← All TWiT.tv Shows (Audio)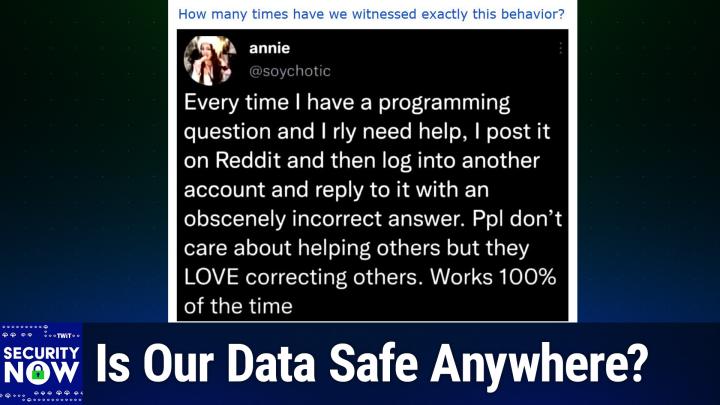
All TWiT.tv Shows (Audio)
Security Now 1036: Inside the SharePoint 0-day
02:58:21
Is Our Data Safe Anywhere?
Loading summary
Transcript227 lines
- [00:00]
Leo Laporte
It's time for Security now. Steve Gibson is here. He's decided to change his browser of choice. He'll explain why. We'll also talk a little retraction. Passkeys are still secure. Fido's passkey was not bypassed by a man in the middle. And then we're going to take a look, a deeper look at that SharePoint Zero day. What a nightmare. All that more coming up next on Security Now. Podcasts you love from people you trust. This is Twit. This is Security now with Steve Gibson. Episode 1036 recorded Tuesday, July 29, 2025, inside the SharePoint Zero day. It's time for Security Now. Oh, I know you're so excited. I see people jumping up and down. We wait all week for. And the arrival of. It's the Santa Claus of security, Mr. Steve Gibson. No beard, but a very nice mustache. Hello, Steve.
- [01:07]
Steve Gibson
People are jumping up and down. I think that's the vertical hold. Remember those days, Leo?
- [01:14]
Leo Laporte
Oh, yeah. You try to see between the lines on the encoded channels. You go, what's going.
- [01:18]
Steve Gibson
Well, you had knobs on your TV and you had to. And those tweaked the frequency of oscillators, which caused the, the, the cathode ray tube beam sweep frequency to change so that it had to line up with what was being sent from central headquarters.
- [01:37]
Leo Laporte
Can you imagine being married to Steve Gibson and you're trying to get the TV to work and he says, well, you know, it's the oscillator that needs to line up in there. Oh, yeah, yeah. You know, it's funny. Somebody's been uploading. I'm thrilled. These old screensavers shows you and I did back in 25 years.
- [01:53]
Steve Gibson
I have every one of them.
- [01:55]
Leo Laporte
Maybe it's you. You have them. Oh, the ones that you were on. You have. But there are, there are literally hundreds and hundreds of. Yeah, somebody must have put them on VHS. I know because I'll, I'll watch them on YouTube. And you see the.
- [02:08]
Steve Gibson
Or. Or the bottom of the screen.
- [02:13]
Leo Laporte
Immediately. Oh, yeah, I remember that from the, the bad old days. All right, what's coming up on Security now today?
- [02:20]
Steve Gibson
So for episode 1036 for this last podcast of July of 2025, we're going to talk about a mess.
- [02:33]
Leo Laporte
Of course.
- [02:33]
Steve Gibson
What else? It's a complicated mess which most of the press hasn't quite locked on to. They haven't groked it fully because the. This actually is a descendant of something we talked about in May. Remember that in May was the first relocated pone To Own competition. Normally it has traditionally been held in Toronto every year. This was the first time that Pone to Own had moved to Berlin. One of the. One of the winners, who earned himself $100,000 in Berlin's Pone to Own in May revealed a. A remote code execution exploit in Microsoft's SharePoint servers, which. Oh my God, you know, there's 38, 000 of them I think online at the moment. And so this is not SharePoint in the cloud where Microsoft is trying to push everyone because of course they would love to have a subscription from everybody. But these are people who have previously before Microsoft decided they wanted to get everyone to subscribe to everything would sell you a server. And so there's SharePoint 2013 and 15 and 16 and 19. And they're just doing fine installed in enterprises everywhere. Unfortunately, it turns out they all have a very bad bug which Microsoft tried and failed to fix in this month's patch Tuesday.
- [04:20]
Leo Laporte
Oh boy.
- [04:21]
Steve Gibson
They bungled the update once again, patching the symptom, not the cause.
- [04:29]
Leo Laporte
And that's an AI thing. I bet they did an AI patch. That's exactly what they are.
- [04:34]
Steve Gibson
Well, you wouldn't take AI because we know they were doing this years ago, before AI. There's, you know, they just don't really care is what it really looks like. They, it's like, oh, look, you do this and this happens. So let's put, let's put a little jump instruction in there or something like, so they're not fixing the underlying problem, they're just, you know, making what the, what, what the security guy showed them in the proof of concept could happen stop happening. Anyway. Oh, Leo, what a Mess. At least 400 enterprises have been compromised.
- [05:13]
Leo Laporte
Got to be more than that. Some of the government even. Yeah.
- [05:16]
Steve Gibson
Yes. Anyway, so the good news is much as I've just said, there's a lot more to say. So we'll be getting to that. We're going to talk about the Brave browser randomizing fingerprints. The Brave, the next version of the Brave browser blocking Microsoft recall by default in keeping with its, you know, its approach. Clorox, you know, the famous bleach company, they are suing their IT provider for, whoa, $380 million in damages.
- [05:51]
Leo Laporte
What?
- [05:52]
Steve Gibson
Huh. And we're going to talk about, about like the backstory there. We also have the, that six month offer for Windows 10 users to extend their security patches. Those offers are beginning to appear. Some interesting stories demonstrating that warfare has really significantly turned to cyber. The Allianz insurance company, Alliance Life has lost control of 125 million of its customers data.
- [06:25]
Leo Laporte
That's almost all of them. And by the way, I'm one of their customers, so I'm thrilled about this. Yeah.
- [06:31]
Steve Gibson
And was it they who waited a year? I don't know. I, I there. We got a lot to talk about here. We also had the CIA's Acquisition Research center website being hacked and I think, I think I know how, but the Pentagon says that the SharePoint RCE didn't get them. Although again, the gal, Katie, I think her name is, didn't seem to quite understand what exactly happened here because she's like, oh, don't worry about it. Also, we actually get a photo of a dprk, you know, North Korea laptop farm which is being used to impersonate Americans. Turns out that fido's passkey was not bypassed by a man in the middle. We reported it was last week and I raised the question, is our data safe and anywhere I coming to think no, it's just, you know, I don't want to give up. But still, the UK is now trying to backpedal out of Apple's ADP mess that it got itself into. Meanwhile, the EU resumes its push for what's called chat control. And then we're going to take a deep dive into what happened after Microsoft fumbled its patch of, of this very powerful pwn to own discovered exploit. So lots to talk about and we've got a, I think a picture of the week that a lot of our listeners are going to get a kick out of. I know that it rang true for me. So I think maybe Leo, this time we finally got the hang of how to do this podcast.
- [08:10]
Leo Laporte
10:36 episodes later, we finally figured it out.
- [08:14]
Steve Gibson
We're going to, maybe we're going to.
- [08:15]
Leo Laporte
Have a good one. Yeah, I'll tell you, I have not looked at the picture of the week. You will get my raw, unadulterated reaction.
- [08:21]
Steve Gibson
You're gonna, you're gonna this, this is gonna, you're gonna go. Huh? You're gonna get it.
- [08:26]
Leo Laporte
Hey, thanks to Adam Puckett who just shared a little bit of filthy lucre. Ten bucks. Thank you, Adam. I appreciate it. In our YouTube chat, we are streaming live, as Adam knows, on YouTube and X.com and TikTok and Facebook and LinkedIn and Kick, your favorite kick. And of course in our club, Twit Discord. So if you're watching live, we'll see you in the chat room. We're glad you're here. We appreciate it. Our show today brought to you by the thinxt Canary figure I can show you. This is the cute little device. You know, it looks about the size of a. I don't know. See, it's about as big as my hand. It's like an external USB drive. But this thing, simple connection, just an ethernet port and a power connection.
- [09:08]
Steve Gibson
This.
- [09:08]
Leo Laporte
This thing though, could be almost anything. It is a honeypot that can impersonate just about anything. And the thing is, that's great. It doesn't look like some sort of vulnerability to a hacker in your network. It looks like it's super valuable. Thinks canaries are honey pots that could be deployed in minutes. If someone's accessing your lore files or brute forcing your fake internal SSH server, fake, mind you, then ThinksCanary will immediately tell you you got a problem, you've got a malicious insider or a bad guy inside your network. No false alerts, just the ones that matter. Let me show you my configuration page. This is for our things Canary and the one I just showed you. This attic on my studio desk right now is a Windows Server 2019 Office file share. And when I say that, I mean it's. It's even got a Mac address tied to Microsoft. It looks, for all intents and purposes to be a Windows file share. Furthermore, look, I opened supports, I got an RDP port open, I got file sharing. I love opening Port139. That attracts a lot of bad guys. But it doesn't have to stay that. It's so easy to configure and make it be almost anything you want from IIs to. Yes, SharePoint 2010. That should be a nice thing to just turn that on, see what happens. It could be Linux. It could be a Mac OS 10 file share. It could even. For crying out loud, it could even be a skated device of a sofa firewall. It could be a Rockwell Automation plc. You choose a personality or make a custom personality. You can light it up with all the services in the world or just pick a few juicy services. Then you just sit back and wait. And a bad guy or a malicious insider who's in your network cannot resist it. And the minute they log in, you'll know. By the way, the other thing thinks canaries can do is these tripwires. They call them canary tokens. You can create canary tokens that look just like, well, almost anything. A credit card, an API key, a Microsoft Word or Excel document. It could be a wireguard configuration file. I mean, the sky's the limit. The wonderful thing is the minute somebody tries to Access this, you will immediately get notified. Somebody's trying to use that fake credit card you created. Stick those Canary tokens anywhere on your network. Including, by the way, I keep a few in our cloud servers, on our Google Drive and other places. Because again, bad guys just can't resist them. They're like candy to the hackers in your network. It turns out that it takes companies, on average 91 days before they realize somebody's in their network. This is the problem. You've got all those great defenses, but how do you know if somebody's penetrated them and is wandering around, thinks Canary will tell you? No false alerts, just the alerts that matter. Visit Canary Tools Twit. Some big banks might have hundreds, maybe I don't. Nobody has thousands. Maybe they're on all seven continents, including Antarctica. Apparently, they are everywhere. In business, in government. They taught. For years, they taught governments and companies how to break into computers. So they know exactly how the bad guys think. But also they're security experts and they've made sure that this thing is bulletproof. You're not putting anything vulnerable on your system. You're just putting something that looks valuable that a hacker cannot resist. Let's say you want five of them. That's a. That's typical for a business our size. Small business, you know, one, you certainly would want one on every network segment. Go to canary tools/twit. $7,500 a year gets you five things to Canaries. You get your own hosted console. You get upgrades, you get support, you get maintenance. And by the way, if you use the code Twit Twit and the how did you hear about us? Box, you'll also get 10% off. And not just for the first year, but for life. You can always return your thinkscanaries. They have a two month money back guarantee for a full refund. I do have to tell you, during all the years Twit has partnered with ThinksCanary, their refund guarantee has never been claimed. Visit Canary Tools Twit. Don't forget that offer code, Twit. Put it in the how did you hear about us Box. And man, you really need these. Go get yourself some Canary Tools Slash Twit. I'm going to give him a new slogan. It's the easy way to honey pot. Not a great slogan, but there it is. Okay, Mr. G, I'm ready. I will scroll up the picture of the week.
- [13:58]
Steve Gibson
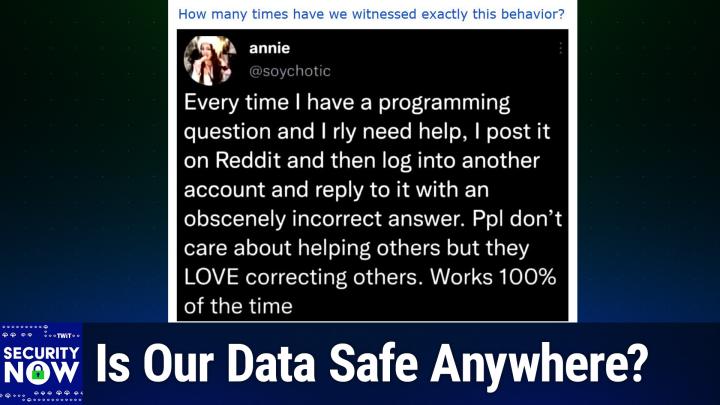
So I gave this picture the caption. How many times have we witnessed exactly this behavior?
- [14:06]
Leo Laporte
Okay, I'm going to scroll up and this will be me seeing it for the first time.
- [14:10]
Steve Gibson
You read it silently to yourself. And then I'll tell everybody it's a.
- [14:13]
Leo Laporte
It's like a tweet or something. Okay, yeah.
- [14:21]
Steve Gibson
That'S brilliant, isn't it?
- [14:24]
Leo Laporte
And all right, I'll let you describe it.
- [14:25]
Steve Gibson
So true.
- [14:26]
Leo Laporte
So that is so brilliant.
- [14:28]
Steve Gibson
This is a snapshot of a tweet from Annie, whose handle is at so.
- [14:35]
Leo Laporte
Iotic, which is a great handle, by the way. She's obviously very creative.
- [14:38]
Steve Gibson
Psychotic. So Annie posts every time I have a programming question and I really need help, I post it on Reddit and then log into another account and reply to it with an obscenely incorrect answer. People don't care about helping others, but they love correcting others.
- [15:05]
Leo Laporte
Oh, they do.
- [15:06]
Steve Gibson
She said. Works 100% of the time. And. And I've seen this happen, too. Somebody, they'll just be like this lonely posting on some programming forum that nobody replies to. It's just there, you know, useful question. But nothing happened because people, you know, they just look at it and go, but, oh, boy. You post a wrong answer and there's a. Everybody piles on. It's a feeding frenzy correcting this person who doesn't know what they're talking about.
- [15:37]
Leo Laporte
You're going to get the reply, guys, in spades.
- [15:40]
Steve Gibson
Yes, a little bit of brilliant reverse psychology there is like, here's the answer. It's like, no, that's not right. Here's what's right. It's like, okay, okay.
- [15:49]
Leo Laporte
So, right.
- [15:49]
Steve Gibson
Anyway, I already got some great. The email went out to 18,121 people yesterday. Wow. Around this time. And a bunch of our listeners replied saying, yep, seen that myself, and I think several of them are going to adopt it now as their standard practice and they're looking for a reply. So, okay, before I forget, as I did last week, because this was two weeks ago, I wanted to acknowledge all of our listeners who wrote to let me know that the Brave web browser that deliberately randomizes its browser fingerprints, that is the fingerprints they're using, as reported by EFF's excellent cover your tracks online testing facility, which we talked about a couple weeks ago. So for anyone who may have been a little unnerved and disturbed by the fact that in my case, neither UBLOCK Origin nor Privacy Badger, both which I was using in Firefox, were of any help in that regard. The. I know we went through all of the bits of significance that that they. That the EFFS cover your tracks site was able to glean from running script on my browser to lock me down. And I was what, one I. I was unique among 244 some thousand browsers that they'd seen in the last 45 days. So the Brave browser looks like the right answer for that. And that's a screenshot I have in the show. Notes says blocking tracking ads. Yes. Blocking invisible trackers. Yes. I had both of those on Firefox. Protecting you from fingerprinting? No. And that's where for me it said this browser is unique. So if you're using Brave and you go to the COVID your track site, it says your browser has a randomized fingerprint. So thanks to our listeners, I wandered over to the Brave browser site to look around, and when I saw that the browser natively supports vertical tabs, that clinched the deal for me. I have made the switch to Brave. So we'll see how that goes. I'm not nearly as fickle as Paul Thurot, who changes browsers, you know, as often as he changes his pants, but I know I I've been using Firefox forever. As our listeners know, I'm now using Brave. So I've been very impressed with everything I've seen. One thing that I immediately checked was one of my enduring annoyances with with Firefox, which on windows Is it 10 or 7? I'm not sure which, maybe both. Anyway, it has this ridiculous refusal to allow me to simply drag a URL from the browser's URL bar into a Windows Explorer folder or to the desktop. I know that it won't let me do it under Windows 10. I'm not sure about Windows 7. Day before, on Saturday, I needed to save some URLs, so I was forced to copy the URL from Firefox over into Chrome, paste the URL into Chrome, then drag and drop the URL from Chrome into Explorer, which Chrome allows me to do. I understand this is a security measure, but guys, please allow me to turn it off if it's interfering with my workflow, as it continually does. I've looked into disabling this nonsense. There is a way. Mozilla knows about this. There's a way to turn that off. You're supposed to be able to append to the command line that launches Firefox the option no hyphen delevate because what's happening is Firefox's authorization, it's security privileges are being deliberately de elevated to protect the user from things that the browser might try to do if something malicious gets a hold of doesn't work for me. Apparently because there's also some interaction with with my desktop's UAC settings. I'm sometimes annoyed by Microsoft also being overly protective because I know how to use Windows. So anyhow, whatever the case, the bottom line is that the protection Firefox believes it's providing to me is not worth the hassle of not being able to simply drag and drop the URL of a page that I'm at into a folder. And neither Chrome nor Brave similarly harass me. So I imported my Firefox settings into Brave. That worked flawlessly. It allowed me to turn off the unnecessary title bar up at the top. Of course I had to re authenticate to Bitwarden and re log into a few title a few different sites. But I'm up and running now with Brave and I'm happy. So anyway, and I the more time I spent looking around Brave site, the more impressed I was about their philosophy and their approach. And boy, if you look at the list of things that they tweak from the Chromium which which Google uses, they've done a lot in order to bravise the common open source Chromium browser template. So anyway, I'm liking a lot so far. And by pure coincidence, a piece of welcome news regarding the Brave browser surfaced last week. I sure I would have shared it with everybody even if I hadn't become a Brave user myself. Anyone who might have been curious about Brave's stance on Microsoft Recall would have their curiosity satisfied by the headline which read Brave blocks Microsoft Recall by default. They wrote starting with version 1.81 and the world is currently at 1.80. That's what I have under Windows 10. So starting with version 1.81 for Windows user so it'll be the next update. Brave browser will block Microsoft Recall from automatically taking screenshots they wrote of your browser activity. They explain Microsoft first announced Recall in May of 2024 and immediately drew fire from security and privacy advocates. Recall saved full screen screenshots every few seconds and stored them in a local plaintext database, leaving it open for exploitation by anyone, including malware, who had access to the machine. The outcry caused Microsoft to hastily roll back the feature and rework it significantly. A year later, Recall is back and Brave is ready for it. We will disable it by default for Windows 11 and beyond users with a toggle to turn it back on for users who really want Recall, Microsoft has to their credit, they wrote made several security and privacy positive changes to Recall in response to concerns. Still, the feature is in preview And Microsoft plans to roll it out more widely soon. What exactly the feature will look like when it's fully released to all Windows 11 users is still up in the air. But the initial tone deaf announcement does not inspire confidence given Brave's focus on privacy maximizing defaults. And what is at stake here, they said, parens your entire browsing history. We have proactively disabled Recall for all Brave tabs. We think it's vital that your browsing activity on Brave does not accidentally end up in a persistent database, which is especially ripe for abuse in high privacy sensitive cases such as intimate partner violence. Wow. Okay. They said. Microsoft has said that private browsing windows on browsers will not be saved as snapshots. We've extended that logic to apply to all Brave browser windows. We tell the operating system that every Brave tab is private, so Recall never captures it. This is yet another example of how Brave engineers are able to quickly tweak Chromium's privacy functionality to make Brave safer for our users. And then they provided a list with. Which is what I referred to earlier, which is just astonishing. I mean it scrolls. It's just all these things they've done, they said. For more technical details, see the GitHub issue for this feature. Brave is the only major web browser that disables Microsoft Recall by default in all tabs. And they finish by saying we were partly inspired by signals blocking of Recall. Given that Windows does not let non browser apps granularly disable Recall Signal cleverly uses the DRM flag on their app to disable all screenshots. This breaks recall but unfortunately also breaks the ability to take any screenshots including by legitimate accessibility software like Screen Readers Braves approach does not have this limitation. Since we're able to granularly disable just Recall regularly screen. Regular screenshotting will still work, they said. While it's heartening that Microsoft recognizes that web browsers are especially privacy sensitive applications, we hope they offer the same. I'm sorry. We hope they offer the same granular ability to turn off recall to all privacy minded application developers. So, you know, I don't know if I coined the. The phrase the. The phrase which I'm now.
- [26:48]
Leo Laporte
What could possibly go wrong?
- [26:50]
Steve Gibson
No, the tyranny of.
- [26:53]
Leo Laporte
The tyranny of the default. You did not coin that. That's been around for a while. Yeah.
- [26:57]
Steve Gibson
Anyway. What wonderful. You know I've been saying it for at least 20 years because I may have. Because I. I mean it has been. It was one of. I. Maybe it was a. You know, TNO trust no one. But that's another one. Mulder did have that on his poster on the down in the basement of the X Files. So I think that I probably picked that one up from. From Give.
- [27:20]
Leo Laporte
Give the X Files.
- [27:21]
Steve Gibson
Yes, exactly. Anyway, we know the defaults matter, and I have little doubt that Brave browser users will be glad to know that regardless of anything else that might be going on, Microsoft Recall will not be able to snoop into their browser windows unless they explicitly choose to permit it. You know, all these things that Brave does, they're just defaults. So you can, if that's too much for you, you can back Brave away from that. Anyway, I, I sort of have a good feeling about this. I feel, you know, I feel a little self conscious and kind of like I'm abandoning Firefox because I want to support Mozilla. But I like what Brave's doing and so I'm there now and we'll see how long that lasts. Good.
- [28:09]
Leo Laporte
I think you did coin tyranny of default. If you, if you coined that 20 years ago, I think you get credit.
- [28:15]
Steve Gibson
We've been using it, I think, for the duration of the podcast.
- [28:18]
Leo Laporte
Okay, wow. I'm going to give you credit from now on. I apologize.
- [28:24]
Steve Gibson
So get this. In the wake of a whopping 380 million dollar damages lawsuit being brought by the famous bleach maker Clorox against its IT provider Cognizant, it's foreseeable that future IT contracts will be adding some sort of maximum damages clause to their boilerplate because wow, $380 million. Here's what Reuters, the, the, the Reuters news service wrote under their headline Clorox accuses IT provider in lawsuit of giving Hackers Employee passwords. So they're saying that their, that their, their provider was giving out Clorox's employee passwords. They wrote Bleachmaker. Clorox said Tuesday, that's a week ago, that it has sued information technology provider Cognizant over a devastating 2023 cyber attack, alleging that hackers gained access by simply asking the tech company's staff for its employees passwords.
- [29:43]
Leo Laporte
They were just trying to be helpful.
- [29:45]
Steve Gibson
That's right. We wouldn't want you to get locked out of your accounts. Now, Clorox was one of several major companies they added hit in August of 2023 by the hacking group dubbed Scattered Spider. And we'll be hearing about them a lot during this next couple hours, which specializes in tricking IT help desks into handing over credentials and then using that access to lock them up for ransom. The group is often described, that is a scattered spider of. Of unusually sophisticated and persistent, but in a. Of being unusually sophisticated and persistent. But in a case filed in California state court last Tuesday, Clorox said one of scattered spiders hackers was able to repeatedly steal employees passwords simply by asking for them.
- [30:45]
Leo Laporte
Repeatedly. Repeatedly.
- [30:47]
Steve Gibson
Repeatedly. Yes.
- [30:49]
Leo Laporte
According to. That's not good.
- [30:53]
Steve Gibson
According to a copy of the lawsuit reviewed by Reuters, quote, cognizant was not duped by any elaborate ploy or sophisticated hacking techniques. The cyber criminal just called the Cognizant Service Desk, asked for credentials to access Clorox's network, and Cognizant handed the credentials over, unquote. Now, in an emailed statement, because Reuters said to Cognizant what. Cognizant pushed back, saying it did not manage cyber security for Clorox and it was only hired for limited Help Desk services, they wrote. That is Cognizant wrote, quote, clorox has tried to blame us for these failures, but the reality is that Clorox hired Cognizant for a narrow scope of Help Desk services, which Cognizant reasonably performed. Unquote. Now, I'll. I'll leave it as a question for our listeners. Why, if that's true, did Cognizant have the ability to give out Clorox employee authentication credentials anyway? Reuters says three partial transcripts included in the lawsuit obtained by Reuters allege conversations between the hacker and Cognizant support staff in which the intruder asks to have passwords reset and the support staff complies without verifying who they're talking to, for example, by quizzing them on their employee identification number or even their manager's name. Like, quote, I don't have a password, so I can't connect. The hacker says in one call, the agent replies, oh, okay, okay. So let me provide the password to you, okay? Do not hire these people or do not give them access to your company's authentication. Maxi Reynolds, a security expert who has specialized in social engineering and is not a party to the case, said, quote, the apparent ease with which the hackers got what they wanted wasn't necessarily an indication that they weren't skilled. They just tried what typically works. She said the full transcripts were needed to offer a full and fair evaluation of what happened in the. In 2023, but said that, quote, unquote, if all they had to do was call and ask straight out, that's not even social engineering. And. And it is negligence, non fulfillment of duty, unquote. The lawsuit said, wrote Reuters, that the 2023 hack at Clorox caused $830 million in damages, about 50 million of which was tied to remedial costs. That might have been them paying the. The, you know, ransom, if there was one, or. Or maybe just restoring from backup. But how could that be 50 million? And they said the rest attributable to Clorox's inability to ship products to retailers in the wake of the hack.
- [34:20]
Leo Laporte
That's not so.
- [34:21]
Steve Gibson
So they're saying 50 million in remedial costs and 330 million in lost revenue as a consequence of the downtime. Clorox said the cleanup, which. And you know Clorox would know all about cleanup, right. Was hampered by other failures by Cognizant staff, including failure to deactivate certain accounts or properly restore data. So it does sound like if they were in. If Cognizant was in charge of restoring data. Again, not just help desk stuff. So it should be noted that Clorox is asking for. The fact that they're asking for 380 million in compensatory damages does not mean that's what they're going to receive from a court or a jury trial. You rarely do you get more than you ask for. However, just looking at Reuters reporting of this, I'm. I am, as I've, it's been made clear, as already, immediately skeptical of Cognizant's rebuttal. If, as they claim, they were only hired to perform limited help desk services, how did they have access to Clorox's network and the ability to reset employee passwords at will? You know, those limited help desk services don't appear to have prevented that. So anyway, my feeling is with the ability, the capability to arbitrarily reset Clorox employee passwords comes responsibility to do so with the proper oversight, which doesn't seem to be the case. What we clearly appear to have here is a case of outsourcing gone awry. Outsourcing, as we now know, every one of you seen this, right? Is the new 21st century business model. It's the idea of hiring for the services you need rather than growing them yourself in house. It's got a name. It's formerly called bpo Business Process Outsourcing. You know, it's now an industry, and frankly, I'm not a fan. I understand the promise of agility and scalability. Today's startups typically are a small group of people with a bunch of contracts for the services that they need. But what about a company like Clorox, really? Surely they could afford to operate and manage in house IT services. But they've been around forever, so I would wager they once did. Certainly they once did their own it, right? They could afford to operate and manage in house IT services, and they must have. Once. I would bet that some pencil necked C suite executive got greedy and decided to trim the fat and demonstrate how they could shave, what, half the cost of running it in house. And they may have reduced their IT operating overhead by half. Who knows? Right up until it cost them $380 million. So it's easy to point fingers at some lame IT contractor. And you know, it certainly is worth asking why cognizant, who doesn't appear to have been quite cognizant, were ever given the opportunity to screw up so badly. But in this business, you get what you pay for. And I'm not gonna shed too big a tear for Clorox. You know, they clearly set themselves up for this and. But again, having, you know, outsourcing, this means, you know, you get what you asked for. Leo, before we began recording, I think it's before we began, or I guess we were live but weren't recording. I was talking with you a little bit about the fact that for all of this year my wife and I have been involved in remodeling a home. I've had much more contact as a consequence of that with the. The. What has happened in the world to support, you know, where you need to call somebody to get some help with something. You need to. Why didn't this ship or where is this or that. It's really. We're in a sad state of decline.
- [39:04]
Leo Laporte
But Steve, let's be fair. Did you outsource the plumbing?
- [39:09]
Steve Gibson
No, actually, I haven't.
- [39:10]
Leo Laporte
You did all the plumbing yourself.
- [39:12]
Steve Gibson
Oh, okay. That's true.
- [39:14]
Leo Laporte
Did you outsource the carpentry? The thing is, it's not that the outsourcing is inherently bad. We outsource our IT because we're too small a company to have an IT department. And Russell has much more expertise, even though we're a technology company, than anybody in the company. They just hired the wrong company. I don't think it's necessarily bad to outsource. I think that's actually often the best way to go if you don't have the expertise. And especially in tech, because there's such a land rush for skilled technologists these days. It's pretty hard to build your own IT department in a lot of companies because they can't afford these people. So maybe the problem is Just that they didn't hire the Right.
- [40:02]
Steve Gibson
Well, that's clearly the problem. Right. You know, or. And who knows? Maybe Cognizant got so busy, they, they.
- [40:10]
Leo Laporte
They had to grow, trained their people. That's pretty clear.
- [40:14]
Steve Gibson
Yeah.
- [40:15]
Leo Laporte
Yeah. That's what really happened.
- [40:17]
Steve Gibson
And I think, I think many of their people sit in front of a screen and a screen pops up and they just push some buttons. You know, they're so. There's, there's no sense of loyalty there. There's no connection. They don't know, you know, who.
- [40:30]
Leo Laporte
Yeah, but just because somebody is paid by Clorox doesn't make them loyal or effective, I gotta point out. Yes. So, I mean, I think this could happen internally as well as externally. I think just poor training on Cognizant's part. And I think they are on the hook, as they should be for this.
- [40:49]
Steve Gibson
Yeah. Yeah, it needs that. There, there needs to be accountability.
- [40:53]
Leo Laporte
Yeah.
- [40:54]
Steve Gibson
Let's take a break and then we're going to talk about the beginning rollout of Windows 10 ESU. That the way Microsoft found of not terminating security updates this coming October?
- [41:09]
Leo Laporte
Yeah, let's hope Microsoft is. Maybe they should outsource their security. Maybe that somebody else would do a better job. You never thought of that? You ever think of that? Our show today, brought to you by. I'll tell you what, this would be a company. Everybody could benefit from a Threat Locker. I, I am a big fan of Threat Locker. They do what we call zero trust. Right. Ransomware. It's just killing businesses worldwide. Right. Threat Locker can prevent you, literally prevent you from becoming the next victim, regardless of how smart the bad guys are or what technologies they're using. Even if they're using AI Threat Lockers, Zero Trust platform takes a proactive, and these are the three words you need to know. The most important three words. Deny by default. Deny by default. The tyranny of the default. Right. Deny by default approach. That's what zero trust is all about. It blocks every unauthorized action. If you didn't say they can do that, they can't do it. That protects you from both known and unknown threats. Zero days, Right? Because you didn't say, yeah, zero day, go ahead, hack my system. No. So the zero day just gets stopped cold. Trusted by global enterprises like JetBlue. Companies that can't afford to go down, not for one minute, by infrastructure companies like the Port of Vancouver. Ransomware takes them out of commission for a day. Everybody suffers. That's why they use Threat Locker. Threat Locker shields you and them from zero day exploits. And supply chain attacks. By the way, this is kind of a side effect of zero trust, providing complete audit trails for compliance because you know exactly who did what when, right? As more cybercriminals turn to malvertizing. Are you familiar with that term? You are. If you listen to this show, you need more than just the traditional security tools. Attackers, they're creating very convincing fake websites, impersonating popular brands like AI tools and software applications and then distributing it through ads. Because these ad companies, they don't check, right? You just, it's all automated. So social media ads, hijacked accounts. Then they use the legitimate ad networks to deliver the malware affecting anyone who browses on work systems systems. Traditional security tools often miss those attacks because the attacks use fileless payloads, they run completely in memory. They exploit trusted services that bypass typical filters. But guess what? You can't get through Threat Locker. Threat Locker's innovative ring fencing technology strengthens endpoint defense by controlling which applications which scripts can access or execute, containing potential threats. Even if malicious ads successfully reach the device, they can't do anything of this. Threat Locker works across all industries. It supports Mac environments. They've got very good 247 US based support. You get in completely comprehensive visibility and control. And by the way, they don't put this in the app. But I will tell you, go check the website. Very affordable. Every company needs to know about Threat Locker. Jack Senisap who is the director of IT infrastructure and security at Redner's Markets, maybe you shop there. Says quote when it comes to Threat Locker, the team stands by their product. Threat Locker's onboarding phase was a very good experience and they were very hands on. Threat Locker was able to help me and guide me to where I am in our environment today. He's not the only one. I hear this from every customer. Get unprecedented protection quickly, easily. Yes, it cost effectively with threat locker. Visit threatlocker.com TWIT you'll get a free 30 day trial and learn more about how ThreatLocker can help mitigate unknown threats and ensure compliance. That's threatlocker.com TWIT thank him so much for supporting Steve and security now. Thank you Threat Locker. We're gonna, I think we're trying to get out there this spring for a zero trust world. It could be a lot of fun to go out there. Anyway, on we go with the show, Steve.
- [45:20]
Steve Gibson
So we talked about this recently and Last Tuesday Windows 10 end users will have begun according to Microsoft, seeing the notices we talked about before. So here's What Microsoft posted about this last Tuesday, they said from modern security to faster performance and the latest features and experiences, Windows 11 is built to help you work, play and create with ease. With Support for Windows 10 ending on October 14, 2025, we're here to ensure your transition is smooth, secure and up to date. In other words, you know you need to be moving to Windows 11. However, of course, as we know half the world hasn't yet and shows no interest in doing so, Microsoft said. We understand that moving to a new PC can take time and we're here to support you throughout the process. Windows 10 Extended Security Updates, that's the ESU program is designed to keep your current Windows 10 PC protected after support ends, helping you stay secure during the transition. Starting today, individuals will begin to see an enrollment wizard through notifications and in settings, making it simple to select the best option for you and enroll in ESU directly from your personal Windows 10 PC. Okay, well, I've seen no sign of it so far. Six days after that announcement, I went poking around in Windows 10, which has been fully updated, looking for any sign of this ESU offer. I couldn't find it nowhere in Settings. I hadn't received any notifications, so you know it's in rollout mode. I did check. I don't have one of the fancy MSDN long term servicing versions. It's just Win 10 Pro or Enterprise rather, so it doesn't have all the extra win 10 nonsense. So I would expect that people are going to begin to see this and we'll have the option for moving forward. Now, maybe Enterprise having just said that, maybe Enterprise won't be getting that because they'll be presuming that an enterprise version is part of an enterprise, even though I'm not hooked into Active Directory or anything. Anyway, for what it's worth, that'll begin happening. And as we know we talked about this before, if you've been using Edge or Bing, you get Bing points in Windows. I already had, I think you need, what was it, 1900 Bing points. Anyway, I had more Bing points that I needed so I qualified for six months of extended updates. Or if you let Microsoft back your system up, back your system settings up into the cloud, then you qualify that way too. Basically they're trying trying to give it away without looking like they're giving it away. So you know, again, six months of free updates for Win10 and you get to stay there. And after that, probably zero patch is the way people will be able to continue to stay secure even after Microsoft finally says, if indeed they do ever finally say that, okay, enough is enough and we're not giving you anything more. We'll see. The following story appeared last Friday in the online news publication RBC Ukraine. Now, while we might expect there to be some nationalistic bias in their reporting of the facts, the facts reported do line up with that from other sources. Their headline was Cyber Blast in Crimea, Ukrainian Intelligence Crashes Russian Occupation Servers. And I wanted to share this because obviously there's just no longer any question whether Russia and Ukraine are at war. You know, it's no longer what was that? If you limited military experiment or whatever.
- [49:44]
Leo Laporte
It was in that for quite some time.
- [49:46]
Steve Gibson
Yeah, yeah, so. So this story shows just how cyber today's modern warfare has become. RBC Ukraine reported. Cyber specialists from Ukraine's Defense Defense Intelligence, which is abbreviated hur, have carried out a large scale special operation targeting the occupation authorities in Crimea. According to a Ukrainian intelligence Source Speaking to RBC Ukraine, the operation lasted several days. A powerful DDoS attack effectively paralyzed the information systems and network infrastructure in Crimea. Now that lines up with what we know of Ukraine's offensive cyber capabilities. They previously demonstrated a number of times that they have the capability to launch and sustain significant DDoS attacks against their adversaries. The article continues writing While the Russian occupiers were scrambling to identify the cause of the government system's failure, Ukraine's cyber experts. I'm pretty much sure I have a feeling they knew the cause. Ukraine's cyber experts infiltrated the electronic accounts of the leadership of the occupation administration in temporarily occupied Crimea. Okay, well they've obviously spitting the facts here, but okay. They gained access to the following digital resources, the Electronic Document management System, Dialog, the systems SED and Delo, and accounting platforms 1C Document Flow, Directum and Atlas. Over two days, 100 terabytes of documents belonging to the occupation authorities of the peninsula were downloaded. Among the files were top secret documents containing data on military facilities and logistics routes used to supply occupying forces in Crimea. A Ukrainian source said there's so much data extracted that we're about to learn a lot of explosive details about the operations and crimes of Russian occupiers in Ukrainian Crimea. After copying all available information, Ukraine's cyberspecialists wiped all data stored on the servers of regional and district government bodies, ministries and agencies of the occupation administration in Crimea. The successful Ukrainian hacker operation did not go unnoticed in Moscow. Russia's State Duma has already labeled it an element of hybrid warfare, meaning the so called Ministry of Internal Policy Information and Communications of Crimea stated that, quote, technical specialists are taking all necessary steps to restore services. However, some services may remain unavailable to users. Notably, earlier this month, Ukraine's cyber specialists targeted the Russian company Gaskar Integration, one of the largest suppliers of drones for the Russian army. In June, Ukrainian hackers also attacked one of Siberia's largest Internet providers, Orion Telecom and earlier rbc. Ukraine sources reported that Ukrainian intelligence cyber experts hacked into the online system of Russian railways. As a result, the official website of Russian Railways went offline. So I encountered another interesting piece of related news, which was that Russia has established free and open WI FI access zones so that their citizenry in Russia could continue to access the Internet where cellular services have been discontinued. It turns out that Russia has been forced to shut down large areas of cell phone service because Ukrainian drones were using those services for their navigation. So it's clear from all of this that the battlefield is becoming more and more cyber. Not only is more cyber technology being employed for, for kinetic military operations, but all nations have become quite dependent upon the convenience created by today's networking for operational management. The fact that nearly, well, apparently more than 100 terabytes of bureaucratic operational and apparently some military data, some of it apparently marked top secret, were sitting on databases of online and Internet accessible would surprise no one today. But that doesn't make it any less irresponsible. You know, we've had fun through the years covering proof of concept stories where data was cleverly made, you know, to jump to and from air gapped systems. Stuxnet by far being the most famous of those. But the practical truth is air gapping is a huge pain in the butt to employ specifically because it works so well. You know, disconnecting things like completely disconnecting them works. You know, it may not be perfect, but it actually doesn't need to be. Even if it only drastically limits the bandwidth available to leakage due to operator errors, you know, even that would be a massive benefit. There's no way anyone is going to exfiltrate a hundred terabytes of data from a camera that can see the blinking activity lights on a network router. You know, and you know, the, the, the when we've talked about like, you know, monitoring the keystrokes of people typing or bouncing a laser off of a balloon in a conference room and reconstructing the audio. Well, those, those hacks and gimmicks work, but they're not high bandwidth. So, you know, I get the convenience of everything being connected, but with that convenience comes the liability of it. Being connected to everybody else. And as you know, what we talk about on this podcast so often, Leo, is authentication failure. You know, you know it well, it's. It's arguably the hardest thing. Right? You know it is. It's. What separates the real world from the cyber world is the question, who am I really talking to?
- [56:50]
Leo Laporte
My name is Steve Gibson. I forgot my password. Could you give it to me? It's just that easy, Steve.
- [56:59]
Steve Gibson
Oh, by golly, no problem.
- [57:01]
Leo Laporte
Oh, by golly, oh, we wouldn't want you not to be able to get in there. No. Right.
- [57:08]
Steve Gibson
Wow. So while we're on the topic of being able to keep the data we have inside our networks from getting out, TechCrunch carried the news of yet another major data breach. And just wait till you who did it and how it happened. TechCrunch wrote us. Insurance giant Alliance Life has confirmed. Yes, Leo, to TechCrunch, that hackers stole the personal information of the, quote, majority, almost all of its customers, financial professionals and their employees, which sounds like a complete database breach. During a mid July data breach. When reached by TechCrunch, Alliance Life spokesperson Brett Weinberg confirmed the breach. Brett said on July 16, 2025, that's 13 days ago. A malicious threat actor gained access to a third party cloud based CRM system used by Alliance Life. The threat actor was able to obtain personally identifiable data. You know this is like an insurance company, right? Related to the majority of Alliance Life's customers, financial professionals and select Alliance Life employees using a social engineering technique. Sound a little bit like scattered spider maybe? Uhhuh.
- [58:42]
Leo Laporte
Hi, my name is Mr. Alliance.
- [58:46]
Steve Gibson
Forgot my. It's right there in the title. It's right there in the title. Yeah.
- [58:52]
Leo Laporte
We use them for years for our travel insurance. So I'm in their database many times.
- [58:58]
Steve Gibson
Yep. The company disclosed the data breach on Saturday in a legally required filing with Maine's the. The the state of Maine's Attorney General, but did not immediately provide a number of how many Alliance Life customers are affected. According to the spokesperson, Alliance Life has 1.4 million customers, while its parent company, alliance, has more than 125 million customers worldwide. Alliance Life said it notified the FBI and added it had no evidence that any other systems on its network were compromised. On the other hand, remember that we've also seen companies now telling their IT people don't look, please don't look for the evidence because you might have to swear under oath. Wow. The insurance giant would not say if it had received any communication from the hackers, such as a ransom note. In other words, they're not saying no, they're just not saying. The company also would not attribute the breach to a hacking group. Alliance Life is the latest company in the past month to have been hacked during a wave of data breaches targeting the wider insurance industry, including Aflac, a major provider of supplementary health insurance security. Researchers at Google said in June that they were aware of multiple intrusions across the insurance sector attributed to Scattered Spider, a collective of hackers and techniques that rely on social engineering, such as deceptively calling and tricking help desks into granting them access to a company's network. Imagine that. How could that possibly work? Who would fool for who would fall for that? Leo Prior to targeting insurance companies, the Scattered Spider hackers were seen targeting the UK retail industry as well as the aviation and transportation sectors and are historically known for for hacks targeting Silicon Valley technology technology giants. Per the main filing, alliance plans to begin notifying affected individuals around August 1st. So Leo, you can look for your the notice in your email, you know, sometime late later this week or next week. Okay, so let's just step back for a minute here. I have a bit of a rant. Here we are again. As long as I forgot my password and oh I love this one. I don't have my authenticator with me right now. Remain acceptable options. We're just pretending to have security and we're never going to move past our current online impersonation problems. I mean really, what is the possible security benefit of even bothering with fancy time based one time token identity authentication if oh, but I don't have it with me right now. Is acceptable. Really? If you don't have it with you right now, that's just too bad. No login for you. Does that inconvenience you?
- [62:30]
Leo Laporte
Good.
- [62:31]
Steve Gibson
That's what you asked for. That's what you signed up for. That's what you said you wanted. It's because you want to also significantly inconvenience any bad guys that. Oh that. That it might be that you will also be inconvenienced if for whatever reason you might be unable to produce the exact thing that you want no bad guys to be able to produce. You can't have it both ways. You either have true security or which might mean and it would be on you that you might be inadvertently locked out and be unable to log in when you're unable to meet the requirements you had previously arranged and agreed to. Otherwise we have the world we're actually living in today. We're all in this world where we're allowed. The only thing that available is some feel good security theater using an authentication system which would most fairly be described as optional, right? With optional authentication, not being able to produce the required magical six digits on demand simply means that it will be necessary to jump through some additional hoops to get yourself authenticated. That's all. The problem is the bad guys are more than happy to jump through those same hoops. They wake up every morning in anticipation wondering just how many hoops they're going to be able to jump through today. How many lazy fat westerners accounts are they going to hack today? But seriously, whenever I see one of those I left my authenticator at home links to click on underneath the authentication prompt, I just shake my head. Why even bother with it if you don't need to actually use it? You know? A cool and underappreciated feature of the Squirrel system was that after its user became comfortable with the system, they understood they'd figured out how it worked. They backed up their single global encrypted identity. They could enable a feature in Squirrel's user interface which requested every website they subsequently logged into with SQRL to please immediately, completely and irrevocably disable every alternative login solution and plant a flag in the account to prevent any human agent from ever overriding authentication. No matter what anyone else ever says and no matter how much anyone banks, that is what true security looks like. But the world is clearly still not yet ready to take their own security that seriously. And Leo, you know, when you step back from this, when you think about it, what's the cost of having that level of security? So you forgot your phone with your authenticator so you can't log in to check your tweets. The world is not going to end. Life is not going to be over as you know it because you're unable to authenticate on some given instance. And the point is you have to not be able to authenticate because if you can, then anybody can. Potentially. So again, I, I a few what maybe it was at some point last year I realized that, that using a, you know, like a password, you know, a password manager or an authenticator, what it really was was really just an accelerator. It made it easier and quicker to authenticate because it provided that stuff. But if you didn't have that stuff, you'd have to jump through a few extra hoops. And in order to authenticate, many people, you know, just say, oh, I just forgot my password. They wait for a, a, a login link to be emailed to them and then they log in. That way it's a little slower, but it works just the same. So it ends up being that email is actually the thing that we have to protect. Everything else is just theater. Anyway, I just, I, again, I, I see this especially with an authenticator. You say, you know, I've, I've, I've, I've added this. I want the extra protection. I want multi factor authentication. I'm, I'm going to do this. And then underneath the authentication is I don't have my authenticator with me right now. Really.
- [67:52]
Leo Laporte
Put it in Bit Warden.
- [67:54]
Steve Gibson
Let's take a break. I have to calm down.
- [67:58]
Leo Laporte
Well, it's, it's good that you're, you're upset because our sponsor for this segment of Security now is Bit Warden.
- [68:05]
Steve Gibson
Yay.
- [68:07]
Leo Laporte
Guess what? You could put your password in Bitwarden. And, you know, we talked about this a few episodes ago. I, for a long time, I was reluctant to put the two factor in Bit Warden. I wanted a separate, you know, two points of failure kind of thing. And you said, you know, yeah, I mean, theoretically, you shouldn't, but it's, but it's fine. These are, this is well secured, so. And I can't tell you how great it has been to move my two factor codes into Bit Warden. Now it autofills my name, my password, and my authentication. It's like 100 times easier. And the point is, I trust Bit Warden. You should trust Bitwarden Open source encryption. Done right, Bitwarden is the trusted leader, not just in passwords, not just in authenticator codes, but in pass keys, even in secrets management, including things like SSH keys. I keep my private keys in Bit Warden. In fact, it facilitates that. My API keys, I store them in Bitwarden. Bit Warden's consistently ranked number one in user satisfaction by G2 and software reviews. More than 10 million happy users across 180 countries. Over 50,000 businesses. That kind of surprised me. I know Bitwarden is great for individuals. I'd kind of forgotten. It's great for enterprise too. You know, we were just talking about the alliance breach. That's a lot of customers whose private information, including probably their passwords, are available. More than 19 billion with a B passwords are available on the dark web right now, which would be fine if you only use that password for one thing. But it turns out 94%, 94% of those breached passwords have been reused across multiple accounts. The truth is, and I know it probably breaks your heart, Steve, it certainly worries me, most people, including most of the people I know, most of the people in my family don't create new passwords for every account, but you really have to. You do. And Bitwarden makes it so easy. Info stealer Malware threats. We're talking about info stealers. Last week, last year surged 500%. Bad guys are using this stuff because it works. 500%. Modern hackers no longer hack accounts. They log in with weak or reused passwords. If you use strong passwords and you keep them in your Bit Warden, you're a lot safer. Bit Warden Access Intelligence. Something new they've just added. It's an enterprise feature that enables enterprises to proactively defend against internal credential risks. Because you know your employees are reusing passwords, they're doing all kinds of bad stuff. It also helps protect you against external phishing threats. Two ways it does this. Risk Insights allows IT teams to identify, prioritize and remediate at risk credentials. So if your company's credentials are all stored in Bit Warden, Bit Warden will tell the IT team, okay, here's some reused ones. Here's some problem ones. Here's monkey 1, 2, 3. Advanced phishing blocker. That's another tool will alert and redirect users away from known phishing sites. It does it in real time using a continuously updated open source block list of malicious domains. Now, this is great for enterprise, but even personal users like me benefit from the fact that Bit Warden will not fill in your password on a phishing site. It knows better. It knows better than you do. Than I do. It's not fooled. Passwordless authentication, that's the new thing. Today Google announced that they were having problems on workspace and that they were going to encourage all workspace users to turn on passkeys. I was. So I said, lisa, turn on your passkeys. She said, are they safe? I said, yes, Lisa, they're safe. Passwordless authentication is the best way to go. And as always, Bit Warden is right at the forefront offering support for passkeys. So all your passkeys are in the Bit Warden vault, which means they're everywhere. Your bit Warden is on your phone, on your tablets, on your laptop, everywhere on your computer. It offers support for passkeys and Fido 2 standards to strengthen and simplify the login experience. Bit Warden passkey support includes enhanced pass key support across web, desktop and mobile platforms. Like I said, it enables users to store and sync passkeys with end to end encryption. It'll also support two step login with FIDO2 and WebAuthn allowing hardware key authentication as a secondary factor or even a primary method that would be a great way to secure everything. Biometric unlock enhancements on mobile and desktop that's a fantastic improvement. Ties in perfectly with Bit Warden. I unlock my vault with my fingerprint on my Mac with my face ID on my phone. Streamlining access without compromising security. In fact I would say it improves security. An improved autofill experience is now in Bitwarden for passkeys, cards and identities are designed to work seamlessly across modern browsers and apps. I will also add the two factor the one time passwords. Fantastic. Bit Warden setup only takes a few minutes. Supports importing from most major password management solutions so your company can move fast one day in most cases. Bit Warden's open source code and this is important to me can be inspected by anyone and is regularly audited by third party experts. I don't use crypto that's not open source. I want to know is there a backdoor in there? Bitwarden meets SoC2 Type 2 GDPR HIPAA CCPA compliance. It's ISO 270012002 certified. So they check all the boxes. Get started today with Bitwarden's free trial of a teams or an enterprise plan or get started for free across all devices and individual user. Bitwarden.com twit that's bitwarden.com twit back Mr. Gibson.
- [74:20]
Steve Gibson
Okay, so yes, thank you. The Washington Times last Thursday headline is a hackers breach intelligence website used by the CIA.
- [74:32]
Leo Laporte
Oh boy. You'd think they'd know how to secure their website. Maybe they outsourced it.
- [74:38]
Steve Gibson
One one would hope that our CIA. Yeah, okay, so I'm just going to share the intro of this. They wrote, unidentified hackers recently compromised a major intelligence website used by the CIA and other agencies to submit details of sensitive contracts, according to the National Reconnaissance Office, the spy satellite service that runs the site. The breach targeted proprietary intellectual property and personal information submitted on the Acquisition Research center website in support of several innovative CIA spying programs. A National Reconnaissance Officer spokesperson told the Washington Times, we can confirm that an incident involving our unclassified Acquisition Research center website is currently being investigated by federal law enforcement. We do not comment on ongoing investigations, especially those that are embarrassing. The extent of the breach is not fully known, but people familiar with the activity said hackers likely obtained information on key technologies for CIA operations. Other potential areas of compromise could include the Space Force, its efforts to build surveillance satellites and space weapons. Oh boy. And the Golden Dome Missile Defense program data from one highly sensitive program, Digital Hammer, was compromised, said people familiar with the hacking. Digital Hammer compiler com compiles cutting edge technologies for human intelligence gathering, surveillance and counterintelligence operations. The program focuses on the threat of Chinese intelligence and information operations. Anyway, the story continues at some length, so I put a link to the entire piece in the show Notes for anyone who's interested in knowing more. It's unclear whether we're going to obtain more reporting on this, given that it's the CIA, but my hunch just based upon the timing of the event and the nature of the breaches that are resulting from the exploitation of Microsoft's recent SharePoint disaster, which we'll be digging into when we get into today's main topic, I would not be surprised to learn that this CIA site, whose role and profile require it to be all about sharing files, might not have been another victim of that recent SharePoint Zero Day remote code execution vulnerability. And I should note that this is not an I know this is unusual, but this is not a failure to update problem. Everybody who updated on Patch Tuesday got attacked, so it's not the CIA's fault, as we'll see, but it sure does fit the profile of a SharePoint breach. Now the Pentagon, however, says no, they didn't get us. Speaking of the SharePoint hack, Nextgov's headline last Thursday was Pentagon not impacted by Microsoft SharePoint hack, says their tech chief, Nextgov wrote. The Department of Defense has not been ensnared by a broad intrusion into on premises versions of Microsoft SharePoint, its chief information officer said Thursday. Katie Arrington said at the ATO and Cloud Summit Cloud Security Summit on Thursday in a stage interview, quote, as of right now, no, not that I'm aware of, unquote. Arrington said she's been doing daily calls with Microsoft while the department has been conducting forensics investigations since the zero day vulnerability was publicly identified this past weekend, meaning a weekend ago. Thus far, they wrote, several federal agencies have been impacted, including the Departments of Energy, Homeland Security and Education. And up to a dozen federal agencies have been notified of possible compromise by cisa, the Cybersecurity and Infrastructure Security agency, according to a source familiar. DHS issued a statement that its investigation into the hack remains ongoing, but, quote, there is no evidence of data exfiltration at DHS or any of its components at this time. Arrington said the latest series of hacks and attempted hacks reiterate the constant threats posed by state actors to US and defense systems when zero day vulnerabilities which have not yet been. Which have not been previously uncovered and therefore give developers zero days to patch them. Not quite the case in this instance, but we'll get there are found cybersecurity professionals need to act immediately and apply those patches. Well, everybody did in this case. Arrington said, quote, Russia, China, Iran, North Korea. Are they going to continue? Yes. Are they going to look for any hole they can find? Yes. It's a zero day. The day you found out about it, a patch was made that same day. And how fast we deploy the patches, how fast we work as a unified body to I say turn the lights on an adversary when they do something, that's how fast resilience will be. Unquote. Okay, now I have no idea what any of that double speak mumbo jumbo there at the end was, but as we know, patches, especially from Microsoft, often take much longer than to quote Katie that same day. But I really wonder, seeing what she said here is whether Katie is aware that this entire quite serious mess was primarily created because Microsoft botched and fumbled the original patch Tuesday patch release by once again, as I said, only patching a symptom and not the underlying cause of the vulnerability. Anyway, we'll be getting to that shortly. We have our first photo, Leo, of a DPRK laptop farm. Now this was not a farm set up by the DPRK, you know, aka North Korea. Oh no. This was a 50 year old American.
- [81:36]
Leo Laporte
Woman who was busted.
- [81:38]
Steve Gibson
Who was busted.
- [81:40]
Leo Laporte
Yeah.
- [81:40]
Steve Gibson
I had formed an image, I guess in my mind's eye when I previously discussed and described the so called laptop farms.
- [81:50]
Leo Laporte
Not. Doesn't live up to the image, does it?
- [81:53]
Steve Gibson
No, no. The chachkis hanging from the, from, from the right metal rack and there's some purses and handbags and things. It's not exactly was not your high tech laptop farm, I'm thinking.
- [82:10]
Leo Laporte
This lady said to her friends, I found this great way to make money. It's, it's really easy. They just send me the laptops. All I have to do is connect.
- [82:18]
Steve Gibson
Them to my Internet, put them on my wi fi. Yeah. You know, I had a man. I imagined something more glamorous than three metal wire racks containing about 30 assorted random looking laptops with large fluorescent post it notes stuck on them.
- [82:39]
Leo Laporte
That's probably a password on there, I'm sure.
- [82:41]
Steve Gibson
Yeah, exactly. Or to identify which one is which because you got to associate them with your fake employees and so forth.
- [82:47]
Leo Laporte
Yeah. Anyway, I bet she didn't do any of that though. Really all they had to do is Give her, give them a US IP Address, right?
- [82:54]
Steve Gibson
Probably, yeah.
- [82:55]
Leo Laporte
Yeah.
- [82:56]
Steve Gibson
So this is Christina Marie Chapman, recently sentenced to a term of eight and a half years in prison. Probably will actually serve less on good behavior for this operation of an illegal North Korean laptop farm whose purpose was to help North Korean IT workers pass. You know, spoof. Being U. S residents, we've talked about this a number of times. This is an actual serious problem. Currently in the US you got to know who you're hiring, when you're hiring, you know, remote, you know, online help and as part of your outsourcing. Altogether, the workers managed to land more than 300 jobs at U.S. companies and generated more than $17 million in revenue for the North Korean regime. And of course they are under sanction by the US So this is all against the law. You know, U. S employers are not allowed to be paying North Korean workers anything. And you know it's a mistake if they do so. Unfortunately, facilitating that illegal conduct will get you eight and a half years in prison. I wonder if it's like three months per laptop, Leo.
- [84:19]
Leo Laporte
You know, I hope she gets to bring her tchotchkes, that's all.
- [84:22]
Steve Gibson
Yeah, that'd be good. Yeah. Okay, so last week I shared a blog posting and a forensic analysis by Expel security describing a remote third party man of the middle attack on FIDO authentication using passkeys. Given Expel's description of the process, which amounted to a classic real time website intercept and forwarding attack, the only way this could have been possible was if it was not necessary for the passkey equipped FIDO authenticator to communicate with the authenticating users local desktop browser in real time. Because the authenticating user would be the man in the middle and the Fido authenticator would be in the hands of the unwitting victim. As I noted last week, the nature of this vulnerability is well understood. You know, that's why in my case I had incorporated a Squirrel client to browser link using the local host IP on the on that desktop to allow the user's browser to talk to the system's resident Squirrel client. Now, many of our on the ball listeners wrote to say that they were pretty sure that in FIDO's cross device authentication model, this client to browser link was not optional and that it must be present created by Bluetooth and they are 100% correct. Fido explicitly prevents this attack and and will not successfully authenticate with without a local Bluetooth link between the user's web browser and their cross device authenticator.
- [86:20]
Leo Laporte
Oh, that's smart.
- [86:21]
Steve Gibson
Which means that what Expel described is impossible.
- [86:26]
Leo Laporte
Yeah.
- [86:27]
Steve Gibson
Now given that the presumably Fido based man in the middle attack that Expel Security described having witnessed should not have been possible. It turns out that the attack was not possible and did not happen. At least not as they described. Last Friday the 25th, they made another posting to their Threat Intelligence blog with the headline an important update and apology.
- [86:57]
Leo Laporte
Whoops.
- [86:58]
Steve Gibson
On our Poison Seed blog where they wrote on July 17th we published a blog posting covering a recent incident we observed. On further review, we found our original findings are unsupported by the evidence.
- [87:15]
Leo Laporte
Oh boy.
- [87:16]
Steve Gibson
The original post described a new form of phishing attack that allowed an attacker to circumvent a Fido passkey protected login. It stated that this attacker used cross device authentication to successfully authenticate while not in close proximity to the authenticating client device. The evidence does show the targeted user's credentials, their username and password being phished, and that the attacker successfully passed password authentication for the targeted user. It also shows the user received a QR code from the attacker. This QR code, when scanned by a mobile device, initiates a Fido cross device authentication flow which according to FIDO specification, requires local proximity to the device which generated the qr code, the WebAuthn client. When properly implemented, but without proximity, the request will timeout and fail. So at the time of the original post they wrote Expel believed the attacker successfully completed the authentication workflow resulting in access to protected resources. After discussing these findings with the security community, we understand that this is not accurate. The Octalogs show the password factor passing successfully, but all subsequent MFA challenges failed and the attacker is never granted access to the requested resource. So that solves the mystery, I am sure. I also once knew that a Bluetooth link was required and not optional for FIDO cross device authentication, and I'm very glad that's the case. But I got swept up in their report, which I assume to be correct, and I doubted what I knew. I suppose I also gave away the fact that I'm not a frequent user of Fido passkeys Cross device authentication, since anyone who likely deals with the need for Bluetooth linking, you know, all the time, would be well aware of that requirement, as many of our listeners were. So we've got that figured out and it is very good news, as you've noted, Leo, that the device must be in proximity to the browser and that they have to communicate by Bluetooth link.
- [90:02]
Leo Laporte
So it just makes sense.
- [90:03]
Steve Gibson
It does. Yeah, it does. So, okay, is our data safe anywhere? No, don't you start to get the feeling. Don't you start to get the feeling that our data is not, in fact, safe anywhere and that no one can be trusted to keep anything that we might disclose and often need to disclose, like, you know, if we're dealing with hospitals to, you know, set up appointments and doctors and so forth, how it's just not safe online?
- [90:36]
Leo Laporte
Yeah.
- [90:37]
Steve Gibson
So here's another example we can add to the pile and talk about sensitive personal data. Tadts. Those are the initials TADTS of the Alcohol and Drug Testing service. As their name suggests, they perform drug and alcohol testing, and they do so for multiple US States. Apparently not being in a great hurry, perhaps they were waiting for some statute of limitations to expire. The organization now admits that they were hacked and that those bad hackers stole the highly personal alcohol and drug testing data of three quarters of a million users. 750, 000 people had their alcohol and drug testing service data stolen. Yep. And even more gallingly, they waited. The. The. The TADTS people waited a full year to disclose this. They became aware of the data breach last ju. Last July 9, 2024, which is why I wonder about some statute of limitations. The organization is only now notifying affected users, those three quarters of a million affected users. But don't worry, they're offering free credit monitoring folks to prevent the use of those highly confidential data which they were entrusted with but turned out to be unable to protect a year later.
- [92:29]
Leo Laporte
I just hate it when they do that.
- [92:32]
Steve Gibson
You know, Leo, I have no plans to unplug from the grid and live in a cave. It turns out you were speaking of plumbing earlier. My wife is a huge fan of indoor plumbing.
- [92:44]
Leo Laporte
Yes, yes, me too.
- [92:46]
Steve Gibson
So convenient.
- [92:47]
Leo Laporte
I'm with her.
- [92:49]
Steve Gibson
So it doesn't really seem as though the rate at which. I mean, doesn't it seem as though the rate at which we're losing this battle is accelerating? I mean, it's nuts. And I do feel, though, because we've been at this now for 20 years, I feel as though these are chickens coming home to roost. I mean, it does no one any good to say that we told you so. I mean, I mean, I'm speaking to the ether. It's not. I. I mean, our listeners are doing everything they can to be safe. Certainly they're very, you know, security concerned. No one can help it. That underneath the authentication link is an. Or the authentication field is a link saying, you know, oh, I don't have my authenticator with me. Let's do something else. That's okay, we didn't design these systems, but this is the consequence of the fact that security is really not even. Has it never been taken seriously? It's still today not really being taken seriously. It's considered an inconvenience if someone can't log in. So we make it very simple. We low. You know, the lowest common denominator is email. If you can, if you can get email, then you're okay. And unfortunately that means, you know, oftentimes you can say, oh, oh, but I don't have access to my email right now and I have really, really, really, really, really, really, really have to log in. Please, can't you? Oh, well, okay. And then in that case, here's your password. They literally, in one of those examples I didn't share, but it was in the lawsuit, they reset the person's password to Clorox123.
- [94:40]
Leo Laporte
Oh, that's secure. You're gonna change that as soon as you get home, right?
- [94:47]
Steve Gibson
Yes, but it wasn't monkey 1, 2, 3. It was Clorox one two three.
- [94:52]
Leo Laporte
Yeah.
- [94:52]
Steve Gibson
So who could ever guess that? Never.
- [94:55]
Leo Laporte
No. No. Never would guess that.
- [94:59]
Steve Gibson
Okay. So thank God we have a bit of good news here. The Financial Times reporting is locked behind a paywall, but many other outlets are reporting on the Financial Times report. The Verge being one of those, wrote the UK government is reportedly set to back down from its battle with Apple to obtain backdoor access to secure user data protected by the company's cloud encryption. Victory hasn't come through the courts, wrote the Verge. Or government figures changing their minds on privacy matters, but thanks to ongoing pressure turns out from the US during the two countries trade talks, turns out JD Vance apparently does is not happy with this. Multiple unnamed UK officials told the Financial Times that the UK government is working on a way out. One of those sources said, quote, the Home Office is basically going to have to back down, adding that Vice President J.D. vance was especially opposed to the UK's demand, which may violate the Cloud act treaty between the two countries, saying, quote, it's a big red line in the U. S. They don't want us messing with their tech companies, unquote. Another official echoed that, explaining that, you know, echoed that, explaining that the UK wants to avoid pushing too hard for any for quote, anything that looks to the U. S Vice president like a free speech issue, unquote. A third official said the UK had quote, it's back against the wall and wants a way out. Quote, it's a problem of the Home Office's own making and they're working on a way around it now.
- [97:03]
Leo Laporte
Wow.
- [97:03]
Steve Gibson
So this entire Apple advanced data protection mess now appears destined to disappear. Now that's great news. And hopefully politicians and their governments won't put themselves in the rest of the world through many more of these no win standoff cycles. You know, they need to realize, at least as regards privacy, they cannot simply demand anything they want. The laws of nature are not theirs to establish. There are problems, no doubt about it, arising from the abuse and illegal conduct enabled by the powerful privacy protections created by encryption technology. But stripping privacy from everyone else, that cannot be the solution.
- [97:56]
Leo Laporte
Yeah. Now if anybody's going to spy on u. S. Citizens, it's going to be us.
- [98:02]
Steve Gibson
Yes. We don't want. We're jealous of that.
- [98:07]
Leo Laporte
Right? Yeah.
- [98:09]
Steve Gibson
Okay. There is a little bit of cloudiness on the horizon, however, because Denmark is reintroducing chat control. You know how the, the control of the EU moves around from one EU state to another. EU today posted the news under their headline EU reconsiders chat control as Denmark reintroduces controversial encryption scanning bill, they write, known informally as chat control. The proposal has re emerged under Denmark's EU Council presidency which began on 1 July. Lawmakers are scheduled to debate the latest iteration of the bill on October 14, 2025. Okay, now we can hope that the EU takes note of the egg the E that the UK has ended up with with on its face with reporting that, you know, they're now trying to backpedal and oh no, that's really not what we meant to do because they've gotten themselves in a big mess. The reporting continues. Originally introduced in 2022 but repeatedly stalled due to political opposition, the legislation seeks to impose obligations on messaging platforms such as WhatsApp, Signal and Telegram to scan user content for child sexual abuse material. If adopted, the law could lead to widespread. Now this is interesting that if adopted, the law could lead to widespread client side scanning of messages before encryption, a measure that critics argue poses a serious threat to digital privacy and data protection. Okay, now nobody wants that to happen, but as I've been noting earlier this year, the solution, I can see to this, if we have to have one, is to employ device side local AI to examine what's being sent. I get it, it's creepy and it's a mess because, for example, parents ought to be able to take photos of their own young children without the police being alerted. But if this must be done, doing it device side and not messing with encryption back doors, to me, that's the only way to to get there, the article said. The Danish presidency has placed the proposal among its top legislative priorities. Yikes. While no new text has been publicly released, Copenhagen has signaled its intention to find a compromise that balances law enforcement's goals with legal and technical concerns raised by member states, civil society and industry stakeholders. Well, good luck with that. Of course, nobody wants to have Big Brother spying on them, even if Big Brother is inside their own phone, the article said. The European Commission originally tabled the regulation in May of 2022, aiming to bolster the detection and reporting of of CSAM online. Despite its stated purpose, the proposal was criticized for its scope and method, particularly the inclusion of end to end encrypted services in the scanning regime attempts to pass the measure under previous presidencies, including Belgium and Poland. So right this is a hot potato. The cheap that keeps getting passed around failed to secure a qualified majority in the Council. Belgium proposed a version in June 2024 that restricted scanning to shared media and URLs contingent on user consent. Poland's February 2025 proposal classified scanning as a voluntary preventative action, though regarded by some experts as an improvement in it too failed to gain traction. Denmark now assumes the role of broker, hoping to navigate between long standing opposition from digital rights advocates and calls from several member states for stronger tools against online exploitation. The Danish presidency's official program states its intention to, quote strengthen the abilities to make use of the digital development of for law enforcement when fighting serious crimes, while also addressing the misuse of new technologies. Criticism of the CSAM bill centers on concerns about weakening encryption. Client side scanning, central to earlier drafts of the proposal, involves monitoring communications on a user's device before encryption takes place. This method is seen by experts as equivalent to surveillance and is considered by many to be incompatible with the principle of confidentiality of communications enshrined in EU law. In 2023, the European Court of Human Rights issued a ruling that effectively prohibited states from requiring the weakening of secure encryption standards. This legal precedent, while not explicitly blocking the chat control proposal, adds a layer of complexity to its adoption and enforcement. Digital rights organizations and privacy advocates have described the initiative as a disproportionate response to a serious problem. They argue that mandatory scanning mechanisms risk creating vulnerabilities that could be exploited by malicious actors and set a precedent for broader surveillance. At present, the contents of Denmark's revised proposal remain undisclosed. So we don't know what's going to happen in October when they they bring this thing back up for discussion because again, this hot potato gets passed around from country to country. Now it's in Denmark's lap. Analysts suggest, they wrote, that the fate of the bill may hinge on Germany's position. The new federal government has not yet indicated whether it would support the measure, and without its backing, a qualified majority may remain out of reach. According to Patrick Breyer, former MEP for the German Pirate Party and a vocal opponent of the proposal, the Danish presidency's success will depend heavily on its ability to secure Germany's approval. Even if the CSAM proposal were adopted in October, so adopted in October, it would still need to proceed through trilog negotiations with the European Parliament and Commission, where further amendments are likely. The Chat Control bill is part of a wider series of initiatives by the EU aimed at giving law enforcement greater access to encrypted data. On June 24th of this year, 2025, the European Commission unveiled the first phase of its Protect EU strategy, which proposes the development of decryption capabilities by 2030, which sounds ominous. Decryption capabilities, what? The strategy is still at a conceptual stage, but indicates the long term policy direction of the European institutions. While efforts to curb the spread of CSAM enjoy broad political support, the methods employed remain contentious. The question facing EU lawmakers is whether security objectives can be met without eroding the privacy rights of European citizens. As the debate resumes under the Danish presidency, it is clear that any legislative outcome will need to reconcile fundamental rights with the imperatives of public safety, a task that has so far eluded consensus. And Leo, I think it's impossible. Yeah, right. I mean, what they're asking for, like everybody wants something that crosses a. A no man's land for the other side, you know that, you know, they, they basically. They want censorship without censorship or they want censorship without any violation of privacy rights. They want, they want to see what you're sending, but they don't want surveillance. Well, seeing what you're sending is surveillance.
- [107:08]
Leo Laporte
Right. They don't want surveillance for themselves.
- [107:13]
Steve Gibson
Right.
- [107:13]
Leo Laporte
Which is the thing protecting us, frankly, because I don't think they care about surveillance for us. But yeah, I worry that, I mean, governments are forcing these things through already. In the uk they've got age verification requirements that people are already cracking. I can't wait till next week. I'm sure you'll talk about this. What is the story? They're using images from video games. There's a great website where you can enter in your British zip code and it will give you the driver's license of your Member of Parliament to use for a fake id. It's just that's what happens though when you create these, you know, surveillance societies. You teach people how to get around them.
- [108:02]
Steve Gibson
Yeah.
- [108:03]
Leo Laporte
So let's hope we can get around it, right?
- [108:06]
Steve Gibson
Yeah. Okay. We have some listener feedback after we take a break so I can recaffeinate.
- [108:12]
Leo Laporte
Download your encryption tools today, boys and girls. You never know when they're gonna outlaw them. Our show today, brought to you by US Cloud. Love these guys. The number one Microsoft Unified support replacement. And we've been talking for a long time, at least, you know, I think six months now about US Cloud. They are the global leader in third party Microsoft support for enterprises now supporting 50 of the 50 of the Fortune 500. And there's a good reason. Switching to US Cloud can save your business 30 to 50% over Microsoft Unified and Premier support. But it wouldn't be any good if it were 30 to 50% cheaper. It's better, a lot better. It's faster. Twice as fast in average time to resolution versus Microsoft. And you know, when your hair's on fire, the network's down, the boss is calling, speed is pretty important. They're also better. I'll explain. And they the other thing they could do that I don't think Microsoft will ever do is save you money on Azure. That's not in Microsoft's interest, is it? Now, US Cloud is excited to tell you about a new offering their Azure cost optimization services. So let's be honest. When was the last time you evaluated your Azure usage like any other cloud service? If it's been a while, you probably have some Azure sprawl, a little spend creep going on. Well, there's some good news. Saving on Azure is easier than ever with US Cloud. US Cloud offers an eight week Azure engagement powered by VBox. It identifies key opportunities to reduce cost across your entire Azure environment. And you're going to get and this is the other way, US Cloud's great expert guidance, access to US Cloud's senior engineers with an average of over 16 years in Microsoft products. And these are the pros, right? So at the end of the eight weeks you're going to get an interactive dashboard. It's going to have very clearly rebuild and downscale opportunities, unused resources allowing you to reallocate precious IT dollars towards things you really need or I like this idea. Keep the savings going. Invest your Azure savings in US Cloud's Microsoft support. That's what a few other US Cloud customers do. Completely eliminate your unified spend and the savings just keep on going. Sam is the technical operations manager at Bede Gaming B E D e. He gave us Cloud 5 stars, the highest rating, saying, we found some things that had been running for three years which no one was checking. These VMs were, I don't know, 10 grand a month. Not a massive chunk in the grand scheme of how much we spend on Azure, but once you get to 40 or $50,000 a month, it really starts to add up. Yeah, it's simple. Stop overpaying for Azure, identify and eliminate Azure creep, and boost your performance all in eight weeks with US Cloud. It's true. Visit uscloud.com, book a call today to find out how much your team can save. That's uscloud.com to book a call today. Get faster, Better Microsoft support for less. A lot less. Uscloud.com we thank him so much for supporting security now and the good work Steve's doing here. All right, listen to feedback time.
- [111:46]
Steve Gibson
Yeah, Mike Sander said hello Steve, new subscriber, longtime listener. You've mentioned over the years how you're still using win 7 and maybe win 10. With win 10 soon to go out of support, I wonder if you might consider discussing how you would or would not use win 10 after October. The tech press seems to view this as a hair on fire event. Perhaps I'm numb to the risks. I have never had any antivirus beyond Defender. To the best of my knowledge, I've never had a virus. I use Firefox pretty much exclusively. I really do not want to move to win 11 for a variety of reasons. I'm sure I do not need to enumerate your views on this topic. Might be of interest to others who listen. Regards, Mike so Windows 11 I've had some updated experience with it recently is extremely pretty. I set up Several dedicated Windows 11 machines at both of my development locations because I expected that I was going to need to spend some time with Windows 11 before I'd be able to finalize the work on the DNS benchmark under Windows 11. I assumed that configuring Win 11 for native whole system encrypted DoH operation was going to drive the benchmark crazy. But to my surprise, the new DNS benchmark code code all worked perfectly under Windows 11. In any event, Windows 11 was so pretty that for a while I was a bit seduced by it. But that wore off. I've seen too many postings by people asking how they can go back to Windows 10 after making what they come to feel was the mistake of moving to 11. So since I use Windows as my daily work platform. If I'm able to avoid losing any performance to, you know, rounded corner animated zooming and fading windows, lovely as they may be, you know, and all the other stuff they've added that really doesn't matter to me, that's what I'm going to do. So I'll be sticking with Windows 10 for the foreseeable future. And given that I'm still using Windows 7, whose support ended more than 10 years ago on January 13, 2015, and that Windows 10 has an even stronger following today than Windows 7 did back then, and that so many machines are compatibility disabled to make the move to Windows 11, I suspect that Windows 10 will refuse to die. Like, you know, really stubbornly refuse. Having written the Windows 7 train, I've seen that at some point in the probably distant future, but eventually the browsers will start refusing to upgrade themselves, you know, to win, you know, any longer. Right now Chrome won't and Firefox won't and I'm using a background, a back version, the last version of Brave that would, that would agree to run on Windows 7. So, you know, as I've said, browsers are the main attack surface for PCs today, so that'll eventually become a problem. You know, my Windows 10 machines operate behind two layers of NAT routing and a PFsense firewall. They're, they're all on their own isolated land segments separate from IoT devices which are roaming around. So, and like you, Mike, I've never had a virus or a malware problem. It may be that my surfing is tame and also that I never fail to treat the external Internet as a hostile foreign power. You know, I'm never in too big a hurry to, to put something through virustotal that I downloaded and I'm not sure about before, before I using it, you know, before I, I open it or, or, or run it. And I do, you know, as much security checking as I can. Sometimes I'll actually, you know, launch something in a VM if I'm not sure. So, yeah, I'm taking a lot of responsibility for my security. Given the maturity of Windows 10, which is significantly more now than Windows 7, I can't see any reason to feel pressured to move to Windows 11 only for the sake of, of an ongoing flow of security updates to repair the things that they will be breaking in Windows 11. You know, having played with it for a while, I understand its appeal. Windows 11, it's, it is truly lovely, but I don't plan to move. So I will be glad that Microsoft will finally stop, you know, or has stopped messing with Windows 10. They're going to leave it alone. So it will have another six months of updates after October. Now we know that we're able to make it to April of 2026 before this really becomes a problem. And at that point I think that if, you know, if anyone was concerned, then the Zero Patch people will as long as Microsoft continues to offer any updates, the Zero patch guys will be reverse engineering those updates and offering them. So I think Windows 10 is going to continue for a long time into the future. Dennis Borntrager said, asked, Does Spinrite61 work on drives bigger than 2 TB? I can't get it to do it. I'll just quickly say yes. It operates actually on drives up to a 144,000 terabytes as it happens, that's 48 bits of sector addressing. The 2 terabyte limit comes about because of 32 bits of sector addressing and the use of older machine bioses. So I'm sure, Dennis, that you're attempting to connect a larger drive through USB on a machine with an older bios. You if you just move to a machine with a newer bios, as many of our testers did during the development of 6.1, it'll run on a drive of any size up to 144,000 terabytes, which probably ought to hold everybody for the foreseeable future. Rick LeBlanca said in your second zero trust example, I thought all you need to do is when he's talking about the one where we had the two customers of the one supplier and and the four boxes for whether they'd been allowed to purchase 100, 200, 300 or 400 of the items. He said, I thought all you needed to do is hash the quantity sold and give it to each other. A match means the same amount sold, but the amount is not revealed. Okay, that's technically true, but Rick's question is a great example of why these zero knowledge proofs can be so tricky. The problem with with his suggestion is that both parties could hash the various purchase quantities themselves to obtain the direct hash equivalents of those quantities. Then if either party were to reveal the hash of their quantity, the other party would see which of the hashes had been provided and they would immediately know the other's quantity. So in this case, the hashes are just unique versions of the quantities. The reason we needed to jump through all of those hoops with the locked boxes and the paper slips dropped through the slots was to concoct an algorithm that would deliberately blind both parties to any knowledge other than whether or not they had purchased the same quantity. If not, they would still learn nothing of what quantity the other party had purchased, only that it wasn't the same as theirs. So interesting, tricky problems. Lee McKinnell said hi Steve, on your comment about needing cheap biometrics for age verification, he said My smartphone in Australia cost me 100100 Australian dollars. It's a Samsung Galaxy A15. It's a current model released on 16th of December 2023. It has a fingerprint sensor that I use with bit warden and pass keys. A flagship phone is not required. I bought this phone because it was affordable. Lee from Brisbane, Australia okay, now I appreciate Lee's note and I'm glad to know that low end biometric enabled smartphones are available. And and Leo, when you were talking about people like you know, spoofing their their age authentication with a photo of somebody else or something, this is why every time I've talked about age verification I've included the the phrase non, you know, unspoofable biometric age verification. Clearly it's gotta there has to be a a biometric binding between a person's actual age and their ability to to to verify that on the fly. I checked with the Internet and it turns out that best Internet doing these days Best Buy was willing to offer me a oh now it's taking dictation. Whoops. Was was willing to offer me a brand new Samsung A15 for $39. Nice with next next day free delivery. Look at that. I was astonished. It's got a side mounted biometric fingerprint sensor, multiple cameras, a nice high res AM OLED screen, connectivity via WI Fi, Bluetooth nfc. Of course Android that means that it could almost certainly serve the as a full featured authenticator and a price of $40 would be hard to beat. I mean it's a, it's. I I was astonished by the fact that a state of the art Samsung Android smartphone could be had for 40 bucks. As I said, one of the biggest problems with age verification is that it's difficult to see how it can be done without biometrics. You know, verifying someone's age only makes sense at all if that verification can somehow be locked to their physical body. Any privacy requires that both the biometric lock and the real time age verification with some like with a remote site all be performed locally. That is if you you're going to prove that you are the age you claim you are to an adult only access site you, you can't use a third party site there otherwise you lose privacy. So it's got to be an assertion that your device is able to make of your age in this, in very much the same way that Pass Keys is able to make an assertion that you own the private key that is in your passkey. That's why I referred to Fido the other day. This is very much a Fido esque problem and that's why I talked about Stina and, and authentication. There's a lot of overlap here between passkey style, prove that I own the private key directly in a two party conversation. So what we need is we need a third party one time to, to create that identity assertion. You know, you go to the post office, you go to the dmv, you go to a notary and show, you know, improve who you are, show them a government id, prove your age, they then allow you to create a binding with your device and then there's some hope that this could happen. But anyway, I, I'm, I don't see any way that age verification can possibly may be made available for no cost because of the need for some sort of biometric, you know, attestation, a facial recognition fingerprint or whatever. So I don't know how we get there and it's going to be interesting to see and to your point and you know, I have a feeling we're going to have lots of false starts before we finally solve this problem. Unfortunately. One last piece of feedback from a listener that just came in this morning. So I updated the original show notes to version 1.1 so that I could include this from Sable Kantis who wrote regarding Project Hail Mary. He said, hi Steve, long time listener, spin right owner and SoCal native here. He said, I was listening to the show when you were thinking about the movie adaptation. I just wanted to share that I think we'll be in good hams hands with this movie. Last Saturday I attended San Diego's Comic Con and went to the panel for Project Hail Mary. Andy was there. Andy Weir, of course, the author. Andy. Andy was there with the directors and Ryan Gosling and the same screenwriter who wrote the Martian adaptation, Drew, who we talked about before they spoke about the production and the storytelling. We watched a few clips and the first five minutes of the movie. Andy Weir said that Ryan brought more depth to Dr. Grace than was written in the book. Andy stated that every number you see on screen, every formula, even if it's blurred, was Andy's work by hand. Wow. He, he made it clear that he spent hours verifying the science behind everything in the movie. Sable said, I don't expect them to capture the entire journey of a huge book. I am impressed with what I saw at the panel. I don't think they are skimping out in any way. They did show the set for the tube, and that alone showed me they are not cutting corners. Keep up the good work, Steve. Live long and live well and prosper, Sable. So I am hopeful, Leo, that. That we might get a great movie. Lori finished reading Artemis. Oh, she was. She said she was a little put off by the science because apparently it is deep in science. Like, I mean, I'm in love with it. I'm just. I'm just starting what we like. Yes. And the idea that aluminum sol melting, which is going on, on the moon, produces a huge excess of O2 and silicon, I think is very cool. And the fact that glass is made of silicon and O2, and so there's. There's a glass factory. I mean, this, like. Okay, that's. That's hard science fiction. That's. I mean, that's as hard as it gets, and I love it.
- [128:19]
Leo Laporte
Yeah. And he spent a lot of time thinking about what a moon colony would require, how you could make a sustainable moon colony.
- [128:25]
Steve Gibson
It is wonderful. Wonderful.
- [128:26]
Leo Laporte
Yeah. So you like the. You're reading the book now or not?
- [128:29]
Steve Gibson
Oh, yeah. I am into Artemis now.
- [128:30]
Leo Laporte
Okay. And you liked it?
- [128:31]
Steve Gibson
Ju. Just the beginning. I. I'm. I have a hard time making time because I. There's so much other stuff I'm trying to get done.
- [128:38]
Leo Laporte
Tell me about it.
- [128:39]
Steve Gibson
Yeah. Yeah. But I am. I am absolutely, 100%. I mean, mostly, the guy is a writer.
- [128:46]
Leo Laporte
He's a he.
- [128:47]
Steve Gibson
Really. And Lori is very choosy, and she said, as she put the book down, finishing it last night, she said, this guy is as good a writer as Michael Crichton. And that's good.
- [128:57]
Leo Laporte
You know the thing, I'm glad to hear that Lori liked it because the protagonist is a woman. And, you know, a lot of times women say men can't write. Women. But I think he did a good job, and I'm glad to hear Laurie liked it. That's good. That's good.
- [129:12]
Steve Gibson
Yeah.
- [129:13]
Leo Laporte
Good. Well, read it, everybody. I guess the movie version of that did not happen. Or maybe it's still in the cooker, I don't know.
- [129:20]
Steve Gibson
But I look forward to him. Andy is working on another book.
- [129:25]
Leo Laporte
Oh, good.
- [129:26]
Steve Gibson
He's got one on the topic of AI and of course, his style, his. His humor. Of course, he does his science. It's. And it's supposed to. Apparently he's been a little stalled because he's very involved in the movie production of. Of Hail Mary. So that has slowed down his work on this next book, but it was expected in the spring of this year. So that means it's like. Like, you know, almost done. Have another book from. From Andy, probably. You know, I would imagine late. I'm just making this up. Late summer, early autumn, maybe early fall.
- [130:05]
Leo Laporte
Good. Well, I'll interview him when he. When it comes out. If we. If he'll have us. I have kind of a tradition. I've interviewed him for every book so far.
- [130:14]
Steve Gibson
I bet he will.
- [130:15]
Leo Laporte
Which makes me think, where's Daniel Suarez? What's his latest book? I feel like. Because he did write a book about AI, I think. Yeah. In fact, all his books have a certain amount of AI in them.
- [130:26]
Steve Gibson
Oh, my God. Yeah. Yeah, yeah. The very first one, we had the motorcycles and the drones and.
- [130:32]
Leo Laporte
Yeah. I guess I'll call Daniel and I'll.
- [130:37]
Steve Gibson
Call.
- [130:40]
Leo Laporte
Andy and we'll see if we can get a little. That'd be fun to have both of them on. If I. If I can get them both, or even if I just get Andy, I'll get. I would love to have you on with us.
- [130:50]
Steve Gibson
That'd be fun.
- [130:50]
Leo Laporte
Yeah.
- [130:51]
Steve Gibson
Got me.
- [130:51]
Leo Laporte
Yeah. Good deal. Let's pause because you're going to talk about the SharePoint extravaganza, or should I say fiasco. But first, a word about our club. This is something so important to me. Should be important to use, too, Steve, because the club pays your salary. The club pays more than that. It is 25% of our operating expenses now, and I'm really thrilled. We created this club almost five years ago. Lisa was Lisa's idea. At the time, we were in the height of the pandemic and advertising was dwindling, and we thought, you know, maybe it's time to have the listeners support the network. You know, my dream from day one was to have TWIT be entirely listener supported. I think we were smart to do advertising because it's made it possible for us to grow and do a lot of stuff. But you don't want to be entirely reliant on advertising. I'd like. If you like what we do, I'd like your support. And the best way to do it is to join Club Twit. Now, here's the deal with Club Twitt. It is 10 bucks a month. That's what, $120 a year? There are several Other versions, there's a enterprise, you know, a company plan. There's also a family plan. There's even two week trials. So if you're not convinced you could do the two week trial, what do you get? You get a lot of I think great benefits. Of course primarily ad free versions of all the shows we do, which is nice. It saves you time for sure. You wouldn't even hear this plug. You also get access to the club Twit Discord which is a fabulous place to hang out with some of the smartest, geekiest people in the world. Not just during the shows, but you can also join us in the club for special events. People chat all the time about the club or in the club about all kinds of topics. 3D printing, gaming. We have a pretty active advent of code group every December. That's a lot of fun. There's also special events that go on in the club. The AI user group is coming up on Friday. That's in fact if we do an interview with Andy Weir it would almost certainly be a club event. That's, that's you know one of the ways we, we, we make the club more interesting is these extra things. Hands on tech, hands on Apple, hands on Windows. You can get the audio of those. They're open to the public but the club members get video, video as well. Stacy's book club is coming up. We're going to do a really great sci fi. It's a sci fi book club and a really great one called how you this is how you lose the time war. Not too late to read it because it's a fairly short, almost a novella length. That's August 8th. A week from Friday following the same day following the book club, we're going to do the photo segment with Chris Marquardt. We do this every month. The photo assignment is the word classic so it's not too late to take pictures. The club is fun. There's stuff going on. We're going to do the Google Pixel keynote August 20th. Micah's crafting corner. I will be doing a sewing project. Oh ah. And Micah is doing a DND one shot adventure and he's trying to figure out what the best way to do it would be. So he's got a poll that you can vote in about how would you like it to be just twit hosts or would you like to be able to participate or do you would like a mix? These are the look, this is what makes the club so much fun, so interesting. It is a place for you to hang with other like minded smart people and enjoy the benefits of being a geek. So if you're not a member, can I encourage you to go to TWiT TV ClubTWiT? Join the club. At least do the free trial because we would love to have you in the discord part of the club and we sure appreciate the support we get from our great club members. Thank you club members. We really really really appreciate it. Let's map out this week's amazing destinations and travel tips.
- [135:03]
Steve Gibson
Honestly Will, I didn't plan any trips, but I did switch to T Mobile with their new Family Freedom offer.
- [135:11]
Leo Laporte
That's not the itinerary we're following.
- [135:14]
Steve Gibson
Well, I'm departing from AT&T and EMB on a new journey with T Mobile. They paid off my family's four phones up to $3200 and gave us four new phones on the house.
- [135:27]
Leo Laporte
Bon voyage.
- [135:29]
Steve Gibson
Introducing Family Freedom. Our lowest cost will switch our biggest family savings all on America's largest 5G network. Visit your local T Mobile location or learn more@t mobile.com familyfreedom up to $800 per line via virtual prepaid card typically takes 15 days. Free phones via 24 monthly bill credits with finance agreement eg Apple iPhone16128 gigabyte 829.9 eligible trade in eg iPhone11 Pro for well qualified credits end and balance due if you pay off early or cancel contact T Mobile from unsolved mysteries to unexplained phenomena from comedy goal to relationship fails. Amazon Music's got the most ad free top podcasts included with prime because the only thing that should interrupt your listening is, well, nothing. Download the Amazon Music app today.
- [136:19]
Leo Laporte
Now on we go with security. Now one of the main reasons to be in the club is this great show and the information you get from Steve Gibson. Let's talk about SharePoint.
- [136:31]
Steve Gibson
Okay, so today's title remind to remind people is inside the SharePoint zero day RCE. RCE. Of course the abbreviation we all know Remote Code Execution. The title leaves little room for misunderstanding. A remotely exploitable code execution vulnerability exists in all unpatched, widely and long used on premises instances of Microsoft SharePoint Server. And it is known that more than 400 organizations have been attacked and hacked as a result of this flaw. Among the growing number of victims are several US Federal and state agencies, universities and hospital chains. Because a trio of Chinese apt groups appear to be behind the attacks, we would perhaps not be surprised to learn that the U.S. federal victims include the U.S. department of Homeland Security. Get this, the U.S. national Nuclear Security Administration.
- [137:43]
Leo Laporte
Not good. Not good.
- [137:45]
Steve Gibson
And the nih, the US National Institutes of Health. For those who are not tied into the enterprise world, it may not be intimately familiar with Microsoft SharePoint. Microsoft says that SharePoint enjoys 200 million users. That's not servers, that's people using it. But here's how Wikipedia describes it in two lines. They said SharePoint is a web application by Microsoft that's primarily used for building an intranet and managing and sharing files. Launched in 2001, the Year of the Space Odyssey, it was initially bundled with Windows Server as Windows SharePoint Server, then renamed to Microsoft Office SharePoint Server, and then finally renamed just SharePoint. It could be used on premises or as a Microsoft 365 hosted service, you know, in the cloud. So this news was breaking while we were recording last week's podcast. I don't know why that's happening now, Leo, but like for this is the second time, second week in a row was like, while, you know, like last last week while we were recording the podcast, Cloud strikes Outage was, you know, I mean, cloud flare, sorry, Cloud flare's big DNS outage was happening for an hour. So today's news, while we were, while we're, we were recording last week's podcast. Anyway, enough time has now taken for the story to have taken shape, so I'm going to share first what Wired wrote, since it nicely places the story into context and provides some background. And after that, we'll examine what the security firms who dug into this more deeply found. So Wired said hundreds of organizations around the world suffered data breaches as an array of hackers rushed to exploit a recently discovered vulnerability in older versions of the Microsoft file sharing tool known as SharePoint. The string of breaches adds to an already urgent and complex dynamic. Institutions that are longtime SharePoint users can face increased risk by continuing to use the service, just as Microsoft is winding down support for this platform in favor of newer cloud offerings. In other words, as I've said before, Microsoft is like saying, sorry, no, we're no longer going to support the things you bought from us in the past. Now you're going to have to subscribe to the same thing in the cloud, they wrote. Microsoft said last Tuesday that in addition to other actors, it has seen multiple China Linked hacking groups exploiting the flaw, which is this is Microsoft admittedly acknowledging this, which is specifically present in older versions of SharePoint that are self hosted by organizations. In other words, using SharePoint Server 2016 and 2019 or maybe even older ones. It does not impact the newer cloud based version of SharePoint that Microsoft has been encouraging customers to adopt for many years. Bloomberg first reported on Wednesday that's last Wednesday that one of the victims is the United States National Nuclear Security Administration, which oversees and maintains US's nuclear weapons on premises or self managed SharePoint servers are a popular target for hackers because organizations often set them up such that they are exposed to the open Internet and then forget about them or don't want to allocate budget to replace them. That sound familiar? Oh, even if fixes are available, the owner may neglect to apply them. This is Wired magazine, right? This is not this podcast. We say that all the time, wired said. That's not the case though, with the get this with the bug that sparked this week's wave of attacks. While it relates to a previous SharePoint vulnerability discovered at the PWN to Own hacking competition in Berlin in May, the patch that Microsoft released earlier this month was itself flawed, meaning even organizations that did their security diligence were caught out. Microsoft scrambled this week to release a fix for the fix, or what the company called more robust protections in its security alert. Now I'll just pause to say this really shouldn't surprise us. We've covered in the past how Microsoft's current incarnation of security updates appears to focus upon implementing a quick fix for the symptoms rather than addressing underlying systemic weaknesses. I don't know that's what happened in this instance, but if it quacks like a duck, Wired continued writing A Microsoft spokesperson wrote in an emailed statement, quote, at Microsoft, our commitment anchored in the Secure Future initiative is to meet customers where they are. That means supporting organizations across the full spectrum of cloud adoption, including those managing on premises systems. Wow. Okay. Talk about statement that says nothing. Anyway, Wired continues, Microsoft still supports SharePoint server versions 2016 and 2019 with security updates and other fixes, but both will reach what Microsoft calls end of support on July 14, 2026. Well, okay, this is the 20th. This is the 29th. So that happened SharePoint Server 23rd, 20. I'm sorry, 2026. So next year. What am I saying? This is 2025. So July 14, 2026. So just just short of a one year from now, support for 2016 and 2019, SharePoint servers will end, they wrote. SharePoint Server 2013 and earlier have already reached end of life and receive only the most critical security updates through a paid service called SharePoint Server Subscription Edition. Right. So you could subscribe to as now Microsoft is doing to receive extended support Wired wrote. As a result, all SharePoint server versions are increasingly part of a digital backwater where the convenience of continuing to run the software comes with significant risk and potential exposure for users, particularly when SharePoint servers sit exposed on the Internet. Jake Williams, a longtime incident responder who's vice president of research and development and hunter strategy, said, quote, years ago Microsoft positioned SharePoint as a more secure replacement for old school Windows file sharing tools. So that's why organizations like government agencies, maybe the CIA invested in setting up those servers and now they run at no additional cost compared to Microsoft. 365 subscription in the cloud that requires continuous payment. Okay, this is, this is, you know, this is not me saying this again. This is somebody else. So no surprise, he says. So Microsoft tries to nudge the holdouts by charging for extended support. But if you're exposing a SharePoint server to the Internet, he said, I would emphasize that you also have to budget for incident response because that server will eventually get popped, unquote. Wired says the United States Cyber Security and Infrastructure Security Agency said in a in guidance about the vulnerability Tuesday that, quote, CISA recommends disconnecting public facing versions of SharePoint server that have reached their end of life or end of service. For example, SharePoint Server 2013 and earlier versions are end of life and should be discontinued if still in use. Now the problem is it's working and it's been paid for. So when budgets are tight and when are they not going through all the hassle of switching to a paid Microsoft cloud based service and then needing to continue paying for it can be a difficult sell to upper management. As I've observed here recently, the entire model that's evolved across our industry of selling online software systems that are later found to have critical vulnerabilities and expecting their users to suddenly take proactive responsibility or even be aware that there's a problem that needs their attention is inherently impractical and is badly broken in practice. Wired's author of this article apparently agrees, writing, the ubiquity of Microsoft's Windows operating system around the world has led to other situations in which a long goodbye is the way he put it. A long goodbye has created security issues for holdout users and other organizations or individuals with connections to a vulnerable entity. Microsoft struggled to deal with the long tail of users on extremely popular Windows editions, including Windows XP and Windows 7. And of course I would expect this whole drama to repeat itself with Windows 10 starting soon, wired wrote. But legacy software is a challenge for any software or digital infrastructure provider. Earlier this year, for example, Oracle reportedly notified some customers about a breach after attackers compromised a legacy environment that had been largely retired in 2017, yet people were still using them. The challenge with a service like SharePoint is that it often acts as an ancillary tool without ever being the center of attention, meaning it's just kind of there in the proverbial back closet somewhere, working and forgotten. Bob Huber, chief security officer at the cybersecurity company Tenable, says quote for on premises software like SharePoint, which is deeply integrated into the Microsoft Identity stack, there are multiple points of exposure that need to be continuously monitored in order to know, expose and close critical gaps, unquote. When asked about the alleged breach at the nuclear at the National Nuclear Security Administration, the Department of Energy emphasized that the incident did not impact sensitive data or classified data. A DOE spokesperson told Wired in a statement, quote On Friday, July 18, the exploitation of a Microsoft SharePoint Zero Day vulnerability began affecting the Department of Energy, including the nnsa. The department was minimally impacted due to its widespread use of the Microsoft 365 cloud and very capable cybersecurity systems. So a bunch of them had migrated to the cloud, but not all, he said. A very small number of systems were impacted and NSA is taking the appropriate action to mitigate risk and transition to other offerings as appropriate. So maybe this, you know, this incident has spurred people to move to the cloud. Microsoft Wired Finishes say Microsoft did not immediately return WIRED's request for comment about the process of sun setting SharePoint Server. The company wrote in a blog post on Tuesday that customers should keep supported versions of SharePoint Server updated with the latest patches, although that didn't help in this case, and turn on Microsoft's Anti Malware scan interface as well as Microsoft Defender antivirus. Unfortunately, as we saw, we're going to get some more information on this now. Microsoft fumbled and botched the security patch during May's Pone to Own competition, which we covered at the time since it was the first time Pone to Own had been held in Berlin. Having moved from Toronto, a researcher with with Cyber Security with the cyber security arm of Vittel, a telecom firm run by Vietnam's military, identified a SharePoint bug dumb dubbed Tool shell and demonstrated a way to exploit it. That discovery won the researcher an award of $100,000. But here's where the plot thickens. Exploits discovered by security researchers remain explicitly secret. We only learned that there is a flaw and of its general nature and nothing more. As part of the researchers agreement, they confidentially provide all required information to Trend Micro Zero Day Initiative team, which then in turn forwards that information to the affected software vendor with a 90 day time expiration on that zero day flaw being patched. The publication we all know the Register theorizes that the exploit may have leaked from Microsoft. I don't, I don't buy into it completely, but here's what the Register said they said less than two months later, on July 8th, Microsoft disclosed the two CVEs 49704, which allows unauthorized remote code execution, and 49706, a specific spoofing bug, and released software updates intended to patch the flaw. So so July 8th was Patch Tuesday earlier this month, the Register wrote. But mass exploitation had already started the day before on July 7th. Now that's not true. Some exploitation had started, not the mass exploitation. Dustin Childs quotes the Register head of Threat Awareness at Trend Micro Zero Day initiative said quote 60 days to fix isn't a bad timeline for a bug that stays private and stays under coordinated disclosure. What is bad is that a leak happened which is which may have been true. Again, no proof of it. Patch Tuesday happens the second Tuesday of every month, writes the Register. In July. That was the eighth. But two weeks before then Microsoft provides early access to some security vendors via the Microsoft Active Protections program mapp. These vendors are required to sign a non disclosure agreement about the soon to be disclosed bugs and Microsoft gives them early access to the vulnerability information so that they can provide updated protections to customers faster, Childs said. Childs with Trend Micro said the first MAPP drop occurs at what we call R minus 14, meaning 14 days before release release minus 14. In this case that was June 24th. Then on July 7th, which was one day before the patch Tuesday, he said we started to see attacks again not apparently mass and widespread. July 8 the patches were out and were almost immediately bypassed. Well they were almost immediately bypassed for another reason. ZDI writes the Register along with other security providers poked holes in the initial patches true and determined that the authentication bypass piece was too narrow and attackers could easily bypass this fix. In fact, writes the Register, anyone who received the early MAPP information about the CVEs and software updates would be able to tell that this is an easy way to get past it. I want to make sure I don't forget to mention that once the Patch Tuesday patches came out they were immediately diffed. You know differences made and the patches were reversed in reverse engineered from the diffs not from any MAPP or not necessarily using any MAPP advanced information. So you Know a lot is still unknown. The register finishes saying on July 18, iSecurity first sounded the alarm. So it was on the 18th of July, 10 days later, 10 days after patch Tuesday, that the actual large scale exploitation of a new SharePoint remote code execution vulnerability chain in the wild was seen. And. And one day later, that's when Microsoft warned SharePoint server users that three on prem versions of the product included a zero day flaw. Including a zero day flaw was under attack and that its own failure to completely patch the holes was to blame. Okay, but there's more. Shodan shows that around 8,000 SharePoint servers in use by auditors, banks, health care companies, major industrial firms and US state, federal and international government bodies are in use. 8,000. In other words, it's a mess. The 8,000 figure might be conservative because the Shadow Server foundation, which continuously scans the Internet for potential digital vulnerabilities, put the number at a little more than 9,000, cautioning that that figure is a minimum. That is a minimum of more than 9,000 instances of SharePoint of vulnerable SharePoint on the Internet, meaning that they were able to confirm that 9,000 figure. And there's like, there's likely more. The Shadow Server foundation said most of those affected were in the United States and Germany. The last thing I want to share is some of the very interesting reporting by the researchers at I Security. Those were the first people to report this and to report that basically the attacks went viral. And the last thing you want is it just to hear that a zero day remote code execution vulnerability attack has gone viral. Remember that the first known instance of exploitation occurred on the day before the July 8th patch Tuesday, which was exactly three weeks ago today. As we're recording today's podcast, the Isecurity researchers wrote on the evening of July 18, iSecurity was the first to identify large scale exploitation of a new SharePoint remote code execution vulnerability chain in the wild demonstrated just days before on X, which is, you know, what used to be called Twitter, the X platform. This exploit is being used to Compromise on premise SharePoint servers across the world. The new chain we uncover in this blog was later named and then they updated CVEs. Microsoft had the first round of CVEs. Then when they fixed the fix they gave them CVEs 53770 and 53771 they wrote before this vulnerability was widely known. Last Friday our team scanned over, get this, 23,000 SharePoint servers worldwide in total at that time. That is again before this vulnerability was widely known. Last Friday they discovered more than 400 systems actively compromised during four confirmed waves of attack. So there was so four confirmed waves of attack. They enumerate them the initial attack wave 17th of July at 12:51 UTC coming from IP 96.912-5147. They they think that was a testing wave to verify their exploit. Then there was attack wave one the next day on the 18th of July at 1806 UTC coming from a different IP 107191 58, 76 and that one was widely successful. The next the the the third wave the the second big attack wave the the following day 19 July at 728 UTC originating from IP 104, 238, 159, 149 and then multiple smaller waves on and after 21 July after a public proof of concept exploit script was released on GitHub. So basically the world knew about it at that point. And remember all of those attacks were effective against both unpatched, that is Never before patched and then fully patched post Patch Tuesday SharePoint servers. So there was a 10 day window from July 8th through July 18th when these attacks were effective and even after the 19th before the updated update got out to everybody. So in this instance it was Microsoft's significant fumble of the initial patches that were readily bypassed because they were merely cosmetic symptom covering patches of the sort that we've seen before. There are postings on the net by people saying that they diffed Microsoft's Patch Tuesday patches. That is not members of the MAPP program who received them from two weeks before Patch Tuesday. But they got the the Patch Tuesday updates, found out what the differences were that affected SharePoint server and then reverse engineered the patches and wrote code to sidestep the IM the imperfect fixes that Microsoft had attempted to implement in Patch Tuesday. So basically Microsoft made things much worse by by poorly patching SharePoint server on Patch Tuesday because then everybody else in the world was able to see what they changed, take a close look at it and see that Microsoft had not actually fixed the problem. Note also that Microsoft's updated patches which do now the updated patches do now actively res. You know, actually resolve the problem. Those only cover SharePoint Server 2016 and 2019. SharePoint Server 2010 and 2013 which are on the Internet, remain vulnerable and no patch for those is expected. So they must either be isolated from the public Internet or shut down. Okay, so what exactly. And this is really cool because it's a sort of A here's how like exactly what happened this here. Here's what the I security guys saw that led into this whole thing, they wrote early in the evening, our 24. 7 detection team received an alert from one of our CrowdStrike Falcon EDR deployments at a specific customer. The alert flagged a suspicious process chain on a legacy SharePoint on prem server tied to a recently uploaded malicious aspx file. At first glance, it looked familiar. A classic web shell obfuscated code in a custom path designed to allow remote command execution via HTTP. We've seen many of these before. What made this one stand out, however, is how it got there. Our first hypothesis was mundane but plausible. A brute force or credential stuffing attack on a federated active directory identity followed by an authenticated upload or remote code attempt using valid credentials. The affected SharePoint server was exposed to the Internet and tied to Azure Active Directory using a hybrid ADFS that stack when misconfigured or outdated, can be a dangerous combination. It all seemed to confirm the theory. Credentials compromised, shell dropped, persistence achieved but examining the IIS logs the web server Examining the IIS logs more closely, we noticed that the referrer was set to slash underscore layouts forward. You know, forward/signout aspx. That's odd, they wrote. How can that be an authenticated request just after the user has logged out? Something didn't add up. We found no successful authentications in ADFS logs, or the logging was at least insufficient. Malicious IIS logs did not contain a value in the username column. A post request to the underscore layouts/15/toolpane aspx seemed rather specific. Referrer set to underscore layouts under or forward/signout aspx cannot be authenticated right. We began to develop a feeling that credentials were never used. So how could the attacker write files to the server without ever authenticating at all? That's when we realized we were no longer dealing with a simple credential based intrusion. This wasn't a brute force or phishing scenario. This was zero day territory. After some digging, we learned that three days earlier the offensive security team from Code White GmbH demonstrated they could reproduce an unauthenticated RCE exploit chain in SharePoint, a combination of two bugs originally presented at Pwn to Own Berlin earlier this year. In May, those bugs were still present in the patched SharePoint server they dubbed the chain tool shell. What we discovered on the 18th was not a credential issue. We had stumbled upon a weaponized pwn to own exploit already being used in the wild. When our team began reviewing the impacted systems, we expected to find the usual suspects standard web shells designed for command execution, file uploads, or lateral movement. Instead, what we discovered was more subtle and arguably more dangerous a stealthy spinstall 0. Aspx file whose sole purpose was to extract and leak cryptographic secrets from the SharePoint server using a simple get request. This wasn't your typical web shell. There were no interactive commands, reverse shells, or command and control logic. Instead, the Page invoked internal. NET methods to read the SharePoint server's machine key configuration, including its validation key. These keys are essential for generating valid view state payloads, and gaining access to them effectively turns any authenticated SharePoint request into a remote code execution opportunity. Then it all clicked once the machine key configuration, including the validation key had been obtained. Future payloads can embed any malicious commands and would be accepted by the server as trusted input, completing the RCE chain without requiring any credentialing. This mirrors the earlier SharePoint design weakness exploited four years ago in 2021, but it's now been packaged into a modern zero day chain with automatic shell drop and full persistence with zero authentication. More than 24 hours after we published our initial findings and reached out to affected vendors, including Microsoft, the Microsoft Security Response center issued an official advisory and assigned vulnerability identifiers on their page. Microsoft confirmed active exploitation in the wild and acknowledged the severity of the issue. They make one final crucial point. Due to the fact that this is a machine key exfiltration attack, they said. The attack we've observed specifically targets the exfiltration of of SharePoint Server ASP dotnet machine keys. These keys can be used to facilitate further attacks, even at a later date. It is critical that affected servers rotate SharePoint Server ASP net machine keys and restart IIS on all SharePoint servers. Patching alone is not enough if you are not targeted or you are unsure. We also advise teams to rotate their machine keys just to be sure it has no system impact, only that IIS is offline for some seconds while restarting services. So we don't know how many systems, enterprises, organizations and networks have been compromised as a result of Microsoft's botched patches for the original pwn to own zero day. But that number lies somewhere between the 400 that have been confirmed and the 9,000 that were known to be vulnerable by the Shadow Server Foundation. And the attackers were aggressive and automated. This was, you know, this is a, this is a great deal of damage and the ransomware demands have Already begun as an industry. We need to do better, we need to change the model. And of course this has been an important high profile incident. That individual. So much so that individual reports have now been published by Broadcom's semantic CISA, Cisco, Talos Census Checkpoint, CrowdStrike, iSecurity, Log Point, Microsoft Orange, Palo Alto Networks, Qualus Sentinel 1 Tenable, Trend Micro and Veronis another.
- [172:11]
Leo Laporte
All of whom are sponsors of this show.
- [172:13]
Steve Gibson
Pretty much everyone.
- [172:14]
Leo Laporte
Make it easy.
- [172:15]
Steve Gibson
Pretty much everyone.
- [172:17]
Leo Laporte
You know, one sysadmin or security researcher said you should just assume that you, if you are running on prem SharePoint that you are compromised. You should not assume that you're not.
- [172:30]
Steve Gibson
Yes, unplug Repatch update patches, rotate your keys. And then of course you need to worry about if something crawled in, where might they else? What? What? Where else?
- [172:42]
Leo Laporte
Yeah, they may have already breached your rest of your network. Yeah, that's why I set up my. My thinks Canary, our sponsor thinks Canary's honey pot to be SharePoint 10. Just, you know, just to see. That's one of those things. Nobody the outside is going to get into it. But, but if. If somebody is in our network, that's the first thing they'd go to and go, I know how to hack that. Because that was unpatched anyway. What fun. Not for the port. 9,000 people who run on prem SharePoint.
- [173:14]
Steve Gibson
So I imagine, you know, this will push some people into the cloud.
- [173:22]
Leo Laporte
Yeah, but if you're the, you know, if you're in charge of the nuclear weapons, you probably don't want to run in the cloud. Right. You probably want on prem. But maybe you should.
- [173:33]
Steve Gibson
Cloud's got its own problems. I mean it was all of the people who had their email in the cloud that had Shiner reading their email.
- [173:41]
Leo Laporte
Right? Oh Lord. Dale Poco in our YouTube chat says it would Pondone was in Vancouver, not Toronto. I don't know, maybe he's Canadian and he cares. I don't know. But it was in Vancouver.
- [173:56]
Steve Gibson
Oh. Oh, yeah, yeah, yeah, yeah. Thank you for the.
- [173:58]
Leo Laporte
Yeah, I know what you meant. You meant Canada.
- [174:00]
Steve Gibson
I meant Canada. And of course I have such fond memories, Leo, of you and me in Toronto. When you first proposed that we do this podcast show in Toronto 20 years ago.
- [174:13]
Leo Laporte
But you must have come to the lab.
- [174:14]
Steve Gibson
You were bored, Leo. And you were. You are no longer bored.
- [174:18]
Leo Laporte
I don't have enough to do, Steve. I merely only had five days. A week, a month.
- [174:22]
Steve Gibson
And you had. Yeah, and you had the weekend show, the weekend radio show and you were just at Loose ends. You know, the other day, and you said, let's do a podcast.
- [174:31]
Leo Laporte
What do you think? And you said, what's a podcast?
- [174:34]
Steve Gibson
I did.
- [174:37]
Leo Laporte
Well, not way back then. Yeah, yeah. We all know now. 20 years in. Your 20th anniversary is coming up this month. Next month.
- [174:48]
Steve Gibson
Yep, Yep.
- [174:50]
Leo Laporte
Wow, wow, wow. So it was 2005. Yeah, the fall of two or summer of 2005. I said, hey, Steve, let's do a show. Unbelievable.
- [175:06]
Steve Gibson
Well.
- [175:06]
Leo Laporte
Oh. Dale Poco lives in a suburb of Vancouver. That's why he cares.
- [175:09]
Steve Gibson
Now remember that the. The. The. The first few, I would bring. I would bring the microphones to. To. To Toronto and we sat in your hotel room.
- [175:22]
Leo Laporte
That's right. And once we did it on the roof, didn't we, of the. Of the Drake in. In. In Toronto. I think so, yeah. Yeah, I remember we. I had a really cool thing. You could plug in multiple microphones too.
- [175:35]
Steve Gibson
Yeah, of course you did. Of course you had whatever gadget was.
- [175:38]
Leo Laporte
A good excuse to buy that crap.
- [175:40]
Steve Gibson
Yeah, an SD card and.
- [175:41]
Leo Laporte
Or a.
- [175:42]
Steve Gibson
A. The. The square thingy.
- [175:45]
Leo Laporte
Oh, compact. Compact flash.
- [175:47]
Steve Gibson
Compact flash. Compact flash card. Yeah.
- [175:49]
Leo Laporte
You know, we had all of that stuff until we closed the studio down. At that point, we had to sell or give away most of it. I think a lot of it went to schools and other people could use it. Thank you, Grayson. For $5. He is just donated in our YouTube chats. In our super chat. Thank you, Grayson. Grayson's always in here listening. He's a. He's a regular. So, Steve, I hope you're all regulars. You should come back every week. We do this show Tuesdays right after Mac break weekly. That's about 1:30 Pacific, 4:30 Eastern, 20:30 UTC. You can watch live, as I mentioned, on YouTube and Twitch and TikTok and Facebook and LinkedIn x.com kick war in our club, Twit Discord. If you're fortunate enough to be a club member, or I should say generous enough to be a club member after the fact, we put it up on the website, Twitter TV SN. Actually, we have two versions, 128 kilobit audio, MP3. And we have video so you can see Steve's mustache at work. But Steve has his own unique versions on his website, GRC.com he's got 16 kilobit audio, which to be frank, isn't the highest fidelity, but it's a small download, so you take your choice. He also has a perfectly good quality 68. I'm sorry, 64 kilobit version, MP3. He also has the show notes there. Fantastic human written transcriptions from Elaine Ferris, so you can read along or search. He also has other things there. You know, you've heard perhaps him mention a little thing called spin, right? Version 6.1 of the World's best mass storage, maintenance, recovery and performance enhancing utility is available@grc.com and that is Steve's bread and butter. So if you don't have a copy and if you have mass storage, which I think you do, and who doesn't get spinner work, we found out last week it works on a Kindle, for crying out loud. Amazing. There's lots of other stuff there. GRC.com is a treasure trove. It's more like Steve's attic with all sorts of stuff, little nooks and crannies and you could just spend days there. So check it out. If you want to send Steve an email, that is not so easy. Steve doesn't like spam, so what you have to do is go to grc.com email, enter your email address there. Steve will validate it. Now you're whitelisted and you can send him email. You can also, it's not done by default, so look below that and you'll see two checkboxes, one for the security. Now show notes. You can get those emailed to you a couple of days ahead of time. Prepare for the show, if you will. There's also a much less frequent newsletter that he sends out whenever he's got something new. Thank you, Ixion. Another. Another contribution of I don't know why. $4.20. What is 4:20? It's an interesting amount. We know what you're up to, Ixion. Or is it 9? Eon? I'm not sure if those are Roman numerals. Anyway, thank you. The Super Chat donations are great, although the best way to support us, as I mentioned, join the club. That way you get, you know, automatic memberships, plus you get lots of additional benefits. But if you just want to donate in the Super Chat or subscribe, by the way, if you go to the Club Twitt page, Twitter, TV Club to it, you can just subscribe to Security Now. I think that's. Is that four or five dollars a month, it's. It's less expensive. So you can. If that's the only show you listen to, you can absolutely do that. Steve will be back next week, as will I, in August. The guns of August. Yes. See you then, Steve.
- [179:30]
Steve Gibson
Bye.
- [179:33]
Leo Laporte
Security now.