizable training packages. But that AI can also help you generate your own. You can purpose build something to meet your unique situation. I love this program. Hoxon has everything you need to run effective security training in one platform, meaning it's easy to measurably reduce your human cyber risk at scale. You need to do that, but you don't have to take my word for it. There are over 3,000 user reviews on G2, making Hox Hunt the top rated security training platform for the enterprise they want. Easiest to use best results also recognized as customers choice by Gartner. Thousands of companies use Hawkshunt, Qualcomm, AES, Nokia. They use it to train millions of employees all over the globe and they know it works. Visit Hawkshunt.com SecurityNow right now to learn why modern secure companies are making the switch to Hawkshunt. That's Hawkshunt.com security now. It's really nice to be able to recommend something that is so smart about getting the job done. Hawkshunt.com Security now states are not Good About Healthcare Privacy what's this?
- [39:51]
Steve Gibson
Oh boy. The publication the Markup has the tagline challenging technology to serve the public good, which is their mission. And I would agree with the need for more of this sort of tech savvy investigation and public airing of widespread misbehavior. Here's what they're reporting last Wednesday found there the headline of their most recent investigation was quote, we caught four more states and we'll be looking back retrospectively too of what they'd found previously sharing personal health data with big tech. And the subhead was Healthcare exchanges in Nevada, excuse me, in Nevada, Maine, Massachusetts and Rhode island shared user sensitive health data with companies like Google and LinkedIn. And of course you know, begs the question what four more on top of what. So here's what they reported. They said state run health care websites around the country meant to provide a simple way to shop for insurance, have been quietly sending visitors sensitive health information to Google and social media companies.
- [41:09]
Leo Laporte
Oh man.
- [41:11]
Steve Gibson
The data, including prescription drug names and dosages, was sent by web trackers on state exchanges set up under the Affordable Care act to help Americans purchase health coverage. The exchange websites ask users to answer a series of questions, including about their health histories, to help find them the most relevant information on plans. But in some cases, when visitors responded to sensitive questions, the invisible trackers sent that information to platforms like Google, LinkedIn and Snapchat. And they're reporting they have some, some screenshots of, of, of asking someone to select the to enter the drug name that they're interested in and then select the dosage. And in this case, when an individual indicated that they took Fluoxetine, commonly known as Prozac, on the Nevada Health Link site, that information was sent to LinkedIn. So they wrote the markup audited.
- [42:25]
Leo Laporte
Could add that to my resume, would you?
- [42:28]
Steve Gibson
Geez Louise, that's unbelievable. Leo. Just wait though. It's so bad. They wrote the markup audited the websites of all 19 states that independently operate their own online health exchanges. While most of the states contained advertising trackers of some kind, the markup found that four states exposed visitors sensitive health information. Nevada's exchange Nevada HealthLink asks visitors about what prescriptions they use, including the names and dosages of the drugs to help them find their best options for health insurance. When visitors started typing, it suggests specific medications, right to help them spell them correctly, including antidepressants, birth control and hormone therapies. As visitors answered the questions, their responses were sent to LinkedIn and Snapchat, according to tests conducted by the markup in April and May. On the other side of the country, Maine's exchange coverme.gov sent information on drug prescriptions and dosages to Google through an analytics tool. It also sent the names of doctors and hospitals that people had previously visited. Rhode Island's exchange Health Source RI sent prescription information dosages and doctors names to Google. Massachusetts Health Connector, another exchange, told LinkedIn whether visitors said they were pregnant, blind or disabled. After being contacted by the markup, Nevada's health exchange stopped sending visitors data to Snapchat and Massachusetts stopped sending data to LinkedIn. Additionally, the markup found that Nevada stopped sending data to LinkedIn in early May as they were testing the markup discovered the sharing after finding that California's exchange, known as Covered California, told LinkedIn when a visitor indicated they were blind, pregnant or a victim of domestic violence. Security and privacy experts said state health exchanges use advertising trackers is troubling, if not particularly surprising. Such tools can help organizations to reach visitors and tailor ads for them. And I'll just say, why do we need ads on state health care sites? Google Analytics, they wrote, allows website operators to better understand who's coming to their site and to optimize advertising campaigns. The LinkedIn and Snapchat trackers like a similar offering from Meta, help companies target their social media ads. Nevada uses the trackers to help target marketing at uninsured residents, according to Russell Cook, executive director of the state agency that operates Nevada's Exchange, Silver State Health Insurance Exchange. But health care services need to be especially careful with these tools, said John Haskell, a data privacy attorney who has previously worked as an investigator for the Department of Health and Human Services. Haskell said, quote, it doesn't surprise me that organizations that have these massive tech stacks that rely on third party resources, don't have an understanding, a full understanding of what the configuration is, what the data flows are and then once they go to somebody, what that data is being used for, it's something that needs to be addressed. In other words, as I think evidenced by the fact that the sites that were contacted by the markup said, whoops, sorry and like discontinued this. It wasn't deliberate, it was just naive. It was just dumping trackers on websites, not recognizing what the privacy consequences were for for sites that are transacting sensitive data, they said. After the markup reported uncovered California sharing of health data with LinkedIn, the exchange, meaning covered California, removed its trackers and said it would review its data practices. The news triggered a class action lawsuit and questions from federal lawmakers. The markup then examined websites operated by 18 states other than California, as well as Washington D.C. to see what information they shared as users navigated them. The sites were established under the Affordable Care act, which requires states to offer health insurance either through their own exchanges or one operated by the federal government. And of course we all remember back at the time the crazy scramble to get these websites online and that there were problems and delays and they were crashing and not working and you know, government needs computer to test them, they wrote. We first ran the sites through blacklight, a tool we developed. We the markup developed to reveal web trackers. We then reviewed network traffic on the sites to see what data the trackers received when when visitors filled out forms. The results showed that 18 used some sort of tracker. Some were filled with them. Nevada, for example. Leo, are you sitting down? Nevada, for example, used nearly 50, 50, 50 trackers.
- [48:28]
Leo Laporte
Hey, healthcare ain't free, buddy.
- [48:32]
Steve Gibson
Somebody's got to pay for it.
- [48:33]
Leo Laporte
Yeah.
- [48:34]
Steve Gibson
By Contrast, they said Blacklight found no tracker of any kind on Washington D.C. 's Exchange. Popular websites use on average seven trackers, according to Blacklight. Scans of the 100,000, most trafficked, not trafficked, not trackered websites on the web. Many of the sites use trackers in relatively innocuous ways, like counting page views. The four exchanges they said we found sharing sensitive health data sent varied responses to questions about the tracking. Cook said in a statement the trackers placed by his Nevada agency were, quote, inadvertently obtaining information regarding the name and dosage of. Whoa. Of prescription drugs.
- [49:29]
Leo Laporte
Whoops. It was an accident. It was an invert.
- [49:32]
Steve Gibson
We didn't mean it. And sending it to LinkedIn and Snapchat. Wow. And you know that these aggregators, they're just sucking anything. Oh, yeah. Get their hands on.
- [49:43]
Leo Laporte
Oh, they're thrilled. This is exactly the kind of information they love.
- [49:47]
Steve Gibson
Prozac. Yay. Okay. Cook acknowledged such data was, quote, wholly irrelevant to our marketing efforts, unquote. You think? And said it had disabled tracking software pending an audit. Jason Lefferts, a spokesman for Massachusetts Health Connector, said in a statement that, quote, personally identifiable information is not part of the tool structure. And no personally identifiable information, not even the IP address of the users of the tool, has ever been shared with any party in any way via this tool. But LinkedIn's tracker documentation makes clear that it correlates the information it receives with specific LinkedIn accounts so companies can use the data for features like retargeting website visitors. The company's documentation also states it later obscures this information and eventually deletes it.
- [50:48]
Leo Laporte
Oh, sure.
- [50:48]
Steve Gibson
Right.
- [50:49]
Leo Laporte
Yeah, yeah.
- [50:49]
Steve Gibson
So if this spokesperson in Massachusetts believes what he's saying about no IP addresses, he just may not understand how trackers operate. You know, I mean, it's.
- [51:03]
Leo Laporte
He doesn't understand how the Internet operates.
- [51:05]
Steve Gibson
Right, Exactly. The hosting website page provides some script or at least a URL to the tracker's home. When loaded, that causes the. You. When the script is loaded, that causes the user's browser to fetch something from the tracking site, and that immediately reveals their public IP address.
- [51:28]
Leo Laporte
Of necessity, yes.
- [51:31]
Steve Gibson
Anyone who imagines that a facility that was established for the sake of tracking will not be capturing and logging that IP has not been paying attention. The markups article continues. Spokespeople for the Rhode island and Maine health exchanges said that they pay a vendor consumer's checkbook.
- [51:54]
Leo Laporte
Oh, there you go.
- [51:57]
Steve Gibson
What could possibly go wrong to run a separate site that allows visitors to explore what plans are available to them through their state's exchanges? So they've subbed it out. It was from these sites they wrote that sensitive information was shared to Google consumers. Checkbooks sites are at a different web address than the exchange sites, but are prominently linked to on the exchange sites and display identical branding like the state health exchange's logo, making it unlikely that an average visitor would realize that they were no longer on the state run domain. Right. And saying that it's not our fault because our health management subcontractor is doing something wrong. You know, that doesn't do much to avoid those pesky class action lawsuits. Christina Speight O'Reilly, a spokesperson for Health Source RI Rhode island, said the company uses Google Analytics to study trends, but not to serve ads and quote, disable, disables Google signals data collection, ensuring that no data is shared with Google Ads for audience creation or ad personalization, and no session data is linked to Google's advertising cookies or identifiers, unquote. Health Source RI's terms of use mention the use of Google Analytics. She noted. A spokesperson for CoverMe.gov made similar points, saying that the agency does not collect or retain any data entered into the tool. Right. But again, the markup's independent testing found 10 ad trackers to which medication names and dosages, doctors and hospitals were being leaked. So this tells us that these spokespeople are, you know, in the best case. Well, I guess it's a mixed, mixed bag, clueless, but that either way, anything they claim should be treated as here's an acronym for you PRBs and independently verified by, you know, actual traffic analysis, which is exactly what these markup guys did. They wrote Consumers Checkbook. The subcontractor in two cases declined to comment beyond the exchanges comments. All of the exchanges said that individually identifiable health information, like names and addresses was not sent to third parties. But the point of the trackers is to enhance information. This is them enhance information sent about a user with data the platforms already have on that user. As we know, they're aggregators and every tracker they wrote found by the markup logged details about individual visitors such as their operating system, IP browser, device and times of visit. In response to requests for comment, the tech companies whose trackers we examined uniformly said they do not want organizations sending them potentially sensitive data and that doing so is against their terms of use. Oh, that's right, don't send it to us. But you know, if you do, while we gotta log it because it came in and we'll have to look at it later, we'll get around to that, right? Steve Gannam, director of product management for Google Analytics, said, quote, by default, any data sent to Google Analytics does not identify individuals and we have strict policies against collecting private health information or advertising based on sensitive information, unquote. A spokesperson for LinkedIn Breonna Ruff said that advertisers are not allowed to target ads based on sensitive data categories such as health issues. A spokesperson for Snapchat owner Snap said the same, noting that sending purchases of supplies like prescriptions or would run afoul of the company's rules about sensitive data. A Google Analytics information page specifically discusses how organizations that use the company's tools should comply with the Health Insurance Portability and Accountability act, of course, known as hipaa, which protects health data. The page notes that Google makes no representations that Google Analytics satisfies HIPAA requirements themselves.
- [56:41]
Leo Laporte
That's on you, buddy.
- [56:42]
Steve Gibson
That's right. It's important to ensure that your implementation of Google Analytics and the data collected about visitors to your properties satisfies all applicable legal requirements, says Google's page. So, okay, there are several trackers that we would hope would be more responsible. But the Markups report listed the number of ad trackers discovered on the state health care portals they examined in order of decreasing tracker count. California took dubious first place with 63 trackers. Oh.
- [57:33]
Leo Laporte
Whoa.
- [57:34]
Steve Gibson
You betcha. The Golden State. Where we're gonna, we're gonna, we're gonna.
- [57:38]
Leo Laporte
Well, I have family members on the California.
- [57:41]
Steve Gibson
This is on the covered California.
- [57:43]
Leo Laporte
Yeah.
- [57:44]
Steve Gibson
Yes. State sponsored Affordable Care act.
- [57:47]
Leo Laporte
Oh, boy.
- [57:47]
Steve Gibson
Portal 63 tracker.
- [57:50]
Leo Laporte
Yeah. Holy cow.
- [57:52]
Steve Gibson
That was followed By Nevada with 49, Maryland with 31, Massachusetts with 28, Georgia with 16, New Mexico, Colorado, New York and New Jersey each having 15, Pennsylvania with 14 trackers, Maine with 12, the state of Washington, Rhode island and Idaho each holding 10.
- [58:15]
Leo Laporte
Merely 10?
- [58:17]
Steve Gibson
Yeah. Connecticut and Virginia with nine each, Kentucky with four, Minnesota with two, and Vermont with just one. And as the article noted, Washington, DC's site somehow had not a single one.
- [58:31]
Leo Laporte
How do they do it without transport?
- [58:33]
Steve Gibson
That's a model to follow. Yes. Wow. The Markups investigated finishes by noting state exchanges aren't the only health sites that have sent medical information to social media companies. In 2022, the markup revealed that dozens of hospital websites shared information with Facebook's parent company Meta, through a tool called the Metal Pixel. The Meta Pixel. And of course, we were just talking about the infamous metapixel, since that's the thing that was connecting to a local device Meta app on the local host IP for the sole purpose of de anonymizing them to every instance of the metapixel appearing on the web, such as apparently any of dozens of hospital websites they might have the occasion to visit, or which was sending sensitive information to Facebook.
- [59:34]
Leo Laporte
Wow.
- [59:35]
Steve Gibson
The hospitals faced scrutiny from Congress and legal action, says the markup. Another Markup investigation found trackers logging information about online drugstore visitors purchasing HIV tests and Plan B. So what could possibly go wrong with that? They said. In 2023, a New York hospital agreed to pay a $300,000 fine for violations of the Health Insurance Portability Accountability act. Hipaa. In response to a series of incidents, the Department of Health and Human services said in 2023 that use of social media trackers to log health information could violate hipaa. Although recent court decisions have narrowed how the law can be applied against companies that use those trackers. Some plaintiffs have used state laws like those in California to argue that they should be compensated for having their health data sent to third parties without their consent. Others have argued that this kind of tracking runs afoul of wiretapping and even racketeering laws. So they end with a quote from John Haskell, that data privacy attorney who had previously worked as an investigator for the Department of Health and Human Services, who now advises clients to be very careful about the information they track on their sites. He said, quote, organizations are not investing enough time and resources into properly vetting everything they do. Organizations saying they did not understand the consequences of the tools they're using will not be seen as an effective defense. So what does this mean for consumers who need to use and trust the privacy of these sites? In practice, it means that the advertising, tracking and profiteering that has become the true underlying fabric of the web has shredded privacy and made a complete joke of any guarantees of a site's claim of HIPAA compliance. The only thing the covered California site is covered in is tracking technology. And notice that none of it, not a single bit of it, is about doing the job that the site is there to do for us. I'm as I said at the top, I am very glad the group such as the markup are there to keep bringing these egregious privacy failures to light. I'm glad they're asking states, you know, what is going on and that class actions are being brought against anyone who's making a mockery of hipaa. You know, again, this is all going to get better over time, but only if it is forced to do so. And unfortunately, you know, well, fortunately we have organizations like the the markup to do the forcing. Yeah, that's a good thing. While we're on the topic of pass keys, we're on the topic of pass keys.
- [62:50]
Leo Laporte
No, you mentioned them. You mentioned you said the word.
- [62:52]
Steve Gibson
I think I changed the order of this. We do have something about that. But I did want to mention an announcement during the recent Apple Worldwide Development Developer Conference regarding their support for pass keys was significant. For that, and for a bit of additional background, let's turn to Ars Technica's Dan Guden, who posted under the headline Coming to Apple OSS A Seamless, Secure way to Import and Export pass keys. The subhead he gave it was Apple OSS will soon transfer pass keys seamlessly and securely across platforms, Dan wrote. Apple this week provided a glimpse into a feature that solves one of the biggest drawbacks of passkeys, the industry passkeys, which and he's adding, is the industry wide standard for website and app authentication that is not susceptible to credential phishing and other attacks targeting passwords, he said. The import export feature, which Apple demonstrated at this week's Worldwide Developer Conference, will be available in the next major releases of iOS, iOS, iPadOS and Vision OS. It aims to solve one of the biggest shortcomings of passkeys as they've existed to date. Passkeys created on one operating system or credential manager are largely bound to those environments. A passkey created on a Mac, for instance, can sync easily with other Apple devices connected to the same iCloud account. Transferring them to a Windows device or even a dedicated credential manager installed on the same Apple device has been impossible. That limitation has led to criticisms that passkeys are a power play by large companies to lock users into specific product ecosystems. Users have also rightly worried that the lack of transferability increases the risk of getting locked out of important accounts if a device storing pass keys is lost, stolen or destroyed. The Fido alliance, the consortium of more than 100 platform providers, app makers and websites developing the authentication standard, has been keenly aware of the drawback and has been working on programming interfaces that will make the passkey syncing more flexible. A recent teardown of the Google Password Manager by Android Authority shows that developers at Google are actively implementing import export tools, although Google has yet to provide any timeline for their general availability and he has in parens. Earlier this year, the Google Password Manager added functionality to transfer passwords to iOS apps, but the process is clunky, he said. A recent update from Fido shows that a large roster of companies are participating in the development, including Dashlane, 1Password, Bitwarden, Devolutions, NordPass and Okta. The narrator of the Apple announcement video says, quote, people own their credentials and should have the flexibility to manage them where they choose. This gives people more control over their data and the choice of which credential manager they use. The transfer feature, writes Dan, which will also work with passwords and verification codes, provides an industry standard means for apps and OSes to more securely sync these credentials, as the video explains. He then he then quotes the video, saying, this new process is fundamentally different and more secure than traditional credential export methods, which often involve exporting an unencrypted CSV or JSON file, then manually importing it into another app. The transfer process is user initiated, occurs directly between participating credential manager apps and is secured by local authentication like Face id. This transfer uses a data schema that was built in collaboration with the members of the Fido Alliance. It standardizes the data format for passkeys, passwords, verification codes, and more data types, to which I say hallelujah. It finishes the the system provides a secure mechanism to move the data between apps. No insecure files are created on disk, eliminating the risk of credential leaks from exported files. It's a modern, secure way to move credentials. And needless to say, this podcast will have a full technical readout on this shortly.
- [68:20]
Leo Laporte
Yay.
- [68:22]
Steve Gibson
Dan finished saying. The push to pass keys is fueled by the tremendous costs associated with passwords. Creating and managing a sufficiently long, randomly generated password for each account is a burden on many users, a difficulty that often leads to weak choices and reused passwords. Leaked passwords have also been a chronic problem. Passkeys, in theory, provide a means of authentication that's immune to credential phishing, password leaks, blah blah blah. Anyway, we know all about passkeys. We've talked about them, you know, ad infinitum. And Dan gets the explanation exactly right, explaining that it's a switch to a public key crypto system. So I would anyway, I am super happy we knew that Fido was working on this. We knew, we knew that there was going to be a specification. We didn't know who was going to adopt it. Right. Because just saying that Fido has a means, you know, an official specified means for allowing passkey transport doesn't mean that everybody's going to adopt it. The fact that Apple has arguably one of the most closely held ecosystems is a really great sign. So that is just super news. That means that it will be possible to to finally, you know, we're not going to have dynamic pass key syncing like across the Apple boundary, but at least we'll be able to take all the pass keys we've created inside and outside of Apple and send them in both directions in order to, to, to. To create a, a, a single composite. So that's just, that's super welcome news. And Meta, by the way, also just announced that Facebook login is being enhanced with pass keys. And Leo, I heard you recently somewhere commenting that you were seeing you are really happy more and more seeing passwords. Yeah, pass keys being, you know, much more widely adopted across the industry.
- [70:36]
Leo Laporte
Yeah, Fast Mail now uses it, Google uses I use it for my Google accounts Meta. Yeah, it's good. I mean it's starting to get to the point where you can actually say oh good. I could just log in quickly.
- [70:46]
Steve Gibson
Yep.
- [70:47]
Leo Laporte
It's the only thing that really bugged me. I can't remember what it was. I had a, I think it was Amazon. I did pass keys and then it said, okay, but you still have to Give us the 6 digit 1 time password. It's like, dude, no you shouldn't. Right.
- [71:02]
Steve Gibson
What part of this do you not understand?
- [71:05]
Leo Laporte
There's no point in that.
- [71:07]
Steve Gibson
Right.
- [71:08]
Leo Laporte
Am I wrong?
- [71:08]
Steve Gibson
That is correct. Because you are. You're talking about secure biometrics that are being used to unlock the user's private key.
- [71:20]
Leo Laporte
It's so weird. Like in Amazon, you would think would understand this, but no, I guess. Okay, now what's the only problem would.
- [71:30]
Steve Gibson
Be as for example, password managers that don't enforce biometrics begin to do passkeys. Then if somebody else got a hold of that, then you might still want to send something to their phone or use an external authenticator in order to, to, you know, get further verification. So there's a little bit of belt and suspenders on it. But I agree, it's the only one that I do it really want is just seamless authentication.
- [72:01]
Leo Laporte
Yeah, it completely, I mean, then I might as well give you a password if that's what you're going to do.
- [72:05]
Steve Gibson
Right? Right.
- [72:06]
Leo Laporte
All right. We will continue in just a moment with security now. Can't wait to hear more. I know you can't either, but I got to tell you about our friends at Outsystems is our sponsor for this segment on security now this is so cool. This to me is exactly the promise of AI. Our friends at OutSystems are the leading AI powered application and agent development platform. Now these guys are not new to the game. For more than 20 years, the mission of Outsystems has been to give every company the power to innovate through software. And they've been doing it all along with low code, with DevSecOps automation. Now you put AI in the mix. Now you got something, you got something sweet. So this solves a problem that every IT team knows, every company knows we knew it. You typically have two choices when you need new software. Either by off the shelf SaaS products for speed of implementation, but you lose flexibility and you lose differentiation because everybody else in your sector is probably using the same product. So that's the buy side of the conundrum. Or maybe you think build, right, build custom software. But that's expensive. You lose time. AI has given us a third row between the build and the buy. It's forging another way for this solution. It's the fusion, as I mentioned, of AI low code and devsecops automation into a single development platform. Now this is the future, frankly, if you ask me, of software. Your teams are going to build custom applications, but they're going to do it with AI agents as easily as buying generic off the shelf sameware. And because you're using this grayed Outsystems platform, flexibility, security and scalability just come built right in. They're standard with AI powered low code teams can build custom future proof applications and at the speed of buying with fully automated architecture, security integrations, data flows, permissions, it's all built right in. See, Outsystems is the last platform you'll ever buy because you can use it now to build anything you need and to customize and extend your existing core systems. Build your future, build it without systems. This is so cool. Visit outsystems.com TWIT to learn more. That's outsystems.com Twitter we thank him so much for supporting Security now and the great Steve Gibson. All right, and back we go to Mr. Steve Gibson.
- [74:47]
Steve Gibson
Okay, so I mentioned the top of the show. I'll just say it again and I know that you were talking about this previously, Leo. TikTok has been, has had its end of life extended again another 90 days. Third time it gets another 90 days. And I guess as I understand it, they're trying to, you know, they're trying to finish negotiating, negotiating with China to, to allow some US consortium to purchase it and run it like Oracle or something. So.
- [75:20]
Leo Laporte
Yeah, but I don't think that's going to happen. They're trying to, I think what they're really trying to do is strong arm China with the tariffs, but China doesn't really kind of take to that too well. So. No, so far we'll see. But, but also the President really likes Tick Tock, so I don't think they're gonna ban it either.
- [75:38]
Steve Gibson
Yeah, yeah, well, and it's good for all the Tick Tockers who don't want to lose that platform. That is like.
- [75:45]
Leo Laporte
But you, you know, you heard on Sunday, Jason Calacanis said something that actually struck me. He said, do you think if we could figure out an app to make the Chinese citizens use that maybe we would be able to get information about half of them and reach them via, via content? Would we do it? Yeah. So that kind of, that catalyzed it for me that the real advantage to the Chinese Communist Party of owning Tick Tock because they do.
- [76:13]
Steve Gibson
They have a huge social media platform.
- [76:15]
Leo Laporte
In the U.S. in the U.S. huge influence operation.
- [76:20]
Steve Gibson
Okay, one more little piece of sort of prefacing SALT Typhoon information. Canada has become the first specifically known non US victim of SALT Typhoons Cisco based attacks. I should explain that the this following news was just declassified after I had chosen and completely written the coverage of today's main topic which Assault Typhoon. After I did that I went back looking for other stuff and it's like whoa now Canada. So the the details of the technology underlying these devastating and pervasive attacks are what we will get to so here's the news that just broke yesterday as I was wrapping up this week's show. Notes the Canadian center for Cybersecurity their so called Cyber center and the United States FBI are warning Canadians of the threat posed by People's Republic of China. You know, PRC State sponsored cyber threat actor being tracked as SALT Typhoon the Cyber center previously joined our partners oh, this is an actual announcement from the Canadian center for Cybersecurity. They're, they're the voice of this announcement. So they said the the Cyber center previously joined our partners in warning that PRC cyber actors have compromised networks of major global telecommunications providers to conduct broad and significant cyber espionage campaign. This Cyber Bulletin aims to raise awareness of the threat posed by PRC cyber threat activity, particularly to Canadian telecommunications organizations in light of new SALT Typhoon related compromises of entities in Canada. The Cyber center is aware of malicious cyber activities currently targeting Canadian telecommunications companies. The responsible actors are almost certainly PRC state sponsored actors, specifically SALT Typhoon. They said three network devices registered to a Canadian telecommunications company were compromised by likely SALT Typhoon actors in mid February of 2025. So three devices that they're aware of. The actors exploited CVE202320198 to retrieve the running configuration files from all three devices and modified at least one of the files to configure a GRE which is an encrypted form of tunnel enabling traffic collection from the network. And at the end of the show we're going to be looking at the actual Cisco commands that were used, which have been seen in use in separate investigations, they wrote. The Cyber center has found overlaps with malicious indicators associated with Salt Typhoon reported by our partners and through industry reporting, which suggests that this targeting is broader than just the telecommunications sector. Targeting of Canadian why wouldn't it be? Targeting of Canadian devices may allow the threat actors to collect information from the victim's internal networks or use the victim's device to enable the compromise of Further victims. In other words, you know, pivoting in some cases, we assess that the threat actors activities were very likely limited to network reconnaissance. While our understanding of this activity continues to evolve, we assess that PRC cyber actors will almost certainly continue to target Canadian organizations as part of this espionage campaign, including telecommunications service providers and their clients over the next year two years to monitor and mitigate this threat, we encourage Canadian organizations to consult the guidance linked below on hardening networks, security considerations for edge devices and additional cyber threat information pertaining to the prc. Telecommunications networks are almost certainly among the highest priority espionage targets for cyber sponsored cyber threat actors. State Sponsored Cyber Threat Actors Hostile state actors very likely rely on access to telecommunications service providers and telecommunications networks around the world as a key source of foreign intelligence collection. In other words, it's really bad that this is where the PRC is. You know, it's not inside some random enterprise somewhere that they're in the heart of telecommunications backbone for in this case Canada. They said TSPS Telecommunications Service Providers Terry Telecommunications traffic and collect and store large amounts of customer data that have intelligence value, including communication, location and device data. State sponsored cyber threat actors have persistently compromised TSPs globally, often as part of broad and long running intelligence programs to exfiltrate bulk customer data and collect information on high value targets of interest such as government officials. This includes geolocating and tracking individuals, monitoring phone calls and intercepting SMS messages. State actors have gained access to telecommunications networks and data by exploiting vulnerabilities in network devices such as routers, and by taking advantage of insecure design in the systems that route, bill and manage communications in 2024. So last year, partner investigations discovered that PRC state sponsored cyber threat actors had compromised the networks of major global tsps telecommunications service providers, including US wireless carriers, very likely as part of a targeted espionage operation. According to our partners, the actors were able to steal customer data call records from the compromised TSPs. The threat actors also collected the private communications of a limited number of individuals primarily involved in government or political activity. We are concerned with the potential impacts to the sensitive information of client organizations working directly with telecommunications providers. PRC cyber threat actors frequently attempt to compromise trusted service providers, including telecommunications managed service providers and cloud service providers to access client information or networks indirectly. PRC cyber threat actors exploit vulnerabilities in edge devices. They finished saying, as we noted in the national cyber threat assessment 2025, 26, cyber threat actors are exploiting vulnerabilities in security and networking devices. And let me just say these are not unknown vulnerabilities. That's what's so galling about this? These are long known vulnerabilities which we'll be talking about in detail shortly. They said that sit at the perimeter of networks, including routers, firewalls, and virtual private network solutions. By compromising these edge devices, a cyber threat actor can enter a network monitor, modify and exfiltrate network traffic. And we're going to look at the commands they used flowing through the device or possibly move deeper into the victim network. As part of this campaign, PRC cyber actors are targeting these network devices, exploiting existing vulnerabilities to gain and maintain access to DSPs. Despite public reporting outlining their activities, it is very likely that the actors continue to operate. In other words, as we've seen tangentially and parenthetically, the people in the know say, we don't think we got rid of them. You know, you'll, you'll see Verizon saying, oh, don't worry about it. We got, you know, we're all clear. We, we have expunged them from our network. They don't know that. So this alert managed to get a great deal of the facts correct, and it nicely serves to place these salt typhoon attacks into the foreground again, where I think it's clear they still belong. There's an understandably strong desire, especially on the part of the many identified victim companies, from a public relations standpoint, to loudly proclaim that the dastardly bad guys have been found and, and evicted with prejudice. But by the end of today's podcast, everyone here is going to appreciate why this is a claim that these companies would have a difficult time substantiating. They really don't have the ability to say that. Removal of unwanted drivers from Windows Update was the headline of last Thursday's announcement from Microsoft. We briefly touched on this before when it was something Microsoft was considering doing. And it's, it's good, but it's also dangerous because what's an unwanted or unneeded driver? You know, there's a lot of machines in the closet and people still using, you know, what was that bar scanning cat thing?
- [86:42]
Leo Laporte
Oh, the Q cat.
- [86:43]
Steve Gibson
Yeah, the cute cat.
- [86:45]
Leo Laporte
Who could forget the Q cat, right?
- [86:48]
Steve Gibson
No, I'm sure there's some out there still.
- [86:50]
Leo Laporte
Yeah.
- [86:52]
Steve Gibson
One of the pictures of the week shows, I think it's a bakery or a donut shop or something operating today. Contemporary picture with Commodore 64 cash registers.
- [87:06]
Leo Laporte
Oh, wow. Well, if it works, why replace it?
- [87:09]
Steve Gibson
Right? Okay, so.
- [87:12]
Leo Laporte
And you could play Star Raiders on it. So there's that.
- [87:15]
Steve Gibson
That's right. Oregon Trail Space Invaders.
- [87:19]
Leo Laporte
Yeah, right.
- [87:21]
Steve Gibson
Okay, so Microsoft wrote this blog post is intended to notify all Windows hardware program partners, that is the people who submit hardware drivers to Microsoft, that Microsoft has taken a strategic initiative to clean up legacy drivers published on Windows Update to reduce to reduce security and compatibility risks. Reduce the risks brought by security and compatibility problems. They said the rationale behind this initiative is to ensure that we have the optimal set of drivers on Windows Update that cater to a variety of hardware devices across the Windows ecosystem, while making sure that Microsoft Windows security posture is not compromised. This initiative involves periodic cleanup of drivers from Windows Update, meaning removal, thereby resulting in some drivers not being offered to any systems in the ecosystem. Further details of the effort are as follows. Then they switch into a Q and A format. So they ask themselves what category of drivers are targeted in the first cut of the cleanup, and they answer, the first phase targets legacy drivers that have newer replacements already on Windows Update. So why would you use an older obsoleted driver when there's a newer replacement? So that seems like a safe thing to do. And that's the approach Microsoft is taking is, you know, let's try not to break anything while we do this. Next question what does cleanup mean in this context? They say cleanup here refers to the process of expiring drivers so that they are no longer associated with an audience in Windows Update, resulting in them not being offered to any system. Technically, expiring a driver means removing all its audience assignments in Hardware Development center, which stops Windows Update from offering that driver to devices. Can partners republish a driver that was expired by Microsoft? Yes, partners will be able to republish the drivers that were expired. Microsoft may require business justification as to why there was a need for republishing. It's like hey qcat, I need my qcat. What happens to the cleaned up drivers after the expiry? Microsoft will publish a blog post mentioning the end of the first cut of driver expiry. After that, there will be a six month window for partners to get back with concerns, if any. If no action is taken, the drivers will be permanently removed from Windows Update. Will this be a one time exercise or will similar instances occur in the future? This is meant to be a regular exercise to optimize what Windows Update has to offer. We're beginning with the above mentioned category of drivers, but we'll expand to cover more categories of drivers that Microsoft deems fit to be expired for Windows Update. Each time such a cleanup occurs, Microsoft will communicate broadly so that partners know what to expect. Given the history of byovd. Remember, that's bring your own vulnerable driver being successfully used by bad guys, being proactive about removing an otherwise endlessly growing collection of old and aging drivers, you know, many of which are probably now just taking up space. To me, it makes a lot of sense. They concluded this by writing, in summary, Microsoft removing legacy drivers from Windows Update is a proactive measure to safeguard security and improve driver quality for Windows users. As a partner, you should review your drivers in the hardware program, be aware of what your current drivers in the ecosystem are, and make sure that any unwanted legacy driver is proactively expired from Windows Update. Moving forward, we expect this cleanup to be a routine practice and prepare for the introduction of new publishing guidelines that will help all Windows users keep their systems in a secure and reliable state. We appreciate your cooperation in this initiative as it helps ensure that Windows devices run on the most secure and compatible drivers available. And so, yay. I think this is, you know, this made sense when they talked about it. You know, everyone's worried about, like, their favorite driver disappearing and having, you know, like some random widget of hardware that needs something, that Microsoft doesn't realize what this looks like. The only way I can see this becoming a problem would be if hardware has been abandoned by its producer. And of course, that's not at all unusual. Then that producer of the hardware would no longer be enforcing the presence of that driver going forward. So Microsoft would say, we don't need this anymore, do we? You've got six months to tell us. Otherwise. No word would come in that that driver is still needed and so it would disappear from Windows Update. I don't know if Windows would pull it back out of use. That's an interesting question. Paul might know if, like, if a. If a driver removed from Windows Update could be, you know, retroactively pulled out of a working Windows system. I guess we're going to find out over time. So it would break something randomly, happens for six months. It would. It, Yeah. I mean, there is a danger of. Of breakage here, which is why they are deliberately trying to be careful.
- [93:38]
Leo Laporte
Yeah, I think they have to only take them out if they're not used. They're unused. Yeah.
- [93:43]
Steve Gibson
I love this bit of news. I just think. What are you guys thinking? That the Australian government, I love the headline. Agrees on a plan to allow monitoring of secure messaging. Oh, isn't that nice? They agreed. Last Wednesday, Reuters News carried an interesting bit of reporting from Vienna. On June 18, Reuters, Austria's coalition government has agreed on a plan to enable police to Monitor suspects secure messaging in order to thwart militant attacks, ending what a security officials have said in is a rare and dangerous blind spot for a European Union country because Austria lacks a legal framework for monitoring messaging services like WhatsApp, its main domestic intelligence service. And police rely on allies with far more sweeping powers like Britain and the US alerting them to chatter about planned attacks and spying. None of this makes any sense, but okay, that kind of tip off led to police unraveling what they say was a planned attack on a Taylor Swift concert in Vienna which prompted the cancellation of all three of her planned shows there in August of last year.
- [95:09]
Leo Laporte
Well, that's a relief.
- [95:11]
Steve Gibson
Yeah. Joerg Leichfried of the Social Democrats, the junior minister in charge of overseeing the directorate of for State Security and Intelligence, the DSN told a news conference, quote, the aim here is to make people planning terrorist attacks in Austria feel less secure. That's good. And increase everyone else's sense of security. Right. By knowing that you can be monitored. That is why this decision by the cabinet today is an important milestone in the fight against terrorism and spying. Okay. Against terrorism and spying by spying in Austria, he added. Under the new system, writes Reuters, monitoring of a person's messaging must be approved by a three judge panel and should only apply to a limited number of cases. Interior Minister Gerald Carner told the news conference it was only expected to be used for on 25 to 30 people a year. If it is more than 30, a report must be sent to a parliamentary committee, the government said. Addressing concerns about mass surveillance and the infringement of people's privacy. A government statement said the police must have a well founded suspicion of a possible terror attack to monitor a person's messaging under the new system. Once parliament passes the legislation, a tender process for monitoring technology would be launched and monitoring would begin in 2027, the government said. Okay, but wait. Once parliament passes the legislation, a tender process for monitoring technology would be launched and monitoring would begin in 2027. Well, you bet it's going to be tender. It's probably going to hurt a lot.
- [97:20]
Leo Laporte
I don't know how they propose to do this.
- [97:22]
Steve Gibson
Isn't this the wackiest thing? Yeah, so I guess they think they can. They're like turn on process. They mean a purchasing process. Right. They're going to put it out for bid. You know, we'd like to purchase this monitoring technology. Don't worry. We're only going to use it on 25 to 30 people per year. And if it's more than 30, if we want to Go over that limit. Then we're going to have to do some more hoop jumping. What.
- [97:52]
Leo Laporte
The reality is going to be interesting when they come up against it isn't that.
- [97:56]
Steve Gibson
Yes. Apparently these Austrian politicians believe that all they're lacking is a legal framework which they don't have.
- [98:05]
Leo Laporte
Yeah.
- [98:05]
Steve Gibson
And I wonder, have they not been paying attention? You know just ask the UK how it's going over there with their demand that Apple allow them access to anyone's data.
- [98:15]
Leo Laporte
Is it possible that we are the naive ones? That in fact all encrypted messaging has long ago been cracked by authorities in every country and that's what they're implying. Well the five we don't want to have to go to the five eyes to get that information. We should just be able to get it ourselves. Do the five eyes have it?
- [98:34]
Steve Gibson
We know. What we know is that for example in the case that we were talking about recently of Signal gate where a non approved signal client was being used, the signal correspondence was being sent to a third party email was being emailed to somebody that's secure. So. So we know that it the everything is available on a platform before it's encrypted and after it's decrypted.
- [99:05]
Leo Laporte
Right.
- [99:05]
Steve Gibson
Right. So but we also know Apple is never going to comply with some platform wide Austrian like we promise not to do it more than 30 on 30 few people. Yeah, 30 people a year please.
- [99:23]
Leo Laporte
Of course you have to break it for everybody in order to do it for a few people.
- [99:27]
Steve Gibson
Right. It has to be there and Apple is just not. I mean that is that. That they're not going to do that. I can't imagine. I mean we haven't yet seen. Because it hasn't actually happened where it comes down to a true standoff.
- [99:41]
Leo Laporte
Right.
- [99:42]
Steve Gibson
Of like you must give us access or you are. You're an outlaw company in our country. No one wants to see that.
- [99:54]
Leo Laporte
Forget Apple. Signal is not going to do it. I mean there will always be some strong encrypted end to end solution that terrorists can use.
- [100:04]
Steve Gibson
Well and that's just exactly it. I mean there will all. If. If it comes to if. If encryption is outlawed only the outlaws will be encrypting.
- [100:12]
Leo Laporte
Yeah, they'll write their own. These are well understood algorithms. They're not hard.
- [100:17]
Steve Gibson
Yeah, yeah. That horse has left the barn. Okay, I want to talk about AI and the revelation I had. We have two breaks. I want to do one now and then one before we start talking about salt typhoon.
- [100:28]
Leo Laporte
Awesome. Thank you Steve. Thank you. Dear listeners and viewers we're so glad you're here. You might be noticing if you are watching on video that there are occasional freezes in Steve's video. We are unsure why that's happening. We've tried to figure it out. We'll continue to try to figure it out. But just close your eyes when he's talking and it's amazing. He's perfect and I apologize. Sometimes these things happen. Our show today brought to you by Big id. Yeah, Big id, the next generation AI powered data security and compliance solution. Now let me tell you why you need BigID. It's the first and only leading data security and compliance solution that can uncover dark data. They do it through AI classification. They can identify and manage risk. They can remediate the way you want. They can map and monitor access controls. They can scale your data security strategy along with unmatched coverage for cloud and on prem data sources. BigID also seamlessly integrates with your existing Tech ST stack and allows you to coordinate security and remediation workflows. You can take action on data risks to protect against breaches. You can annotate, delete, quarantine and more based on the data, all while maintaining an audit trail. Partners include ServiceNow, Palo Alto Networks, Microsoft, Google, AWS and more. With BigID's advanced AI models, you can reduce risk and accelerate time to insight. You can gain visibility and control over all your data. Intuit named it the number one platform for data classification in accuracy, speed and scalability. Now let me tell you about one of their clients. They have many but I think this should impress Big ID equipped the US army. Okay, imagine who would have more sources of data stored in more arcane locations in globally than the U.S. army. BigID equipped the U.S. army to illuminate dark data which helped them accelerate cloud migration and minimize redundancy and automate data retention. They loved it so much. US army training and doctor in command gave us this quote, yes from the US Army. The first wow moment with BigID came with being able to have that single interface that inventories a variety of data holdings including structured and unstructured Data across emails, zip files, SharePoint databases and more. To see that mass and to be able to correlate across those is completely novel. I've never seen a capability that brings this together like BigID does. CNBC recognized BigID as one of the top 25 startups for enterprise. They were named to the Inc 5000 and the Deloitte 500 for four years in a row. The publisher of Cyber Defense magazine said quote, BigID embodies three major features we judges look for to become winners. Understanding tomorrow's threats today, providing a cost effective solution and innovating in unexpected ways that can help mitigate cyber risk and get one step ahead of the next breach, end quote. Start protecting your sensitive data wherever your data lives@bigid.com Get a free demo. See how Big ID can help your organization reduce data risk and accelerate the adoption of generative AI. That's BigID B I G I D.com SecurityNow oh, also, there's a free white paper that provides valuable insights for a new framework. You might have heard of it, AI trism, or AI Trust Risk and Security Management to help you harness the full potential of AI responsibly. And you can read all about it@bigid.com Security now these are great partners for anybody who's got dark data who wants to use generative AI but wants to make sure they're training it on the right data. They've got it all together. Big ID.com security now. We thank them so much for supporting the very important work Steve is doing right now. It's not eating lunch, it's. It's delivering these valuable insights to all of our dear listeners. Continue, Steve, continue.
- [105:04]
Steve Gibson
I'm gonna bring up another machine by next Tuesday.
- [105:08]
Leo Laporte
Okay. Do you think it's a machine?
- [105:10]
Steve Gibson
It's a little intel nuc that's been. Oh yeah, for six years. I mean, nothing has changed, but it might be getting old.
- [105:18]
Leo Laporte
Can you launch the resource monitor and see, or the activity monitor, See what's, let's see what's going on.
- [105:23]
Steve Gibson
If there's something going on. At one point it looked fine, but it's, I'm, I'm going to give it a lot more.
- [105:29]
Leo Laporte
Something's happening. Yeah. Yeah. Okay.
- [105:32]
Steve Gibson
Okay. I titled this AI linguistic simulation of intelligent entities and I wanted to share an interaction. I want to start by sharing an interaction that I had Saturday with ChatGPT's latest O3 highest end large reasoning model, which left my mouth hanging open in disbelief.
- [106:00]
Leo Laporte
I love O3, by the way. Very impressive.
- [106:02]
Steve Gibson
Yeah, it is astonishing.
- [106:04]
Leo Laporte
Yeah.
- [106:05]
Steve Gibson
Now, as our listeners know, while I'm not. When I'm not working on this podcast, I'm working to finish off the last bits of the new DNS benchmarks core feature set. The long term cumulative logging features, which is what the Pro edition will have, will follow. Finishing off these core features. For now, we're working to finish sort of the new version 2 base feature set. And I'm down to. I mean, it's like it's done. I'm just down to resolving a few remaining Edge case mysteries. This new code is able to benchmark the performance of IPv4, IPv6, DoH and DoT DNS resolvers either side by side or just per protocol. Because oftentimes you just want to find the fastest DOH resolver you don't care about the others for, because you want to, like, you know, configure your browser best. So that's all working beautifully across all of the mainstream resolvers hosted by Cloudflare, Next DNS, Google, Quad9 and others. But I noticed that while it works on the European Union's new DNS4U dot resolvers, the current code shows their DoH resolvers in red, so it thinks that there's some problem with them and it won't benchmark them to make sure that they all work from where I am in the US because I thought, well, maybe it's a geofencing problem. I configured Chrome to use DOH for its website DNS and set up the DNS for eu, and I use Wireshark to monitor the machine's network interface or for the traffic being sent back and forth. And Chrome worked without any problem at all. So that told me that DOH name resolution was working and available in the US with those DNS for EU resolvers, which meant that something was not working right with the benchmark, even though, as I said, works great with Cloudflare and Quad9 and Google and Next DNS and everybody else. Something about the DNS for eu, but it's working for Chrome, so I need to have it working for the benchmark. One thing Wireshark showed me, which was different between what Chrome was doing and what the benchmark was doing by monitoring the packet capture, was that Chrome was using TLS version 1.3, whereas the DNS benchmark was using TLS 1.2. Chrome brings along with it its own TLS protocol stack, so it can do anything it wants, whereas the DNS benchmark uses Windows native networking APIs, including for TLS, something known as S Channel Secure Channel. When I was originally implementing the Benchmarks TLS protocol on Windows, I noticed online a great deal of confusion about whether Windows 10 offers TLS 1.3, so I needed to determine once and for all. Like, is that what the benchmarks not doing? Chrome's using 1.3, I'm using 1.2 with a benchmark. Is that the problem? So I needed to determine whether it might be possible to for me to get Windows 10 to use TLS 1.3. Was it there? So I did. I the first thing I did, as I often do now, is ask Chat GPT. I decided to see what Chat GPT had to say, so I wrote the following prompt I wrote how can I use the Windows native TLS S channel API under Windows 10 to establish a TLS v1.3 connection to a remote TCP TLS v1.3 server? Okay, now keep in mind when I'm reading its reply that this is a general purpose chatbot that can answer a universe of questions from, you know, why does my navel accumulate lint? To how many angels can dance on the head of a pin? After thinking for 50 seconds, which is quite some time if you watch the second hand of a clock, you know, 550 seconds is you know it like it ground it was grinding on this and it performed four Internet searches on its own and consulted seven sources Chat GPT replied to my question by writing the short answer. You can't what it's like wow. Then it said Windows 10 S channel SSP. Now just listen to the listen to every nuance of this. The short answer you can't Windows 10 S channel SSP simply does not expose TLS 1.3 in any released build, so an SSPI client that runs entirely on Windows 10 cannot negotiate a TLS 1.3 session, period. The highest version the platform will offer is TLS 1.2. Microsoft's own protocol support matrix makes this explicit. Then it quotes it TLS 1.3 is supported starting in Windows 11 and Windows Server 2022. Enabling TLS 1.3 on earlier versions of Windows is not a safe system configuration, unquote. Then it provides the link for that reference and it finishes the SP_ prot_ TLS13_ client constant and the newer SCH_ credentials structure were backported and by the way I had seen those and this was the source of the confusion. So it understood the source of the confusion the that I had that I mean it intuited it I guess were backported to Windows 101809 for source compatibility, which it italicized for me and and the other places it did bold I mean those were its emphasis added, not mine. This is it's just astonishing, it said. But the underlying cryptographic engine that actually implements TLS 1.3 was never shipped in production. Windows 10 builds Insider Preview builds from 2022 to 2021 did contain an experimental TLS 1.3 implementation, but that code never graduated to the GA channel and is no longer available again. My I just looked at this and I thought, what world are we now in where we have this technology? Where again, to me, this is an astonishingly complete and thorough response to my question, which it appears to have anticipated my confusion over the availability of TLS version 1.3 in Windows 10 and explained why there has been some confusion over the question. And I feel as though I should reiterate that this was not a model trained on this domain. It didn't know what I was going to ask. It could just as easily have answered a question about the optimal thread density and caftan robes. I mean, I'm astonished. So I think because I've spent some time in this domain, I've talked about this from all we're coming at, from a whole bunch of different angles on the podcast, and everyone is ringing their hands over AGI and questions of what it means to be conscious. The emergence of these large language and large reasoning models. I think it's going to give cognitive scientists an entire new realm to explore. I mean, that's great for them. It'll be interesting to see where that goes once we figure out exactly what we've created. But having watched ChatGPT work for those 50 seconds to produce that answer, an answer that would have never been possible to imagine just a year ago, I have finally settled upon where I believe we are with all this and why everyone, including me, has been so confused by this. It's because it's confusing. There are.
- [116:01]
Leo Laporte
That's good.
- [116:02]
Steve Gibson
There are two distinctly different things here. On the one hand, we have an amazingly powerful linguistic simulation of an intelligent entity, and on the other hand, we have actually intelligent entities which produce linguistic outputs. And here's the problem. Both of these systems produce linguistic outputs, and the outputs of both systems are identical. The reason for this is that the Intelligent Entity linguistic simulator is an incredibly good linguistic simulator. It's really good at what it does. So no one considering just its linguistic output would have any means of determining that they were not seeing the output of the authentic intelligent entity whose earlier outputs were used to train the simulator. But in no way does that mean that the simulator is actually intelligent, nor is there any reason to believe that it is ever going to be. No simulation, no matter how good it is, is the real thing. The simulator may have been trained on the outputs of the real thing, but that's different from being the real thing. Cognitive scientists are probably falling all over themselves at the prospect of determining exactly to what degree a deep simulation of intelligence is and is not intelligence. But consider this. Although there is admittedly an interaction between thought and language, that's a whole, that's a realm of itself, of philosophy, for a truly intelligent entity, language is the means of communicating the thought. The thought is the motivation which precedes its expression in language for the sake of communication. The difference is that the linguistic simulator has no preceding locus of thought. It is not inspired by thought to express that preceding thought. It simply simulates the result of previous thoughts that were then expressed in language and captured for its training. Without being unduly arrogant, I'm convinced that this is the crucial distinction that separates true thinking beings who use language as a tool and any language models that can never be anything more than empty language shells. This by no mean diminishes the value of what we've created. Having a linguistic interface to the world's stored knowledge expressed as language is astonishingly powerful and useful. But we are much more than that. And so I think, Leo, that's, for me, that rests my case in my mind. I think that there, if you just. Look, the reason people are so confused is if you just examine the output, there is no difference. And that's what all these tests, it looks.
- [119:49]
Leo Laporte
Humans. Yeah.
- [119:50]
Steve Gibson
I mean, there is just no difference.
- [119:53]
Leo Laporte
Right.
- [119:54]
Steve Gibson
You know, many people know people who are far less smart, knowledgeable, intelligent.
- [120:02]
Leo Laporte
That's exactly right.
- [120:03]
Steve Gibson
We have now, you know, coming out of chat GPT.
- [120:06]
Leo Laporte
Exactly.
- [120:07]
Steve Gibson
So there's no difference. But I think we're going to hit a limit because I. Because it will always be a linguistic simulation of an intelligent linguistic creature. I mean, it will always be a simulation of an intelligence. In fact, I sent a show notes out yesterday afternoon and one of our listeners wrote back and said the better term than artificial intelligence is simulated intelligence.
- [120:42]
Leo Laporte
Yeah, mimetic intelligence.
- [120:44]
Steve Gibson
Yeah, yeah, exactly. It is. It is, you know, it is simulating intelligence, which. That solves, you know, calling it a simulated intelligence solves this problem of, you know, well, is it an artificial intelligence? What does intelligence mean? Blah, blah, blah, you know. And again, it doesn't have to be any better than it is. What I've just read is astonishing.
- [121:07]
Leo Laporte
Well, in fact, don't you think we kind of. We looked at HAL 9000 and kind of thought the same thing. We knew that HAL 9000 wasn't a human in any way. That made sense. It was a machine that was very impressive.
- [121:26]
Steve Gibson
But it ran this spaceship. I mean, it was in charge of running this very complicated machine.
- [121:33]
Leo Laporte
Yeah. Until it went wrong. Yeah, but, but maybe because of the way Stanley Kubrick made its voice, it didn't. It talked like this. It didn't attempt to sound human. And one of the things our current AI overlords really want you to think.
- [121:52]
Steve Gibson
Is, boy, the use of personal pronouns.
- [121:55]
Leo Laporte
Yeah.
- [121:55]
Steve Gibson
And, you know, let me think about that for a minute. It's like, oh, my.
- [121:59]
Leo Laporte
And they make the voices as human as they possibly can. And that's what's the deception. I don't think. I don't think we were deceived by HAL 9000. I think we knew it was a simulation. Right.
- [122:11]
Steve Gibson
That's interesting. I. I just. I don't have it here. I just put it back on the bookshelf. I wanted to watch Colossus, the Forbin project again. And I have the dvd. I have. I have the original dvd. Oh, wow. And I just ripped it in order to, you know, to. To move it to a sand. And then. Or. Yeah, and then Lori and I are going to watch it. But the. They used a vocoder, which is back in. You know, this is made in the 70s.
- [122:41]
Leo Laporte
This is. Yeah. Colossus, the Forbin project. Yes.
- [122:44]
Steve Gibson
Right.
- [122:44]
Leo Laporte
Right.
- [122:44]
Steve Gibson
And it's all. What was really creepy was that it had a hard time. I think they deliberately had it, like. It had a hard time, like, saying human. It was like, human. It's like it was little. It's like, whoa. You know, it gave it a little extra creep factor. But I think you're right. I think the. The. The. The use of personal pronouns, especially, you know, talking about an eye and an id, an ego, which is what, you know, we assume, you know, it talking about itself means it does humanize it. It anthropomorizes it.
- [123:21]
Leo Laporte
Yeah. And. And of course, that's what Sam Altman and Elon Musk and all the others want, is they want you to feel like it's a. It's a. It's a human, but it is.
- [123:32]
Steve Gibson
Did you see that. That recent paper that. That compared people who use AI versus don't? And the.
- [123:39]
Leo Laporte
It was such a small sample. I don't credit it with a lot of. It was like 60 people.
- [123:44]
Steve Gibson
Yeah.
- [123:44]
Leo Laporte
And it was pretty clear the researchers were looking for that answer, you know, and that's always a giveaway.
- [123:49]
Steve Gibson
You could always find it in any data.
- [123:51]
Leo Laporte
Any set of data you want.
- [123:53]
Steve Gibson
Yeah.
- [123:54]
Leo Laporte
Look, it's. All we have to say is this is an amazing tool. It does amazing things. It's not perfect, but it's fascinating. And I don't think it's harmful. I really don't.
- [124:05]
Steve Gibson
I don't And I don't think, I don't. I don't think it has that like. And I don't know how to regard this well, it. It disobeyed. It's in, you know, shut.
- [124:14]
Leo Laporte
That's B.S.
- [124:15]
Steve Gibson
Oh, yeah.
- [124:17]
Leo Laporte
It's simulating again. It's a simulation of how a human would act.
- [124:24]
Steve Gibson
Yes, it is. Of what a human would say.
- [124:27]
Leo Laporte
Right. It's doing its best simulation.
- [124:31]
Steve Gibson
Yeah.
- [124:31]
Leo Laporte
That's all.
- [124:32]
Steve Gibson
Yeah. And so what I think we have is an incredibly powerful search engine for content.
- [124:39]
Leo Laporte
That's where it's really useful, just as your example.
- [124:43]
Steve Gibson
I think it's no surprise that that's where it's really useful because that's what it actually is.
- [124:48]
Leo Laporte
It's a summary of all the data. Yeah, it's just encapsulated all the data. Yeah. Good. Yeah. I think, Steve, the more you talk about AI, the. The better. I think you're 100% on track. Yep.
- [125:04]
Steve Gibson
Okay. Okay, last break, then we're going to find out how the world got into this trouble with Typhoon. Oh my God. What happened?
- [125:14]
Leo Laporte
Oh, my God. Well, our show today, brought to you by zscaler, the leader in cloud security. They're a zero trust company, but they use AI to great effect. You know why you have to. Hackers are using AI. Oh, yeah. To breach your organization. AI both powers innovation, drives efficiency, but also helps bad actors deliver more relentless and effective attacks. It's as useful for them as it is for us. You notice perhaps phishing attacks are on the upswing. Phishing attacks over encrypted channels increased by 34.1% last year, fueled by the growing use of generative AI tools. Of course, phishing as a service kits. We've talked about those. Organizations in all industries from small to large are now leveraging AI in response. I guess they're increasing employee productivity with public AI for engineers. We're talking about coding assistance. Marketers use AI for writing tools to great effect. Finance is using AI to create spreadsheet formats. Don't know how to do a pivot table. The AI does. You're also using AI to automate workflows for operational efficiency across individuals and teams. AI is being embedded into applications and services that are customer and partner facing. And ultimately AI is helping us move faster in the market, helping you move faster in the market and gain a competitive advantage. But companies really need to rethink how they protect their private and public use of AI and of course, how they defend against AI powered attacks. I'll give you a reference here, Jason. Kohler. He's the Chief Information Security Officer at Eaton Corporation big company. They leverage Zscaler to embrace AI innovations and to combat AI threats. Here's his quote. Data loss detection has been very helpful for us. ChatGPT came out. We had no visibility into it. Zscaler was our key solution initially to help us understand who was going to IT and what they were uploading. Right? Traditional firewalls VPNs public facing IPs expose your attack surface and they're no match to hackers in the AI era. It's time for a modern approach. Zscaler's comprehensive Zero Trust architecture plus AI ensures safe public AI productivity, protects the integrity of your private AI and stops AI powered attacks. This is a perfect example of AI being a double edged sword. It's great for you, great for the bad guys, but you can thrive in the AI era with Zscaler. Zero Trust plus AI. Stay ahead of the competition, remain resilient even as threats and risks evolve. You're just going to evolve just as faster. Faster. Learn more@zscaler.com security that's zscaler.com security we thank Zscaler so much for supporting security now and Mr. Gibson ready to assault.
- [128:20]
Steve Gibson
His typhoon okay, so Cisco's Talos Intelligence Group have posted their analysis of the SALT Typhoon attacks in a posting titled Weathering the Storm in the Midst of a Typhoon. I don't know whether the fact that Salt Typhoon used three of Cisco's own previous vulnerabilities has anything to do with their decision to reverse engineer Salt Typhoon, but that's what they did. And you know, bravo. I hope they learned some lessons. Cisco's analysis of this super advanced pernicious Persistent threat group begins with this summary. They wrote, Cisco TALAS has been closely monitoring reports, I bet, of widespread intrusion activity against several major US telecommunications companies. The activity, initially reported in late 2024 and later confirmed by the US government is being carried out by a highly sophisticated threat actor dubbed SALT Typhoon. This blog highlights our observations on this campaign and identifies recommendations for detection and prevention of the actor's activities. Public reporting has indicated that the threat actor was able to gain access to core networking infrastructure in several instances and then use that infrastructure to collect a variety of information. There was only one case in which we found evidence suggesting that A Cisco vulnerability, CVE20180171, was actively abused in all other incidents we've investigated to date. The initial access to Cisco devices was determined to be gained through the threat actor obtaining legitimate victim login credentials that's later contradicted, but we'll get there in a second. The threat actor then demonstrated their ability to persist in target environments across equipment from multiple vendors for extended periods, maintaining access in one instance for over three years. A hallmark of this campaign is the use of living off the land techniques on network devices. It's important to note that while the telecommunications industry is the primary victim, the advice contained herein is relevant to and should be considered by all infrastructure defenders. In other words, everybody with Cisco Gear, which is pretty much everybody at the high end. No new Cisco vulnerabilities were discovered during this campaign. That's no new Cisco vulnerabilities. While there have been some reports that Salt Typhoon is abusing three other known Cisco vulnerabilities, we've not identified any evidence to confirm these claims, though others have the vulnerabilities in question are listed below. Note that each of these CVEs have security fixes available. Again, patches available, patches never applied. The threat actors regularly use publicly available malicious tooling. In other words, proofs of concepts that are published, often on GitHub or on the Dark Web to exploit these vulnerabilities, making patching of these vulnerabilities imperative. No argument there. Therefore they wrote our recommendation which is consistent with our standard guidance independent of this particular case, is always to follow best practices to secure network infrastructure. And of course, obviously best practices says keep all your equipment patched up to date, right? That would be nice. So then they list three CVEs CVE2018 0171 as Cisco iOS. Remember that's Internet OS and Internet OS XE software Smart Install Remote code execution vulnerability CVE 20232198 and also 2273 multiple vulnerabilities in Cisco iOS XE software web UI feature and 20242399 Cisco NX OS software command line Injection vulnerability okay, now the fact that a vulnerability Think about this. The fact that a vulnerability Cisco fixed back in 2018 was successfully used by Salt Typhoon to Cisco's own in Cisco with the Cisco's own admission this is what they saw, or anyone for that matter, to penetrate a major telecommunications vendor in 2024 and not just one many in 2024 is difficult to explain away. By 2024 the patch for a 2018 vulnerability would have been six years old. So Cisco gear from before 2018 had been sitting without anyone considering its need for updating throughout that entire time. Six years. And would you like to guess the CVSS score of that now 7 year old vulnerability CVE2018 0171 believe it or not at the time it achieved and still has a whopping CVSS of 9.8 which as we know we rarely see. You have to really work to get a CVSS of 9.8. This is why I stated earlier that our current system of relying upon the timely or any really any post sales maintenance of equipment on a security perimeter is fundamentally broken. We cannot rely on it. Web servers are certainly not permitted to be using any certificate that expired six years before, but critical networking gear is allowed to continue operating month after month and year after year with effectively expired firmware containing critical known CVSS 9.8 scale vulnerabilities. So what different activities did Cisco observe on the part of these threat actors known to be Chinese State sponsored SALT Typhoon under credential use and expansion? Cisco wrote of these attacks which they observed the use of valid stolen credentials have been observed throughout this campaign, though it is unknown at this time exactly how the initial credentials in all cases were obtained by the threat actor. We've observed the threat actor actively attempting to acquire additional credentials by obtaining network device configurations and deciphering local accounts with weak password types, a security configuration that allows users to store passwords using cryptographically weak methods. In addition, we've observed the threat actor capturing SNMP TACs and radius traffic, including the secret keys used between network devices and TACACS RADIUS servers. The intent of this traffic capture is almost certainly to enumerate additional credential details for follow on use. Then we have configuration exfiltration, they wrote. In numerous instances the threat actor exfiltrated device configurations, often over TFTP and or FTP. These configurations often contain sensitive authentication material such as snmp, read write, community strings, and local accounts with weak password encryption types in use. The weak encryption password type would allow an attacker to trivially decrypt the password itself online. In addition to the sensitive authentication material, configurations often contain named interfaces which might allow an attacker to better understand the upstream and downstream network segments and use this information for additional reconnaissance and subsequent lateral movement within the network. So they were in there, they were exfiltrating everything they get their hands on. And unfortunately when you're actually looking at the traffic where you assume no one should ever be, there are lots of secrets there and lots of useful information that tells you where to find other secrets. Under infrastructure pivoting they said a significant part of this campaign is marked by the actors continued movement or pivoting through compromised infrastructure. This machine to machine pivoting or jumping is likely conducted for a couple of reasons. First, it allows the threat actor to move within a trusted infrastructure set where network communications might not otherwise be permitted. Additionally, connections from this type of infrastructure are less likely to be flagged as suspicious by network defenders, allowing the threat actor to remain undetected. The threat actor also pivoted from a compromised device operated by one telecom to target a device in another telecom. We believe that the device associated with the initial telecom was merely used as a hop point and not the intended final target. In several instances, some of these hop points were also used as a first hop for outbound data exfiltration operations. Much of this pivoting included the use of network equipment from a variety of different manufacturers and finally, under configuration modification they said, we observed that the threat actor had modified devices running configurations as well as the subsystems associated with both Bash and Guest Shell. They said in Parens, Guest Shell is a Linux based virtual environment that runs on Cisco devices and allows users to execute Linux commands and utilities, including Bash. Now I'll just stop to say that what this means is that we've got Cisco devices which are being penetrated that are now powerful enough. They're just not switches. Dumb switches with access control lists where packets get routed. They are sophisticated enough to be running Linux based virtual environments and commands. So these are computers on the edge that have serious vulnerabilities that have not been these are computers that haven't been patched in seven years. No Linux user would do that and they're critical infrastructure machines. So they said Running configuration modifications they saw included the loopback interface, IP address was modified, GRE tunnel creation and use meaning setting up outbound encrypted tunnels to exfiltrate whatever they wanted creation of unexpected local accounts, ACL modifications, access access control lists, SNMP community string modifications, changing how SNMP access can be done remotely HTTP and HTTPs server modifications on both standard and non standard ports so setting up local servers so they can access content remotely Then under shell access modifications they said guest shell, enable and disable commands started SSH alternative servers on high ports for persistent access such as SSHDRNs on port 57722 on underlying Linux shell or Guest shell created Linux level users modifying et cetera shadow and et cetera password files and added SSH authorized keys under root or other users at Linux level. So in other words, completely owning this equipment like taking it over setting up servers for remote SSH access. Talk about persistent presence. So it is no surprise that these threat actors were able to obtain and maintain persistence within someone's network. If you have network machines that no one has bothered to maintain for six years containing a persistent and lingering CVSS of 9.8 vulnerability which provides a means for gaining remote entry. And if that system is powerful enough to host a Linux based virtual environment where it's possible for an attacker to modify access control list rules, start HTTP servers on non standard ports and fire up SSH servers on high ports, it would be more surprising if they did not obtain a permanent persistence within a victim network. It's just horrifying. And I get it that Cisco wants to paint the best picture on this that they can. That's only natural. But they and others have enumerated a total of four vulnerabilities that were used by these salt Typhoon attackers. So far I've only talked about the oldest one. It created a six year window of vulnerability for any of these Cisco devices. And notice that we don't know the windows closed yet, right? I mean the presumably there are still routers out there that have that. That are carrying this firmware from 2018. So the window six years and counting in terms of of how of its duration. But even though this flaw from 2018 carried a heart stopping CVSS of 9.8, believe it or not, it wasn't the worst one. Having a 6 year window of opportunity is not good. But all an attacker needs is for that window to still be open when they come knocking. So the fact that one of the other CVEs associated with these salt typhoon attacks was only discovered in 2023 in no way diminishes its severity. So long as it was present at the time of the attacks in 2024. That's all the attackers need. And what CVSS score do you imagine it carries? Would you believe that Cisco's CVE 202320198 has been assigned that rarest of the Rare CVSS of 10.0? Yes, it's a 10.0 because it cannot get any worse.
- [145:24]
Leo Laporte
Wow.
- [145:26]
Steve Gibson
And this is a CVSS for a piece of networking gear that's inherently on the front lines, is exposed to the bad guys and being a set and forget appliance will tend not to be on anyone's maintenance and update radar. As I said earlier, the industries we're doing the best we can and this is the only thing we can think of model of after sales Security maintenance is obviously inherently and badly broken. There's a chain of responsibility that requires everyone to perform perfectly. Cisco needs to not ever make a mistake. And once sold and deployed Anything that's ever found to be wrong with one of their devices needs to be immediately repaired in the field. But this chain is inherently brittle, with everything working against it. Mistakes happen. Entropy is real, so mistakes are always trying to happen, and Cisco is going to ship mistakes. Technicians in the field are always going to appear to have better things to do than to continually run around updating the operating versions of the firmware of every device they have every time an update is made available for the sole purpose of keeping them all up to date. Especially when the updates that really are critical may be much fewer and rarer. So there's inherently pressure to set it and forget it, don't break it if it's not broken, even though doing that means that anything that's later found to have slipped past Cisco's testing and quality control at the time of sales will tend to persist in the field. Now, this podcast has been around for a while, so you might imagine that something like a CVSS of 10.0 might have come to our attention back in 2023, and that I might have believed that this audience should be informed of it.
- [147:46]
Leo Laporte
Oh, yes, and.
- [147:47]
Steve Gibson
And sure Enough, podcast number 945, which you and I Leo, delivered on October 24, 2023, was titled the Power of Privilege. And among the summary items at the top of the show was quote, vulnerabilities with a CVSS score of 10.0 are blessedly rare, but today the industry has another during the coverage of this, A little over 18 months ago, I noted that this was one of those horrific web management UI authentication bypass vulnerabilities, and that this meant it could be scanned for. And scanned for it was, at the moment of its announcement, around 42,000 instances of Cisco Web UI were found to be online and vulnerable, but that number dropped from with surprising speed. This was not because the techs at the world's telecom companies were on the ball and promptly responding to the emergency. No, the numbers of vulnerable Cisco devices were observed to drop precipitously because the bad guys like Salt Typhoon, we now know who were on the ball scanned, located, immediately climbed inside and said thank you very much, see you later, and shut the door behind them.
- [149:26]
Leo Laporte
Oh my God.
- [149:28]
Steve Gibson
Taking their now compromised device off the map while they set up persistent presence.
- [149:35]
Leo Laporte
Did they fix. Did they patch the systems?
- [149:37]
Steve Gibson
They. They closed the vulnerability.
- [149:39]
Leo Laporte
That's.
- [149:40]
Steve Gibson
Nobody else could get them.
- [149:42]
Leo Laporte
That's so amazing.
- [149:43]
Steve Gibson
Or find them.
- [149:45]
Leo Laporte
Holy cow.
- [149:46]
Steve Gibson
Now, we often talk about these vulnerabilities in the abstract, right? As we did just over a year and a Half ago in this instance, because that's normally all we have is an abstraction. You know, it's not often that we're able to follow up with a whatever happened with that horrific 10.0, but today we can because many security researchers, including Cisco's own Talos Group, have identified that event a little over 18 months ago as one of the principal ways China's SALT Typhoon malicious hacking group obtained access to the networks of many domestic US and foreign companies networks. We now know what a disaster has ensued from that event and given the 42,000 initially vulnerable networks scale of this, that it's 42,000 networks. It's also clear why no one can be really sure that Salt Typhoon has been completely expunged from every network they penetrated. There are just too many of them and they weren't all telecom companies. That's just what's making the news now. The other significant thing we learned from Cisco's Talos After Action report is the surprising power of the devices that were found to be infected and that the bad guys knew how to leverage that power to their benefit. In their reports section describing the commands that were observed or logged to have been executed, they list they said Packet capture the threat actor used a variety of tools and techniques to capture packet data throughout the course of the campaign listed below. Then they list TCP dump, a portable command line utility used to capture packet data at the underlying OS system level. TPA cap Cisco iOS XR command line utility used to capture packets being sent to or from a given interface to via Net IO at the underlying OS level embedded packet capture EPC Cisco iOS feature that allows the get this the capture and export of packet capture data. Then they show the command monitor capture cap export FTP and then a URL of an FTP server. When I talked about the concerning power of the Cisco devices the attackers had access to, this is what I meant. The operating systems of these Cisco devices support the installation of a tap into network interfaces which then monitors, captures and exports the intercepted network traffic to any external FTP server. It would be difficult to invent a scenario that was worse than this. If this appeared in the plot of some network hacking movie, I'd raise my eyebrows and think oh yeah, right. But the attackers were observed to be using those commands on Cisco's compromised gear. It's no wonder the title of Talos disclosure is Weathering the Storm. To give a deeper sense for the sophistication of SALT Typhoon, Cisco describes a custom utility they discovered that Salt Typhoon had written just for this purpose under the heading Operational utility Jumbled Path they explain the threat actor used a custom built utility dubbed Jumbled Path which allowed them to execute a packet capture on a remote Cisco device through an actor defined jump host. This tool also attempted to clear logs and impair logging along the jump path and return the resultant compressed encrypted capture. So it's encrypting and compressing the capture via another unique series of actor defined connections or jumps. This allowed the threat actor to create a chain of connections and perform the capture on a remote device. The use of this utility would help to obfuscate the original source and ultimate destination of the request, and would also allow its operator to move through potentially otherwise non publicly reachable or routable devices or or infrastructure. This utility was written in Go and compiled as an ELF binary using an X8664 architecture. Compiling the utility using this architecture makes it widely usable across Linux operating systems, which also includes a variety of multi vendor network devices. This utility was found in Actor configured guest shell instances on Cisco Nexus devices. You know, we're really talking about full penetration here. What's more chilling is that there's really no way to know where these guys might still be, and you really have.
- [155:33]
Leo Laporte
To blame Sisko for leaving that door wide open. Yes, that's appalling.
- [155:39]
Steve Gibson
It is appalling, and we're going to get to appalling in a second. SALT Typhoon also invested in bypassing and evading any defenses. Talos explained the threat actor repeatedly modified the address of the loopback interface on a compromised switch and used that interface as the source of SSH connections to additional devices within the target environment, allowing them to effectively bypass access control lists in place on those devices. The threat actor routinely cleared relevant logs including bash history, auth log, last log, wtemp and BTEMP were applicable to obfuscate their activities. Shell access was restored to a normal state in many cases through the use of the guests shell disable command. The threat actor modified authentication authorization and accounting AAA server settings with supplemental addresses under their control to bypass access control systems. I mean these organizations were completely owned by Chinese malicious state sponsored attackers. In other words, these guys really knew their way around this Cisco environment. You know these were not script kitty weenies. It would be fascinating to to have something we'll likely never see, which would be the SALT Typhoon view of this. Did they discover or learn of this Cisco CVSS 10.0 vulnerability that immediately jump on, you know, scan, find them, jump on them, crawl inside, close the door behind them, and only then tool up and hone their expertise to this level, or were they already fully equipped with this level of knowledge? My guess knowing Salt Typhoon is that it would be the latter. I suspect they were already well versed in in Cisco exploit operations, which would probably be conducted, you know, previously on a much smaller scale. And then this motherlode of A publicly exposed 10.0 login authentication bypass fell into their lap so that they already knew what to do. It was only a matter of identifying victims and doing it all quickly enough. Under the topic of detection, Talos said, we recommend taking the following steps to identify suspicious activity that may be related to this campaign. And I mean, that's just generic pablum, they said. Conduct comprehensive configuration management inclusive of auditing in line with best practices. Conduct comprehensive authentication authorization, command issuance monitoring. Monitor syslog and AAA logs for unusual activity, including a decrease in normal logging events, right, because the bad guys are deleting the logs or a gap in logging activity. Monitor your environment for unusual changes in behavior or configuration profile fingerprint via netflow and port scanning network devices for a shift in surface view including new ports, or opening and closing and traffic to or from where possible. Develop NetFlow visibility to identify unusual volumetric changes. Look for non empty or unusually large bash underscore history files. Additional identification and detection can be performed using Cisco forensic guides now okay, none of that's surprising. It's all very generic. But something in their next section under preventative measures caught my eye. The first item on Cisco's list of preventative measures is Leverage Cisco hardening guides when configuring devices. The fact that there's a hardening guide suggests that even today Cisco Cisco still doesn't get would be like 10 years ago Cisco's hardening guide saying be sure to delete the default admin credentials shipped with your Cisco device. As we'll recall, Cisco was once actually doing that. In other words, there should not be any guide for hardening a device.
- [160:32]
Leo Laporte
Shouldn't be necessary.
- [160:34]
Steve Gibson
The only right, the only guide available should be for optionally loosening a device's security.
- [160:41]
Leo Laporte
Oh, I like that.
- [160:44]
Steve Gibson
It ought to be difficult and require deliberate work to make any such device insecure. There should never be optional advice. Leverage Cisco hardening guides when configuring devices. You know, we know people don't. And how do we know? Because people don't and haven't. Talos's report finishes with an analysts comments section. This should be interesting. They write there are several reasons to believe this activity is being carried out by a highly sophisticated well funded threat actor including the targeted nature of this campaign, the deep levels of developed access into victim networks and the threat actors extensive technical knowledge. Furthermore, the long timeline of this campaign suggests a high degree of coordination, planning and patience, standard hallmarks of advanced persistent threat APT and state sponsored actors. During this investigation we observed additional pervasive targeting of Cisco devices. Yeah gee, why you think they were targeting Cisco with exposed smart install SMI and the subsequent abuse of CVE2018 0171 a vulnerability in the start and small feature of Cisco iOS and iOS XE software. This activity appears to be unrelated to the SALT Typhoon operations and we have not yet been able to attribute it to a specific actor. The IP addresses provided as observables are associated with this potentially unrelated SMI activity. Legacy devices with known vulnerabilities such as smart install should be patched. Wouldn't that be nice? And decommissioned. Okay, if no longer in use. Well we know they're in use because they're on the front lines. Wouldn't it be nice if that was the world we were living in? Again, all of our real world experience informs us that it's not. There were 42,000 instances of that vulnerability. That back door open in 2023. When we talked about it in October of that year, they wrote even if the device is a non critical device or carries no traffic, it may be used as an entry door for the threat actor to pivot to other more critical devices. Uh huh. The findings in this blog represent Cisco Talus understanding of the attacks outlined herein. This campaign and its impact are still being researched and the situation continues to evolve. As such, this post may be updated at any time to reflect new findings or adjustments to assessments. Okay, so we've achieved an unfortunate bit of closure regarding a very serious Cisco flaw that woke up the entire security world a little more than 18 months ago. @ the time that we covered this, I wrote the following for that podcast. This first known instance of attacks against Cisco's iOS XE based routers and switches, which appear to have been initial proof of concept probing incursions, occurred at the end of last month on the 28th. So that would have been September of 2023. Or yeah, 2023. I wrote then more than three weeks passed before Cisco finally released the first fixes last month, October 16th. During those the intervening three weeks, more than 42,000 of Cisco's iOS XE based devices were compromised. We know that it was 42,000 devices because scanners were quickly created by security firms who wanted to track incursions and in response to the visibility of their initial implants, the perpetrators of these attacks are updated their malware to make it less visible. And we know at least some of what became of those devices. China's SALT Typhoon Group assessed their massive inventory of access, discovered that they were now inside the networks of the world's telecom providers, not to mention some large ISPs and even digital Realty. One of the largest cloud providers then began taking advantage of their newfound access for espionage and spying. Are they gone? Have all 42,000 instances of their intrusion been found and removed? Given everything we know of the way today's networks are being managed, that's not a bet I would take. Every listener of this podcast knows that I draw a clear distinction between mistakes and policies. Mistakes happen, but policies are deliberate. In this case I must take issue with Cisco's deliberate design and design as policy of its crucial web management interface. We know for a fact that some 42,000 instances of their XE class devices had web management exposed globally. Web management exposed globally it should not be possible to expose web management globally because there is no management defensible reason for ever allowing global access to a high end devices public management interface. Everyone listening to this podcast also knows what a fan of simple IP filtering I am. I'm a fan because the technology is so simple and it offers so much leverage. So okay, sure, allow a single remote IP or several specific remote IPs or perhaps a slash 24 class C size network block to be specified to have remote access. Those would allow for remote management across disjoint corporate networks, but simply don't provide any provision for access from any IP anywhere in the world. How can that possibly ever actually be necessary? Who would ever actually need to allow China to access your device's management interface? Because that's what's being explicitly allowed whenever unfiltered remote access is is enabled. Sure, an acl, an access control list could and should have been added to that access, but I bet that it that it says so right there and in bold print in Cisco's illustrious hardening guide. But that's not the correct policy. What no one ever wants or needs to have happen should not be possible. It should not be possible for any lack of configuration or misconfiguration to give Chinese hackers anywhere outside of one's immediate control access to something they should not have. It should not be possible. Period. I'm sure that if confronted with this, Cisco's engineers would say well, no one should leave their web admin accessible to anyone, and we provide a very nice access control list that allows anyone to limit that access. Okay, sure, but the default is wide open, and even if it wasn't, it would be possible to innocently add a wide open rule because, hey, that would be easier. However, nothing changes the fact that there is no demonstrable need for for global public access to a high end router's admin Interface. Yet some 42,000 networks were all compromised in the blink of an eye because this was Cisco's responsibility transferring policy. Quote it's not our fault if you don't follow our optional hardening guide. Leo, I am reminded of Douglas Adams original Hitchhiker's Guide novel, where the Earth is scheduled for demolition by the Vogons due to the need to create an intergalactic bypass, and the novel's protagonist, Arthur Dent, says, what are you talking about? You can't just destroy the Earth. And he's told that all the proper notices and required paperwork had been filed with the local Galactic sector office some time ago. You know, similarly, why are they complaining that 42,000 of our XE class devices were all just taken over by Chinese military hackers? Didn't they read the hardening guide that we prepared?
- [170:44]
Leo Laporte
It was stored in the basement of the building in the third arm of the Galactic Galaxy. Yeah, it's amazing. And they should really be. I didn't realize Salt Typhoon was all their fault. I thought it was SS7 and a variety of other things. It's really the Cisco thing. Cisco, man, they need to really take responsibility for this. And so the fix would be to get. Well, the fix would be to patch these routers. But how do you get. If they're already in there, how do you get rid of them?
- [171:19]
Steve Gibson
That's the problem. As we you And I said 20 years ago, if you have malware in your PC, you can't trust it anymore. You never know. You can never trust it. I mean, we know that malware can live in printers, right? So.
- [171:37]
Leo Laporte
Cameras.
- [171:38]
Steve Gibson
I mean, it could be anywhere inside. And when you're talking about AT&T, they don't even know the wires they have. I mean, it is, it is, it's astonishing. I mean, it's just. It's like, you know, for. For years and years and years on this podcast, there's been a tendency to say, whoa, the sky is falling. Oh, we've got the. Well, this is what that looks like. It's not the end of life on Earth. No, but. But the US's networks have fallen to Chinese military and they can't be fixed.
- [172:15]
Leo Laporte
Reason in a reasonable way.
- [172:17]
Steve Gibson
You don't know where they are now.
- [172:19]
Leo Laporte
And people you know might take issue with your idea that you can make software perfect, but this is so much the opposite of perfect. You definitely shouldn't have software with an open portal on a networking device and then say, well, you didn't harden it, it's your fault.
- [172:40]
Steve Gibson
And my point was it should not be possible to allow any IP to access the management interface. What possible need is there? You know, what network or a couple IPs should have access to that management interface? So we've long ago learned username and password doesn't cut it. No one should have access. And if you simply drop any IP packet coming in, it doesn't matter if you then discover a vulnerability later, nobody can connect to that port. And there's no reason Cisco should have ever allowed it. It's hubris on their part and, and, and laziness.
- [173:27]
Leo Laporte
Yeah. And they're not suffering a consequence at all in any way, of course.
- [173:34]
Steve Gibson
No, you know, because, because their license agreement, they're all of their, their attorneys are all over us saying, well, we, we did all this is, is the best effort. Everybody knows things are not perfect and we aren't either. And you use this at your own, at your own risk and any damage that befalls you is yours. And if you don't want that, then don't buy it.
- [173:58]
Leo Laporte
The real problem is that the damage is not to the users of the Cisco equipment, but to their customers.
- [174:05]
Steve Gibson
Right. And that was the point that the, the, the Canadian posting meant the, the telecom service providers, the people that they are selling telecom services to. It's like back in the days where that, that, that, that, that dental managed service provider infected all the dental offices that, that were using them as their service provider. Well, this is a telecom service provider. All of their clients, all of their customers are now victim.
- [174:34]
Leo Laporte
Yeah, Steve, you've done it again. You've raised awareness. I don't know if we fixed the world's problems, but at least people understand a little bit better about why they exist and who's responsible for them. So that's a good thing. Steve Gibson does this show every Tuesday, 11:00am Sorry, it's after Mac Break weekly. That's 11:00am we do this show at 1:30pm Pacific, 4:30 Eastern, 20:30 UTC. We stream it live. So you, if you need it, if you need the freshest version of the show, you can get it. Actually, there's an even fresher version. I'll tell you about in a second. But if you want to watch live, we are on eight different platforms for our Club Twit members are valued, valued Club Twit members. You guys know who you are and we are so grateful to you for your support. They're the ones who put together about 25% of our operating expenses. If you're in the club, you can watch on the Discord, although Discord never was designed for streaming video, so a lot of people choose to watch on some of the other platforms. We're also open to the public on YouTube, Twitch, Discord, TikTok, Facebook, LinkedIn, X.com and Kick. So pick your poison. In some cases, pick your platform and watch live after the fact. On demand versions of the show are available in two different places. Now, Steve has some unique versions of the show. In fact, all the versions he has are unique. At his website, GRC.com he's got a 16 kilobit audio, which no podcast has put out in 20 years, but he does because it's small, it's a little scratchy, it sounds like Thomas Edison, but it's okay. It's small and that's, that's its chief advantage. There's also a 64 kilobit audio, which is the second smallest version because for a variety of technical reasons, we put out a 128 kilobit audio. So, but the 64 is fine. You can get that from Steve. So again, if you have bandwidth issues, that's a good place to go. He has transcripts written by an actual human being, not by AI. Elaine Ferriss does a brilliant job. Those are also available for every show at his site. Takes a couple of days after the show's over to do that. Of course, he also has the show notes, and that's the first version of the show you can get the day before in many cases by subscribing. Easy to do. Go to GRC.com email that's designed for you to get your email address on Steve's whitelist. So you can email them with comments or maybe pictures of the week and something like that. But you'll see when you put in your email address below it, there are two unchecked boxes. Because Steve's cool. There are two unchecked boxes, one for his weekly show notes email, and one for a very irregular email about new products like we're all waiting with bated breath for the DNS Benchmark Pro. You'll get an email when that's available. So that's probably worth signing up to both of Those but again that's GRC.com email. You gotta check the boxes yourself. You know, you gotta choose it. Let's see what else. Oh, while you're there, if you don't already have a copy and I can't imagine there's anyone who doesn't. But if you don't already have a maybe somebody who doesn't have mass storage of any kind, you know, I don't know who that would be. But if you have technology you probably have mass storage. And if you have mass storage, you definitely need space. Spin right this Steve's bread and butter. It's the world's best mass storage maintenance, recovery and performance enhancing utility. Yes, it works with SSDs. Just get it@grc.com Lots of other free stuff including Shields up which is one of the oldest and best and still operating network utilities to check to see if your router is opening up your ports to the public. Well, there's just lots of stuff. It's a fun place to go if you've got an app. Wait, well you got an afternoon and spend some time browsing around GRC. We have, as I said, 128 kilobit audio and some form of video. I guess it's 1080. I don't know what it is, but I think it's 1080i it's whatever it is, it's up at the website. Find out for yourself at Twitt TV SN for security. Now there's a link there to the YouTube channel that might be a little bit higher quality, I don't know. But you can use that to share clips. A good way to, you know, if you've got a. If your company's using Cisco routers for instance, you might want to just send them a little clip from the show and say have you read the hardening guide? Maybe you should. That's a great way to do it. YouTube makes that very easy. Honestly the best thing to do. Subscribe to the show. That way you don't ever miss an episode. It automatically downloads in your favorite podcast client. So whenever you're in the mood for a little Steve Gibson, you can just fire that sucker up. And if you do go that route, please leave us a good review. Leave us a five star review because it helps spread the word. That is more important than you might imagine. Next best thing. Join the club. 10 bucks a month gets you ad free versions of this show. All of our shows access to the club. Twit Discord. A great place to hang out with really smart people ask interesting questions, talk about what you're doing with AI and images and whatever it is you're up to. And you get a special feed of content that we don't put out in public. Like I think is going to be very interesting. On Friday, we're doing a two part music thing with my friend Norman Maslov, who's a vinyl collector. We'll talk about vinyl records, but then we're also going to talk about The History of MP3s and Digital Records with the author of a book, a really interesting book all about that. That's this Friday. AI User Group is next week. A lot of stuff. There's great stuff going on in the club. Please. Twit tv Club Twit. We'd love to have you, Steve. We will be back next Tuesday for another thrilling, gripping edition of security now.
- [180:23]
Steve Gibson
On the 4th of July.
- [180:26]
Leo Laporte
Yay. See you then.
- [180:27]
Steve Gibson
Bye.
- [180:31]
Leo Laporte
Security Now.
- [180:39]
Steve Gibson
Hi, Zoe Saldana. Welcome to T Mobile. Here's your new iPhone 16 Pro on us. Thanks. And here's my old phone to trade in. You don't need a trade in. When you switch to T Mobile, we'll give you a new iPhone 16 Pro. Plus we'll help you pay off your old phone. Up to 800 bucks and you still get to keep it. There's always a trade in. Not right now. @ T Mobile. I feel like I have to give you something in return. Return for karma. That's okay. I don't really have much in my purse. Oh, let's see. Hand sanitizer. It's lavender. I'm good. Seriously. Let me check this pocket. Oh, mints. Really, I'm fine. Oh, I have raisins. I'm a mom. Wait, wait one sec. I've got cupcakes in the car. It's our best iPhone offer ever.
- [181:16]
Leo Laporte
Switch to T Mobile.
- [181:17]
Steve Gibson
Get a new iPhone 16 Pro with.
- [181:19]
Leo Laporte
Apple intelligence on us. No trade in needed.
- [181:21]
Steve Gibson
We'll even pay off your phone up to 800 bucks. Bucks with 24 monthly bill credits. New line, $100 plus a month on.
- [181:28]
Leo Laporte
Experience beyond finance agreement 99999 and qualifying.
- [181:31]
Steve Gibson
Forwarded for well qualified plus tax and $10 connection charge.
- [181:33]
Leo Laporte
Pay off via virtual prepaid card. Allow 15 days credits end imbalance due if you pay off earlier.
- [181:37]
Steve Gibson
Cancel ctmobile.
- [181:38]
Leo Laporte
Com.