← All TWiT.tv Shows (Audio)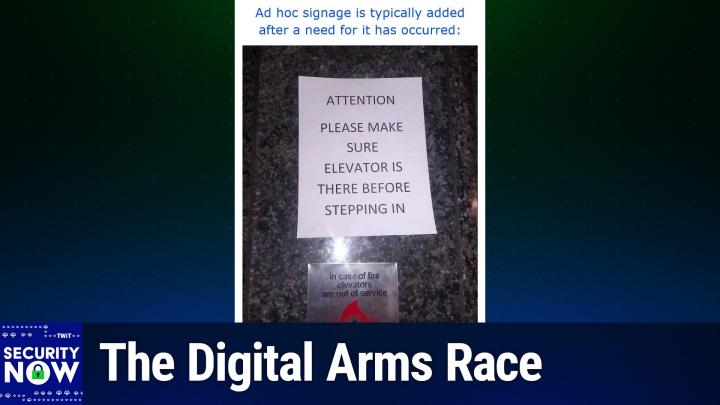
Loading summary
Transcript369 lines
- [00:00]
Leo Laporte
It's time for Security Now. Steve Gibson is here. We'll talk about zero days and what we're doing is the United States to stockpile them and what Israeli companies are doing using their zero days to attack journalists in Italy. Also, now that the Supreme Court has decided it's okay to have age verification, how will that impact the Internet? That and a lot more coming up next on Security Now. Podcasts you love from people you Trust. This is TWiT. This is Security now with Steve Gibson. Episode 1033, recorded Tuesday, July 8, 2025. Going on the offensive. It's time for Security now, the show we cover the latest in security privacy, how computers work, the greatest science fiction in the world, and whatever else Steve Gib is into. He is a polymath. And we all give you the salute. Live long, Prosper never knows. We're all counting on it.
- [01:07]
Steve Gibson
I'm gonna have to bring you up to speed soon about.
- [01:11]
Leo Laporte
What's that? Oh, what's that?
- [01:13]
Steve Gibson
That's.
- [01:14]
Leo Laporte
What is that? A little buzzer?
- [01:15]
Steve Gibson
That's the evolution of the device that you and Lisa experimented with.
- [01:21]
Leo Laporte
We were putting electrolyte gel on our. Our temples, foreheads, and on our forehead, our. No, I didn't ever do the tongue with you. I do that with the other. And then. And then. And. Oh, cool.
- [01:34]
Steve Gibson
I know.
- [01:34]
Leo Laporte
Lori uses this, right? In her practice.
- [01:38]
Steve Gibson
She does. I couldn't sleep if I didn't. It's. It's just completely resolved my.
- [01:43]
Leo Laporte
Well, I need something to help me sleep. I've. I've done everything under the sun and.
- [01:47]
Steve Gibson
I meant to ask you, how's the GLP one?
- [01:51]
Leo Laporte
It's going well. We've upped the dose now to 0.5 milligrams.
- [01:56]
Steve Gibson
Is that double what you were at, were you at.
- [01:58]
Leo Laporte
Yeah. They start you on a basically inconsequential dose and then they slowly double it up to a point, I think, until things start to fall off, until you start. You get the shakes and you can't go on. I think what they're really looking at is what my numbers look like. And then they want to give you the least amount that's effective. So, in fact, I. I'm on 0.5 and they said, before we go up, I want to see your numbers. So I have to say, it's helped the blood glucose a lot. It's really.
- [02:28]
Steve Gibson
And you wait 90 days between changes in order to get a month, A1C, four weeks. Cool.
- [02:34]
Leo Laporte
Oh, for the A1C.
- [02:35]
Steve Gibson
No, I.
- [02:36]
Leo Laporte
My. Yeah, not 90 days. So I don't know when my A1C. Yeah. It wouldn't make sense to do it more than every 90 days. So I don't know when my next A1C is incident. A couple months, I think. But. Well, I see I have. I'm wearing one of those continuous glucose monitors. Yeah, I know exactly how I'm doing.
- [02:51]
Steve Gibson
That's very cool.
- [02:52]
Leo Laporte
Yeah.
- [02:52]
Steve Gibson
And I heard someone say that it mod. Oh, it was Calacanis, I think, who was also experimenting with one, saying that it modified his eating.
- [03:02]
Leo Laporte
Oh, it definitely does.
- [03:04]
Steve Gibson
When you see the consequence of what you eat in on near real time.
- [03:08]
Leo Laporte
Well, it's almost like you can't eat what you used to eat. Your stomach hurts. One of the. One of the negative side effects of.
- [03:15]
Steve Gibson
It is I. I meant having a real time blood glucose feedback.
- [03:19]
Leo Laporte
Oh, that. Absolutely. That was Alex Lindsay talking about that.
- [03:22]
Steve Gibson
Okay, that's right.
- [03:24]
Leo Laporte
Absolutely. But I've worn real time, you know, continuous glucose monitors in the past. It's only a suggestion.
- [03:32]
Steve Gibson
You sort of get used to it after a while. It's a suggestion that thing.
- [03:36]
Leo Laporte
You know, this. For me, the real problem. I'm on Ozempic for folks who don't know my doctor prescribed it. I'm not doing it on my own. But for me, the thing that really helps is I think people like you, and normally thin people don't understand this, but those of us who have weight problems often have this constant hunger. And sometimes people on Ozempic call it hunger noise or it's shouting at you pretty frequently. Oh, I'm hungry, I'm hungry. That's gone. You don't hear the background noise anymore. So that's a huge. More than anything else, that's a huge help.
- [04:14]
Steve Gibson
I. You would be surprised how much I understand that.
- [04:19]
Leo Laporte
Oh, good.
- [04:19]
Steve Gibson
Because I had it and it's. And I.
- [04:21]
Leo Laporte
How'd you get rid of it?
- [04:22]
Steve Gibson
It was my first year. I didn't know whether it was crashing into ketosis or my first experimentations with the zapper, because I was. I did both around the same time.
- [04:32]
Leo Laporte
Keto helps.
- [04:33]
Steve Gibson
And it changed my life. Yeah, well, then. And that's why I was so reluctant. I was scared to leave Keto worried that that would. I would resume, like, you know, a constant battle. And it came back.
- [04:46]
Leo Laporte
If you could get rid of that hunger noise without being on a medication, obviously that would be far preferable. But I also am a type 2 diabetic, and so my blood sugar was going up into the danger zone. I just saw a study, you'd probably be interested in this, that showed that all this excess glucose we talked about, about how it's damaging, it's also damaging to the brain and it can actually be involved in the. In the Alzheimer's. And it's one of the reasons now they're starting to think because they do notice that semiglutide and related drugs are lowering Alzheimer's.
- [05:21]
Steve Gibson
Yeah.
- [05:22]
Leo Laporte
Yeah. So I'm happy about that because my. Both my parents in their 90s are physically fine, but. But they're mentally not so good. She's in a happy place. She doesn't remember what happened yesterday, but she remembers everything that happened in the past. And we have perfectly normal conversations. But she's definitely diagnosed with Alzheimer's. So I would like to keep all my faculties as long as I can possibly think sometimes.
- [05:52]
Steve Gibson
Oh my God, my screen blanker just.
- [05:54]
Leo Laporte
Oh, that's just light. By the way, folks.
- [05:57]
Steve Gibson
I thought I had set it up. Sometimes Google 40 hertz, you know, 40 hertz Alzheimer's. You will be astonished by what comes up.
- [06:11]
Leo Laporte
Well, let me know when you. When you're ready to distribute the box.
- [06:13]
Steve Gibson
Research out of MIT is astonishing.
- [06:17]
Leo Laporte
Does it break up the plaques or something like that?
- [06:20]
Steve Gibson
It reverses.
- [06:22]
Leo Laporte
Nice. Oh, well, I'll bring it over to her and see what. Hey, mom, just strap this to your head and see what happens here. Okay, let's talk about what's going to be on.
- [06:31]
Steve Gibson
I'm actually here, believe it or not, folks.
- [06:34]
Leo Laporte
Yes.
- [06:34]
Steve Gibson
To. To do a podcast about. Nominally about technology, not body technology, but Internet technology. I ran across an amazing. I guess you'd call it a policy paper out of a Washington D.C. think tank, which by an ex. Google. What's the Google Security Group? I. I'm blanking.
- [07:07]
Leo Laporte
Oh, Project Zero.
- [07:09]
Steve Gibson
It's there. It. It's the. It's the related. It's not Project Zero, it's. They. They. They have an acronym for it. We'll end up encountering it. Anyway, this gal Winona really knows her stuff. And I mean she. She organizes defcon conference content and so forth. Anyway, with. She's with the Atlantic Council and addressed the question of what it will take for the US to be effective in offensive cyber war, that is. And she's got fantastic quotes from people on the inside who's who like say things like, you know, we could be effective if we weren't only not afraid to pull the trigger and. And things like that. Anyway, the, the. The. The context is US versus China, of course, like the big two tech superpowers and we know how much trouble we're getting from China and I'VE often opined on the podcast. Gee, I wish. You know, I hope we're given as good as we get. Anyway, we've got some great actual factual content here to share. So I titled Today's podcast number 1033. When I When I came home yesterday to Laurie, I said well, number 130, 1033. The mailing is on its way out. And she just kind of shook her head. She said 10:33. I said yeah, I know.
- [08:42]
Leo Laporte
Anyway, amazing.
- [08:44]
Steve Gibson
And I think we're approaching our 20th.
- [08:47]
Leo Laporte
Birthday here next month, right?
- [08:49]
Steve Gibson
Yeah. Wow.
- [08:51]
Leo Laporte
Anyway, we have to do something. We gotta get you a cake or something.
- [08:54]
Steve Gibson
Just gave me a little pointy hat. So I titled this one Going on the Offensive because that's what we're going to look at for the first time ever on this no 20 years into.
- [09:05]
Leo Laporte
This podcast, August 18th is the 20th.
- [09:08]
Steve Gibson
Nice. We have another Israeli spyware vendor surfacing. We've got the News of Windows 11 choosing to delete its restore points more quickly. Just a heads up in case anybody is worried about that or is like depending upon them sticking around the EU accelerating its plans to abandon Microsoft Azure. We briefly touched on that previously. Also they've set the EU has set a timeline for its post quantum crypto adoption so they're on that road now. Russia creating a massive IMEI database. What could possibly go I'm glad I'm not living there. Canada and the UK creating a common good cyber fund. The US cracking down on Bitcoin ATMs amid growing scams. We'll talk about congressional staffers no longer being allowed to use WhatsApp on government devices. Lib XML 2 is an open source software the sole maintainer very lonely I don't think he's in Nebraska but he's actually I think he's in Germany. Talks about the problems with and we will commercial use of open source software. Why that doesn't really work out well and seem fair. We've got another remote code execution vulnerability in Winrar have I Been Pwned has just got a very cool data visualization site. We look at Sophos analysis of how ransomware is getting into organizations Windows offering hopefully safe non kernel penetrating endpoint security and it looks like proactive age verification will be coming to porn and other sites near you maybe far from you if you use a vpn. We'll look at you know what what that means. Also Canada saying bye bye to Hick Vision Germany will be banishing Deep Seek the whole AU may be following and also has Russia throttled Cloudflare Anyway, lots of stuff to talk about before we get to what must the US do to compete in global exploit acquisition, which is what this all boils down to. And Leo, I know I've got a picture of the week that's going to. If you were still on your ball, it would knock you off the ball.
- [11:48]
Leo Laporte
Well, you'll see my reaction soon, Steve, after a word from our sponsor. It's going to be another great Security now episode, starting with a Picture of the week in moments. But first, a word from ExpressVPN. We talk about VPNs all the time on this show, and I know you know a VPN is a very vital tool in your toolbox, I have to say. It's the one I use. It's the only one I use. Going online without ExpressVPN, how can I?
- [12:18]
Steve Gibson
What?
- [12:19]
Leo Laporte
What's an analogy? It's like leaving your laptop unattended at the coffee shop while you run to the bathroom. You ever do that? Most of the time you're probably fine. But what if one day you come out of the bathroom and your laptop is gone? Right? Everyone needs ExpressVPN because every time you connect to an unencrypted network, whether it's in that coffee shop, a hotel, for me, airports, I'm always nervous when I see free SFO WI fi. I go, jeez, is that safe? Well, it isn't. Your online data is not secure on those open WI fi access points. Any hacker on the same network, and that could be anybody in the terminal or the hotel or the cafe, can gain access to and steal your personal data. In fact, it's easy. It doesn't take much technical knowledge to hack someone, just some cheap hardware widely available. And it's worth it, too. Your data is valuable. Hackers can make up to $1,000 per person selling personal info on the dark web. ExpressVPN stops hackers from stealing your data by creating a secure, encrypted tunnel between your device and the Internet. ExpressVPN is the one I use, and it's the best VPN. In fact, it's the only one I recommend because they're committed to keeping your privacy private. I use it when I travel, to keep up my shows, to watch football games. F1ExpressVPN is the best VPN because it's super secure. It would take a hacker with a supercomputer over a billion years to get past ExpressVPN's encryption. It's easy to use. You fire up the app, you click one button, you get protected. It works on all devices, phones, laptops, tablets and more. So you can stay secure on the go. Optional dedicated IP service engineered with innovative zero knowledge design. Not even ExpressVPN can trace an IP address back to the user. It's rated number one by Top Tech reviewers like CNET and the Verge. And it's the only one I use. Secure your online data today by visiting express vpn.com securitynow. That's E-X P-R-E-S-S vpn.com securitynow oh, and you can get an extra four months free when you buy a two year package. Expressvpn.com security now. All right, Steve, I am ready to scroll up, as they say.
- [14:35]
Steve Gibson
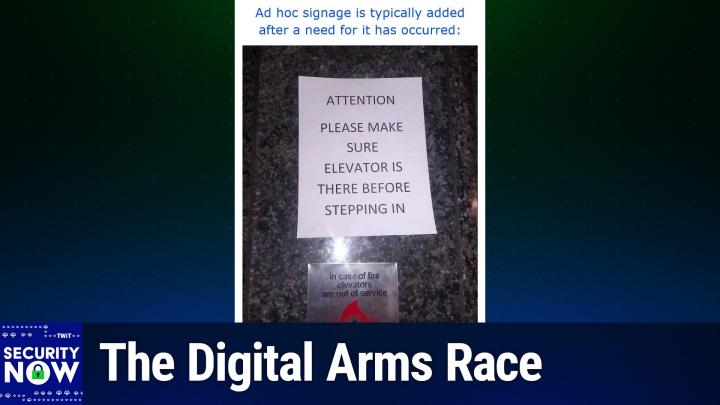
I gave this picture the caption. Ad Hoc signage is typically added after a need for it has occurred. Okay, Ad Hoc signage.
- [14:47]
Leo Laporte
All right, all right, I'm going to scroll up. All right.
- [14:49]
Steve Gibson
After a need for it has occurred.
- [14:56]
Leo Laporte
God, I hope not. I don't know what stimulated this one.
- [15:00]
Steve Gibson
Holy moly.
- [15:01]
Leo Laporte
All right, let me see if I can switch over the camera so everybody else can.
- [15:05]
Steve Gibson
So for those who do not have video, what we have is somebody having very deliberately printed on an 8 and a half by 11 sheet of paper and stuck it on the wall over the elevator call buttons. A sign, A very important sign. Yeah, it can be. Attention, please make sure elevator is there before stepping in.
- [15:33]
Leo Laporte
That's got to be a joke.
- [15:36]
Steve Gibson
It looks like it's there. It is on a marble wall. And you, you. And you can see the little in case of fire elevators are out of service warning below. So you have to wonder what situation occurred that that caused management to, to, you know, get up their word processor, set up, you know, 36 point font type and put a sign on the wall that warned people, make sure it's actually there when the doors open.
- [16:10]
Leo Laporte
Wow.
- [16:11]
Steve Gibson
One has to imagine that they opened at one point and there was no elevator present. So you know, it's there.
- [16:19]
Leo Laporte
Yikes.
- [16:21]
Steve Gibson
I don't know how else to explain this sign, but wow. Yeah. Okay, so I have no idea why all of the major commercial spyware publishers seem to be Israeli, but that's what we see, right? You know, it's apparent that that's the case and it's really not a good look for Israel. I mean, I've often felt sort of self conscious on their behalf because why? You know, Israel is the home of celebrate, which is that that famous iPhone unlocker, the NSO Group, which sells the Pegasus spyware and has been for years and still is A group called Quadream which has been formed from apparently from former ex NSO group members. They offer a spyware called Rain. We have Candiru, also known known as Sato Tech Ltd. But what brought this to the fore today was news of yet another Israeli commercial spyware vendor known as Paragon, which sells a smartphone penetration solution which they call graphite, I guess kind of. I don't know it like let's. It slicks the way in, it lets people into your phone. So this brings the total to five such companies, all Israeli that we currently know about. Well of course we don't know what we don't know, but there's five we do know. In mid June, the citizen lab groups, remember they're, they're the what a University of Toronto I, I believe is where they're located. They posted under the headline graphite caught. First forensic confirmation of Paragon's iOS mercenary spyware finds journalists targeted was what they said and they wrote. On April 29th, 2025, a select group of iOS users were notified by Apple that they were targeted with advanced spyware. Among the group were two journalists that consented for the technical analysis of their cases. The key findings from our forensic analysis of their devices, their physical phone devices, are first, our analysis finds forensic evidence confirming with high confidence that both a prominent European journalist who requested anonymity and an Italian journalist, Ciro Pellegrino, were targeted with Paragon's graphite mercenary spyware, they said. Second, we identify an indicator linking both cases to the same Paragon operator. Actually it's an IP address, as we'll see. And then third, Apple confirms to us that the zero click attack deployed in these cases was mitigated as of iOS 18-3-1 and has assigned the vulnerability CVE2025 43200, they said our analysis is ongoing, so some of the interesting revelations from their posting include they wrote, we analyzed Apple devices belonging to a prominent European journalist who is requested to remain anonymous. On 04-29-2025 this journalist received an Apple notification and sought technical assistance. Apparently our forensic analysis concluded that one of the journalists devices was compromised with Paragon's graphite spyware in January and early February 2025 while running iOS 18. We attribute the compromise to graphite with high confidence because logs on the device indicated that it made a series of requests to a server that during the same period matched Our published fingerprint P1. We linked this fingerprint to Paragon's graphite spyware with high confidence. Graphite spyware server contacted by the journalist's device was at 3184. The server appears to have been rented from VPS provider EDIS Global. The server remained online and continued to match fingerprint P1 until at least April 12th of 2025. We identified an imessage account present in the device logs around the same time as the phone was was communicating with the Paragon server at 46.183.184.91. We redact the account and refer to it as attacker1. Based on our forensic analysis we conclude that this account was used to deploy Paragon's graphite spyware using a sophisticated iMessage 0 click attack. We believe that this infection would not have been visible to the target. Apple confirms to us that the zero click attack deployed here was mitigated as of iOS 3-1-18 and has assigned CVE2025,43 200 to this zero day vulnerability. Now I want everybody to keep in mind we're talking about a zero day vulnerability that Apple did not know about that this group, this Paragon group used. Because at the end of this podcast we're going to be talking all about zero day vulnerabilities which is what it turns out everything today comes down to in the field of offensive cyber war. It's, it's zero days period, they wrote. Cyril Pellegrino is a journalist. This is another guy and head of the naples newsroom@fanpage.it where he has reported on numerous high profile cases. On April 29th, 2025 Mr. Pellegrino received an Apple notification and sought our technical assistance. We analyzed artifacts from Mr. Pellegrino's iPhone and determined with high confidence that it was targeted with Paragon's graphite spyware. Our analysis of the device's logs revealed the presence of the same attacker, one iMessage account used to target the journalist. From the first case, which we associate with a graphite zero click infection, it is standard for each customer of a mercenary spyware company. And, and it's interesting that they're using these terms. We'll see in a second where they got that term to have its own dedicated infrastructure. Again, it's standard for each customer of a mercenary spyware company. Right. So we're talking about that, that they used Paragon's, somebody used Paragon's spyware, purchased it from Paragon, set up an infrastructure where, which they then used with the spyware in order to do the spyware's business.
- [24:05]
Leo Laporte
I think it's often the case that the company you buy it from does the infrastructure. I know that's the case with Pegasus.
- [24:12]
Steve Gibson
Okay.
- [24:12]
Leo Laporte
They would that because they want to control the zero day.
- [24:15]
Steve Gibson
That is true. And we've talked about that in the past. They don't want just anybody letting this thing loose because this zero day is so vulnerable to them that they wanted to. They want to keep under control. So in this case, they're writing and maybe they know more than we do. They said it's. It is standard for each customer of a mercenary spiral company to have its own dedicated infrastructure. They said. Thus we believe that the attacker one account would be used exclusively by a single graphite customer or operator. Now that could again be a division of Paragon, as you say, Leo. They said and we conclude that this customer targeted both individuals. So a single person targeting both, that.
- [24:59]
Leo Laporte
Would make sense because you don't want your customers to interact with each other either. Right? They should all be on a separate channel.
- [25:06]
Steve Gibson
Now, can you explain to me why some journalist is worth this? I mean.
- [25:13]
Leo Laporte
Well, I mean, it depends what he's exposing. High profile cases. He's in Naples. Could be maybe he was writing about the mafia. I don't know. There's a lot of organized crime in Naples.
- [25:26]
Steve Gibson
Okay.
- [25:27]
Leo Laporte
Who knows? It was obviously it's just.
- [25:29]
Steve Gibson
To me it seems like, like usually.
- [25:32]
Leo Laporte
These are nation states, right? Using these.
- [25:34]
Steve Gibson
Yeah, yeah, yeah. But we off. We do often hear that activists and journalists and you know and do gooders of various ilk aren't the targets of these.
- [25:45]
Leo Laporte
It's not just spy versus spy.
- [25:48]
Steve Gibson
Yeah. Okay. So their use of the term. I thought mercenary was interesting. Turns out it's the official Apple term which Apple uses in their formal threat notifications when they are informing targeted individuals. I have a screenshot of their redacted Apple notification which these journalists received and it says, you know, it's got the. The little WI fi antenna at the top and it's very clear. Threat notification, you know, is make sure the elevator is there before you. No threat notification. And it's dated 290425 at 1403 and it says alert in all caps. Apple detected a targeted mercenary spyware attack against your iPhone. Apple sent the following threat notification via email to which they've redacted and via imessage to which they redacted. We also sent a short notification to the recovery addresses associated with your account. So these guys identified a total of seven Italians who've received. And they're to your point, Leo, apparently they're frisky Italians who. Who've received notifications either from Apple or WhatsApp. So this paragon group is definitely now on the map and active as another source of is, you know, Israeli spyware.
- [27:26]
Leo Laporte
Well now you may. Now I may be thinking it's the Italian government, right?
- [27:30]
Steve Gibson
Ah, okay.
- [27:31]
Leo Laporte
Yeah. They might have been writing exposes on the corrupt Italian government.
- [27:38]
Steve Gibson
Wow. Okay. Then a few weeks later, the publication Security Week wrote. Meta owned WhatsApp told Security Week that a recent free type vulnerability, flagged as potentially exploited at the time of disclosure, has been linked to an exploit of Israeli surveillance solutions provider Paragon. So now they're calling Paragon an Israeli surveillance solution in mid March because that's what they are.
- [28:13]
Leo Laporte
Yeah, that's calling. That's naming it as it is.
- [28:15]
Steve Gibson
Yeah, that's right. If you could pay the price, you get to surveil pretty much anybody you want to, they wrote. In mid March, Meta published an advisory on the Facebook Security Advisories page to inform users about this is a CVE 2025 different 127363, an out of bounds vulnerability in the Free Type open source library that could lead to arbitrary code execution. The advisory said the vulnerability may have been exploited in the wild. Meta knew this because the University of Toronto. That's what I was remembering. Citizens Lab Research Group reported that a WhatsApp zero day vulnerability had indeed been exploited in paragon spyware attacks. WhatsApp representatives at the time told Security Week that the zero day attacks involved the use of groups and sending PDF files and that the weakness had been patched on the server side without the need for a client side fix. And that's kind of cool to be able to like fix it so that you're not. So WhatsApp is no longer going to send a. Will no longer send a PDF that exploits a vulnerability in the client's use of of Free type fonts when it renders that page. So Security Week explains Free Type is a development library designed for rendering text onto bitmaps and provides support for other font related operations. In the case of CVE 2025 27363, which is the one that was exploited here, which impacts free type 2.13.0 and earlier, meta said the issue is triggered when attempting to parse font sub glyph structures related to True type GX and variable font files.
- [30:15]
Leo Laporte
It's those damn interpreters again every time.
- [30:18]
Steve Gibson
Right baby, it's hard. It's so hard to get those right. You're right. Every time. Meta's advisory explains the vulnerability. Code assigns. I'm sorry, the vulnerable code. Get this, Assigns a signed short value to an unsigned long and then adds a static value, causing it to wrap around and allocate an undersized heap buffer. The code then writes up to six signed long integers out of bounds relative to this buffer, which can permit the execution of arbitrary code.
- [31:05]
Leo Laporte
It's a buffer overflow, baby, the way it happens.
- [31:07]
Steve Gibson
Yep. Citizen Lab wrote that Paragon is known for developing sophisticated exploits that do not require a. Any interaction from the targeted user. Right. So they just. They send your phone an imessage or. Or they. They send you a WhatsApp PDF and you don't have to do anything.
- [31:28]
Leo Laporte
0 your end. Yeah.
- [31:30]
Steve Gibson
0. Click and your phone is compromised.
- [31:33]
Leo Laporte
Unbelievable.
- [31:34]
Steve Gibson
They found indications that the company was until recently able to hack up to date iPhones, and that their spyware has been used in countries including Australia, Canada, Denmark, Italy, Cyprus, Singapore and Israel.
- [31:49]
Leo Laporte
So Pellegrino, the journalist who this attacked, was also. His editor in chief, was also attacked with the same spyware. The newspaper they work for is known for its investigative journalism critical of the Italian government, including exposing connections between the youth ring of Prime Minister Giorgia Meloni's party and neo Nazi activities. The Italian government denied ordering the surveillance of the journalists, although the head of Italian intelligence said, yeah, well, we use Paragon spyware, but merely to monitor migrant rights activists. So I think it's pretty safe to say, you know, this is why they were targeted. They were investigating the government. And by the way, these companies like Paragon and Pegasus only they say, well, we only sell to responsible governments not known for their human rights violations, like Italy, maybe. Unbelievable.
- [32:53]
Steve Gibson
Well, and. And again, like, are they. Are they. Did they want to get dirt on these guys so they blackmail them into silence? I mean, I just don't. I'd like. I. I guess I don't understand what having your phone hacked by the government because you're like, are they going to delete your article before you publish it? I. I just.
- [33:13]
Leo Laporte
Pellegrino says his phone contains sensitive personal data, medical records, and confidential journalistic sources. That's what they're going after.
- [33:21]
Steve Gibson
Okay, that's. That's. Yes, because protecting your sources is your lifeblood for a journalist. Right. And so if you can't do that, no one's going to talk to you.
- [33:31]
Leo Laporte
And every government feels justified in saying, well, we're just trying to track down these leaks. We don't. We don't want any leaks. So. And the journalist is never going to.
- [33:40]
Steve Gibson
Say, well, we saw our own government go ape a few months ago. When, when, when, when, when, when, when, when Someone questioned whether, you know, the bombing of, of the, the Iranian nuclear facilities was, you know, as devastating as it was initially claimed. Somehow, you know, someone said it wasn't, it was like, oh, we gotta find that guy.
- [34:07]
Leo Laporte
So I would be shocked, shocked if the intell u S Intelligence agencies don't also use Paragon spyware. Well, we're, I'm sure a customer.
- [34:17]
Steve Gibson
Yeah, I think probably all five of the, we're probably buying it from all, all the companies.
- [34:22]
Leo Laporte
And so, you know, God bless Apple for patching these every time they've, they find them and for setting those alerts out. That's huge. Right?
- [34:31]
Steve Gibson
Well, and this is that lockdown mode which is not fun to use because suddenly it's, you know, you don't get balloons exploding on your birthday and all this random knobs.
- [34:44]
Leo Laporte
But is lockdown mode sufficient to stop these zero click attacks? I don't know.
- [34:50]
Steve Gibson
It does what it can. Wow. Yeah. Unbelievable the world we live in today. Leo, let's take a break and then we're going to talk about. I have got a bunch of little quickie bits of news that I think everyone's going to find interesting.
- [35:03]
Leo Laporte
I'm always up for a quickie. Let's, let's talk about bits of news, news, news. Did I say I meant that?
- [35:11]
Steve Gibson
Yeah, I did say a little bit.
- [35:14]
Leo Laporte
Our show today, brought to you by Melissa, the trusted data quality Expert, expert since 1985. We love Melissa. Melissa's address validation app. This is. Oh, this is cool. So if you use Shopify, their address validation app is available for merchants. It's in the Shopify app store. All right. Which means you can enhance your business's fulfillment and of course keep customers happy using Melissa. Why? Well, Melissa offers enhanced address correction so you can cleanse data, you can fix data. You can even fix data as your customer is entering it to make sure those bad addresses don't get it in your database in the first place. And Melissa standardizes addresses in more than 240, 240 countries and territories. Melissa will add missing components, postal codes, for instance, and ensure compliance with local formatting rules. They know them all in every country. Melissa's address engine is certified by leading postal authorities worldwide. Oh, and I love this. The smart alerts will warn in real time if there's a potential issue with a shipping address. So the customer sees that it pops up saying, you know, is that, did you, did you get that right? And the customer can then, before the order's even processed, update that information so that, that is going to be deliverable so you don't send stuff into, you know, thin air. Now a business of any size benefit of course from Melissa and they offer price points for every size business. But their data quality expertise goes a lot deeper, farther than just data validation. There's data cleansing and validation and they and fields like health care, for instance, your physicians, your hospitals, 2 to 4% of the contact data they have becomes outdated every month. Millions of patient records in motion demand precision, which only Melissa can deliver. Slight variations in addresses or misspelled names can cause duplication and fragmentation errors as well. As in the healthcare industry, you don't want misidentification or lost records. Data inconsistencies can delay treatments, introduce errors in care delivery, complicate the billing process. You know, this is a pretty important area. Melissa's data enrichment services remove that gap. By using Melissa's enrichment as part of their data management strategy, healthcare organizations build a more comprehensive view of each patient which supports continuity of care, timely follow up, make sure the right medications go in the right bottle to the right person and all of that. This approach also aids in predictive analytics, allowing providers to identify patterns. This is really cool. And patient behavior or medical needs that can inform preventative care. Now of course with hipaa, it's very important, but in many businesses, in almost every business, data privacy and security is paramount. Don't worry, data is safe, compliant, completely secure with Melissa. Melissa's solutions and services are GDPR and CCPA compliant. They're ISO 27001 certified, they meet SOC2 and yes, HIPAA high trust standards for information security management. Get started today with 1,000 records cleaned for free. Melissa.comTwit for more information, that's Melissa.comTwit thank you Melissa for support and security now and Steve's important work here. All right Steve, now let's get some quickies.
- [38:47]
Steve Gibson
So just in case anyone listening might have some reason to depend upon their Windows 11 system restore points enduring for their traditional 90 days. I wanted to note that Microsoft's most recent Update to the 24H2 edition of Windows 11 has deliberately reduced restore point life to 60 days. I doubt anyone will care, but I thought it was just worth noting. I saw that pass by, you know, it cuts it off by 50% or by, by a third. That's significant. Yeah, I don't know. Yeah, it is. And so if you were like depending upon a 90 day lifetime before you were like, okay, then we're going to restore this and then you look and it's gone. Now you'll know why? Or maybe get to it before it disappears. I don't know if they're wishing to save space on users machines or tightening security because they figure well we don't, you know, no one really uses them after 60 days. And so it's just a more of a security problem, you know or, or what you know. But there it is. So if you're up with the latest Windows 11 and you routinely use restore points now, you'll need to do so within 60 days otherwise windows is going to clean them off for you. I noted last week when talking about the French city of Leon which I listener corrected me it's not which is working to move from away from Microsoft solutions to Linux and other open source alternatives that also the entire European Union is also working to eliminate their dependency upon Microsoft Azure for cloud services. Since then it's come to light that they're looking that they're all almost, they've almost closed the deal with the French company OVH Cloud. They're now in what's considered advanced talks to, you know, dot the eyes. The reporting about this indicated that a little more urgency had been put on the EU's need for increased sovereignty and its distance and dependence upon US solutions after the US administration imposed sanctions on four judges of the International Criminal Court in early June, so early a month ago. One result of those sanctions was that those judges had their Microsoft accounts closed just bang sorry, goodbye. So the EU will be working to provide alternative services that are no longer subject to the prevailing policies and politics of the us. And so, you know, that's probably for the better for the eu. They want to be more independent and so they're going to work out how to do that. Also on the eu, they've published their post quantum cryptography roadmap. This instructs EU member states that they need to begin transitioning all of their systems everywhere to post quantum crypto by the end of 2027. For all high risk systems such as critical infrastructure, this transition should be finished by the end of 2030. So essentially, you know, four and a half years from now, anything considered high risk critical infrastructure can no longer be solely dependent upon pre quantum crypto. You could do things like signal did where you use a hybrid which is, you know, belt and suspenders. Why not have both a pre and a post crypto and and require that both be useful so that if either are broken you're still able to rely on the other anyway. For the less mission critical systems another five years are available. States should have finished the migration of as many systems as feasible is the way it was put by the end of 2035. So nine and a half years from now, here we are mid 2025 for non mission critical, you know, non critical infrastructure and four and a half years before in with all EU member states have to no longer solely depend upon pre quantum crypto. And overall, you know, this, this entire pre and post quantum crypto move in my opinion has been handled with remarkable planning and grace. You know, we have the new algorithms which continue to be trusted tested and stress tested and now they're being rolled out. We've already found some problems early on with a couple and they, they've been strengthened or in some cases abandoned. Academia has had plenty of time to pound on them and, and vet them. We're, and we're, you know, we're all seeing our own protocols are beginning to adopt them. We've updated the underlying protocols like tls, for example, to be able to smoothly accommodate the evolution, the retirement and the introduction of anything new that may be required today. And going forward, you know, all indications are that just as we, I'm sorry, just as we're present during the original design and birth of the Internet, it feels like a bunch of very smart people got together to carefully define and establish these next steps in the evolution of the world's networking and security. And I mean it just, it's just gone beautifully. Now of course this all gets spoiled if someone has some massive quantum computing breakthrough immediately. But I think what we're up to factoring was it we're a ways off seven bit numbers. Yeah. So we're safe because we got to get to 4, 4096 before we start.
- [45:10]
Leo Laporte
Having, well, I don't know, IBM and Microsoft both think they're getting close. So.
- [45:15]
Steve Gibson
Although yes. And these things can tend to go exponential. So but anyway, I just, I, I'm just as you stand back and you look at this, this has just been like somewhere amid all the chaos that we typically see in our industry where we're talking about, you know, Cisco having monthly 9.8 and 10.0, you know, remote execution vulnerabilities and just this catastrophe of being unable to get salt typhoon out of our systems. And all the while there are good people just calmly saying okay, here's here are, you know, lattice based crypto that won't be, you know, that won't rely on the factoring problem. So that's probably not going to be, you know, collapsing in, in the face of quantum computing. And so here's how we do that and here's the timeline and, and we need to update our underlying protocols in order to be able to smoothly, you know, begin using these without having any, and you know, any interruption at any point. All of this is happening and it's just like, you know, somewhere there are adults who are.
- [46:27]
Leo Laporte
Somewhere. Yeah.
- [46:29]
Steve Gibson
I don't know where, but you know, they're doing a good job.
- [46:32]
Leo Laporte
Yeah, it's great.
- [46:34]
Steve Gibson
That old challenge, remember, of why do you care about privacy? You have nothing to hide. It's receiving a stress test in Russia with the government's recent announcement of their plan to create a single national database of IMEI numbers. Oh, wow, talk about big brother. The Russian Ministry of Digital affairs says the database will be used. This is of course the way it starts, right? To combat financial fraud. Batting Banning IMEI codes will allow authorities to block individual devices from mobile networks even after fraudsters change phone numbers. Of course, that's the story. Just as you were saying, Leo. Governments talk about their use of, of surveillance only for, you know, only legitimate instances. Yeah, yeah. And then journalists are, you know, who you would think have rights to privacy have this crap on their phones. As we know, the IMEI numbers indelibly identify physical mobile phone handsets. You know, they are the approximate equivalent of the globally unique Mac addresses that are assigned to every Ethernet NIC to identify and differentiate it from any other. But IMEI numbers must be known to the users to service providing carrier since they're what identifies the mobile device handset to the cellular network. This means that they're never really secret or private. But needing to subpoena individual carriers on a per subscriber basis would be far less convenient than simply requiring every carrier to provide an exhaustive dump of their entire current subscriber IMEI database and then require them to notify the Russian Ministry of Digital affairs of any changes to that data over time. And as I said, I'm happy to be in the U.S. i think. Yeah, you know, wow. Talk about overreach. On June 23, the UK and Canada announced their establishment and initial funding of under the heading New Common Good Cyber Fund launches to strengthen Internet security globally. And we need more of this. Their announcement said the Internet Society, ISOC and Global Cyber Alliance. The GCA on behalf of the Common Good Cyber Secretariat today announced the launch of the Common Good Cyber Fund, an initiative to strengthen global cybersecurity by supporting non profits that deliver core cybersecurity services that protect civil society actors at high risk and the Internet as a whole. This first of its kind effort to fund Cybersecurity for the common good for everyone, including those at the greatest risk of intimidation, harassment, harm and coercion, has the potential to fundamentally improve cybersecurity for billions of people around the world. The Common Good Cyber Secretariat members working to address this challenge are the Global, the Global Cyber alliance, the Cyber Threat alliance, the Cyberpeace Institute for the Forum of Incident Response and Security Teams, Global Forum on Cyber Expertise, Institute for Security and Technology and the Shadow Server Foundation. In other words, a whole bunch of non profit organizations that are, you know, the good guys. Sort of the same people who brought you post quantum crypto in the right way, who are just quietly doing the right thing for everyone. In the background. In a joint statement between the Prime Minister of the United Kingdom and the Prime Minister of Canada was on 15 June, the Prime Ministers announced that they would both invest in the joint Canada UK Common Good Cyber Fund. And I think it's the tune of five point. Oh, it's $5.7 million. They're, they're initially funding June 7th.
- [51:00]
Leo Laporte
Just a million. What are they, cheapskates?
- [51:02]
Steve Gibson
Well, it's just the beginning.
- [51:04]
Leo Laporte
Okay.
- [51:05]
Steve Gibson
On June 17th. And you know, and these are lean organizations that they're not big, you know, money.
- [51:11]
Leo Laporte
I'm so used to billions. Now everything's billions. That millions sounds like chicken feed.
- [51:17]
Steve Gibson
Yeah, I agree. I was surprised. On June 17th during the G7 leaders summit in Alberta, Canada, all the G7 leaders announced they would support initiatives like the Canada UK Common Good Cyber Fund to aid members of civil society who are actively working to counter the threat of transnational repression. Despite serving as a critical frontline defense for the security of the Internet, nonprofits working in cybersecurity remain severely underfunded, exposing millions of users, including journalists, human rights defenders and other civil society groups, to heightened risks of digital transnational repression involving the misuse of cyber capabilities to conduct surveillance, track individuals and facilitate physical targeting. This underfunding also leaves the wider public exposed to increasingly frequent and sophisticated cyber threats. Philip Rettner, the President and CEO of the Global Cyber alliance, said Common Good Cyber represents a pivotal step toward a stronger, more inclusive cybersecurity ecosystem by increasing the resilience and long term sustainability of non profits working in cybersecurity. Improving access to trusted services for civil society organizations and human rights defenders and encouraging greater adoption of best practices and security. Oh my God. Security by design principles. Please, maybe talk Cisco. Give Cisco a call. My God. The Common Good Cyber Fund ultimately helps to protect and empower all Internet users. So the fund will support Nonprofits that, for example, maintain and secure core digital infrastructure, including DNS, routing and threat intelligence systems for the public good. Like somebody is maintaining all of the root servers, right? Not all of those are being run by big organizations. So they need money and they need, for example, help with DDoS attacks, which the bad guys are doing. Also deliver cybersecurity assistance to high risk actors through training, rapid incident response, and free to use tools and give Cisco a call. The announcement indicated that the fund would initially receive $5.7 million to support these efforts. So this is great. You know, the world has become utterly dependent upon a sophisticated system that just sort of known as the Internet, that just sort of blossomed organically. It needs support. So this will be very welcome. And bravo to the UK and Canada for leading this. I hope that the US is ready or planning to step in and, and toss in some money. We can certainly afford a few million because as you said, Leo, this is not wasting a lot of funds.
- [54:25]
Leo Laporte
No, it's very, it's very economical, really.
- [54:28]
Steve Gibson
Arms. Yes.
- [54:29]
Leo Laporte
Yeah.
- [54:33]
Steve Gibson
Axios had some good coverage describing recent US state regulations being enacted. I thought this was really interesting. In response to the rise of crypto ATMs, and not surprisingly, unfortunately, the high level of abuse thereof. So here's what we learn. Axio said states across the US are rolling out tough new laws that cap deposits and tighten oversight on cryptocurrency ATMs, seeking to cut off a favorite tool of scammers and extortionists. You could just see like, you know, some scammer or extortionist telling, you know, gramps to, you know, go to the crypto ATM and put your money in there and then put in this code and, you know, we won't out you to the world or whatever. Anyway, these crypto ATMs, they write kiosks, are the easiest way for ordinary people to turn cash into crypto. And their use by fraudsters has surged to no one's surprise over the last few years, especially with scams targeting older Americans. What? Crypto? What's. What's that? Where do I get crypto? Well, you just go to this atm. These are popular tools, they write of scammers, because cryptocurrency provides criminals with a way to receive money that a third party cannot roll back. These kiosks have popped up all over the country. And over the last few years, scammers have increasingly utilized them in all manners of schemes. And Leo, wait till you hear why they popped up. Oh, boy, they're making the, the poppers some money here.
- [56:24]
Leo Laporte
Oh, boy. Oh, boy.
- [56:25]
Steve Gibson
Yeah. Axios wrote. Last September, the FTC reported that fraud losses specifically involving crypto kiosks jumped nearly 10x from 2020 to 2023. The FBI reported $247 million in losses. Okay, so a quarter billion dollars. Why can't the. The Cyber Do Gooder guys get that money? That would be some money. Instead of, you know, 5.7 million, let's give them. The crypto kiosk lost 2,247 million dollars. Wow. In losses tied to the kiosks in 2024, with a 99% increase in complaints from the year before. I put my money in and nothing came out. Yeah, that's right. Schemes have particularly impacted older Americans. Both the FTC and the FBI warn people 60 and over were more than three times as likely as younger adults to report a loss using a crypto kiosk. States taking action include Illinois. The state legislature sent a bill to Governor J.B. pritzker in early June, who had called for legislation to address the issue earlier in the year. Among other things, the law would require crypto ATM operators to include details on every receipt, such as the blockchain address where funds were sent. That would help law enforcement with any future fraud investigation. Other states have taken similar actions. Vermont passed a law in May. One thing it does is put a daily limit on usage for these machines to throttle how much criminals can gouge their victims. Nebraska stamped a new law in March that establishes a licensing system for crypto ATM operators. Nebraska has been eager to bring crypto business to the state, but they want it to be under license. Arizona, which also enacted a Bitcoin reserve fund, established a law in May that requires funds on fraudulently induced transactions. I'm sorry. That requires refunds on fraudulently induced transactions. A new Oklahoma law, which survived a veto by the state's government. I guess he tried to say no. Will go into effect on November 1, establishing similar protections. And Rhode Island's governor signed a new law last Monday. In addition to enacting similar measures as other states, Rhode Island's law requires, and I love this, a warning about the irreversibility of cryptocurrency transactions. To be clearly posted on the kiosk. Right. Like, don't go into the elevator until you check that there's a floor there. Yeah. So, yeah, make it. Put it like, you know, I've always said that, that, that, that enterprises that have problems with employees not understanding that their use of the company computer is not private just need to post a Sign across the top of the monitor. You know, this is our computer, our network, our bandwidth. What you do is ours too. And like, who can complain? So yeah, signage on the kiosk, that's like when you put your money in the week it's gone. So be careful. Axio said cities have also homed in on the issue. On June 16, the City of Spokane, Washington voted to ban. Okay, so they're just going to get rid of them. Ban all crypto kiosks. No crypto for you. And they've been a topic in Minnesota cities including St. Paul, Stillwater and Forest Lake. So this is an issue. Much of this legislation they, they wrote has been at the urging of the aarp, of course, the well known American association of Retired People who've been after me for quite a while, Leo. They want to get me to join.
- [60:46]
Leo Laporte
You're not retired. I hate to tell them.
- [60:48]
Steve Gibson
That's right. I'm not done yet. Which has been urging state legislators to pass these bills. The AARP says they've endorsed 12 bills that have passed in different states so far. Because you know those old people, we vote. So pay attention to the double arp. It came as a, as a. Oh. What came as a surprise to me, Leo, was that there is a high fee for the use of these services. As I said, there's a reason all these kiosks are popping up all over.
- [61:23]
Leo Laporte
They're not pay for all that hardware.
- [61:25]
Steve Gibson
They're not exactly. And, and presumably they're. That's what's going to pay the fines for when, when complaints are, are, are, are, are filed against these things. So they're going to have to take some responsibility for who's on the other end of these transactions. One crypto ATM provider, Bitcoin Depot reported. That's right, Bitcoin Depot, which is right.
- [61:50]
Leo Laporte
Next door to Repo Depot. So that's good.
- [61:53]
Steve Gibson
Reported an operating profit margin of, of 20%. So they're making 20% on the, on the money. Generating $33 million in profits for the first, just for the first quarter.
- [62:07]
Leo Laporte
I need to get me a kiosk of this year.
- [62:11]
Steve Gibson
Wow. Yeah. Yeah. Just, just don't cash the money that you make. You may be giving it back if, if, if the state that you're in requires that you license and stand behind your transactions.
- [62:24]
Leo Laporte
So I think, do you even get bitcoin? What do they give you like a little wooden nickel or.
- [62:31]
Steve Gibson
It's a good question. It did say that the receipt you get must indicate the bitcoin address that it was put On.
- [62:41]
Leo Laporte
Okay, so they give you a wallet. Basically, yes.
- [62:43]
Steve Gibson
So I think what's happening is it's creating a wallet. You get back the bitcoin address. So, so when, when some scammer says you need to pay for this in bitcoin, what's your address? Well, and, and, and, and you say I don't know what that is. They say, well go to Bitcoin Depot and put your money in there. That will give you, that will give you Bitcoin. And then you come back and you put that in to our web page and then we're going to send you your auto warming socks which you know are going to solve the problem that.
- [63:27]
Leo Laporte
You got with no more cold feet. Cold feet, that's right. Yeah, yeah, yeah.
- [63:32]
Steve Gibson
So anyway, we live in a country where, you know, individuals w wish to preserve as much of their freedom and privacy as possible. So this seems like a tough problem. You know, I, I like more than anything the signage that says all transactions are final. You know, no money ever comes out of this thing. It only goes in and so you know, you're not getting your money back.
- [64:04]
Leo Laporte
No money ever comes out of this thing. It's a roach motel for money.
- [64:10]
Steve Gibson
That's right. Wow. Bitcoin Depot. It ought to be Bitcoin black hole. Yeah. Okay, so one more little bit of news and we'll take another break. It occurs to me that the way to improve an app security is to widely and publicly ban its use due to exactly its demonstrated lack of security. So to that end, the U.S. house Chief Administrative Officer recently informed all congressional staffers that the messaging app we all know of as WhatsApp is now banned on all their government devices. The ban centers on the vulnerability of staffers data at rest. And it comes as Congress is also taking steps to limit the use of AI programs which it deems similarly risky. In recent years the Chief Administrative officer has set at least partial bans on. On. I have Deep Seek. Is that what I mean? Deep Seek.
- [65:22]
Leo Laporte
Yeah, that's the, that's the Chinese.
- [65:24]
Steve Gibson
The Chinese. Much faster. Yeah. Also ByteDances apps of course, TikTok famously and Microsoft copilot. Whoops.
- [65:32]
Leo Laporte
What? How'd that get in there?
- [65:36]
Steve Gibson
It is also heavily. Someone told them that it's just going to store everything you ever do. And, and very much like the Bitcoin Depot, your data goes in and it never comes out. It's also heavily restricted staffers use of chat GPT instructing offices to only use the paid version chat GPT plus which.
- [65:58]
Leo Laporte
Okay, anyway, that's more Private, but now they have your name, address.
- [66:04]
Steve Gibson
These people have no clue what they're doing. But anyway, the Congressional affairs office wrote in an email, quote, the Office of CyberSecurity has deemed WhatsApp a high risk to users due to the lack of transparency in how it protects user data.
- [66:22]
Leo Laporte
I really wanted to ask you about this.
- [66:25]
Steve Gibson
Sounds like what's his face piss somebody off.
- [66:28]
Leo Laporte
Oh, Mark Zuckerberg. I don't think WhatsApp's doing anything different than, for instance, Apple messages.
- [66:35]
Steve Gibson
Well, WhatsApp is Signal.
- [66:37]
Leo Laporte
Right. But. So here's the problem with WhatsApp that we know because it happened to Corey Lewandowski, is that if you back up WhatsApp, it backs up the app, the data in the clear. So. And so it would go up to icloud account. Yep. And then there was a subpoena and they got it from the icloud account. But that's true of a lot of messaging apps, including the one they recommended. Apple's messages.
- [67:01]
Steve Gibson
We know it's true of imessage unless you turn on advanced data protection.
- [67:05]
Leo Laporte
Right, so they're recommending something that does the same thing.
- [67:10]
Steve Gibson
Yes, it's. So the issue is reportedly WhatsApp's lack of on device encryption, which is exactly what you're saying, that, that the, the data on the device is in the clear, not kept encrypted by the app. It's in the clear and then subject to backup and subpoena.
- [67:30]
Leo Laporte
So is, is that an unusual behavior? I mean, I thought that was the problem is if somebody has access to your phone, they have access to your messaging, no matter what you do in transit. Yeah, I, I just.
- [67:47]
Steve Gibson
Could. Yeah, yeah. Oh, yeah. On the phone it is stored encrypted. And, and so it's not in, it's not in the clear. I mean, on the iPhone is so locked down, you know, it's all, it's all in. You know, it, it, it, it encrypts it on the fly in the, in the pipe to the drive.
- [68:05]
Leo Laporte
Right.
- [68:05]
Steve Gibson
And then decrypts it on the fly on the way out.
- [68:08]
Leo Laporte
Right.
- [68:08]
Steve Gibson
So, so Apple has to, I mean, Apple does have a key that encrypts people's icloud data. But, but, but that, but the point is they have the key when, when you.
- [68:20]
Leo Laporte
Same for. The same for WhatsApp.
- [68:22]
Steve Gibson
Yeah. Although maybe WhatsApp is not encrypting on the device. The, the reporting said that it is, it has, does not have on device encrypted. And this, the cao, the Congressional Affairs Office said that Microsoft Teams wicker signal iMessage and FaceTime are acceptable alternatives to.
- [68:42]
Leo Laporte
WhatsApp, but I don't know if they're doing anything differently.
- [68:45]
Steve Gibson
Yeah, I mean, I don't know.
- [68:47]
Leo Laporte
You.
- [68:48]
Steve Gibson
It would have to take. You have to do. Have to have someone take a look at it forensically and see.
- [68:51]
Leo Laporte
And again, because Apple's not telling, and.
- [68:54]
Steve Gibson
As I said, if. If in fact WhatsApp is not doing it, then they should, you know, and.
- [69:02]
Leo Laporte
I can tell you for sure that Apple is. I mean, if I can see the messages on the screen at some point, they're unencrypted on the device.
- [69:11]
Steve Gibson
Yes. Well, but we don't know if they're unencrypted, stored on the device, or when displayed. But we know that. We know.
- [69:21]
Leo Laporte
But I could scroll through old messages and they're all there. You think it's unencrypting them on the fly?
- [69:26]
Steve Gibson
Sure, could. Absolutely. Could be.
- [69:27]
Leo Laporte
Okay.
- [69:28]
Steve Gibson
Yeah. Yeah. So just. Just to finish this, to, To. To share the other side of this. Andy Stone, a spokesperson for Meta, said in a statement to Axios, who. Who covered this story, quote, we disagree with the House Chief Administrative Officers characterization in the strongest possible terms. We know members and their staffs regularly use WhatsApp, and we look forward to ensuring members of the House can join their Senate counterparts in doing so. Officially, messages on WhatsApp are end to end, encrypted by default. We know that because they're using the signal protocol, meaning only the recipients and not even WhatsApp can see them. But that doesn't address the issue. He says this is a higher level of security than most of the apps on the CAO's approved list that do not offer that protection. So.
- [70:24]
Leo Laporte
So Apple says that your messages are encrypted until you enter in your code, till the device is unlocked. Unlocking the device is the process of.
- [70:35]
Steve Gibson
Unencrypted and backing your Device up to iCloud.
- [70:39]
Leo Laporte
Right, we know, but then they have the keys, right? Yeah. Right. Okay. So maybe it is. Maybe. Okay, maybe WhatsApp is less safe.
- [70:50]
Steve Gibson
You know, early in our password manager days, there were issues with password managers that we were, you know, like. I don't even remember them. Like, ones we never recognized.
- [71:00]
Leo Laporte
Long gone. Now. Steve.
- [71:01]
Steve Gibson
Yeah, Where. Where they, you know, like, somebody would discover the file and there was all your passwords. It's like. Wait a minute. You're telling me you're not keeping this encrypted on. No. We decrypt it on your system when you log in. Exactly. And then we re. Encrypt it when it's like, wait a minute, that's not safe.
- [71:21]
Leo Laporte
But nowadays machines are so fast that you can decrypt and encrypt on the.
- [71:25]
Steve Gibson
Fly or incrementally decrypt individual entries.
- [71:28]
Leo Laporte
Right?
- [71:29]
Steve Gibson
Right. Yeah. Okay, great time then. We've got an interesting story about the collision of commercial use of open source software and remembering xKCD's famous cartoon of the lonely guy in Nebraska.
- [71:46]
Leo Laporte
Right, Right. Incidentally, you are not freezing. I don't, I don't know if anybody's seen a phrase, but I haven't seen a freeze. So that's good news.
- [71:56]
Steve Gibson
Yes. That means a restart of the cable modem did the trick.
- [71:59]
Leo Laporte
Yeah, that or maybe it just was freezing at the beginning and then once it got settled in, I don't know. We don't know. We don't know.
- [72:05]
Steve Gibson
Okay. Happiness.
- [72:06]
Leo Laporte
Knock on wood.
- [72:07]
Steve Gibson
Yay. I don't have any. I Formica. I have.
- [72:11]
Leo Laporte
All I have is Formica. What's wood? What's wood, daddy? Well, there used to be this thing called trees.
- [72:19]
Steve Gibson
They had a grain, they were green.
- [72:22]
Leo Laporte
Ladies and gentlemen, our show today brought to you by 1Password over. This doesn't surprise me, but it's a scary stat. Over 1/2 of IT pros say their biggest challenge, their biggest challenge is securing SaaS apps. With the growing problems of SaaS sprawl and shadow it, I mean, let's face it, people are not just using the SaaS apps you approve, but whatever they, whatever the heck they want to, it's not hard to see why this is a problem. Thankfully, there's Trelica by one Password. Trelica can discover and secure access to to all your apps, managed or not. Nice. Trelica by 1Password inventories every app in use at your company, even shadow IT apps. Then pre populated app profiles assess SaaS risks, letting you manage access, optimize, spend and enforce security best practices across every app your employees use. Which means now you can manage shadow it. It means it's easy to securely onboard and offboard employees and meets your compliance goals. Trellica by1Password provides a complete solution for SaaS access governance. And it's just one of the ways that extended access management helps teams strengthen compliance and security. 1Password's award winning password manager is trusted by millions of users, over 150,000 businesses from IBM to Slack. And now they're securing more than just passwords with 1Password Extended Access Management. 1Password is ISO 27001 certified with regular third party audits and the industry's largest bug Bounty. We know how important that is. We talk about that all the time. 1Password exceeds the standards set by various authorities and is a leader in security. So take the first step to better security for your team by securing credentials and protecting every application, even on managed shadow it. Learn more@1Password.com Security now that's 1Password.com SecurityNow do it in all in lowercase. Okay. 1Password.com SecurityNow we thank him so much for supporting security now. And Mr. Steven Tiberius Gibson, did you ever think about where does shadow it? Where does that name come from? I mean, I know what it is. I mean it's unmanaged apps, but I, I just don't. Yeah, like what is it? It's.
- [74:58]
Steve Gibson
I think it's just a made up name. Just.
- [75:00]
Leo Laporte
Well, obviously somebody made it up. All right, I'm just curious. Somebody. Somebody will write you and explain the or.
- [75:07]
Steve Gibson
Okay.
- [75:08]
Leo Laporte
Yes.
- [75:08]
Steve Gibson
Yes, you're right, they will. We will have a listener who will go Steve. Well, as a matter of fact, I.
- [75:14]
Leo Laporte
Was there.
- [75:17]
Steve Gibson
So I was somewhat distressed to hear what was on the mind of a German developer and the maintainer of the open source Lib or Lib. But I like saying lib.
- [75:30]
Leo Laporte
You say live man. It's okay. Nobody's ever told us how to pronounce it.
- [75:34]
Steve Gibson
Library, not library XML 2. Okay, so lib XML 2. And I guess what put a point on it for me was learning that this library is being used by Mac os, Windows and Linux. And of course, when we hear about a loan maintainer of a library that's being used by all top three of the industry's operating systems, and thus indirectly by anyone using those features of those top operating systems were put in mind of the classic XKCD cartoon. So here's what Nick Wellenhoffer recently posted under the topic Triaging Security Issues reported by third parties. So this is the, this is the guy who's maintaining this library that Mac, Windows and Linux are all using. He wrote. I have to spend several hours each week dealing with security issues reported by third parties. Most of these issues are not critical, but it's still a lot of work in the long term. This is unsustainable for an unpaid volunteer like me. I'm thinking about making some changes to allow me to continue working on Live XML too. The basic idea is to treat security issues like any other bug. They will be made public immediately and fixed whenever maintainers have the time, meaning whenever he has the time. There will be no deadlines. This policy will probably make some downstream users nervous, but maybe it encourages them to contribute a little more. The more I think about it, the more I realize that this is the only way forward. I've been doing this long enough to know that most of the secrecy surrounding security issues is just theater. All the best practices like OpenSSF scorecards are just an attempt by big tech companies to guilt trip OSS maintainers and make them work for free. My one man company recently tried to become an Open SSF member. You have to become a Linux foundation member first, which costs at least $10,000 per year. These organizations are very exclusive clubs and anything but open. It's about time to call them and their backers out. In the long run, putting such demands on open source software maintainers without compensating them is detrimental. I just stepped down as Lib XSLT maintainer and it's unlikely that this project will ever be maintained again. It's even more unlikely with Google Project Zero, the best White Hat security researchers money can buy breathing down the necks of volunteers. So he posted that over and on GitHub, and that was his issue opening posting, which evoked a thoughtful reply from Red Hat's Michael Catazaro, who is the GNOME really, who's on the GNOME release team, the Fedora Workstation working group, and the desktop team at Red Hat. So somebody to listen to. Michael's reply was problem is, many of these bugs will actually be exploited in the wild if we do this both in targeted attacks against specific disfavored individuals and mass attacks against vulnerable populations like Uyghurs. So he had three points. He said, I agree that reducing the disclosure deadline for live XML2 vulnerabilities might be strategic, at least for the time being. But there's a cost Downstream vendors might stop reporting bugs here, which is probably worse than the status quo. If you want to do this, then I suggest applying a short disclosure deadline of 14 days rather than 0 days. It might not even be necessary to make any changes to the disclosure deadlines at all. Please take a few days to think about what you prefer since you are the only active maintainer. I will follow whatever you decide. Second, he wrote, if you're burning out, then one option worth considering is to reduce your focus. For example, you might consider focusing on triaging issue reports, reviewing merge requests, and optimistically mentoring new maintainers rather than trying to fix security issues yourself. It's unreasonable to expect you to handle every problem alone, and it's time for downstream vendors to step up if desired. Many extremely wealthy corporations have a stake in fixing live XML 2 security issues and they should help out by becoming upstream maintainers. If nobody else wants to help maintain lib XML 2, then the consequence is security issues will surely reach the disclosure deadline, whatever it is set to, and become public before they are fixed. This is not your fault. And finally, he said, I'm very grateful to Project Zero defending Google and other vulnerability research groups for reporting issues. Their reports are invariably excellent and we should encourage them to continue reporting vulnerabilities as quickly as they can find them. Warning us that problems exist is not a problem. That said, Project Zero has notably reported zero security vulnerabilities in Lib XML 2. Since the start of the year, they have reported three vulnerabilities in Lib XSLT. And Nick, the original poster and maintainer of this, answered Michael's reply writing the point is that lib XML 2 never had the quality to be used in mainstream browsers or operating systems to begin with. It all started when Apple made lib XML 2 a core component of all their OSs. Then Google followed suit and now even Microsoft is using lib XML 2 in their OS. Outside of Edge, this should have never happened. Originally it was kind of a growth hack. But now these companies make billions of profits and refuse to pay back their technical debt, either by switching to better solutions, developing their own, or by trying to improve lib XML 2. The behavior of these companies is irresponsible, even if they claim otherwise. They don't care about the security and privacy of their users. They only try to fix symptoms. I'm not playing a part in this game anymore, he writes. It would be better for the health of this project if these companies stopped using it. I'm thinking about adding the following disclaimer and he writes Quote this is open source software written by hobbyists, maintained by a single volunteer, badly tested, written in a memory, unsafe language, and full of security bugs. It is foolish to use this software to process untrusted data. As such, we treat security issues like any other bug. Each security report we receive will be made public immediately and won't be prioritized. Unquote. That's like the sign on the Bitcoin kiosk. And then he finishes. Most core parts of live XML 2, he writes, should be covered by Google, should be covered by Google's or other bug bounty programs. Already. The rest of the code isn't as security critical. I don't care if I don't receive security reports as early as possible. Most issues should be easily fixable by anyone. As soon as a patch is available. My job is done. I won't embargo security issues until a release is made. The only time you really want to embargo are on non trivial issues that take longer to fix. I can live with that risk. Regarding Michael's bullet points, he says, I'd love to mentor new maintainers, but there simply aren't any candidates. I'm not burning out. Thanks for asking. So earlier I was admiring with some awe the graceful way our industry has been managing the growing threat of quantum computing, which has the potential to overturn our well established public key crypto systems. That's in the sharpest possible contrast to the sad and arguably pathetic mess the same industry has made of the open source model. XKCD's famous teetering tower is so poignant exactly because it's so true. The idea that Apple, Microsoft and Google are all using this code for free, then Google's Project Zero is finding and reporting flaws while starting a disclosure deadline countdown clock as a means of forcing the software's developers to to fix the discovered mistakes is so deeply wrong on so many levels. Yes, so I can see the logic behind Nick's solution. If all flaws, whether or not they are also security vulnerabilities, are immediately made public, then Project Zero is defanged and deadlines cease to exist. Next follow up posting made it clear that he's well over the glory and flattery of having all of the big OSes incorporating his code into their commercial offerings. Thanks very much. How about paying for the privilege of having me maintaining this code base for you to use year after year after year? And that's the problem of course. The open source software concept has always been that it's there to be freely used by anyone for free. And that's what happened when another hobbyist uses it for their own little project. That's different from when a massive multi billion dollar corporation does so. In the latter case, the value proposition there seems unbalanced. Those multi billion dollar corporations are paying for their own code maintainers to keep their code working. But then they also take whatever they want from the open source community without ever returning anything other than complaints when there's a problem. Now we know that there are more socially responsible large corporations that do employ developers to work on improving open source software. Certainly Google does a great deal of that as well. But not everybody, you know, this open source movement, while it certainly has its heart in the right place, hasn't yet, I think, managed to figure out how to manage a fair exchange of value.
- [87:46]
Leo Laporte
Right on Steve. Right on. Yep, agree. 100%.
- [87:51]
Steve Gibson
Okay, I have to report the second remote code execution vulnerability that we've talked about on this podcast in a utility, an app for Windows that a great many of us use, and that's WinRAR. I'm a registered and paid RAR and WinRAR user, so when I hear of an exploitable remote code execution vulnerability in WinRAR, I'm quick to up to download an update. WinRAR just moved to version 12 point I'm sorry to ver to version 7.12 and everyone using it should update you just go to win rar you know w I n-rar.com download.HTML their notes winrar's notes said directory traversal remote code execution vulnerability and this was it's it's got a ZDI so it came from the Zero Day Initiative. It's their number 27198. They wrote in previous versions of WinRar, meaning before 7.12. So in previous versions of WinRar as well as raw UnRar, an UnRar DLL and the portable unrar source code for Windows, especially crafted archive containing arbitrary code could be used to manipulate file paths during extraction. User interaction is required to exploit this vulnerability, that is you have to extract things which could cause files to be written outside the intended directory. Whoops. This flaw could be exploited. They wrote to place files in sensitive locations such as the Windows startup folder, potentially leading to unintended code execution on the next system login. This issue affects only Windows based builds versions of RAR and UNRAR for Unix. The portable source code on Unix and RAR for Android are not affected. We thank WHS3 hyphen detonator working with Trend Micro Zero Day Initiative for responsibly reporting this vulnerability. So the danger would be that miscreants would arrange to induce Windows users to download, open and extract the contents of what would essentially be booby trapped RAR files when doing so, even though a user responsibly set the extraction to directory for some special malicious files that can be overwritten, causing them to be written anywhere the miscreants choose. We covered a similar problem with RAR and winrar many years ago, and I recall that by the time we reported it, that problem was under active exploitation, so fixing it was extra imperative. This time RAR users have the opportunity to get ahead of the day. I've not heard yet of this being exploited in the wild, but it's just going to be a matter of time. My Windows 10 machine had version 5.18 and the installer simply overwrote that with the newer version, registration remained intact and I now have a much more current release of RAR and WinRAR on my machine. So just wanted to make sure everybody knew about this. Oh, we have a very cool new site for everyone to check out. Have I been Pwned Watch. You're probably going to want to bring this up, Leo. H A H A V I B E E N P W Ned. You know Pwned Pwned dot Watch. A security engineer named George Andre Iasif who's with Snap, created haveiben Pwned Watch. It is a portal to display the data from live data from the haveibeenpwn.com website in very easy to use graphs and infographics. The headline of his page reads open source no fluff charts showcasing have I been pwned.com's pwned account data. And his charts support mouse hovers so you can float your mouse around to explore the charts. Anyway, just. I just wanted to give everybody a heads up about it. It's just a very cool facility.
- [92:56]
Leo Laporte
I'm trying to pull it up, but I think I'm being. It's probably newly registered domain and I've been being blocked.
- [93:02]
Steve Gibson
It worked for me. Do you have maybe.
- [93:04]
Leo Laporte
Oh no, I have all that weird security.
- [93:07]
Steve Gibson
Of course you do stuff on there. Yeah, sometimes when. When your guys are sending me a link to like a different zoom session or something. It's like oh crap, that's on a different computer. Which is well firewall even for me. And so I. It's like how do I get it over to it?
- [93:25]
Leo Laporte
So let me see. I just added it to my allow list. It takes a little while to.
- [93:30]
Steve Gibson
But. But you're right, I've never seen a Dot Watch top level domain.
- [93:34]
Leo Laporte
Yeah. So yeah, I don't know. Now unable to connect. That's. It's blocked somehow. So I'm sorry. Leave this as an exercise for our listeners at home.
- [93:44]
Steve Gibson
Let me see if I can bring it up.
- [93:46]
Leo Laporte
I'm sure you can.
- [93:46]
Steve Gibson
Yeah.
- [93:47]
Leo Laporte
Next DNS. I. Yeah, yeah.
- [93:49]
Steve Gibson
Ah, right, right, right. And actually I think I told you that I stopped using it. Stop using Next DNS because as a. I'm developing the DNS benchmark.
- [94:00]
Leo Laporte
Right.
- [94:00]
Steve Gibson
One of the things it does is. Well, yes. And. And it. It produces a burst. Actually it no longer does, but I was experimenting with removing the throttling so that it was just unthrottled and it looked like a DDOS attack on Net. On next DNS I said, oops, sorry guys. Yeah, never had a problem again. Okay. So Sophos tells us how the bad guys are getting in. They produced a very nice infographic in bar chart form among each of the six possible technical root causes, as they called it, of eventual that will lead to eventual ransomware attack. It breaks down the percentage of each of those six possible causes for the most recent three years and in this case 2025 year to date. So 2023, 2024 and so far, like the first half of 2025. I wish they had shown this as three pie charts, one for each year. Then we could more easily see the relative percentages for the year overall among the the six different ways of getting in. And then by looking across the pies, we could see how those vary from year to year. But I just think they didn't give it that much thought. Not as much as, as I did putting this into the show notes thinking, wow, this is not done right. And I guess I could have done it myself, but no. Anyway, the six categories in order of clearly increasing incidents, so from least likely to most often occurring regardless of the year. So there's no change from year to year. They the least often is just a download of a file. Doesn't happen very often. Like 1 or 2% brute force attacks, around 3 to 6%, phishing between 11 and 18%. And that's across the three years. Malicious email from 18 to 23%, compromised credentials, now we're getting there, that's between 23 and 29%. And finally the biggie is exploited vulnerabilities, and that's at 32 to 36% regardless of the year. One category, that biggest one exploited vulnerabilities, was responsible for a little over one third of all ransomware attacks. And you know, can you say Cisco compromised credentials, as I, as we saw, took a strong second place. And in fact, for every year, the sum of exploited vulnerabilities and compromised credential percentages accounted for over half of all across all six causes. So compromised credentials, exploited vulnerabilities, and not surprisingly, that's why that's what we end up talking about so much and seeing so much in the news. That's the way the guys are getting in. You know, there were slight differences in the percentages from, from, from year to year, but no real huge pattern. It's not like anything got better over time. So we don't appear to be doing any better from 2023 than we are through through the first half of 2025. And in fact, the reverse is clearly the case since these bars represent percentages we don't see actual numbers, but down in the fine print of Sophos's caption, we see this. You know the statistical N values for the number of ransomware attacks tracked from which those percentages were taken? For 2023, all of that year, that number is 1974. For all of 2024, it was 2974.
- [98:20]
Leo Laporte
Oh, big jump.
- [98:21]
Steve Gibson
Exactly a thousand more during 2024 than 2023. But for 2025 year to date, we're already at 3400, so twice that probably. Right? Yes. Twice what we had last year.
- [98:39]
Leo Laporte
Wow.
- [98:40]
Steve Gibson
And hello, Cisco.
- [98:42]
Leo Laporte
Anyway, you said that like 12 times in the show today.
- [98:47]
Steve Gibson
Are you.
- [98:47]
Leo Laporte
Are you a little salty about Cisco?
- [98:49]
Steve Gibson
A little annoyed, yeah.
- [98:51]
Leo Laporte
This is actually very interesting from Sophos. It's not so much downloaded or even brute force, it's. It's vulnerabilities. It's a big problem.
- [99:01]
Steve Gibson
And we're going to see that acquiring those is the way you win this game, Leo.
- [99:07]
Leo Laporte
Yeah, not a surprise. By the way, it was next DNS. I have been able to go to the. The haveibenpwned watched site.
- [99:16]
Steve Gibson
Nice site. Lots of cool.
- [99:17]
Leo Laporte
Yeah, really cool. Very interesting. I love it. That. Have I been pwned? Has an API.
- [99:22]
Steve Gibson
Yes. Isn't that cool? And are you able to hover your mouse and pick up stats? Yeah, oh, yeah. There. Yeah. Yeah.
- [99:29]
Leo Laporte
Cool reaches per year. Yeah.
- [99:31]
Steve Gibson
Yeah. Wow.
- [99:33]
Leo Laporte
Poned accounts per year. Why was 2019 so bad, I wonder? Maybe one or two really big ones. Right.
- [99:42]
Steve Gibson
You know, we got hit with those credential attack surprises.
- [99:46]
Leo Laporte
Yeah.
- [99:47]
Steve Gibson
And you know, we were talking about that a lot back then.
- [99:50]
Leo Laporte
Look at this.
- [99:51]
Steve Gibson
And that. Yeah. Those little stacked bars are very cool because you're able to explore them.
- [99:56]
Leo Laporte
Yeah, yeah, very nice. Anyway, thank you for blocking it. Next DNS, I'm going to turn you back on now, probably.
- [100:06]
Steve Gibson
That is probably just a. A block, unless we know otherwise.
- [100:12]
Leo Laporte
Right, right.
- [100:13]
Steve Gibson
So the bad guys are not cooking up new random TLDs and using that in order to get through until next DNS, you know, is able to add a. A block on it. So, like, if we don't know it's okay, we're just saying no.
- [100:27]
Leo Laporte
Yeah, yeah.
- [100:28]
Steve Gibson
That's very cool.
- [100:29]
Leo Laporte
Yeah.
- [100:30]
Steve Gibson
What is also cool, Leo? We're at an hour and a half is we're going to talk about what Microsoft hopes they have done to fix the crowdstrike flaw which brought down all those 8.5 million machines last summer. Take a break. I'm going to take a sip of coffee and then we're going to look at that.
- [100:50]
Leo Laporte
I want to look one more time at this chart. Snowfall's chart. See that big stack there? Malicious email, the root cause of ransomware attacks. You know, between 18 and 23% of all these attacks are email that comes in over the transom. That's why you need our sponsor for this segment of security now. Hawkshunt. As a security leader, your job, your paycheck depends on protecting your company against cyber attacks. But it's getting harder, right, with more cyber attacks than ever. And now thanks to AI, these phishing emails used to be, you could say, oh, obviously a phony look at the grammar or not an English speaker or whatever, right? No, now they're generating phishing emails with AI and perfect grammar, perfect spelling. Unfortunately, training your staff can be a challenge. Legacy training programs, these one size fits all awareness programs, they're not gonna, they don't stand a chance. They send at most 4 generic trainings a year every quarter. Most employees, you know, they have a heave, a deep sigh when they get these and they just ignore them. And then when somebody actually clicks, they're forced into embarrassing, let's face it, embarrassing training programs that feel more like punishment. Nobody learns if they're embarrassed and they're feeling punished. That's why more and more organizations are trying Hawks Hunt. H O X Hunt goes beyond security awareness. It actually changes behaviors by gamifying the whole thing. Employees love it. It's fun. Hox Hunt rewards good clicks, coaches away the bad clicks. Whenever an employee suspects an email might be a scam, they click a button. Hocks Hunt will tell them immediately, you know, big flash, it's really cool. It's a game. Providing them with that gaming rush, that dopamine rush that incense your team to click learn and protect your company. They do it because they love it, because it's fun. As an admin, Hawkshunt makes it easy for you to automatically delivering phishing simulations, by the way, just not just email. In fact, if you look at this chart again, phishing is a big reason, right? Well, it goes through email. It works on Slack, it works on teams using AI to mimic the latest real world attacks. And I love the simulations are personalized to each employee based on department location and more. The bad guys are doing it. The simulation's got to do it. While instant micro trainings, not big, long, complicated, boring punishment trainings, but instant micro trainings solidify understanding and drive lasting, safe behavior. You can trigger gamified security awareness training. This is I think, really the secret sauce they've made it fun. They reward employees who spot the bad guy who spot the bad clicks with gold stars and it works. And I'm not surprised it works. They get badges. This boosts the completion rates. This ensures compliance and you can choose from a huge library of customizable training packages. Generate your own with AI. It's fun for you. It's fun for them. Everybody learns your company is protected. Hawkshunt has everything you need to run effective security training on one platform, meaning it's easy to measurably reduce your human cyber risk at scale. You don't have to take my word for it. There are over 3,000 user reviews on G True, making Hawkshunt the top rated security training program for the enterprise. It won easiest to use, best results. It's also recognized as customers choice by Gartner and thousands of companies like Qualcomm, AES and Nokia use Hawkshunt to train millions of employees all over the globe. Visit hoxhunt.com securitynow today to learn why modern secure companies are making the switch to to hawks hunt. That's hawkshunt.com security now don't add to these numbers. Don't be part of these statistics. You want to. You want to use Hawks Hunt and your employees will thank you. Your boss will thank you. He'll thank you because your life's easier. Hawkshunt.com Security now. We thank them so much for their support of the show. Back to you, Steve.
- [105:21]
Steve Gibson
Okay, so we were recently remembering last July's Windows mess, which was triggered by a flaw in CrowdStrike's endpoint security system.
- [105:32]
Leo Laporte
Yes. Oh, what a mess that was.
- [105:35]
Steve Gibson
It resulted in more than 8 1/2 million windows systems crashing hard and staying crashed hard. Although, Leo, we should be sensitive to the fact that this is no longer the official term for such events, I'm pretty sure that Microsoft would prefer that we refer to those 8.5 million systems as taking an unplanned group vacation. In any event, once those eight and a half million machines returned from vacation and went back to work, Microsoft hosted in September the Windows Endpoint Security Ecosystem Summit, which, if you had an ac, if you made it turn it into initials, would be wesys W E S E S. That summit assembled a diverse group of Endpoint security vendors and global government officials to discuss strategies for improving resiliency and protecting their mutual customers. In other words, you know, how the F do we prevent that from ever happening again? Because, boy, was that. That was a mess. So that brings us to today's news. Microsoft is close to launching a new security platform next month. They've said that they will begin privately previewing their new technology that will allow antivirus and security tools to run without kernel access. And as we know, this has been the great challenge for Windows to provide truly strong endpoint security. Third party vendors have needed to dig deeply into the OS to get their hooks into all of the various APIs that malware might attempt to abuse. Basically, you know, being able to watch what, what Windows is encountering and preventing malware from taking advantage of that if there's a weakness that lies behind, and this is not something that any operating system wants to permit, that is allowing anything else to hook deeply into it. For precisely the reasons that befell all of Microsoft's and CrowdStrike's customers last summer. When something goes wrong, it's bad. So Microsoft has been caught between a rock and a hard place because they've also been unwilling apparently until now, to provide any workable alternative solution to keep API, you know, to a, an alternative solution to the need for deep API kernel hooking. We're now being told that this will finally be changing. So I'm just reporting that it'll be interesting to see whether the vendors themselves who have been actively participating in this process end up being satisfied with what Microsoft ends up doing. The, the, the, one of the issues is performance. You know, the, the, you know, coming in and out of the kernel is expensive. This is the reason that the graphics device interface, the GDI component of Windows, which was deliberately kept outside the kernel because, can you say interpreter? It, it's so much potential for problem. Unfortunately, this gdi, the graphics device interface portion, needed to be talking to the kernel all the time. So Microsoft analyzed the overhead of that dialogue and decided we can't afford not to move GDI into the kernel. What happened was Windows got faster and its security collapse words. Yes, yes, much worse. So you know, they've been recovering from that decision for a long time. And what's really annoying is it was transient because now systems are so fast and GPUs are, are ubiquitous that you don't, you no longer have this problem with having a slow graphics device interface portion of Windows. But you know, we have history. Anyway, I think we're going to have to wait to see. It's only being released for preview on a selected basis, not even broadly as I understand it. So they're going to, you know, creep this out and, and we'll see how that goes. It would be good if we could move Endpoint Security out of the kernel without incurring a performance problem. You know, no one's done it yet, so let's hope. And they've, you know, they've been working on it for a year basically since this disaster last July.
- [110:45]
Leo Laporte
Nothing should run in the kernel. I mean, ring zero should be sacred. Right?
- [110:49]
Steve Gibson
And you want a. The concept is a microkernel, right? You know, you want a little small bunch of code whose integrity you can be absolutely sure of, manages processes, it manages threads, it manages memory, and that's pretty much all it does. Then everything else is around it. Are clients of this microkernel. That's the. I mean, everyone starts out that way. And then just like anything else, it's like, it's like our U. S. Tax code. Everything starts out looking great. It's like, well, but you know, those, those farmers, they need some extra help. So let's, let's cut out a little current, you know, little, little change in the tax code. Similarly, it's like, oh, well, yeah, but this networking API, it turns out that this is a little slow to do outside the kernel. So let's just put a little. Move a little bit of that code into the kernel and before you know it, you end up with a big bloated operating system and you no longer have any control over it.
- [111:52]
Leo Laporte
It's even happened on the Mac. The mock kernel they use was a micro kernel, but at this point, you'd be hard pressed to call it that.
- [111:58]
Steve Gibson
Yeah, it's just, it's. I, you know, it's one of the unsolved problems of computer science. We have not yet figured out how to evolve software in a way that doesn't cause it to just get really ugly.
- [112:13]
Leo Laporte
Yeah.
- [112:13]
Steve Gibson
Over time. Okay. The U.S. supreme Court just upheld a contentious Texas law. You know where I'm going with this?
- [112:24]
Leo Laporte
I do. We talked about it extensively on Sunday.
- [112:26]
Steve Gibson
Yeah. Oh, yeah. It requires proactive age verification before accessing pornographic content on the Internet. And as I've noted before, this is fundamentally different from mom and dad setting the dates of birth into Johnny's and Sally's phones so that they'll be able to use Facebook. This is mommy and daddy needing to prove their own ages to some of the websites they have every legal right to visit. This is made tricky by the fact that at the moment, we have no technology for providing anonymous age verification. And the challenge of providing unspoofable anonymous age verification remains an unsolved problem. Wired's coverage of this had the headline US Supreme Court upholds Texas porn ID law and the subhead is. In a 6 to 3 decision, the Supreme Court held that age verification for explicit sites is constitutional. In a dissent, Justice Elena Kagan warned it burdens adults and ignores First Amendment precedent. The first four paragraphs of Wired's extensive coverage I want to share because you get the gist of everything they said. If you try to access Pornhub, one of the world's biggest websites from any of 17 US states, you'll be blocked. Pornhub's parent company, Alo holdings, has restricted access in response to a slew of laws that says pornhub itself should be responsible for checking that every visitor is over 18. Now the United States Supreme Court has made a decision on a key age verification law, which could have ramifications for the entire country and the wider Internet as a whole. On Friday, in a 6 to 3 decision that could reshape the landscape of online privacy and free speech, the Supreme Court upheld in full the Texas age verification law, one of the first passed in the country, requiring many websites publishing pornographic content to check that all visitors are over 18. The law, Texas HB 1181, says sites that are more than one third sexual material can face fines of up to $10,000 per day if they don't put in place age verification systems, plus extra penalties of up to $250,000. It also states websites should display health warnings about the potential health risks of pornography. Writing for the majority, Justice Clarence Thomas said that because the law, quote, simply requires proof of age to access content that is obscene to minors, it does not directly regulate adults protected speech, unquote adding, quote, adults have no First Amendment right to avoid age verification, unquote. In her dissent, Justice Elena Kagan argued that the Texas law imposes a direct and unconstitutional burden on adults access to protected speech, writing, quote, a state may not care much about safeguarding adults access to sexually explicit speech. A state may even prefer to curtail those materials for everyone, she wrote, but the First Amendment protects those sexually explicit materials for every adult, unquote. So I had no idea that pornhub could be described as one of the world's biggest websites. I did a little bit of checking and sure enough, it is. I. It's. It's unbelievable. So it seems from a technically, from a technology standpoint, it seems clear to me that this creates a market in the short term for VPN services which provide for virtual Internet relocation. But I suppose that anyone living in any of those 17 blacked out US states who wishes to obtain access to this proscribed content will have already found A way to appear to be connecting from a non blacked out location. But I said in the short term because VPN services operating within the United States are also subject to the law. And the law doesn't say no one connecting from within Texas, it says no one residing within Texas. So once the use of VPNs for geo relocation becomes commonplace, we can expect our duly elected representatives to close that loophole too. So this is going to be interesting to watch. And it's another intractable mess we've gotten ourselves into. Where the cyber world collides with the physical world.
- [118:08]
Leo Laporte
Yeah, I mean, no one would contest that. You know, grocery store owners should be able to age check kids buying adult material on the newsstand. That's not a problem. This though, has a much larger impact because age verification is inherently a privacy violation. And furthermore, the definition of what is adult material is very flexible. And it's not hard to imagine at some point Texas or some other state's legislature saying LGBTQ content is adult or, or content about contraception or even, you know, content that is unfriendly to the.
- [118:49]
Steve Gibson
Administration, increasing the, the breadth of the band. Yeah, well, and, and I've made the point that in the physical world, you know, a 14 year old trying to sneak into a, to a strip club is going to be stopped at the door by the bouncer.
- [119:05]
Leo Laporte
Right.
- [119:05]
Steve Gibson
Because you're obviously 14. Exactly.
- [119:09]
Leo Laporte
Right. They don't check your ID at every, @ every person.
- [119:13]
Steve Gibson
Right. But on the Internet, no one knows how old you are.
- [119:16]
Leo Laporte
Exactly, exactly. It's a very, very bad precedent. It really undermines the First Amendment, I think. And.
- [119:24]
Steve Gibson
Well, it is an intractable mess. And I mean, you know, coming from, from a technology standpoint, I can, I can solve the problem of mom and dad wanting Johnny and Sally. I love your station. To have their, their phones identify their age. Yeah, that's not a problem.
- [119:40]
Leo Laporte
Right.
- [119:41]
Steve Gibson
But, but dad or mom needs to prove that they're, that they are of age if they want to access this, this now prescribed content. And, and, and we've also made the point too, that if a 14 year old, they can get, or wants to get around. Yeah. I mean, that's just not gonna block anybody who's determined. No, I mean, were I 14 years old, I'd be having a lot of fun selling access to my, to my peers. I.
- [120:11]
Leo Laporte
Look, it's a, I think it's probably a laudable goal to try to restrict access to that kind of content.
- [120:16]
Steve Gibson
Yes.
- [120:17]
Leo Laporte
I mean, kids, I don't think that's a bad thing.
- [120:19]
Steve Gibson
But having A yes, I'm 18 button, that does nothing, right? I mean, we know that does nothing. It's like, you know, is, look, the, the handle on the door is unlocked.
- [120:29]
Leo Laporte
Every website that sells liquor, every whiskey site we go to on Wednesdays has that age verification thing on there. That's nonsense. But I wouldn't want to have to present ID before I could go to a liquor site. That's a very different thing.
- [120:45]
Steve Gibson
And that is the problem is that, you know, I'm sure that a lot of people who do want to visit pornhub do not want to identify themselves.
- [120:55]
Leo Laporte
Oh, I wonder why.
- [120:57]
Steve Gibson
Because of this interest, you don't want.
- [120:59]
Leo Laporte
To give your government issues issued ID to pornhub or Jack Daniels. Either way, it's a bad idea.
- [121:06]
Steve Gibson
Nice. Yeah. All right. Okay, a few other bits. Hick Vision is another controversial Chinese company. We've talked about them in the past. I remember at one point, Leo, years ago when they were like, in the doghouse, you brought up a picture of their website that had like, cameras up in the sky and it was like, it was quite spooky. So they, you know, they manufacture security cameras and the Canadian government has just ordered them to close their Canadian operations, basically kicking Hick Vision out of Canada.
- [121:41]
Leo Laporte
Interesting. Wow.
- [121:42]
Steve Gibson
The. The Canadian official said that the company's business is an active threat to Canada's national security and banned government agencies from purchasing new Hick Vision products, even using stores outside of Canada. And as we know when we covered this previously, the US Sanctioned Hick Vision for aiding the Chinese government's surveillance of the Uyghur minority in Western China. So, you know, there again another instance of, of this growing divide that unfortunately that we are seeing. Meanwhile, Berlin, Germany's Data Protection Agency is seeking to ban Deepseek throughout Germany over its. Over what they're claiming is Deep seeks illegal transfer of user data to China. Germany's Data Protection Agency has reported both apps to the Apple and Google app stores for GDPR violations. In other words, get them out of the store. According to cnbc, this initial action in Germany may lead to a European Union wide ban on Deep Sea. So Germany first, maybe all of the eu. And I, I do regard all this as unfortunate, but I guess inevitable. Early last month, Russian ISPs. I love the word throttling in this reporting. ISPs began throttling traffic from Cloudflare to their customers. Okay, and as we've talked about recently, what, a massive percentage of the Internet is now being hosted by Cloudflare. So if Russian ISPs are throttling Cloudflare's traffic, then that means that all of the customers of those ISPs are are going to have a problem. Well, they're going to have a bigger problem than throttling would suggest. You would think that that meant forcing pages to load more slowly. No, Russian ISPs are, get this, only allowing 16k bytes of data to load from a page before completely blocking anything more. Now you could actually surf GRC with 16k pages, but probably nothing else on the Internet.
- [124:17]
Leo Laporte
Yeah, that's pretty remarkable, you know, because.
- [124:19]
Steve Gibson
I'm still ham coding all of the HTML and there's no libraries or scripts or anything, so. Okay, the only rationale that I could imagine would be that it would be possible to have a Cloudflare site return an HTTP redirect in fewer than 16k bytes. I mean, it only takes a few hundred bytes, which would redirect to a Russian located site. So I don't know, maybe that was the idea. I mean, 16k, you can't even get off the ground on a web page with 16k these days. Any Russian sites hosted by Cloudflare could re host themselves in Russia and redirect any previous Cloudflare visitors to their Russian hosted site. But on the other hand, why not just repoint the domain to a Russian hosted ip and that would be easier. So I don't understand it. I mean, why, if you wanted to block Cloudflare, just shut it off? I don't get what 16k bytes does. It seems crazy to me, but.
- [125:32]
Leo Laporte
Okay.
- [125:36]
Steve Gibson
Just a brief update, Leo. Having caught up with Rick Brown's Frontiers Saga series over the weekend, I started into my reread of Project Hail Mary.
- [125:48]
Leo Laporte
Oh, good.
- [125:49]
Steve Gibson
I had forgotten how much I must have enjoyed it the first time.
- [125:56]
Leo Laporte
Yeah.
- [125:56]
Steve Gibson
Since I am astonished by how much fun I am having with this book and you.
- [126:02]
Leo Laporte
And even though you know what's going to happen, you're still loving it.
- [126:05]
Steve Gibson
Oh, well, that's me. I. Yes, we. There are some things that my wife Lori will do more than once we really like. Well, there are a number of movies that we've seen several times, but generally, if she knows what's going to happen, she has no interest. Now, she loved the Martian and I don't think she really paid attention. When I was reading Project Hail Mary the first time, she may have been in the middle of another book, but when I came home last week with the news of this trailer that we talked about last week and we started watching it, she immediately stopped me. Before, like we all we Only got, like, I don't know, a third of the way in because she didn't want any spoilers. She wanted to read the book because she liked the Martians so much. She finished that book. She finished Project Hail Mary this weekend and really enjoyed it. Although she thought the ending was sappy. I thought it was wonderful, so. And it was sappy, but okay.
- [127:20]
Leo Laporte
Yeah, well, we're old softies, I guess, right? She's a hard woman. A hard woman.
- [127:26]
Steve Gibson
Anyway, so, for what it's worth, for anyone listening to as geeky a podcast as this, who obtains pleasure from reading or listening to books, you will likely love Andy Weir's writing. You know, his science and his humor. He's great. Yeah. You know, I. I missed reading Andy's second book, Artemis, when It was released eight years ago in 2017. I must have been deep into some other series at the time, but I'm not now. So once I finish my reread of Project Hail Mary, I plan to follow that with Artemis.
- [128:05]
Leo Laporte
Not as good.
- [128:07]
Steve Gibson
That's okay. I don't need it to be as good.
- [128:10]
Leo Laporte
I interviewed, I've interviewed him, as, you know, every time he comes, I think three times now, because I did interview him for Artemis as well.
- [128:17]
Steve Gibson
Oh, okay.
- [128:18]
Leo Laporte
And Artemis was his plan. He had some really interesting ideas. It was his plan to create a new series, and it has a very. Has a great protagonist. It's a moon colony. It's kind of interesting. I'd be very curious what you think of it. The problem was he started with the Martian and everybody was expecting another Martian.
- [128:41]
Steve Gibson
Like a high bar.
- [128:42]
Leo Laporte
Right. And it wasn't another Martian. And Project Hail Mary is much more in the Martian vein of, you know, sciencing the crap out of it.
- [128:50]
Steve Gibson
Oh, my God. It's. And it's funny, too, because, I mean, I'm, you know, I love physics and I love the science, and there, there have been several points because. Because I, I, I use continuous scroll on my Kindle.
- [129:04]
Leo Laporte
Right.
- [129:04]
Steve Gibson
And. And so there have been points where I've, like, gone and Lori's. And, like, Lori's sitting next to me. She says, what? And I said, oh, I know what the next page is going to have on it because I, you know, I'm following all of the science and, And I'm surprised. I said, deloria, I said, I'm. I'm very surprised that he is this good with the science.
- [129:28]
Leo Laporte
He really isn't he?
- [129:29]
Steve Gibson
Yeah, yeah. But I think he has lots of advisors. Oh, maybe he gets it really right. I mean, it's Astonishing. I like, I like. Anyway, I don't want to give any of it away, but I just wanted to say again to our listeners, what's wrong with you?
- [129:45]
Leo Laporte
What's wrong with you?
- [129:49]
Steve Gibson
The, the only thing that I could see that's wrong is that it's not free. Free is a lot easier than asking anyone to pay, you know, 750 or whatever it is on Kindle. Apparently.
- [130:00]
Leo Laporte
I can't. I can't wait till the.
- [130:02]
Steve Gibson
The movie.
- [130:03]
Leo Laporte
The movie, you know, but I, I wonder.
- [130:06]
Steve Gibson
I'm dying to know how they're going to do this, because all of this is in his head. We're listening to his thoughts. So the only way I can think they're going to do this is that we're just going to hear his inner dialogue, you know, throughout the entire movie, because all, like, I'm. I'm a quarter of the way in, I think, now, and it's mostly inner dialogue. We have to be hearing his voice telling us what he's thinking here.
- [130:33]
Leo Laporte
Andy Weir is. Was on triangulation 428 talking about Project Hail Mary. That was in 2021. We had him on after the Martian in 2014, which is pretty wild. I didn't realize it had been such a big spread. And I feel like we also interviewed him on the new screensavers and there's another one. Oh, for Artemis. Yeah. Triangulation 322, which is in 2017. So, yes, I've spent a lot of time with Andy Weir. Love the guy.
- [131:07]
Steve Gibson
Well. And apparently there were plans for an Artemis movie which fell through. Yeah, maybe because that. It just didn't, you know, do as well as it was expected to. I mean, after you do the Martian, you.
- [131:20]
Leo Laporte
It's pretty hard.
- [131:20]
Steve Gibson
You get the rights grabbed before you even go to print on.
- [131:24]
Leo Laporte
Well, and that's. And that's what happened. I remember him telling us with Project Hail Mary, he knew that Lord and Miller were going to direct it and that Ryan Gosling was going to star in it even before it was published. Yeah, I mean, he, he, he, he already knew all of that. So. Yeah, I don't know what happened to Artemis. Yeah, I think it's actually quite a good book. If it hadn't come on the heels of the Martian to be compared by. Yes. Because it's such a different kind of book. But I love his protagonist. I think it's a great story. It's about the moon colony, and I think you'll like the science in it. There's some good science in it.
- [132:01]
Steve Gibson
Cool.
- [132:01]
Leo Laporte
Yeah.
- [132:02]
Steve Gibson
Well, I will let everybody know what I think. Let's let everybody know what we think. Oh, about this final sponsor, our last.
- [132:10]
Leo Laporte
Ad for the show.
- [132:11]
Steve Gibson
And then we're going to look at going on the offensive. What it's going to take for the US to get nasty.
- [132:21]
Leo Laporte
This episode of Security now brought to you by. Well, I've got it right here. Thanks, Canary. If you are in the business of protecting your company's security, you have probably very strong defenses, right, surrounding you, perimeter defenses. But do. How would you know if somebody got through them? Because, you know, once these wily hackers get in, they are good at covering their tracks. They delete logs. They're very careful not to set off any trip wires.
- [132:54]
Steve Gibson
Everybody agrees that detection is as important as prevention.
- [132:58]
Leo Laporte
Of course, you know, even if somebody gets in, they can't, you know, they, they usually. In fact, on average companies don't know they've been breached for 91 days because why? Because the guy. Guys don't set off the ransomware that day. They spend some time. They get. This is the latest thing, right? They exfiltrate customer information, private emails, they blackmail you. They say, hey, we have all this stuff. Then they set off the time bomb and meanwhile, they've had three months to wander around, look for all the places you might be backing stuff up. It's really, It's a nightmare. That's why you need the THIN canary. It's a honeypot that can be deployed in minutes. You know, traditional honeypots are very tricky to write and maintain, but thinkst canaries, they've done it all. The folks at THIN are experts in this. They teach penetration to governments. And companies have been doing this for years. They took everything they've learned and they've created a honeypot that is irresistible to hackers. Let me show you the. This is the console. I have a thinkscanary right next to me right now. And I'll show you how easy it is to configure. Right now it's posing as a Windows Server 2019 Office file share. That's a pretty good thing to pose as. A hacker sees that share and is going to go, gee, that sounds like something I should be looking at. Of course he's going to look at the Mac address, say, well, let's see if this is. Oh, no, that's a Microsoft Mac address. He's going to look at everything. He's going to. And he's going to realize no RDP is turned on here. This is good news. It isn't, though. It's a honeypot. The minute he attacks it, I'm going to get an alert. Email, sms, Slack, Webhooks, Syslog, whatever you want. Look at all the things it can be. It can be an IIS server, an XP desktop file, Share that. That might be. That's just too obvious. That's too vulnerable. Although I bet there's a few of those around. It could be a server, it could be Linux, it could be Mac OS server. It could be. Oh, hey, maybe we should make it a Cisco router. Steve, what do you think? Bad guys love that. Thing is, it's going to look in every respect. See, the Mac prefix is going to be from Cisco Systems. If there's a login screen, it's going to look exactly like a Cisco router in every respect. But when the bad guy hits it, you're gonna know if someone's asking, oh, I didn't show you the Lore files. Let's. I'm gonna discard the changes for now and I'll show you the Lore files. You can also create these Canary tokens. An infinite number of these, and they can be so many things, including a credit card. It can be an AWS credentials, it could be a MySQL dump, it could be a split spreadsheet, or it could be a Windows folder. The point is these. These you scatter around.
- [135:52]
Steve Gibson
Yeah.
- [135:52]
Leo Laporte
I even put them on our cloud servers. And if somebody attacks them again, you're going to get an alert that matters. If they try to brute force your fake server, you're going to get an alert. But only the alerts that matter. That's the key. The Canary doesn't do false positives. The Canary will never bug you. The think scenary will tell you when you have a problem. Choose a profile on the console. You saw how easy it is. I could change it every day if I wanted to. Register it for monitoring and notifications. And then you just sit back, you relax. Attackers who've breached your network or malicious insiders. Any adversary in your network will let himself known because they cannot resist accessing your. Thanks to Canary. Or those tripwires, those tokens you've spread around. Visit Canary Tools Twit. $7,500 a year for five things to Canaries. You get your own hosted console. You get upgrades, you get support, you get maintenance. And if you use the code twit in the how did you hear about us? Box, you'll also get 10% off the price. And not just for that first year, but for life. You can always return your things to canary with their 2 month money back guarantee for a full refund. 2 months, 60 days. Plenty of time. However, I should point out, during the eight years that THINST has been advertising with us, their refund guarantee has never, not once, been claimed. Because once you have a thin Canary in your network, you're never going to want to give it up. Visit Canary Tools Twit Enter the code TWIT in the how did you hear about us? Box. You know, everybody always says security is about layers and you might have the outer layer, but who do you have protecting you against breaches? You need your thanks to Canary. Canary Tools Twit offer code TWIT in the how did you hear about us? Box for 10 off for life. Thank you. Thanks for the thingst Canary all right.
- [137:49]
Steve Gibson
Steve Areno okay, so this podcast has often wondered what's going on with the United States cyber war posture. You know, we're endlessly covering China's intrusions in the US Networks and all the trouble that causes for us here in the States. We recently looked at the concerns over the discovery of undocumented radios turning up in Chinese made power inverters used in wind and solar energy production. Chinese made security cameras are being increasingly banned from sensitive locations. We talked about hikvision just now and we're worried about the ubiquitous presence of DJI drones being used on military bases and other sensitive areas. What I wonder is whether similarly cyber aware Chinese citizens located in China, especially, you know, our counterparts, are covering the same sorts of stories about intrusions, plotting and planning being made by the U.S. you know, because we're here in the U.S. we don't have the same visibility into U S operations in China as we do into China's operations in the US So I've often wondered whether the US Is giving as well as it's getting. You know, are things balanced? Is China worrying about us as much as we're worrying about them? And I just want to say before we go any further, I always want to be very clear that this entire subject area, and I've alluded to this from time to time, always makes me feel a bit queasy. You know, I know we have Chinese listeners and there are very few things in this life that feel more unjust to me than racism. So I want to be crystal clear here that in every instance we're talking about the actions of our respective governments and their militaries, not their people.
- [139:50]
Leo Laporte
I love the Chinese people, I love the Chinese country. But the ccp, not so nice.
- [139:54]
Steve Gibson
So this is, this is this has nothing to do with ethnicity. You know, although democracies elect their leaders, those leaders don't always do what many of those they lead wish they would. So, you know, we fill out our ballots and hope for the best. So I ran across a fascinating document which was prepared by Winona Desambre Bernson, a former security engineer at Google's oh, that's the name. Leo Tag, the Threat Analysis Group. Google's tag group. You know, Tag, you're it. She's the founder of the Offensive Security Conference District Con held in Washington D.C. and she has organized policy content at DEFCON and authored multiple pieces of offensive cyber capability proliferation. She's a fellow at the Atlantic Council, a Washington D.C. based policy think tank, and in that capacity she interviewed a sobering list of people whom she lists at the end of her piece. In many cases she's only able to use their approximate titles because of the sensitive nature of their positions within the US Government or military. She titled her piece Crash. Well, it would be Crash and Burn, but she put after Crash she had Imper, Exploit and Burn colon Securing the Offensive Cyber Supply Chain to counter China in Cyberspace. So she's taking a, you know, a a clearly US centric how do we give as well as we get stance. And note that her use of the term offensive cyber supply chain. In other words, how can the United States reliably obtain the tools, meaning the exploits we need to attack others? The PDF of this report is 44 pages and I placed a link to that PDF in the show notes for anyone who wishes to dig deeper. I'm certainly not going to go through all of that, but it's beautifully organized for the harried policy pusher. It makes all of its points quickly, then backs them up with data and specifics. So I only need to share the beginning of this well organized, lengthy, in depth and detailed report since it contains a ton of very interesting insights and specifics that we've never covered on this on this podcast before because we didn't have the the the results of these interviews which she has made. So the report begins by posing a question. As its thesis, she writes, if the United States wants to increasingly use offensive cyber operations internationally, does it have the supply chain and acquisition capabilities to back it up? Especially if its adversary is the People's Republic of China, she writes. Strategic Competition Strategic competition between the United States and China has long played out in cyberspace, where offensive cyber capabilities like zero day vulnerabilities are a strategic resource. Since 2016, China has been turning zero the zero day marketplace in East Asia into a funnel of offensive cyber capabilities for its military and and intelligence services, both to ensure it can break into the most secure Western technologies and to deny the United States from obtaining similar capabilities from the region. If the United States wishes to compete in cyberspace, it must compete against China to secure its offensive cyber supply chain. This report is the first to conduct a comparative study within the international offensive cyber supply chain comparing the United States fragmented risk averse acquisition model with China's outsourced and funnel like approach. Our key findings are we have some bullet points. First, zero day exploitation is becoming more difficult, opaque and expensive leading to feast or famine contract cycles and I'll get to explaining that in a minute. Middlemen with prior government connections further drive up costs and create inefficiency in the US and Five Eyes market while eroding trust between buyers and sellers. China's domestic cyber pipeline dwarfs that of the United States. China is also increasingly moving to recruit from the Middle east and East Asia. The United States relies on international talent for its zero day capabilities and its domestic talent investment in is sparse, focused on defense rather than offense. The U.S. acquisition process favors large prime contractors and prioritize extremely high levels of accuracy, trust and stealth which can create market inefficiencies and overly index on high cost exquisite zero day exploit procurements China's acquisition processes use decentralized contracting methods. The Chinese Communist Party outsources operations, shortens contract cycles and prolongs the life of an exploit through additional resourcing and end day usage. Meaning not just zero day. US Cyber security goals coupled with big tech market dominance are strategic counterweights to the U.S. offensive cyber capability program, demonstrating a strategic trade off between economic prosperity and national security. China's offensive cyber industry is already heavily integrated with artificial intelligence institutions and China's private sector has been proactively using AI for cyber operations. And finally, given the opaque international market for zero day exploits, preference among government customers for full exploit chains, leveraging multiple exploit primitives, and the increasing and the increase in bug collisions, governments can almost never be sure they truly have a unique capability. Okay, so it feels as though there may be an inherent conflict between the traditional way the US military has conducted its business and the faster, more furious and significantly less certain way the zero day cyber marketplace functions. It also sounds as though the US may still be stuck in a but we're the good guys mindset, whereas China's management may evidence more of a just get it done style which more closely aligns with the realities of cyber winona next lists three recommendations, writing first, strengthen the supply chain by creating Department of Defense dodge vulnerability research accelerators, funding domestic hacking clubs and competitions, expanding the NSA's Centers of Academic excellence in cyber operations and providing legal protections to security researchers. Second, improve acquisition processes by establishing a government sponsored vulnerability broker in a federally funded research and development center to decentralize and simplify exploit purchases while increasing cyber capability budgets and expanding research on automated exploit chain generation and third, adjust policy frameworks to consider counterintelligence strategies in the zero day marketplace, burning capabilities of malicious actors while recruiting willing responsible actors into a more formal pipeline, funding end day research through U.S. cyber Command where appropriate, and leveraging alliances to counter China's growing cyber dominance. That all appears to amount to, you know, quote, you know we need to be getting serious right now about zero day exploit acquisition. That's where all the action is and where it's going to be in the future and we're going to be in trouble if we don't rearrange our operations and priorities right away. She concludes, without meaningful reforms, the United States risks ceding China whatever strategic advantage it has left in cyberspace. By fostering a more deliberate offensive cyber supply chain and adjusting acquisition strategies, the US can retain a steady supply of offensive cyber capabilities to maintain its edge in the digital battlefield. Okay, it's unclear to me where the assumption comes from that the US Currently has any edge at all in the digital battlefield. We don't know what we don't know, but I wonder if this isn't just a bit of soft pedaling so as not to ruffle too many higher up feathers who are reading this policy piece. Her report then provides a pair of pull quotes to set the stage for a bit more background. The first quote is from Alexi Bullizel, incumbent on Special Assistant to the President and National Security Council Senior Director for Cyber Alexi says, quote, america has incredible offensive cyber power. We need to stop being afraid to use it. I dearly hope that America has incredible offensive cyberpower and that the only reason why we haven't seen more evidence of it is that we've been afraid to use it. That suggests that it might be available if and when needed. Jeremy Fleming, former GCHQ Director, is quoted saying, geopolitical conflicts are increasingly shifting to cyberspace, including tensions between the US And China. Technology is therefore no longer just an area for opportunity, but also a battlefield for control, values and influence. Unquote. Okay, so here's the background Winona provides to preface her more detailed analysis that follows, which I'm not going to share, but the background has got some good stuff in it, she says. China and the United States are engaged in strategic competition in cyberspace. While cyber operations are often an overlooked area of geopolitical power, both countries, militaries, intelligence communities, and law enforcement agencies conduct cyber operations. They do so to obtain intelligence crucial to national security, assist conventional military operations, and even create kinetic effects to achieve strategic goals. To make a cyber operation possible, one must have the capacity to break into a particular system. I want to repeat that because this is where the whole thing turns. To make a cyber operation possible, one must have the capacity to break into a particular system. Offensive cyber capacities, and particularly zero day vulnerabilities are the necessary strategic resources required to conduct such operations. In other words, that's it, that's what we need. That's the future zero days. We need them, she writes. The United States clearly wishes to further leverage its cyber prowess in the international arena, particularly against the People's Republic of China. Doing so would help the United States protect its vital national security and economic interests, international partnerships and norms. However, to operationalize a cyber power strategy, the United States must acquire enough high end capabilities to ensure it can achieve such strategic goals. Moreover, the timeline for implementing these policies is urgent given the increasing potential for conflict with China in the coming years. Thus, given the international privatized offensive cyber capability marketplace. Let me say that again. Given the international privatized offensive cyber capability marketplace, how can the United States and its allies continue to ensure the availability of offensive cyber capabilities? She says, focusing on zero day vulnerabilities while limiting China's access to those same capabilities. In other words, we want to buy them, we don't want them to be able to buy them. Cyber operations consists, she writes, of a variety of offensive cyber capabilities. Many of the most crucial cyber capabilities involve the exploitation of zero day vulnerabilities, also known as zero days or O days zero day vulnerabilities. And I'm repeating, we all know this, but I'll just just to set the context, zero day vulnerabilities are issues or weaknesses, bugs in software or hardware typically unknown to the vendor and for which no fix is available. In other words, the vendor has had zero days to fix the issue. Some of these vulnerabilities are exploitable. An actor with knowledge of the vulnerability could write code that takes advantage of said vulnerability. This results in a zero day exploit code enabling a range of behaviors that could include establishing access into the computer system the software is installed on, escalating privileges on those systems, or remotely issuing commands you could tell this woman knows of what she speaks and she was after all, In Google's exploit world, the work of finding vulnerabilities and writing exploits, thanks to its strategic necessity to governments worldwide, has become get this. The work of finding vulnerabilities, writing exploits, thanks to its strategic necessity to governments worldwide, has become a billion dollar international services industry in the last 20 years. During this podcast, a billion dollar international services industry has appeared selling exploits to governments, she writes. Private firms now often create cutting edge offensive cyber capabilities for governments. Given the sensitivity around supporting government cyber operations, many of these firms do not openly advertise their services, shrouding the industry in secrecy. Between this secrecy and the variation in products offered, for example, governments target different technology systems and no 20 days are identical. The supply chain for such capabilities is not only opaque to outsiders, but also to governments and even among players in the industry. Within this highly fragmented and opaque market, large firms like The United States, L3Harris or Mantech frequently hold multimillion dollar valuations. Notably, Israel's NSO group's worth reached $1 billion at its peak. Meanwhile, individual US government agencies receive millions of dollars to procure offensive tools. Such company's tools have clearly been purchased by such government agencies and put to use in modern day cyber operations. Notably, of all the zero day vulnerabilities found exploited in the wild in 2023 and 2024 by Google, around 50% of them were attributed to commercial vendors that sell capabilities to government customers. Again, half of the zero days that Google found through 2023 and 2024 are directly attributable to commercial vendors selling them to government customers, she says. While this statistic only encompasses detected zero day exploits, this is still a significant set of capabilities being provided by private sector actors private companies selling to government customers, she says. The offensive cyber capability industry itself is international and ranges in professionalism depending on the region. Companies in Russia, Israel, Spain, Singapore and the United States all have varying relationships with their home governments, other firms including middlemen and brokers, international government customers, and even cyber criminal groups. However, the study of offensive cyber capabilities has largely over indexed on firms based in Israel and Europe rather than the United States greatest political rival, China. This is surprising as the Chinese hacking and cybersecurity ecosystem is robust. Chinese companies have on multiple occasions been directly linked to Chinese government sponsored cyber operations against the United States. Moreover, the development of offensive cyber capabilities in the United States remains largely unstudied or examined in a way that does a disservice to the domestic hacker community. In other words, she just said, what I keep talking about on this podcast is that what's going on here, we don't ever see anything right? She asks. Why is this question important? At first glance, it can be difficult to see why the private sector zero day exploit market, a series of obscure companies selling code that can enable governments to break into widely used software, would be important in preserving national interests in cyberspace, particularly against China. A simple explanation of this relationship is as follows. The United States and its allies rely on an increasingly digital world, and China is both a savvy adversary and a hardened target in cyberspace. When any country's intelligence community wishes to infiltrate high value, hard to access digital targets, it likely must use zero day exploits or other bespoke, in other words, custom made or tailored offensive cyber capabilities. Intelligence organizations from both the United States and China, due to decreasing internal supply and rising demand for such capabilities, have increasingly relied on acquiring such exploits from the private sector zero day exploit market. However, the private sector zero day market is murky and more international than policymakers expect. Even if the United States and China are truly entering a new cold war, both countries cyber capability firms and cold war both countries still Sorry, both countries still source these capabilities from an overwhelmingly opaque and international market of offensive cyber capability firms and do not know if they are being supplied with potentially overlapping capabilities. In short, any cyber operation that relies on an acquired capability conducted by the United States, China, or anyone else carries a counterintelligence and operational security risk with no guarantee that that they can source a similar capability in the future. Thus, securing the cyber supply chain, which means understanding the industry, constraining malicious actors, and ensuring availability from trusted parties is important to address such risks. While former President Joe Biden's administration sought to constrain private sector actors with additional regulations and placing bad actors on the enemies list, these policies were framed around human rights concerns, largely out of Europe and Israel. President Donald Trump's administration is moving away from this approach, focusing on China as a geostrategic threat over transnational digital repression framings, as well as signaling willingness to engage with private sector actors in the space. The Trump administration as of 2025 has accelerated plans for a U.S. cyber Command 2.0, focusing on working better with private industry partners. This is a continuation of the first Trump administration's policies. Trump was the first president to delegate the authority for offensive cyber operations down to the Secretary of defense, allowing U.S. cybercom more leeway to conduct operations without presidential approval, albeit still with a re with a robust interagency review process and finally, if the United States wishes to further leverage its cyber prowess in the United in the international arena by leveraging private sector partners, does it have the supply chain and acquisition capabilities to back it up, especially if its adversary is the People's Republic of China? Although the author does not condone general analogies between cyber and other domains, supply chain and acquisition analysis in the cyber domain can be similar to nuclear or other arms proliferation. For example, to answer whether a country has the capability to construct a nuclear weapon, one must understand how much enriched uranium the country can easily acquire. Similarly, she writes, to answer whether a country can become a cyber power that can access the hardest of digital targets, one must ask how easily it can source and acquire Zero days and other offensive cyber capabilities. So Winona made assertions in a lot of assertions and what I just read. In nearly every case those assertions were followed by a reference in her text to their source. So none of this was just her opinion, regardless of how well informed it may be. So we have a somewhat bizarre new world where governments need to purchase newly discovered zero day vulnerabilities from anywhere they can be purchased, and where the anywhere they can be purchased is an entirely ad hoc mishmash of entities from someone in their mother's basement to an international weapons dealer or a public government contractor. If we were to extend Winona's uranium acquisition analogy a bit, this would be analogous to tens of thousands of individuals, each with their own little backyard uranium enrichment operation, who then sell what they've created to the highest bidder or to someone they trust. She offered some interesting numbers to give us a sense of scale of what's going on today, she wrote. Live hacking competitions where hackers hack into systems live on stage and bug bounty programs, usually company run reward programs that encourage hackers to find and report system vulnerabilities, enable hackers to develop similar skill sets as those required for government sponsored hacking. These programs and competitions are both common recruiting pipelines for defensive cybersecurity companies and offensive vendors alike. Common recruiting pipelines, she said. The number of individuals that participate in such programs globally is staggering. In 2020, HackerOne, a well respected bug bounty program, reported around 600,000 contributors spanning 170 countries. A 2024 survey of bug Crowd, one of the largest bug bounty and vulnerability disclosure companies on the Internet, revealed Most of bug crowd's over 200,000 hackers hailed from India, Egypt, Nigeria, Pakistan, Nepal, Vietnam, Australia and the United States. 78% of them are self taught, 78% are self taught and 58% of them were under 25 years old. While not all of these individuals possess the skills to find zero day vulnerabilities and write code to exploit them, multiple security experts interviewed estimated that there are likely thousands of international individuals able to do so, with numbers in the low hundreds that could be trained to do so well. Okay, so we have an informal community of hackers who are potentially able to make a bunch of money, but as the saying goes, don't quit your day job. Winona provides some interesting background to that writing. While selling offensive cyber capabilities, and particularly zero day vulnerabilities to governments is a lucrative profession, it's a risky industry. Creating a zero day exploit to leverage against a widely used technology product may require between six and 18 months of full time engineering and research work. Unless an offensive cyber capability firm has multiple engineers working on different products or uses different payment schemes teams, meaning salaries, this timeline can lead to long down times between exploit sales. And this is what she means when she says this feast or famine payout schedule carries risks for companies that rely on one or two windfalls a year to pay their overhead and engineering costs. In addition, finding a customer to sell exploits to is more difficult than it first seems. In general, potential sellers must find an existing government contract through which to sell their exploits or know the right government individual to speak with. Unless an offensive cyber capability firm has hired employees who've recently left a government interested in such capabilities, actual buyers may be extremely hard to find. Thus, international hackers without former former government connections normally sell their products to middlemen, many of whom operate internationally like Zerodium. Right. We've talked about Zerodium a lot in the past. You know the. This is exactly that. Even then, the exploit may go through multiple levels of middlemen to get to a government customer. This frustrates both buyers and sellers. Buyers know that exploits sold to them have extremely high markups given the number of middlemen involved, and often will not know who the original bug producers are. Meanwhile, the sellers are likely aware of the extreme markups, but they don't know whether their bugs were sold to multiple governments. So she she quotes a former official with the with the Office of the National Cyber Director saying an individual researcher who is not informed on what bugs are selling for may sell a good bug for $100,000. By the time it makes it to a customer, an individual bug could go for 750,000 to $1 million. And a senior this was this is the National Cyber Director saying this And a senior DoD official working on offensive cyber security research programs who thus knows exactly what he's talking about says quote, the system by which zero day vulnerabilities are acquired is horrendously inefficient and broken. Okay, so we learn that there is a system of middlemen who are not contributing anything meaningful beyond their connections and contacts within government. And they're almost, and they almost certainly owe their loyalty only to the dollar, not to any nation. Nothing prevents them from double dipping. We know that money motivates. So if a program existed to cut out the middlemen, to protect hackers legally and to allow governments to purchase those vulnerabilities directly, hackers could be making 10 times the money and have 10 times the motivation. They would also have the assurance that their work would only go to help the company they the country they wish to help and not their country's enemies. The problem is that there's a well deserved prevalent mistrust of government within the hacking community. Winona reminds us of a bit of this past writing. Undermining all these efforts is the anti government sentiment that remains Strong within the U.S. cybersecurity and hacking community, which likely contributes to difficulty in maintaining an offensive talent pipeline. Much of the original US hacking community emerged from countercultural activities like phone freaking, she says in Parens I. E. Bypassing Pac Bell telephone lines to make long distance phone calls without paying. She said law enforcement responses from the 1960s to the early 2000s treated many hackers as criminals rather than as innovators. In in 1990, the Secret Services Operation Sun Devil seized more than 40 computers and 23,000 data disks from teenagers in 14American cities and charged individuals who managed the hacker magazine FRACK with interstate transport of stolen property. The charge was based on information published by FRACK that later proved to have already been widely publicly available. The arrests and subsequent court cases resulted in the creation of the Electronic Frontier Foundation. While the US government has made significant strides toward repairing their relationship with domestic hackers in recent years, anti government sentiment still persists. And of course Leo, we all remember our friend being arrested and handcuffed at the at at McLaren in Las Vegas as he was leaving, you know, trying to go back to England.
- [174:23]
Leo Laporte
So we also remember the wonderful scene in Goodwill hunting where Matt Damon is. They attempt to recruit Matt Damon to the NSA and you know, he has a fairly good cogent reason why he would never win work for the nsa. Y so I, I recommend that if people haven't watched the movie, I wish I could play the sound, but I don't want to get taken down.
- [174:43]
Steve Gibson
It's a great scene yeah, so yeah, Uncle Sam, you've been a big bad bully in the past and now you want and need the brains of those people whose rights and freedoms you blithely ignored out of your own fear of the unknown. Not cool. There is so much content in this fantastic 44 page paper that I've had to skip over. So all I can do is commend this to any of our listeners who are interested in knowing more. The paper goes into much more depth about the many significant challenges presented. By the way the US is organized versus the comparative ease that China's processes face. So anyway.
- [175:31]
Leo Laporte
Well, also they have a kind of compelling regime. You don't think you have a lot of choice. Yeah, right. By the way, I don't know if you saw it last night one of the Chinese nationals associated with Salt Typhoon was arrested in Italy and the US is seeking extradition. So that will be interesting to follow.
- [175:51]
Steve Gibson
So we come away with a much better appreciation for what's going on out in the world of offensive warfare. Offensive Cyber warfare is 100% about penetrating into one's perceived adversaries networks. That's it. And in turn that's all about leveraging exploitable zero day, which is to say currently unknown vulnerabilities that exist in the devices attached to that network. What's really interesting is, is that there's an inherently level playing field when it comes to discovering these potentially ultra valuable zero day exploits. I would like to be seeing hackers getting paid much more and not having this, you know, lining the pockets by huge, you know, factors, huge multiples of the middlemen. Anyone anywhere can make a discovery of a flaw in software, then work to engineer that into a working exploit. And we heard more than half of the, what is almost 3/4 are self taught and more than half of these of these hackers are less than 25 years old. @ that point when you've created a working exploit, the holder of that intellectual property has has an asset worth potentially a million dollars, but only if that intellectual property can be conveyed to a deep pocketed government that in turn has the means to exploit it for its own ends. Today, opportunists who may provide some value, such as mutual anonymity for both the buyer and the seller are taking the lion's share of the value for a hacker's work because only they are able to turn that highly valuable and volatile intellectual property into cash. Hackers who receive only 10 cents on the dollar are much less incentivized to hunt down tomorrow's exploit. Yet what we have learned is that offensive cyber warfare is all about having that next exploit. It's called a supply chain because it creates a supply and that's what it needs to do. It's clear that the US government itself needs to emerge from the shadows. It needs to become a well advertised, high value, explicit buyer of zero day exploits. It has to stop being ashamed or embarrassed by that. It needs to put the middlemen out of business. It needs to provide irrevocable protection to any hackers against any form of blowback for their work in discovering valuable cyber attack tooling. It needs to be widely known that it's possible to become wealthy from selling zero day exploits to Uncle Sam. This is not the world I wish we had, but it's today's reality. If having a strong deterrent helps to keep the peace, then let's get one.
- [179:08]
Leo Laporte
Yeah, yeah. I mean, I think there's also been some reluctance on our part to escalate cyber warfare because what, what happens when you escalate is you escalate.
- [179:21]
Steve Gibson
Yeah, you get, you get a reaction.
- [179:24]
Leo Laporte
But it's being escalated with or without us. So.
- [179:26]
Steve Gibson
Yes, it's happening either way.
- [179:29]
Leo Laporte
Yeah, yeah.
- [179:30]
Steve Gibson
And, and there is this notion too, if we can maintain an inventory. The problem with Zero Days is that they're volatile. We have, we have, we have seen many instances. In fact, we just covered them on that most recent pwn to own where the hackers believe they had zero days, but those just had not yet been updated Right. From the vendors.
- [179:53]
Leo Laporte
Well, there's also the problem of once you use them, you've burned them.
- [179:56]
Steve Gibson
Yes.
- [179:57]
Leo Laporte
So you need many.
- [179:59]
Steve Gibson
Yes, exactly. They are consumables.
- [180:03]
Leo Laporte
The good news is there seems to be an unlimited supply.
- [180:08]
Steve Gibson
Isn't that bizarre? It's just amazing. Even Apple, with all the work Apple has done.
- [180:14]
Leo Laporte
Yeah, you'd think we'd have fixed it by now. But you know, perfect software and all of that, but I guess not. That's Steve Gibson, ladies and gentlemen. He writes Perfect Software, the world's best mass storage maintenance, performance enhancing and recovery utility. It's known as Spinrite. He writes it in assembly language. So it's fast, it's small, and you can get it from him directly@grc.com Just finished version 6.1. I'm gonna bet on the fact that it took a little while for 6.1 that we shouldn't worry too much about 7.0 yet.
- [180:51]
Steve Gibson
I have some other things to do first.
- [180:54]
Leo Laporte
I think it might be a little while. So get it, get it right now. If you don't already have it@grc.com while you're there. There's plenty of other things to do, including download copies of this show. Steve's got all the his versions are unique. All of them. We don't overlap at all anymore. He has a 16 kilobit audio version which is a little scratchy but has the virtue of being small. He has a 64 kilobit audio version which is a little bit bigger but sounds pretty much perfect. We do for some reason, 100. Well, I know the reason, but it's complicated. 128 kilobit audio at our site. So if you want the smaller audio versions, go to Steve's site. He also has the transcripts written by Elaine Ferriss. She does a great job with those. The show notes are there. Actually. You could get those show notes mailed to you ahead of time. Steve has a mailing list for show notes and a much less frequent mailing list for new product ideas and things like that. We're waiting for the DNS benchmark Pro to come out and that'll be the next email you'll get from Steve. If you want to sign up for that and get your email whitelisted on Steve's server, go to grc.comemail grc.comemail but remember, when you enter your email address, you still have to check those boxes for those newsletters because. Because Steve's an opt in kind of guy. We have video at our website, 128 kilobit audio, but also video at Twit TV SN. There's also when you get there, you'll see a link to a YouTube channel. A great way to share clips. If you see something, you think, oh man, I got to tell the IT department about this or the boss should know or whatever. Or maybe you like our advertisers so much you want to send that to your boss. It's easy to clip on YouTube and everybody can play back a YouTube video. You may also. In fact, I think probably this would be the best way to get the show subscribe in your favorite podcast client. Whether it's pocket casts or ipods or Apple's itunes, I should say, or Google's or whatever it is that you use to get podcasts subscribe and that way you'll get it automatically. You won't have to think about it. Audio or video, your choice. Mmm. When you do go to those sites, if they allow reviews, please do us a favor. Do Steve a solid and leave a five star review. Let the world know how Great. Security now is if you are in the club. Well thank you. First of all, your membership supports everything we do, including this show. It's 25% of our operating expenses come from our club Twit members. So you guys are golden. You get access to the Discord. You get a special video feed just for you. You also get special programming. We're going to do our AI users group on Friday. Chris Margaret's photo group coming up as well our science fiction book club. A lot of great stuff in the club. Only find out more at Twitt TV Club. Twit Club members, as I said will watch Inside the Discord on that feed. But there are seven other ways you can watch live Every Tuesday right after Mac break weekly 1:30 Pacific. That's 4:30 Eastern Time 20:30 UTC. We stream on YouTube, Twitch, tick tock, Facebook, LinkedIn, X.com and kick seven different places you can go to watch the show live that way but you don't have to watch live, download it or subscribe. Whatever works for you. Do all of them do all of the above Steve have a wonderful week and we will see you next week right right here.
- [184:25]
Steve Gibson
We'll do I will probably have finished Hail Mary and Beyond to Artemis by then. So good.
- [184:30]
Leo Laporte
I'd love to get your your thought thoughts have my report. In hindsight I really liked it. It just was different.
- [184:38]
Steve Gibson
Not yeah yeah hard to hard to follow the Martian. No kidding. That was uniquely good. Thanks my friend. Next week.
- [184:49]
Leo Laporte
Security now. High interest debt is one of the toughest opponents you'll face unless you power up with a SOFI personal loan. A Sofi personal loan could repackage your bad debt into one low fixed rate monthly payment. It's even got super speed since you could get the funds as soon as the same day you sign. Visit sofi.com to learn more. That's s o f I.com p o w E R Loans originated By SoFi Bank NA Member FDIC Terms and conditions apply NMLS 696891.