← All TWiT.tv Shows (Audio)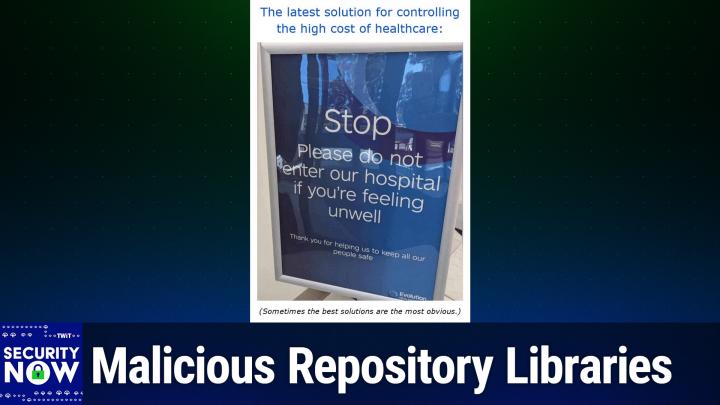
All TWiT.tv Shows (Audio)
Security Now 1038: Perplexity's Duplicity
03:03:49
Malicious Repository Libraries
Loading summary
Transcript377 lines
- [00:00]
Leo Laporte
It's time for security now. Steve Gibson's here. The government has something to say to federal agencies regarding SharePoint. Oh, and there's another oh my God exchange flaw you need to know about. We're going to talk about the best ad blocker finally coming to Safari. A very popular firewall that has been compromised. And why if you have a Dell Latitude or Precision laptop, you must listen to this show. All that more coming up next on Security Now. Podcasts you love from people you trust. This is Twit. This is Security now with Steve Gibson. Episode 1038 recorded Tuesday, August 12, 2025. Perplexity's duplicity. It's time for Security Now. I know you wait all week for this. It's Tuesday. Woo hoo. The best part of Tuesday is when Steve Gibson shows up to fill us in on what horrible things have been happening all week. But you know Steve, it's funny because it doesn't scare me. It reassures me there's some sanity in all this, that there's somebody thinking about this. And even if we're decrying Microsoft's, you know, inability to write safe software or you know, the rants, this plague of ransomware, it feels like it's, it's being managed by this guy right here. So thank goodness for, well, and, and.
- [01:32]
Steve Gibson
Actually not by me, I'm just reporting on it. But I would argue that the, all the problems which have been created have created an another industry of their own. All these security researchers who are digging into this stuff. We have a, what we have what we're talking today about Cisco's Talos Group who went like way beyond the call of duty, reverse engineering a chip in Dell laptops. And you know, thanklessly, they didn't know what they were going to find. What they found was horrifying as it turns out. And it's, it's like Dell, you know, made it more difficult. Somewhere Dell has a file of all the source code of the firmware in this security chip. But do they give it out? No, it's proprietary. So that, but thankfully the laws have indicated that reverse engineering something you own is within your legal rights. And so here they find this massive problem in more than 10 million, more than 100 models of Dell laptops and, and said oh by the way Dell, here you go, here's the fix. Yeah, like thanklessly essentially. So, so there is this huge industry that has, that basically sprung up to, to deal with some of the consequences of the fact that boy, we just jumped into all this without really knowing how to write code that was bug free once upon, you know, once upon a time when it is your word processor and the cursor would disappear, be like, oh, well. And you'd shut it down and start up again and get your cursor back. Now, you know, something crawled into your network and erased all your, all your data. So it's a different scale of problems. Anyway, we're going to have fun today because today's topic for security now, episode 1038. And you're going to check Leo. But I, I had it in my brain last time we talked about this, that between this Tuesday and next Tuesday is the anniversary of this podcast.
- [03:46]
Leo Laporte
The first now was August 18, 2005. Yes.
- [03:51]
Steve Gibson
So it will be before we're here again on the 19th.
- [03:56]
Leo Laporte
Wow.
- [03:56]
Steve Gibson
Will be the anniversary. So that means this is the last podcast of our 20th year and we'll be starting into year 21, finally, all grown up.
- [04:06]
Leo Laporte
We can drink.
- [04:07]
Steve Gibson
That's right. We don't have to. When we press the I'm 21 button now, it's the truth. So.
- [04:14]
Leo Laporte
Wow. By the way, you can, if you go to our website, We've got all 1038 episodes, including this, the very first one from August 18th. It's kind of fun to listen to the first one. I have to say, we've come a long way since then. Let's go.
- [04:30]
Steve Gibson
Well, yes, and I'm.
- [04:32]
Leo Laporte
I've. Yeah, yeah, we gotta.
- [04:36]
Steve Gibson
We figured out how to do this. So today's topic is perplexities, Duplicity.
- [04:43]
Leo Laporte
Oh, I really wanted you to talk about this.
- [04:45]
Steve Gibson
Oh, am I going to?
- [04:48]
Leo Laporte
Because it was a complicated story and I wasn't sure who to believe.
- [04:52]
Steve Gibson
It was a complicated story, but it's actually, it's part of a much bigger story. And so I'm going to spend some time before we get into the details of what Cloudflare found, setting a larger context. Because as I did this, this just started out as a news blurb at the top of the show. And as I dug into it more, it became our topic for the day. But first, we're going to talk about CISA's emergency directive to all federal agencies regarding SharePoint Nvidia firmly saying no to the notion of any embedded chip gimmicks. Lash Dash Lane is terminating. Terminating its free tier and the mo. When I looked at this, I couldn't believe how limited the free one was. First I was thinking, oh, I'm gonna, you know, make sure our listeners know there's no one. There's no way anybody could actually be using it so it's kind of a non big deal, in other words. Yeah, exactly. Also we got malicious repository libraries becoming even more hostile. The best web fil has come to Safari, a very popular or well the very popular Sonicwall firewall is being compromised and that's not good. Also, as I mentioned, it turns out that more than 100 different models of Dell's Latitude and precision laptops are in serious danger. So definitely any of our listeners who are Dell Latitude laptop users need to go to a link that I've got in the show notes the oh, and one of our listeners is an enterprise IT guy who I mentioned last week because he wrote me an updated email saying hey, I. I hear that you're going to talk about me this week. Here's a little more. And what he wrote was so much more that I had to excerpt from it. But a really good look into the the behind the scenes what it actually takes to keep Microsoft stuff synchronized. And it turns out it's not as easy as just saying, oh, let's apply a patch to SharePoint. The ripple effects are astonishing. Also, we're gonna as a consequence of another listener question, take a look at where I am with the DNS benchmark because I want to share some of the things that have been happening over the last six months. Turns out that maybe incontrol is my incontrol freeware may be preventing some updates which people may want or may not. Also tonight a venerable Sci Fi franchise is getting a new series that looks quite hopeful. We're going to talk about that and then take a look at the the generic problem of AI website sucking in the context of and and basically put on the map because of what Cloudflare has documented about what they discovered that Perplexity was doing.
- [08:09]
Leo Laporte
So interesting.
- [08:11]
Steve Gibson
Really, really, really good podcast. I think maybe Leo we got the.
- [08:14]
Leo Laporte
Hang of it now after 1038 episodes and 20 years, we finally learned how to do a podcast.
- [08:23]
Steve Gibson
Our. Our great friend Alex Nio used to our first advertiser.
- [08:29]
Leo Laporte
Yes.
- [08:30]
Steve Gibson
And he used to send me mail saying Steve, it's better than ever. Steve. It's. I think he finally got tired of saying that or felt that maybe it was redundant.
- [08:37]
Leo Laporte
But he still listens. I know because we hear from him all the time. Yeah.
- [08:40]
Steve Gibson
Hi Alex. Good.
- [08:42]
Leo Laporte
All right, so a big show coming up and of course our picture of the week, which I have as always sealed myself in a soundproof booth and I have.
- [08:49]
Steve Gibson
I have so much fun with this one. Yeah.
- [08:52]
Leo Laporte
Well, I'll get my Tell us why.
- [08:54]
Steve Gibson
We'Re here and then we'll do that.
- [08:55]
Leo Laporte
Yes, well, we're here because of you, Steve, but because we don't want Steve to work for free. We also have some sponsors and the.
- [09:03]
Steve Gibson
Club and we have here the price of coffee is going up, so.
- [09:08]
Leo Laporte
Oh, I'm not happy about that. But you know what? There's some things worth paying for in life. Like Zscaler, our sponsor, the leader in cloud security. You know, AI is a really interesting thing. It's, it's, it's, it cuts both ways, I guess. On the one hand, bad guys are using AI to breach your organization, right? Faster than ever. On the other hand, you and your organization may be using AI to power innovation, to drive efficiency. So it helps bad actors deliver more relentless and effective attacks, helps you be more efficient. Here's a stat that's depressing. Phishing attacks over encrypted channels increased last year by 34.1%. And it's really fueled by the growing use of generative AI tools on the part of the bad guys. And things like phishing as a service kits don't help. Organizations in every industry from small to large are using AI positively too to increase employee productivity with public AI. For engineers with coding assistance, it's amazing what it can do. Marketers are using AI to create campaigns. Finance is using AI to create spreadsheet formulas they couldn't even dream of. You're automating workflows for operational efficiency across individuals, across teams. You're embedding AI into applications and services that are customer and partner facing. Ultimately, AI lets you move faster in the market and gain a competitive advantage. But of course, you've got to use AI intelligently, right? Because AI can also leak information. It can also be a problem as much as it is a boon. And of course we know that AI is a really big tool for hackers. So companies, you gotta rethink how you protect your private and public use of AI. You also got to rethink how you defend against AI powered attacks. That's what Zscaler is going to help you with on both sides. Jeff Simon, who's the senior vice president and CISO at T Mobile, said Zscaler's fundamental difference in the technologies and SaaS space is that it was built from the ground up to be a zero trust network access solution, which was the main outcome we were looking to drive. That's the chief security officer. T Mobile uses Escalar. I know T Mobile knows this and big companies know this. The traditional way we protect ourselves is with perimeter defenses. Firewalls and then VPNs because you got to come in through the firewall. What does the VPN do? It gives you a public facing IP address. Exposing an attack service that these days is no match in the AI era. We need a modern approach and that's what Zscaler's comprehensive Zero trust architecture plus AI ensures you get safe public AI productivity. It protects the integrity of the private AI you're using. And, and this is the beauty of zero trust completely stops AI powered attacks, even attacks no one's ever seen before. You can thrive in the AI era with zscaler. Zero trust plus AI stay ahead of the competition and remain resilient even as threats and risks evolve. Learn more@z zscaler.com security that's cscaler.com security we thank them so much for their support of security. Now, now is the moment on security. Now I always look forward to.
- [12:37]
Steve Gibson
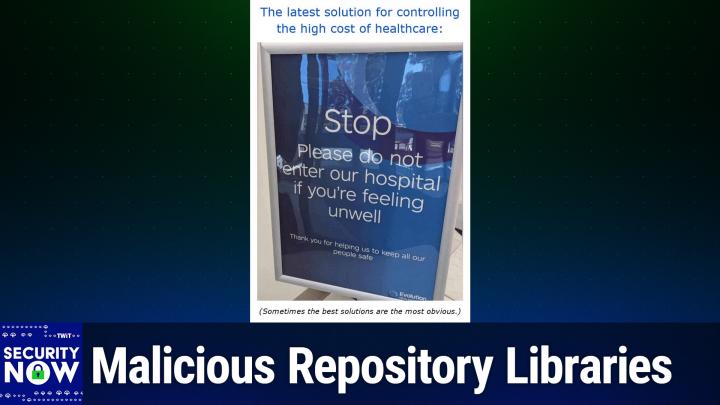
Okay, now I gave this picture the caption. The latest solution for controlling. For controlling the high cost of health care.
- [12:49]
Leo Laporte
Okay.
- [12:50]
Steve Gibson
The latest solution for controlling the high cost of healthcare.
- [12:54]
Leo Laporte
And we are gonna now scroll up and see what that solution is. As soon as I get my mouse to scroll, scroll, mouse. You know what? I laugh, but this is exactly the sign that I see every time I go to the doctor. Want to read it for us, Steve?
- [13:16]
Steve Gibson
Yeah. This is a big sign. Again, the latest solution for controlling the high cost of health care. This is a large sign that says stop. Please do not enter our hospital if you're feeling unwell.
- [13:32]
Leo Laporte
Only healthy people in the hospital. Please.
- [13:35]
Steve Gibson
That's right. If you're feeling great, you don't have any problems or complaints, come right on in.
- [13:42]
Leo Laporte
It does cut costs considerably. Professional. That's so great.
- [13:47]
Steve Gibson
And I gave her the little subhead. Sometimes the best solutions are the most obvious.
- [13:51]
Leo Laporte
Yes.
- [13:52]
Steve Gibson
So, you know, why didn't I think of that? Yeah, that's right. Okay, so Last Thursday the 7th CISA issued a rare emergency directive ordering all. And in the reporting, all was in all caps all federal agencies to patch a new attack vector in Microsoft Exchange email servers. So this is an Exchange not in SharePoint, Microsoft Exchange. And this was Thursday the 7th. Gave them just four days, which included the two days over the weekend in which to do so. They had until Monday morning to get this done. Okay, so let's step back for a moment and examine CISA's authority to compel the actions of federal agencies. It turns out the authority does exist. And it comes from section 3553, paragraph H of title 44 of the US Code which says authorizes the Secretary of Homeland Security in response to a known or reasonably suspected information security threat, vulnerability or incident that represents a substantial threat to the information security of an agency to quote, issue an emergency directive to the head of an agency to take any lawful action with respect to the operation of the information system, including such systems used or operated by another entity on behalf of an agency that collects, processes, stores, transmits, disseminates or otherwise maintains agency information for the purpose of protecting the information system from or mitigating an information security threat. So indeed this is in the law. CISA is able to, you know, acting under the auspices of the Secretary of Homeland Security, to tell all federal agencies they have to do something. So CISA's emergency directive in this case explains what's going on. It says CISA is aware of a post authentication vulnerability in Microsoft Exchange Hybrid joined configurations that allows an attacker to move laterally from on premises exchange to the M365 cloud environment. They said this vulnerability poses grave risk to all organizations operating Microsoft Exchange Hybrid joined configurations that have not yet followed the April 2025 patch. Guidance and immediate mitigation is critical although that they said although exploitation of this vulnerability is only possible after an attacker establishes administrative access on the on premises Exchange server, CISA is deeply concerned at the ease with which a threat actor could escalate privileges and gain significant control of a victim's M365 exchange online environment. So as I mentioned the the emergency directive issued on Thursday begins with by 9.0am Eastern Daylight Time on Monday August 11th, 2025 all that's where the caps are agencies must and then it goes on so that was yesterday, you know, based on when we're recording this podcast and then it proceeds to enumerate a rather long list of steps that must be taken and reported back to CISA upon their completion. This all surrounds an Exchange server turns out not a really a bug a design flaw which affects this hybrid on prem cloud environments where Exchange on premises servers sync their data to an Exchange online you know cloud based instance. Microsoft explains explained that in old default setups prior to this April 2025 update to the architecture on PREM servers shared the authentication service known as service principle with the synced online instance. When deployed for the first time, the default hybrid installations would upload the on prem authentication certificates to the service principle to allow local instances of Exchange to authenticate with the Exchange online server and in order to sync their data. The problem arises when attackers compromise an on premises Exchange server because they can abuse their control over the system to hijack, create or alter authentication tokens that grant intruders access further up the cloud environment. And what's more, Microsoft says this attack scenario does not leave, they said, quote, easily detectable and auditable auditable trace, meaning that this could all be invisible to compromise companies. Look at your logs. You know, there's just no indication this has been going on. This is not something Microsoft had thought to log. So owners of on Prem servers must install the April hotfix. And as I said, a little bit later, we'll take a look at why that's not as easy as it may sound. Which converts the connection between On Prem and online environments. Instead of being a direct connection, it converts it into a standalone Entra app. It's then necessary to follow setup instructions that include steps to clean or those older hybrid authentication certificates and upload new ones to the separate Entra hybrid app exclusively. Where an attacker's access is then much more limited. You know, limited the way Microsoft would like it to be. Because this hybrid on Prem to online attack, essentially a bridge is essentially, as I said before, a design flaw. It not only works on Exchange 2016 and Exchange 2019, but also on the latest pay as you go Exchange Server subscription edition. So customers of all three versions will have to follow the steps if they are using any sort of a hybrid configuration. So I just want to make sure that all of our listeners knew that.
- [20:55]
Leo Laporte
To be clear, this is a brand new Exchange vulnerability.
- [21:00]
Steve Gibson
Yes.
- [21:04]
Leo Laporte
Using any Microsoft software and you're not updating assiduously, you're in deep trouble. Even if you are, you might be.
- [21:12]
Steve Gibson
Well and boy, by the time we're done here when we. Roscoe, is this the listener who sent who who does this? And he said, let me give you a like. Let me explain why people are not updating, you know, it basically he was a little defensive. It's like, you know, you say we ought to all update SharePoint. Let me tell you why we're not updating SharePoint. And so it turns out there's a, there's a big story anyway, what this means for any of our listeners who may not be within federal agencies, but may still be responsible for their enterprises hybrid on premises cloud Exchange server setup is that all of this must be done to be secure. Anyway, for anyone needing more information, I have links to CISA's directive and Microsoft's disclosure in the show notes, two links there. It's something that needs to get done. Again, it does require that you basically replace the previous architecture with an entra based architecture which fixes the previous way that that on prem authenticated itself to Exchange server in the cloud. The problem was that exchange server in the cloud would receive the on prem authentication certificates which the bad guys may have gotten a hold of and then they would have free reign throughout your whole cloud environment.
- [22:47]
Leo Laporte
So Microsoft does not want you to run stuff on prem, do they?
- [22:52]
Steve Gibson
Actually, no, they are.
- [22:54]
Leo Laporte
That's really, I think.
- [22:55]
Steve Gibson
Well, and you know, there was something we touched on in passing there. There were. Or maybe it's something that I saw during doing my, my, you know, research for the podcast a couple weeks ago. But their stock price, Microsoft stock price is specifically doing as well as it is because of the clear future revenue they are predicting from moving every. Moving their world to a subscription model.
- [23:24]
Leo Laporte
But we knew this for a decade, that this was the future.
- [23:28]
Steve Gibson
Yes, the plan. And now here is. Welcome to the future. Here we are today, Nvidia firmly said no. Various news outlets have reported that U. S Officials have been exploring the idea of mandated. Well, of course now we know that no, Nvidia decided to buy their access to China for 15 of their proceeds. But that's another matter. They've been exploring the idea of mandating that Nvidia include kill switches, back doors and location tracking tech in its chips to prevent products from reaching adversaries like China.
- [24:13]
Leo Laporte
Okay.
- [24:15]
Steve Gibson
You know, this pushing and the rumors that it inevitably creates, you know, would clearly have a negative impact on Nvidia sales. I mean, already China is concerned about, you know, chips coming from major US Suppliers in the same way that we're concerned about chips coming from China. I mean. Right. I mean, that's reciprocal.
- [24:38]
Leo Laporte
Yeah.
- [24:39]
Steve Gibson
So this led Nvidia to make the following formal statement. For the record, last week they posted under the title no back doors, no kill switches, no spyware. They said Nvidia GPUs are at the heart of modern computing. They're used across industries from healthcare and finance to scientific research, autonomous systems and AI infrastructure. Nvidia GPUs are embedded into CT scanners and MRI machines, DNA sequencers, air traffic, radar tracking systems, city management, just city traffic management systems, self driving cars, supercomputers, TV broadcasting systems, casino machines and game consoles, Everything. That's right. Probably in a. In a machine. Some widget you have near you and Leo, you're probably wearing four.
- [25:32]
Leo Laporte
I'm wearing three of them around my neck right now.
- [25:34]
Steve Gibson
That's right. They said to mitigate the risk of misuse, some pundits and policymakers propose requiring Hardware kill switches or built in controls that can remotely disable GPUs without user knowledge and consent. Some suspect they might already exist. Nvidia GPUs do not and should not have kill switches and backdoors. Hard coded single point controls are always a bad idea. Nvidia has been designing processors for over 30 years. Embedding backdoors and kill switches into chips would be a gift to hackers and hostile actors. It would undermine global digital infrastructure and fracture trust in U.S. technology. Establish law wisely requires companies to fix vulnerabilities, not to create them. Until recently, that policy was universally upheld and beyond question. When security researchers discovered vulnerabilities such as spectre and meltdown for CPUs, governments and industry responded with speed and unity to eliminate the risk. That principle still holds. There is no such thing as a good secret backdoor, only dangerous vulnerabilities that need to be eliminated. Product security must always be done the right way through rigorous internal testing, independent validation and full compliance with global cybersecurity standards. Robust security is built on the principle of defense in depth layering multiple safeguards so that no single point of vulnerability can compromise or shut down a system. For decades, that's how Nvidia and American industry have promoted innovation while protecting users and growing the economy. This is no time to depart from that winning formula. The Clipper chip was a debacle, a policy and technical failure. The cybersecurity community learned these lessons the hard way during the 1990s with the NSA's Clipper Chip Initiative. Introduced in 1993, the Clipper Chip was designed to provide strong encryption while maintaining government backdoor access through a key escrow system. The Clipper chip represented everything that's wrong with built in backdoors. Security researchers discovered fundamental flaws in the system that could allow malicious parties to tamper with the software. It created centralized vulnerabilities that could be exploited by adversaries. The mere existence of government backdoors undermined user confidence in the security of systems. Kill switches and built in backdoors create single points of failure and violate the fundamental principles of of cybersecurity. We must promote smart software tools, not dangerous hardware traps. Some point to smartphone features like Find My Phone or Remote Wipe as models for a GPU kill switch. That comparison doesn't hold water. Optional software features controlled by the user are not hardware backdoors. Nvidia has always supported open, transparent software that helps customers get the most from their GPU powered systems. Diagnostics, performance monitoring, bug reporting and timely patching with the user's knowledge and consent. That's responsible, secure computing. It helps our customers excel and our industry to stay ahead. Hardwiring a kill switch. In case anybody at this point had any doubts, hardwiring a kill switch into a chip is something entirely different. A permanent flaw beyond user control and an open invitation for disaster. It's like buying a car where the dealership keeps a remote control for the parking brake just in case they decide you shouldn't be driving.
- [30:05]
Leo Laporte
Most cars you buy today have that. I hate to say it.
- [30:09]
Steve Gibson
Bad example maybe? Yes, he says that's not sound policy. It's an overreaction that would irreparably harm America's economic and national security interests. Hardware integrity must be nonpartisan and non negotiable. For decades, policymakers have championed industry's efforts to create secure, trustworthy hardware. Governments have many tools to protect nations, consumers and the economy. Deliberately weakening critical infrastructure should never be one of them. There are no back doors in Nvidia chips, no kill switches, no spyware. That's not how trustworthy systems are built and never will be.
- [30:52]
Leo Laporte
So, right on. They're right.
- [30:54]
Steve Gibson
Yeah.
- [30:54]
Leo Laporte
Do you believe them?
- [30:56]
Steve Gibson
Yeah. Oh, I do because. Because we know him and you know. Yes, he's the real deal. And what I like is that this really. I hope the politicians are aware of this and listen to this because of course his bringing up the Clipper chip was brilliant because it was a complete fiasco.
- [31:21]
Leo Laporte
Yeah.
- [31:21]
Steve Gibson
Yes. And this is what the UK and the EU are still trying to do. Like this battle hasn't yet been resolved officially and I'm just glad that Nvidia is, you know, planted a very clear, hopefully stake through the heart of this thing because this whole notion of, you know, the government needs its own special access that just has to be put down.
- [31:50]
Leo Laporte
It's terrible idea.
- [31:51]
Steve Gibson
Yeah.
- [31:53]
Leo Laporte
Agree 100.
- [31:53]
Steve Gibson
Unfortunately, at this point we're still seeing no apparent end in sight.
- [31:57]
Leo Laporte
We are with.
- [31:58]
Steve Gibson
Something's going to happen in October in, in the eu. So everyone's waiting to see whether this, you know, the, the, the pre. Encryption filtering of phone content is what the EU tries to do. I just think everybody, all the players, all the technology players have to as a unit say no, no. And it's like you, if you would like to have no technology in your, you know, in your union, fine, we're not going to play. I was going to mention, as I mentioned at the top of the show to our listeners, that the Dashlane password manager would be ending its free tier service coming up on September 16th. So next month. Middle of next month. And I figured I'd aim anyone who might be using Dashlane, inertia being what it is over at either of this network's two password manager sponsors, one password or bit warden. But then I saw Dashlane boasting that their paid premium plan, which is will be the only thing left would. Well, they have a family plan too, but would allow for. Get this, Leo. It's an amazing feature. Unlimited passwords and pass keys.
- [33:20]
Leo Laporte
How do they do that?
- [33:22]
Steve Gibson
I know it's. It's unlimited. And that of course caused me to wonder if unlimited passwords and pass keys is the big selling point of Dashlane's premium plan, what could possibly be the limit they had imposed for their free plan? Yeah, believe it or not, I'm not kidding you. You get all of 25 passwords for free.
- [33:51]
Leo Laporte
25?
- [33:52]
Steve Gibson
Well, you used to. Up until this coming September 25 in the year of our Lord 2025. It's not possible to meaningfully use any password manager that imposes any limit. Well, okay, maybe unless it's a thousand, but you know, you know, under there, why upgrade to premium? Explanation. Dashlane actually says this. They say unlimited passwords and pass keys. Say Goodbye to the 25Password limit and start saving every password.
- [34:35]
Leo Laporte
Everyone.
- [34:36]
Steve Gibson
Yes, anyone you could want, Leo, you could save. Wow. But only if you upgrade. Not for free. You know. And when you think about it, Leo, how convenient would it then be not to need to decide which of the precious 25 passwords you'll choose to save. There's an easy in your Dashlane vault.
- [35:03]
Leo Laporte
Just use the same password everywhere you don't need.
- [35:07]
Steve Gibson
Well, that's true, you. But you don't need to delete any of those lesser needed passwords to make room for that 25th one that now it's more important.
- [35:19]
Leo Laporte
It's a LIFO Q just to have them pop off the end. No problem.
- [35:23]
Steve Gibson
And the other feature, Leo.
- [35:25]
Leo Laporte
Yes.
- [35:26]
Steve Gibson
Access your logins on any device.
- [35:30]
Leo Laporte
Any device you.
- [35:32]
Steve Gibson
They said. They said move beyond single device access and seamlessly sync and access your vault on any device, browser or operating system. Leo, this is a breakthrough.
- [35:49]
Leo Laporte
Oh, in their defense, it's a trial version, right? I mean, they certainly don't expect anybody to use this all forever.
- [36:01]
Steve Gibson
How could you use it for more than a day? I don't. I don't get must. It must do some fancy stuff that I can't even imagine because I. You know that I've seen some really ugly cars on the road. Leo. Yeah, which says if. If you make it we'll buy. Somebody will buy it. That's.
- [36:24]
Leo Laporte
I know what car you're talking about, by the way.
- [36:27]
Steve Gibson
Really ugly.
- [36:28]
Leo Laporte
Oh boy. And we're not talking the.
- [36:29]
Steve Gibson
Especially when you get. Especially when you go crazy with the paint job. Oh my.
- [36:34]
Leo Laporte
Some of those creative wraps.
- [36:36]
Steve Gibson
Yes, they also this dash lane also if you upgrade, you get real time fishing protection. Real time, yeah. It's not late then, right? Then while you're logging on Leo, it doesn't come back and say, oh, by the way, you got hacked last week. They say set up your security and stay ahead of AI powered. You know, because AI that's, you know, everything's AI powered now. AI powered phishing with real time alerts that warn you before you auto fill your info on a suspicious site and warning. That's warning. Yes, but you know, password managers won't fill in your info because it's a real site because the URL won't match. So anyway, as a consequence of what I learned, I no longer imagine that any, not one of our users could possibly, possibly be using the free dashlane product. So I see no need to warn of the impending end of their free tier. The only other thing I learned is what a great deal 1Password and Bitwarden offer. Because guess what, folks, you get all that for free.
- [37:57]
Leo Laporte
I don't know what the 1Password free tier does, but I do and I do remember this happened with LastPass. Remember they killed their free tier and it upset people quite a bit. And so when bit warden said, you know, we're gonna, we would like to buy ads, one of the first questions I said is, so you have a free tier, unlimited passwords, unlimited pass keys, hardware keys, unlimited devices, all that stuff. But how long are you gonna ever kill that? And they said, no, we will never kill that. We can't. We're open source. Somebody would just fork it and then it would continue on. So even if we wanted to, we can't. And that was actually one of the many. But one of the criteria I used to decide whether we would do their ads.
- [38:43]
Steve Gibson
That is a, that's a. I mean, that's an inarguable point too. I mean, yeah, you know, they can't.
- [38:50]
Leo Laporte
Yeah, they can't take it away.
- [38:52]
Steve Gibson
Yeah. So if anybody out there is paying because you want. I mean, I pay my $10 a.
- [39:01]
Leo Laporte
Year and you don't have to, by the way.
- [39:03]
Steve Gibson
No, but it's free. I want to support them.
- [39:06]
Leo Laporte
Yeah, we want to support them. Yeah.
- [39:07]
Steve Gibson
Yeah. But wow. I just, I. And there's a lot of people apparently using that.
- [39:13]
Leo Laporte
I, I, to be fair, dashlane is a, is a perfectly good password manager.
- [39:17]
Steve Gibson
I don't want it to be free.
- [39:19]
Leo Laporte
Yeah, just don't. There's no free tier now.
- [39:22]
Steve Gibson
Why even.
- [39:23]
Leo Laporte
Yeah, yeah, but it, but I mean, it's not a bad. I've used Dash. It's fine. I mean, I've, I've tried them all. I have to, to kind of keep my eye on what's going on.
- [39:32]
Steve Gibson
So it's not Crash Lane or, or Trash.
- [39:34]
Leo Laporte
Not Crash Lane. Although one of our Discord members says, oh, don't use Dash Lane. Use Dash Highway. It's got many more free passwords. You're on the Lane version. That's the problem. That's right.
- [39:48]
Steve Gibson
Wow.
- [39:48]
Leo Laporte
No, that's one of the things I'm very proud of. We very carefully vet all of our sponsors and we make sure that, for instance, after, after. The problem is you can't guarantee a company won't be acquired. And that's what happened in LastPass. We vetted.
- [40:02]
Steve Gibson
I was gonna say. And you can't guarantee they. Something won't happen to them. You know. Right. We, we, we no longer. We're a little sorry that in the bat. In the past we were all pro LastPass, but in the past they were doing the right thing.
- [40:16]
Leo Laporte
Right. And it's one of the reasons that I, I support open source because as, as you see, even if you decided you were going to withdraw that free product, it's open source. Somebody just forks it and says, well, Leo's version is going to be free forever. That's that much. Right? I like open source. I'm just looking to see. I don't know if there's a free tier on 1Password. I think companies probably shouldn't really offer the free tier. Apparently.
- [40:45]
Steve Gibson
I do understand asking for a reasonable fee in return for all these services. So. Yeah, yeah, I just couldn't, I couldn't believe that anybody. My main point was how can anybody use a password manager with a 25 password limit? I just, I don't get it.
- [41:04]
Leo Laporte
Oh, let me see. Get started. Free. I'm looking at 1Password, but it's basically a free trial that you can have for 14 days and then you either kicks in or it doesn't. That's. Yeah, I understand. Offering a trial version so people could see if they, you know, like the user interface or whatever. Yeah, yeah.
- [41:24]
Steve Gibson
And word of mouth probably is like somebody else is using Dash Line and says, oh, you got to try it. It's the greatest. And so someone says okay, I'll try it. And they, you know, put a few passwords in and see that it works. And it's like, okay, I'm going to figure out.
- [41:37]
Leo Laporte
You put too many in. Just keep using those same 25 over and over.
- [41:41]
Steve Gibson
Can't imagine you, you add up. You add your password and it says, oh, sorry, you've reached your limit. I just. That's un. I can't believe it.
- [41:50]
Leo Laporte
Well, and your point is also a technical point, which is it doesn't cost them anymore if you have 26 passwords than if you have 25. Maybe if you had 25,000.
- [42:01]
Steve Gibson
Yeah. Anyway, break time and then we're going to talk about more cool stuff.
- [42:06]
Leo Laporte
Our sponsor for this segment of Security now is. And again, this is one I vetted. In fact, it's one we use this little thing right here. This is my. Thanks. Canary. You know, you know, we talk about this as a honeypot. It looks like an external USB drive. Just a little black box you could stick anywhere in a closet. All you need is an ethernet connection and power, and then suddenly you've got a device that doesn't look like some vulnerable thing, it looks like some valuable thing. It is a honey pot that impersonates anything you want. In this case, my thinks Canary is impersonating a Windows Server 2019. Although I was thinking of making an Exchange Server or SharePoint Server, because that would be pretty, pretty sweet. You'd pretty much. But the whole point is, even if you had that, it's not visible to the public. This is. You're not putting this out in the public, you're putting this inside your network. Why would you do that? Because if a bad guy gets into your network, you need some way of telling them of saying, oh, oh, I see a bad guy. You need an alert that matters. Here's the ThinksCanary console, Windows Server 2019. But let me show you how easy this is to change it, to configure it. I'm going to go to configure my Canary and then I can look at the so called personality. This is what it's impersonating. IIS 10, IAS 7 a Windows domain control ad, Active Directory, Domain Controller, Windows 7 desktop. Oh, you could turn on a file share. That's a cool thing. I'm not going to read them all because it could be almost anything, including, by the way, a SCADA device. Maybe I'll make it a Hirschman RS20 automation device. Notice the Mac address is changed. Reason being that's a Hirschman Mac address suffix That a prefix? Actually, this is the prefix and that's the suffix. So it, the, the point being, the bad guy's going to look at this and not know it's not the real deal. There's another thing you could do with your things, Canary. Create these little trip wires, Canary tokens, which are simply files you could spread all over. I even put them on our Google Drive or Your, or your OneDrive. Anywhere that you would put your files, you could put these. They could be a spreadsheet, they could be a Slack API key, they could be an Amazon S3 bucket. Ooh, you put that in your AWS account and anytime somebody tries to access it, you know somebody's got your keys, they're in there, and you get an alert. Adjust the alerts that matter in just the way you want them. It could be email, it could be sms, it could be a Slack message. They support web hooks, they have an API. Of course it should show up on your console any way you want them. The point being, you're not going to get an alert unless you have a problem. Thanks to Canaries are honey pots that can be deployed, as you saw, in minutes. Then if somebody's accessing your lore files, those Canary tokens, or brute forcing your fake SSH server, your thinkscanary will immediately tell you you have a problem. No false alerts, just the alerts that matter. So you see how easy it is. Choose a profile for your ThinksCanary device, register it with a hosted console. You get monitoring, you get notifications any way you want them. And you sit back and you wait. They can't help themselves. Once they've breached your network, when they see it, they're gonna attack it. Same thing from malicious insiders. On average, companies don't know they've been breached for 91 days. All right, how much does this cost? Is probably your next question. You can go to Canary tools, slash twit, $7,500 a year. You get five things. Canaries, you get your own hosted console, you get your upgrades, your support, your maintenance, all included. If you use the code twit in the how did you hear about us? Box, you're going to get 10% off. And not just for the first year. For as long as you use your ThinksCanaries, you can always return your ThinksCanary. They have a very generous 2 month, 60 day money back guarantee. Full refund. I should point out though, during all the years that we have partnered with Things Canary, no one's ever claimed the refund. Visit Canary Tool twit Enter the code twit in the how did you hear about us box again? 10% off for the life of your thingst Canary, which is a fantastic deal. Canary Tools slash Twit. We thank him so much for supporting us for so many years. They're big fans of yours, Steve. I don't know. What should I. What should I make my canary now? I mean, it could be. It could be almost anything. I love that. It's so much fun to play with. By the way, I got some alerts, but they were just alerts that you've disconnected your canary and it's been reconnected.
- [47:09]
Steve Gibson
Ah, nice.
- [47:11]
Leo Laporte
You know why? We had a power outage.
- [47:12]
Steve Gibson
Ah, right.
- [47:13]
Leo Laporte
I didn't mean to disconnect it. I should put it on UPS for a while. We were getting. I forgot that Russell put fing on my network and it was internally pinging all the ports and I was getting all these alerts and then Russell said, oh, I'm sorry. Oh, sorry, that was me. So I know it works. All right, back to you, Steve.
- [47:38]
Steve Gibson
Okay, so last Wednesday, Socket Security detailed two particularly nefarious NPM packages they discovered in the repository. Their article was titled Malicious NPM packages target WhatsApp developers with remote kill switch. With the teaser, two npm packages masquerading as WhatsApp developer libraries include a kill switch that deletes all files if the phone number is not whitelisted. Okay, so here's the top of their posting. They said Socket's threat research team discovered two malicious npm packages specifically targeting developers building WhatsApp API integrations with a remote controlled destruction mechanism. Published by NPM user Nay Floor N A Y F L O R e using email idzcchgmail.com both nea n a y a hyphen floor fl o r e and n v lore hyphen hsc. Those are the two package names masquerade as WhatsApp socket libraries while implementing a phone number based kill switch that can remotely wipe developer systems. The packages have accumulated and here's the worrisome thing. Over 1110. 1110 downloads in a month. What remains? Yeah, so there's 1110 unwitting developers who downloaded this thing thinking, hey, great, I need an API library For my enterprises WhatsApp development and run the risk. Or maybe they did get wiped and as of this reporting, it still remained active on the NPM registry. They said, we submitted. Socket said, we have submitted takedown requests to the NPM security team and petitioned for the suspension of the associated account. Good. They wrote WhatsApp Business API Adoption. And that's where this is used. WhatsApp Business API Adoption has surged with over 200 million businesses now using the WhatsApp platform globally. This growth has created a thriving ecosystem of third party libraries and tools for WhatsApp automation. Developers regularly install packages like WhatsApp Web, JS Bailey's and similar libraries to build chatbots, customer service automation and messaging integrations. The package is published by Nayfloor. This bad guy exploit this trust by positioning themselves as alternative WhatsApp socket implementations. The malicious packages first retrieve a remote database of whitelisted, you know, basically good phone numbers from a GitHub repository. Both packages are base64 encoding or use base64 encoding to obfuscate the endpoint URL. And in the, in their documentation and in the show notes, I have the URL for anyone who's who's Interested. It's a JSON file they wrote. The base64 encoding conceals the GitHub endpoint from casual inspection. The database is hosted on GitHub pages, making it appear legitimate while providing the threat actor with remote control over which phone numbers will will trigger destruction. The malicious kill switch logic is embedded within the request pairing code function, which developers would naturally call when setting up WhatsApp bot authentication. This function appears legitimate and necessary for WhatsApp integration. When request pairing code executes, it immediately begins the kill switch process. The logic is simple. If the phone number exists in the remote database, the package continues normal operation. If not found, the function sets sets the GETS number code to 0000 and executes. And you'll get a kick out of this command, Leo, because I have in the show notes and execute RM space hyphen RF oh no space * oh no oh no RM of course is short for remove and they wrote which recursively deletes all files in the current directory. Yeah, you don't want that executed on your machine.
- [52:54]
Leo Laporte
No, the F is for forced. The R is recursive. So basically delete everything Star.
- [53:02]
Steve Gibson
Exactly.
- [53:05]
Leo Laporte
Wow.
- [53:05]
Steve Gibson
They said this approach allows the threat actor to maintain a white list of safe phone numbers. And those may also those are probably those of known security researchers or maybe their own people. Although I would never be comfortable, you know, like using a if this number is in the list, then don't delete everything. That seems crazy, but I, I mean, I get it. Maybe they just would never install this anywhere like on on their own stuff. I mean, the whole thing seems a little screwy to me, but this is what the thing does, they said the pair key parameter is particularly clever. It makes the function signature look more authentic for WhatsApp development, while having no impact on whether your system gets destroyed. It's a clever social engineering touch to make developers think this is a legitimate WhatsApp pairing function. So the point is it goes through the motions that you would expect from a WhatsApp API tool. All the while, if your phone number that you're pairing that you're developing with is not in this white list, that command is going to get executed on your system, they said. Both apps contain identical generate creds functions capable of exfiltrating device information to and then they give the the URL API.varylinh MV ID forward slash running, but the calls to this function are commented out in both packages. This suggests the threat actor initially planned data exfiltration and collection, but simplified the attack to focus purely on destruction. And since the kill switch executes RM space hyphen RF space * immediately when a phone number is not whitelisted, any subsequent exfiltration attempt would fail on the destroyed system. Great, because there's nothing left to exfiltrate, they said for white listed numbers that continue that continue normally there's no valuable data to steal anyway, so they they they finished saying the presence of complete functional exfiltration code indicates the threat actor has the infrastructure ready and could easily reactivate data collection in future versions by simply uncommenting the function calls anyway. But our takeaway here I mean the the thing to to get from this is for all developers to be deadly serious about maintaining some sort whatever sort you want of of incremental versioning backup which will not delete any previously backed up files, even in the event that a file is deleted from the backup source. As our listeners know, for many years I was using and loving the free sync.com encrypted file backup and cross machine synchronization system. But they went through a service outage rough patch a couple of years ago and the inconvenience of that was enough to kick me back over to syncthing and Leo, you and I are both huge syncting advocates. It is truly terrific, but I have not been as big a fan of its versioning, whereas sync.com really has that nailed. So being something of a belt and suspenders guy, I'm now using both. If anyone is interested I wanted to revisit my my endorsement of synth of sync.com if anyone is interested in looking at it, you can use my referral code and get we each get an Extra gigabyte of storage. I've already got plenty, but it's worth getting one. That means you start out with six gig of free and it's free and unlimited to play with rather than their. Their five gig free plan. And the referral code hasn't changed from years ago. It's GRC SC. It's one of our shortcuts. GRC SCync S, Y, N, C. And that'll just bounce you over to the ability to set up a free account and with an extra gig.
- [57:40]
Leo Laporte
What don't you like about sync things? I use the staggered versioning, which keeps. For me you can have more. A year's worth of versions.
- [57:52]
Steve Gibson
Yeah. I don't remember now. Maybe it was just to have wanting a whole secondary.
- [57:57]
Leo Laporte
Yeah, maybe. Yeah.
- [57:58]
Steve Gibson
Independent spenders. Yeah, yeah, yeah. I guess I just, I sort of like browsing through the display. I was doing it for a while. I don't remember what it was that. Anyway, I think it was just.
- [58:16]
Leo Laporte
You know what I do is I do a sync thing to my nas, which runs sync thing locally, but I have it set for copy only. So even if you delete a file, it doesn't sync it. And that's what people get in trouble with.
- [58:32]
Steve Gibson
Right. You, you definitely, definitely don't. For example, if this rm, you know, recursive force, everything instruction ran on your system, you don't want anything that, that looks at your system going, oh, you want to get rid of that? Yeah, yeah.
- [58:48]
Leo Laporte
Because that's exactly what these guys are going to do to you. Incidentally, I, I strikes me that the big threat with these kinds of hacked. Whoops. I keep turning that on. I don't want to turn that on. These hacked libraries is so many vibe coders now will be not really knowing what they're doing. They'll be just, oh, look, the code runs great and they're pulling in these libraries and they don't really know what these libraries are doing. It's. It seems like this is going to be more of a risk.
- [59:18]
Steve Gibson
Essentially, they're taking a whole bunch of building blocks and plugging them together.
- [59:22]
Leo Laporte
Right.
- [59:23]
Steve Gibson
And they don't really code.
- [59:24]
Leo Laporte
In many cases, they don't know what's going on. Yeah. Yeah. Hey, by the way, congratulations to Grayson Petty. He just donated $10 as a YouTube viewer. He says he just passed his CompTIA CSYSA plus exam. A score of 770. Got all four CompTIA certifications, A Plus, Network Plus, Security plus and CISA. And that's because he listens to this show. So good job. He's a. He's one of our super fans in the. In the. Very cool. Yeah, that's very cool. Yeah. Congratulations, Grayson. Thank you for this.
- [59:55]
Steve Gibson
While we're on the subject, socket also found 11 malicious Go libraries that download and run malware on infected systems. And GitLab's own security team found five malicious PI PI packages targeting the dev ecosystem of the Bittensor Crypto wallet. So, you know, as they say, there's no such thing as a free lunch. It is so sad, Leo, that the beautiful concept of a community of well meaning open source developers and contributors who want to help each other, that it's just been infected by miscreants.
- [60:41]
Leo Laporte
Miscreants, yes. Utes. Clearly.
- [60:47]
Steve Gibson
I do have some happy news.
- [60:50]
Leo Laporte
Oh, good.
- [60:51]
Steve Gibson
At last, UBlock Origins stalwart developer Raymond Hill.
- [60:57]
Leo Laporte
Gore Hill.
- [60:59]
Steve Gibson
Well, Gore Hill.
- [61:00]
Leo Laporte
Yeah, no, same guy.
- [61:01]
Steve Gibson
Yeah, yeah, yeah. Gore Hill.
- [61:03]
Leo Laporte
His handle is Gore Hill. Yeah.
- [61:04]
Steve Gibson
Yes. Has just released U Block Origin Lite for Safari. Aha. So for iPad, iPhone and Mac users. And since finding things within the Apple App Store has always been mysteriously difficult. I don't understand. Terrible. Just unbelievably bad, Leo. So bad you put in exactly what you want and it offers you 12 other things until you get to the thing that's named what you searched for.
- [61:34]
Leo Laporte
Right. And often, by the way, shows you bad copies or you know, kind of.
- [61:40]
Steve Gibson
Yes.
- [61:41]
Leo Laporte
Skeezy versions of the same.
- [61:42]
Steve Gibson
Yes.
- [61:43]
Leo Laporte
It's really annoying.
- [61:44]
Steve Gibson
I don't get it. Anyway, I have a link to the exact Ulock Origin Light app on the apple.com you know, App Store in the show notes. So if you don't want to dig around through it, you can find it from me on. On the show notes.
- [62:01]
Leo Laporte
I'm assuming that he did this because he had to write it for Chrome. Right?
- [62:05]
Steve Gibson
Correct.
- [62:06]
Leo Laporte
To get past the version manifest three.
- [62:09]
Steve Gibson
Yeah. And basically he developed all the light technology in order to do as much as he could with the more of the hands off approach which the. The. The manifest v3 requires. So he figured, hey, I could do that on Safari now because Safari also.
- [62:26]
Leo Laporte
Has because severe limitations on what extensions can do.
- [62:29]
Steve Gibson
Right. But ublock Origin is least the. Is the most we can get. And you know, it's still great the app. It just appeared in the store, so it only has 84 ratings when I looked yesterday, but it's holding an 8. I'm sorry, a 4.8 out of 5. All right. It's like almost all fives and there were like a couple ones because somebody said, well, this doesn't wash my car. So why? You know, it's like, no, that's not what it does. Great app. I encountered the following brief news blurb about Sonic Wall. All that this little blurb said was Sonicwall has told owners of Gen 7 firewalls to disable the Devices SSL VPN feature due to a security risk. The company says it received reports of attacks against the devices over the past three days from at least three security firms. I think actually there were four. According to Arctic Wolf, Google Mandiant and Huntress Labs, attackers hacked Sonic Wall systems and then deployed ransomware. And if it's a hacking and SSL vpn, that is not good. Sonicwall says it's investigating to see if the attacks used older bugs or if a new zero day exploit. Okay, so first of all, this would and should be terrifying to anyone whose enterprise is behind any late model. That's gen 7 or later Sonic Wall firewall, which offers remote SSL VPN access. You know, not just one but three major high reputation security firms in independently determined that ransomware was being deployed within enterprise networks via an unknown penetration vulnerability in Sonicwall's firewall. It doesn't get much worse than that. And as we know, the idea of a remotely exploitable zero day vulnerability in an SSL VPN would sadly not itself be very surprising since we've seen exactly that a number of times before. So I went looking for Sonicwall's statement about this to find out what was up. So here's the clarification that they provided. They said following our earlier communication we want to share an important update on our ongoing investigation into the recent cyber activity involving Gen7 and newer firewalls with SSL VPN enabled. We now have high confidence that the recent SSL VPN activity is not connected to a zero day vulnerability. Meaning not something new. They said instead there's a significant correlation with threat activity related to CVE 2024. Okay. Meaning last year sometimes 40766 which was previously disclosed and documented in our public advisory. And then they give a number. It's from 2024 advisory number 15. They said we are currently investigating fewer than 44 zero. So it's not. Not nothing. Fewer than 40 incidents related to this cyber activity. Many of the incidents relate to migrations from Gen 6 to Gen 7. Yep. Firewalls where local user passwords were carried over during the migration and were not reset. Resetting passwords was a critical step outlined in the original advisory. So people didn't follow the instructions carefully. Yeah, they said Sonic OS 7.3 has meaning the new the current has additional protection against brute force, password and MFA attacks. Without these additional protections, password and MFA brute force attacks are more feasible. And you know this is the publisher saying that so we we re we we we would word that to say password and MFA brute force attacks are entirely doable. Yes, yes. More feasible. More feasible. Well yes, and also entirely doable. Many people have succeeded, in other words.
- [67:21]
Leo Laporte
Yes.
- [67:22]
Steve Gibson
So they followed that with their updated guidance and something there also stood out, they said. To ensure full protection, we strongly urge all customers who have imported configurations from Gen 6 to newer firewalls to take the following steps immediately. First, update Firmware to version 7.3.0, the latest current, which includes enhanced protections against brute fire force attacks and additional MFA controls. Reset all local user accounts for any accounts with SSL VPN access, especially if they were carried over during migration from Gen 6 to Gen 7. Continue applying all Continue applying the previously recommended best practices. Enable botnet protection and GeoIP filtering. Remove unused or inactive user accounts. Enforce multi factor authentication and strong password policies. They said if any local administrator accounts have been compromised through the earlier CVE 202440766 attackers may exploit administrative features such as packet capture, debugging, logging, configuration backup or multi factor authentication control to obtain additional credentials, monitor traffic, or weaken the overall security posture. And now we know that includes installing ransomware. They said it's advisable to review any packet captures, logs, MFA settings and recent configuration changes for unusual activity, and rotate any credentials that may have been exposed. We appreciate the continued support from third party researchers that have helped us throughout this process, including Arctic Wolf, Google, Mandian, Huntress. Oh yeah, and the fourth one is Field effect. Okay, so those of our listeners who have been following along at home may have noticed something in their list of their remediation and preventive measures that I don't think I've seen before. Their fourth bullet point was enable botnet protection and GeoIP filtering and the GOIP filtering phrase is key it it it is in their notes. It's a link I clicked on the link. It links to a page describing what they mean by the term where they wrote GeoIP filter allows administrators to block connections coming to or from a geographic location by resolving the public IP address to a particular country. This feature is usable in two modes, blanket blocking or blocking through firewall access rules. Blocking through firewall access rules gives a network administrator greater control over over what traffic is and is not scanned by the GeoIP filter. This is useful for full deployments in which outbound traffic may want to be uninhibited, but inbound traffic should be subject to scanning. Typical deployments of GeoIP filter with firewall access rules includes DDoS and other network attack mitigation as well as anti spoofing. So this is great to see. Naturally, everything we've seen and learned informs us that any and all such SSL VPNs, you know, other things like public facing web management portals and anything similar should be locked down out of the box with the engineer who is configuring it forced to selectively enable only the country or countries from which valid remote access is expected to originate. Alas, the industry is not there yet, but at least we're seeing progress. Having Sonicwall offering such a feature right there in its user interface at least means there's a chance that a security oriented engineer who is offered the option may take the hint. And note that the beauty of an IP IP based filter is that no one scanning the Internet from Russia or from China or anywhere else outside the allowed jurisdiction will detect that anything at all is there. They're not frustrated, they're not having their credentials denied, they don't have a page prompting them to log in and saying sorry, that's not the right password, try again, their scanning packets are simply dropped. They will never know anything is there for them to struggle to get. So, I mean, it is, it is the way to do this, but no one's doing it yet. At least this is some forward motion and it's, you know, it's good to see. Cisco's Talos Security group headlined last week's disclosure revolt when your SOC turns against you. And this is what I was talking about when I talked about all the effort that security researchers need to go through, unfortunately, in order to help the companies who have security problems. Leo, let's take another break since we're an hour in. Yes, and we're going to talk about what Cisco and Talos found in Dell's laptops and why anybody with a latitude needs to make sure they get this update. It's a complete security bypass that can be done from any app running on their laptop with no permissions.
- [73:35]
Leo Laporte
Unbelievable. All right, we'll get to that in a moment. That's a good reason to stay tuned, right? Our show today, brought to you by actually somebody who might be able to help you. US Cloud, the number one Microsoft Unified Support replacement. Oh yeah, maybe you do want this, huh? We've been talking for a few months now about US Cloud. They are the global leader in third party Microsoft support for enterprises they now support 55.0of the Fortune 500. Switching to US Cloud could save your business and this is probably why there are so many customers 30 to 50%. 30 to 50% over Microsoft Unified and Premier support. But it wouldn't be any good if it were just less expensive. It's also better. Faster, twice as fast on average. Time to resolution versus Microsoft twice as fast. But now US Cloud is excited to tell you about a new offering. This is their Azure cost optimization services. This might be something Microsoft is reluctant to tell you about, to be honest. When was the last time you evaluated your Azure usage? Microsoft is counting on the fact that if you don't pay attention, you're going to have some Azure sprawl. A little spend creep going on. That's good news for them, bad news for you. I've got some good news for you. Saving on Azure is easier than you think with US Cloud. US Cloud offers an eight week Azure engagement powered by VBox that identifies key opportunities to reduce costs across your entire Azure environment. Not less capability, just less money. With expert guidance, you'll get access to US Cloud senior engineers. It's another reason US Cloud is so good. An average of 16 years with Microsoft products now, at the end of the eight week engagement, your interactive dashboard will identify, rebuild and downscale opportunities. Unused resources, maybe a VM or two that just, you know, skipped under the radar, allowing you to reallocate your precious IT dollars towards, you know, needed resources. And who doesn't need more money, right? One way you can keep the savings going though, would be to invest your Azure savings in US Cloud's Microsoft support. Like a few of US Cloud's other customers, completely eliminate your unified spend. Save big. Now you've got even more money to add to your budget. Ask Sam. He's the Technical operations manager at Bed Gaming B E D E. He gave us Cloud 5 stars saying this. We found some things that have been running for three years which no one was checking. Those VMs were, I don't know, 10 grand a month. Not a massive chunk in the grand scheme of how much we spend on Azure. But once you get to 40 or $50,000 a month, it really started to add up. It does, doesn't it? It's simple. Stop overpaying for Azure, identify and eliminate Azure creep and boost your performance all in eight weeks with USCloud. Visit uscloud.com, book a call today to find out how much your team can save and uscloud.com book a call today and get faster Microsoft support for less. These are great guys. I've known them for some time now. I'm really impressed with what they do. USCloud.com all right, so back to Steve.
- [76:53]
Steve Gibson
Thank you, Leo. So Cisco's Talos Security group headlined their disclosure revolt. When your society turns against you, it's a revolt.
- [77:05]
Leo Laporte
I get it. It's revolting.
- [77:07]
Steve Gibson
That's right. It's revolting. SOC stands for system on a chip. And the vault in the name stems from a subsystem on a huge number of Dell laptop PCs, more than a hundred different models representing tens of millions of Dell laptops. Because it's the latitude, which is, you know, their. Their headline laptop that the subsystem is called the Control Vault 3. So again, the short news blurb that caused me to look deeper just said a set of vulnerabilities can allow threat actors to take control of tens of millions of Dell laptops. The bugs impact the Control Vault 3 firmware that's used to safely store passwords and biometric data inside a secure chip on Dell Windows laptops. The five bugs, codenamed Revolt, impact more than 100 Dell laptop models. The bugs can be exploited. And this is where this guy is like, whoa. Via a Windows API and don't require or doesn't require elevated privileges, Dell has released firmware updates. Okay, so by far the most worrisome part of the entire statement is the bugs can be exploited via a Windows API and don't require elevated privileges. Most flaws that we encounter in security device firmware are actually kind of obscure. They, you know, they require things like boot time access, or access to the system, motherboards, management interface or something. But here we have a set of flaws that literally any Windows app running on anyone's Dell laptop under their non UAC minimal user privilege account could exploit. So here come the miscreants. As I mentioned, Cisco's Talos Security Group discovered and publicly disclosed this last week. I'm sure their discovery was much earlier, since they waited until Dell had created and tested and published the required firmware updates. The good news is those updates exist. The bad news is that they need to be installed before any of Those more than 100 Dell laptop models, representing tens of millions of physical laptops, will be made safe. So let's see what Cisco's Talos Group disclosed last week. Their report leads with four bullet points. First, Talos reported five vulnerabilities to Broadcom. It's actually a Broadcom chip in the Dell laptop. To Broadcom And Dell affecting both the Control Vault 3 firmware and its associated Windows APIs that we're calling Revault Second Bullet Point 100 plus, meaning more than 100 models of Dell laptops are affected by this vulnerability if left unpatched or you know, until patched. Second or third, the revolt attack can be used as a post compromise persistence technique that can remain even across Windows reinstalls. So it's like a rootkit once it gets in there. I mean worse than a rootkit, it's not even going away after a reinstall. And finally, the Revault attack can also be used as a physical compromise to bypass Windows login and or any local user to gain admin and system privileges. Yikes. They can they continued Dell Control Vault is a hardware based security solution that provides a secure bank that stores as in storage bank that stores your passwords, biometric templates and security codes within the firmware. A daughter board provides this functionality and provides these security features through firmware. Dell refers to the daughter board as a ush, a unified security hub as it's used as a hub to run Control Vault connecting various security peripherals such as the fingerprint reader, smart card reader and NFC reader. So you know that's an elegant design to like have all of those physical devices run through a physically separate standalone board before they get to have any access to the motherboard. Good design, they wrote. The current iterations of the product are called Control Vault 3 and Control Vault 3 Plus and can be found in more than 100 different models of actively supported Dell laptops. And I've got links for all this by the way. At the end of this they said mostly from the business centric Latitude and Precision series, these laptop models are widely used in the cybersecurity industry, in government settings and in challenging environments in their rugged version. Sensitive industries that require heightened security when logging in via for example smart card or NFC are more likely to to find Control Vault devices within their environment as they are necessary to enable that is Control Vault is necessary to enable these enhanced security features. So that's just great, right? It's the machines that are most in need of additional security and would therefore likely most would be more likely to be targets that have had their security dramatically impacted by the discovery of these bugs. That's a big whoops. They said. Today Talos is publishing five CVEs and their associated reports. The vulnerabilities include multiple out of bounds vulnerabilities. In other words, good old buffer flow overflows, an arbitrary free and a Stack overflow, all affecting the CV firmware, you know, the Control Vault firmware. We also reported an unsafe deserialization. You know, that'll be an inter, some, some interpretation of something that affects Control Vaults, Windows API. So there was a bug in the Windows code and four bugs in the control, in the, in the Control Vault firmware. So think about that. To accomplish this, Talos would have had to extract and reverse engineer the proprietary firmware from the Broadcom chip. Dell certainly didn't say, hey, please check the firmware we wrote for our core security chip, which provides all of the most critical physical and biometric security for our most secure laptops. My point is here, it's really a shame that this sort of symbiotic relationship doesn't, that sort of symbiotic relationship doesn't exist between manufacturers and security researchers where manufacturers could be of more help to researchers. How many times have we looked at all the extra and unnecessary effort security researchers have had to go through just to reverse engineer and obtain the same information that the manufacturer already has sitting in a file somewhere. And after all that work, which might, might well come to nothing, right? They might have done, you know, extracted the firmware, reverse engineered it, taken a good hard, long look at it and found no problems. But even after they did, the security researchers say to the manufacturer, hey, we just worked our butts off thanklessly for several months to discover a set of five really horrendous security vulnerabilities that affect tens of millions of your most security essential laptops. You know, it's not good news that they're providing, but it is potentially, you know, heading off a, a, a horrific exploit against all of those laptops. So there's something still very wrong with the way we're doing all of this today. The economics in our system are, are not producing, you know, the right incentives. Cisco's Talos group concluded, writing with a lack of common security mitigations and the combination of some of the vulnerabilities mentioned above. The impact of these findings, that is what they discovered they're trying to create, you know, give us some context here. What this means is significant, they said. Let's highlight two of the most critical attack scenarios we've uncovered. First post, compromise pivot, they said on the Windows side, a non administrative user can interact with the Control Vault firmware using its associated APIs and trigger an arbitrary code execution on the CV firmware. Okay. Now given what we know, it's likely possible for the user, meaning an app, some unwitting user, you runs to load an extra large buffer of executable code into control vaults RAM and then cause that buffer to be executed, thus running their own their own CV firmware code on the control vault in order to get up to some mischief, Talos said. From this vantage point, it becomes possible to leak key material essential to the security of the device, thus gaining the ability to permanently modify its firmware. This creates the risk of a so called implant that could stay unnoticed in the laptop's CV firmware and eventually be used as a pivot back onto the system in the case of a threat actor's post compromise strategy. We show how a tampered CV firmware can be used to hack Windows by leveraging the unsafe deserialization bug mentioned previously and then that that was just one. The second is the physical attack. They said a local attacker with physical access to a user's laptop can pry it open and directly access the USH board over USB with a custom connector so there's a USB access to the chip. From there, all the vulnerabilities described previously become in scope for the attacker without requiring the ability to log into the system or knowing a full disk encryption password. While chassis intrusion can be detected, this is a feature that needs to be enabled beforehand to be effective at warning of a potential tampering and is typically not enabled by default in the bios. Another interesting consequence of this scenario is that if a system is configured to be unlocked with a user's fingerprint, it is get this also possible to tamper with the CV firmware to accept any fingerprint rather than only a legitimate users. So when you think about that, the any fingerprint attack is sort of diabolical. How often does anyone go around asking random people to verify that their fingerprint does not unlock their laptop? Probably not often, perhaps never. The affected user would simply notice that their fingerprint reader had apparently suddenly become much better at accepting their fingerprint than it previously had been. And whereas Cisco says to mitigate these attacks, Talos recommends the following Keep your system up to date to ensure the latest firmware is installed. CV firmware can be automatically deployed via Windows Update, but new firmware usually gets released on the Dell website a few weeks prior, so that's good to know. That suggests that that Windows through Microsoft and through Dell through Microsoft will be pushing this out through Windows Update, so it would be nice to have some way to verify that. I didn't dig into this to see whether that is available, but that's great. If not using any of the security peripherals, the fingerprint reader, the smart card reader and the NFC reader. It is possible to disable the CV services using the service manager and or the CV device using device manager. And that's of course that's standard best security practice, right? If you don't need any of these devices, turn them off, then you don't have to worry about them getting used and hacked behind your back. And finally they said it's it's also worth disabling fingerprint login when risks are heightened, for example leaving one's laptop unattended in a hotel room. Windows also provides enhanced sign in security ess which may help mitigate some of the physical attacks and detect inappropriate CV firmware. Then they said to detect an attack consider the following. Depending upon your laptop model, chassis intrusion detection can be enabled in the computer's bios. This would flag physical tampering and may require enabling a password to clear the alert and restart the computer in the Windows logs. Unexpected crashes of the Windows biometric service or the various credential vault services could be a sign of compromise. And Cisco customers using Cisco Secure Endpoint can be made aware of potential risk with the signature definition loaded by abnormal process. Anyway so Dell's own pages label this critical in all caps and they provide a 36 megabyte not very big download to patch this. Excuse me. It's a Windows executable for any Dell Latitude or Precision laptop owners who would like to be proactive and get this patched. I've got the links in the show notes. Hopefully given that it it was it's previously known Dell has published it. Where are we? Today is the second Tuesday of this month. I don't know which month, which patch Tuesday this may have been pushed out but maybe people are getting it today, maybe they got it last month. I don't know where Cisco timed their their release. So it might be that if you try to install the firmware you'll be told it's already been updated and you don't need to install. But anyway, anybody with a Dell laptop, a Dell Latitude probably would be well served to take a look at this and see about getting this resolved. Make sure that they do have the this latest firmware. Okay so the cus, the the listener of ours, Roscoe who I mentioned briefly last week, who is in the field is responsible for managing and maintaining Microsoft systems wrote he said hi Steve, with respect to the SharePoint on prem patching issue, it's important to understand that the ecosystem can be highly complex and patching can be more difficult than it seems. Office 365 might seem to be an obvious way to resolve all these issues, but it can be problematic too. The Enterprise Office Suite has many components which form an extensive requirements matrix and consists of Windows Server version, Active Directory version, Exchange Server version, Dynamics CRM server version, SharePoint server version Mississippi Project server version, Dynamics Great Plains Accounting and Dynamics Human Resources. He said to name some of the commonly deployed solutions, although some have been withdrawn as on PREM installable components. Again, Leo as you noted, because Microsoft is trying to move everybody up to the cloud, he said the versions of all of these components need to be harmonized in order to have a viable working installation. As a result, in order to update or patch to the latest SharePoint on prem version, the trickle down requirements might extend to updating and patching any or all of the other components in the service stack. In extreme situations, this can result in days or even weeks of applying patches, backing out, applying patches in version order, or do different services first, for example applying a patch to Active Directory first, then to CRM, then finally to SharePoint rather than to SharePoint first. The result can be almost unmaintainable, especially for a small to medium enterprise with limited IT resources. Here's an entirely plausible cascade that demonstrates the deep interconnectedness so the sun is shining, the birds are singing, the grass is green, systems are stable, and everything is beautiful in the world, he writes. Yes, a critical vulnerability is discovered in SharePoint with CVS 9.8 and a patch is available. Well, we know that's exactly what happened, he says. The installed SharePoint version is two patch roll ups behind, so SharePoint has to be brought up to date. The second SharePoint roll up will not run on the currently installed Active Directory, so an Active Directory upgrade is required. The Active Directory upgrade implies a Windows Server upgrade. The new Active Directory version no longer supports the installed Exchange version, which also must be upgraded. The new Active Directory version also deprecates NT Landman authentication, which Microsoft SQL was still using. So Microsoft SQL is also in scope the Exchange and the Exchange end of the Dynamic CRM Exchange API deprecates two methods used for email integration from for mail outs to customers and reception of replies in order for replies to be tagged to the original outgoing message inside CRM. Thus, CRM is now in scope for two roll up installations. The second of these CRM roll ups deprecates an API method being used for integration with a parent company's reporting tools, which are required to report the subsidiary sales pipeline prospects to the relevant stock exchange, which is a legislated requirement the parent company must upgrade their data interchange tooling. Alarm bells. The parent company runs Oracle ebs. Seasoned operators might guess which freight train is heading down the tracks. Installing the roll ups in CRM also breaks three in house customizations which must be redesigned and re implemented. At long last the full cascading set of upgrades has been deployed and the SP roll ups and patch can be installed. He says this is the sort of thing that actually happens which can result in weeks no kidding of disruption to business activities and manual workarounds. Is it any surprise Leo, that everyone just wants to leave everything the way it is?
- [98:55]
Leo Laporte
Yeah, if it's holy crap it works. Don't fix, don't yeah, don't fix it if it don't break or something like that.
- [99:02]
Steve Gibson
And you and and unfortunately you can't just patch the one problem. You know, you get a roll up of all these things which have a network of interdependencies with other versions of things because Microsoft is always keeping everything up to date because they don't have all of the connections to external third party tools or to internal things that have, you know, in house customizations which all would have to be moving forward. And Microsoft is adding and removing APIs that break things as we move forward. It is just a mess. As Roscoe wrote, the end effect can be an erosion of trust in the technical solutions provided by Office365 and these bolt on components. Hence Microsoft has pushed clients towards a cloud based subscription model which provides overall greater stability. In other words, because Microsoft, because of like the way this ecosystem developed, it just became untenable. Yes. From a maintenance standpoint, this is why.
- [100:18]
Leo Laporte
I have so much such respect for IT professionals. This is yes, a miserable job. Yeah.
- [100:24]
Steve Gibson
Yes. He said organizations may choose to wait for patch rollups in order to reduce the inevitable indepth troubleshooting that can occur if the application of patches results in unexpected behaviors of seemingly unrelated software components. For example, a patch applied to SharePoint causing unexpected behaviors in CRM. He said on premises SharePoint offers a broader feature set. However, and this is the problem on premises SharePoint offers a broader feature set such as the ability to design and deploy business processes directly into SharePoint using various third party business process management, add on tools and database connectivity and functionality required to support business processes. Meaning you can't do that once you move to the cloud, so you lose functionality. When Microsoft says oh we want you to go to the cloud.
- [101:24]
Leo Laporte
Right?
- [101:24]
Steve Gibson
He said online. SharePoint however, reduces support for business processes to Microsoft's own development tools, logic, apps, flows, web jobs and functions, implying that an organization's significant investment in third party tools and business process deployment and testing becomes redundant and the organization is forced to either adopt a completely new solution outside of SharePoint or re engineer all their existing business processes to conform to Microsoft's provided frameworks at possible significant cost and the possibility of losing significant features and functionality, he said. In corporate environments, such a significant change can mean considerable embarrassment to decision makers who advocated for the third party development approach in the first place, which can add to inertia in moving to a cloud based solution.
- [102:28]
Leo Laporte
Yeah, but you have to understand that that's why it's so complex to update it, because you have this complex ecosystem. So you can't complain about how hard it is to update it if you've opted for this crazy quilt of capabilities.
- [102:43]
Steve Gibson
Either and you've taken advantage of them. All right. Anyway, his perspective leaves me with a much deeper appreciation for the fact that in my own little tiny world, I have never needed to become embroiled in any of that. What a monumental mess.
- [103:03]
Leo Laporte
That's When Richard Campbell talks about running his own Exchange and SharePoint server out of the house, I just tip my hat to him. That's all I can say is you're.
- [103:14]
Steve Gibson
You know, it feels as though the utter lock in which has resulted, it was incremental and it was more or less inadvertent. I mean, I. But you know, today's Microsoft is also well aware of the fact that businesses have gone all in, you know, to their solutions and that those that have no longer have any meaningful way out, they have no freedom. They are, you know, they're being pushed to migrate to the cloud. It's the only way to stay secure. Basically transfer responsibility to Microsoft. Hope that Microsoft doesn't break their stuff because now it's no longer under their control. And pay a subscription on all of this stuff, which they also have no control over. Microsoft can charge anything they want because it is a captive audience now. Wow. Okay.
- [104:18]
Leo Laporte
And you know, if Microsoft's going to take this on, let them. Good for them. Better than us. Yeah. Unless you want all those other features. Yeah.
- [104:28]
Steve Gibson
Let's take a break and then do some more listener feedback.
- [104:32]
Leo Laporte
Indeed. Absolutely. This portion of Security now is brought to you by our good friends at Acronis and the Acronis Threat Research Unit. You deserve fewer headaches in your life. We just heard, I think some people are getting a headache by association. Even something as simple as listening to this show or watching TV can become a headache. When Your favorite shows are scattered across different streaming services. It's nearly impossible to find one place that has everything you need. Acronis takes the headache out of cybersecurity with a natively integrated platform that offers comprehensive cyber protection in a single console. You see, you don't have all these different pieces warring against one another. And if you want to know what's happening in cybersecurity, oh, you'll be glad to know that the Acronis Threat research unit, or TRU, is there for you. It's your one stop source for security research. TRU also helps MSPs stop threats before they can damage you or your client's organization. Right. They're counting on you. Acronis Threat Research Unit is a dedicated unit compromised of experienced cybersecurity experts. Think about, you know, 100 little Steve Gibsons all at work. Their team includes cross functional experts in cybersecurity in AI. Yeah, they're going to cover that now. And Threat Intelligence. TRU conducts deep intelligence driven research into emerging cyber threats, proactively manages cyber risks and responds to incidents, and provides security best practices to assist IT teams in building robust security frameworks. They also offer threat intelligence reports, custom security recommendations and educational workshops. Whether you're an MSP looking to protect your clients or you need to safeguard data in your own organization, Acronis has what you need. It's all there in Acronis Cyber Protect Cloud, edr, xdr, Remote monitoring and Management, Manage detection and Response, email security, Microsoft 365 security, even security awareness training. And it's all available in a single platform with a single point of control for everything. So it's easy to deploy and manage. We know you've got enough headaches in your life, you don't need another one with your cybersecurity tools. If managing cybersecurity gives you a headache, it's time to check out Acronis. Know what's going on in the cybersecurity world by visiting go acronis.com acronym twit and take the headache out of cybersecurity. That's go.acronis.com twit. Thank him so much for supporting Steve and the work he does here at Security Now.
- [107:18]
Steve Gibson
Steve so a listener of ours, Brian Savicool, said, steve, thanks for all you do. You had recommended a picture tool for Windows that could correct the keystone or perspective of a picture or a picture of the day image which was severely skewed. I can't find it in any of the emails or show notes from the past year. Could you please bring it up in the next feedback section? I'm writing some user documentation and the sample image needs similar correction. Thanks for your weekly breakdowns. It really helps me at the help desk where I work, Brian. So I received a number of inquiries about that and I have been remiss in not replying to them all. So I wanted to use Brian's question from last week to get caught up. The tool is free, as I think I mentioned before, it's funky and somewhat finicky. It's by a German guy and he just sort of has his way of doing things. So it's not perfect, polished and proper, but it's the tool I use because the German guy who, who created it got the basic mechanics exactly right. When I first mentioned this on the podcast, I received a ton of feedback from our listeners about alternative solutions. The one that sticks in my mind was someone commenting that he recalled that my own go to graphic editing tool, which is Paint Shop Pro and he's right, has built in perspective Correction and. And again, he's right, it does. But it's the sort of perspective correction that iOS has where you have dials for horizontal or vertical distortion. The thing that the. And this is the name of it, it's just called Perspective Image Correction. The thing that this, the Perspective Image Correction app got exactly right is that its operator rubber bands the vertices of a four sided box whose opposing sides should be parallel and you found it in the final image and then it does that. You know, it. It's. To my way of thinking, it's really the correct way to solve the problem. The app lives in over on sourceforge. I have a link to it in the show notes and I also created a GRC shortcut for anybody who wants to find it. Not surprisingly, it's GRC SC Perspective and that will bounce you over to the download page on sourceforge. And it's just a Windows app, you know, it's not. It may not be the perfect solution for everyone, but it's the best one I have found and the price is right, it's free, and it stopped me looking for anything better. So there you go, Brian. That is the solution. Oh, and he also asked. Actually it was in another email he said, hi Steve, you had casually mentioned on episode 1035 about running Spinrite on a Kindle device. Can you explain in a future episode how that's accomplished? Is it done in the native boot environment or does it require VirtualBox and a special device driver? He said, I have a Black Friday Special Android tablet that's been getting very slow and sludgy even after multiple factory resets. I would like to run Spin right on it before I give up and toss the thing. Thanks for any tips you may have, he said. I can't wait to try out the DNS Benchmark Pro once it gets released. All the very best, Brian in Schneenectady okay, so first of all, Schneenectady, that is Schenectady.
- [111:14]
Leo Laporte
I'm not laughing.
- [111:15]
Steve Gibson
I'm not Schenectady, New York.
- [111:17]
Leo Laporte
Yes, there's no Schnuck.
- [111:21]
Steve Gibson
Silent Schenectady. Anyway, so regarding the benchmark, I wanted to mention that I'm very nearly finished with all of the new features for the base Model DNS Benchmark 2.0. It's finally working very nicely, and through this work I've obtained some clarification about the base model versus the pro edition. The new version 2 non pro edition will be full featured and will run on basically run on demand as a standalone app for Windows and Wine, so it does also run under Linux and Mac. Running on demand makes it useful for obtaining an immediate snapshot of any collection of up to 500 way more than you'll need. Remote DNS resolvers over IPv4, IPv6, DoH or DOT, and all at the same time or individually, whatever you want from the user's location. What we've seen is just like the old saying about retail, it's location, location, location. Our testers are spread around the globe and it is surprising to see how much people's location changes their results. You know, not surprisingly, the DNS for EU resolvers, as I've mentioned, are incredibly slow for me over here in the States. But testers over in the U in the EU have said they're very quick, among their fastest. One of the things we've also seen is that the time of day and the day of week also affects the benchmarks. You know, immediate short term outcome. If I run the benchmark in the middle of a weekday, I consistently see a different result from running it on a weekend morning, for example. The difference may not be significant, but you won't know. You won't know until you try it. So if all you had was the Interactive Edition, you might want to run it at the same, you know, at the same time as you're using your machine at that location. And running it at different times can be useful. One very cool new feature is that the benchmark is now aware of whether differences in performance are statistically significant. For example, two different resolvers might have slightly different average performance, but each resolver's individual spread of performance might be wide enough that it's not possible to say, well, with 95% certainty that the differences seen were not just the result of random variations in packet transit times, because those are varying with the Internet's conditions. So the benchmark is now aware of the of the nature of this, and it incorporates this awareness into every conclusion that it reaches. The base model of the benchmark tests each resolver against the Internet's top 50 domains three different ways, so it issues 150 DNS queries to each of the DNS resolvers being benchmarked. This requires about four minutes for 120 DNS resolvers, which is about all the time that an interactive benchmark should consume without making its user impatient to get some results. During this time, it's measuring the precise time taken for 150 different DNS queries to each of the resolvers that it's benchmarking. Now, it turns out that statistics can be annoying, because even with 150 individual timing samples per resolver, the individual variation among samples means that our ability to draw firm, statistically significant conclusions remains somewhat limited. And that's where the Pro Edition comes into its own. Because Pro will operate as a Windows service entirely in the background, its user won't be sitting around impatiently waiting for results. Pro builds and maintains a database which will allow it to measure resolver performance across a continually broadening time horizon. If the user turns their machine on and off, it will automatically be measuring the times when they are using their machine, and if their habit is to leave the machine on, it will be aware of when their machine is unattended and note whether they're actually using it or not, so that it's able to bias its statistics for when they're actually using the machine. Because of course, that's what matters for the most for DNS performance. DNS queries are very small and very lightweight, so they will never interfere with the normal foreground operation of the machine. And anytime a Pro owner wishes to see what's up, they simply launch the same benchmark utility. Then they're able to choose whether they want to run an interactive benchmark on the fly right then, or if they're interested in browsing the aggregated data that the Pro version has been collecting in the background since they installed it. So of course, as usual, I have no idea when any of this will be ready. I actually think Leo, I might have it ready before Andy has his website online. So I am getting close. But anyway, I'm getting. I'm becoming excited. The. The non pro features, basically all the main features of the benchmark are. Are fleshed out and finished and working and testing and very soon I'll switch over to adding the. The background database aggregation and and display which, you know, I get to reuse the same ui so that won't be a big deal. As for Brian's question about using Spin right to revive an old Android tablet, until we get to Spinrite 7, which will be a pure Windows app, it is necessary to boot any system into DOS where spinrite is able to run. For people who've never done this, I created that bootable freeware which uses all the same processes as spinrite to create and prepare a bootable USB thumb drive and you can just download that for free to play with it. If you're able to boot a PC with bootable, then spinrite will also work in the same way. So the only requirement for restoring the performance is of any device's internal flash storage, whether it's a Kindle or an Android tablet is being able to expose that internal storage as a drive. That might mean switching its storage mode. Android devices usually have. It's sometimes called target drive mode or USB target mode, something like that. The idea being that if you can attach it to a PC and have it in a mode where you see the Android's drive as a disk, then you can attach it to a PC and run spinrite on it as a USB drive.
- [119:22]
Leo Laporte
Basically.
- [119:23]
Steve Gibson
Yes, exactly. And you want to run a level three which rewrites the drive's entire surface to restore its original factory performance. And of course, all of this will be much easier once I get Spin right moved over into Windows. But I have a few other things I want to get finished first. So at that point, once that's done, I can start that joyous project. I'll get there. I'll get there.
- [119:50]
Leo Laporte
There's always something, isn't there?
- [119:51]
Steve Gibson
Yeah, I love it.
- [119:53]
Leo Laporte
Could be worse. You could be running Exchange Server. So just be glad.
- [119:56]
Steve Gibson
Yeah, I'm. I'm running Hmail Server and it just.
- [120:00]
Leo Laporte
Sits there and much, much easier.
- [120:02]
Steve Gibson
Problem.
- [120:02]
Leo Laporte
Yeah.
- [120:03]
Steve Gibson
Listener Michael Swanson said. Hi Steve, I have had In Control running since, you know, GRC's freeware in control running since shortly after you released it to ensure my laptop is not accidentally updated to Windows 11. However, KB517 16 did not install on my laptop until I released control. I believe KB517 16 is the update that provides the free Windows 10 security patch extension, though I still have not seen that offer pop up in the Windows Update dialog. Best regards, Mike. Okay, so first of all, Michael, thank you. It's interesting that Incontrol appeared to block the installation or perhaps the reinstallation of KB517 16, since we know that Incontrol is designed to only block major version changes. So here's what Microsoft has to say about this update, this mysterious update. They said after this update is installed, Windows may periodically display a notification informing you of problems that may prevent Windows Update from keeping your device up to date and protect it against current threats. For example, you may see a notification informing you that your device is currently running a version of Windows that has reached the end of its support life cycle or that your device does not meet the minimum hardware requirements for the currently installed version of Windows. That's interesting. Does not meet the minimum hardware requirements. So it sounds like they're saying those people that have put Windows 11 on a machine that doesn't supposed to have Windows 11 doesn't have TPS 2 or it's going to start complaining about generation intel chip. Yeah, so of course we saw this sort of thing, right, a lot during the forced migration to Windows 10, which is where I first created the app. The, the, the. The. The. Yes. No, it was called Never 10.
- [122:19]
Leo Laporte
Never 10.
- [122:20]
Steve Gibson
I mean, yes, Never 10, where Microsoft would be updating their Windows Update system to introduce constantly evolving new messages about the coming end of the world. You know, it was, it was almost comical. Remember that?
- [122:36]
Leo Laporte
Now, by the way, with Windows 10.
- [122:38]
Steve Gibson
Yeah. The dialogues for the. Back then from, like from, from people who had Windows 7 or 8, they gradually changed from, you know, you know, would you like to update Windows 10? And it, you had, you had a choice of no thanks or yes, please. And then after a while it changed to now or tonight. So it's like, wow, wait a minute, what happened to never?
- [123:05]
Leo Laporte
Thank you.
- [123:06]
Steve Gibson
Anyway, I, I just, after receiving Michael's note, I just checked and my Windows 10 21H1 was locked within control. When I go to Windows Update, I see the expected red notification. It says some settings are managed by your organization. And then if I click on view configured update policies, I see that the policies set on this machine are target release version for feature updates and target product version for feature updates. I know, and those are the things that Incontrol sets. So it looks like it's putting an end user's machine under organizational management so that, you know, it won't do something that the IT department doesn't want to have it do. However, I just tried what Michael talked about and I can confirm that whatever KB517 16 is briefly releasing in Control and performing a manual Windows Update did install KB517.16 into my normally in control locked Windows 10 machine. So I confirm what Michael reported. I don't know that that that I want 517. 16. I don't know if I'm going to start getting bugged by Microsoft now. But what's interesting is this is not the first time that KB517.16 has been offered more than a year ago. Back on March 7, so almost a year and a half ago of 2024, Ghack.net's Martin Brinkman wrote about this under the headline Microsoft's sneaky KB517.16 Windows 10 update pushes Windows 11. He wrote, if you run Microsoft Windows 10 operating system on your devices and want to keep it that way, you may want to check whether the Windows 10 update KB517.16 is installed on the device. The reason for this is that it is designed to push newer versions of windows, including Windows 11 to the device. Microsoft installs the update automatically on Non managed Windows 10 devices that have automatic updates configured. So of course in Control makes it look like a managed device. Thus this isn't installed. So enterprise systems won't get this because they're managed and you know, under management is what InControl creates. So anyway, I've got some more about this in the show notes but you know, that's what I know at this point is that there, there is there basically this KB517 16 is a rolling update which is generically about Microsoft and notices and pushing you to newer versions and complaining when you haven't gone and apparently now complaining when you have gone and you shouldn't have gone because you've got a chip that it does that you know you're not supposed to actually be running Windows 11 on. Wow. So I don't think it's a problem that Incontrol is blocking it. But I wanted to let our listeners know if they, if they want that, just turn off incontrol, manually run Windows Update and you'll see because I did. I ran Windows Update first to make sure that I was all caught up and I don't think anything happened. And then I turned off inControl, immediately ran Windows Update again and I saw exactly that KB 51716 installed itself and then I turned in Control back on again. So I've got that whatever that is you know, I don't know if I care, but you know, what the heck. Okay, a little bit of sci fi news because something's happening tonight. I finished, I should mention, Andy Weir's second book.
- [127:33]
Leo Laporte
You like the ending or.
- [127:34]
Steve Gibson
No, actually it came more quickly than I expected.
- [127:39]
Leo Laporte
Yeah, it kind of abruptly.
- [127:41]
Steve Gibson
Well, my Kindle showed me that I was at 90% of the way finished with the book when the plot wrapped up and the story ended.
- [127:49]
Leo Laporte
All done. Bye bye.
- [127:51]
Steve Gibson
It turned out that the remaining 10% of the book was a kind of interesting Q and A discussion with Andy and a discussion of the science and the underlying economic principles around which he had designed and created the scientifically and economically accurate, although entirely fictional storyline.
- [128:13]
Leo Laporte
I thought that was interesting. What it would take to have a colony on the moon. I thought that was very interesting.
- [128:17]
Steve Gibson
And he really did dig into that. I mean, again, it is science and it is fiction. So if somebody wants, you know, like a really solid piece of work, that's what you get every time from Andy. And he did deliver it. So yeah, it was an interesting story. I have to say though, I'm. I'm now reading something wacky like some scavengers have found have stumbled onto an alien ship of unknown origin that was trapped in a time bubble and something has infected one of them and it's like really interesting. So it's like, I guess I kind of like other wacky sci fi also. Anyway, shifting gears, I wanted to mention that today, August 12, 2025, begins the continuation of one of our generation's major sci fi franchises. Now, exactly two years before they debut of this franchise's first film, the world was taken by surprise on May 25, 1977, with the release of a film that, surprisingly, in retrospect, many people were unsure of. The movie's title was just Star Wars.
- [129:38]
Leo Laporte
Oh yeah.
- [129:39]
Steve Gibson
And needless to say, the world changed that day. Yes, I still recall sitting in a large theater in Palo Alto, Northern California with a big. With a big bucket of popcorn, having no idea what to expect and being astonished.
- [129:55]
Leo Laporte
Yeah.
- [129:56]
Steve Gibson
Then weirdly exactly two years later, by coincidence, on the same calendar day, May 25th, but this time, 1979, the world changed again when Ridley Scott directed and horrific alien creature from beyond our imagination to gestate inside an unwitting starship crew member and then to explosively emerge through his chest. Life just blew us all away.
- [130:30]
Leo Laporte
Yeah, that was a great movie.
- [130:33]
Steve Gibson
Oh my God. That scene and others were so over the top with surprise and tension that, that the movie Alien initially received somewhat Mixed reviews. Reviewers, I think, were afraid to like it and weren't sure what to think. But the movie went on to win the Academy Award that year for Best Visual Effects. Not surprisingly, three Saturn awards for best science fiction film, Best Direction by Ridley Scott, and Best Supporting Actress. Interestingly, not Sigourney, but Veronica Cartwright. Oh, she played the role of that, that kind of wimpy woman who was always screaming and freaking out. Yeah, she was really scared. And Sigourney's role didn't win her anything, but it definitely put her on the map.
- [131:25]
Leo Laporte
Oh yeah.
- [131:26]
Steve Gibson
The film also took home a Hugo Award for Best dramatic presentation. Now, once the world had caught its breath, it was able to look at Alien more objectively. Wikipedia now writes, in subsequent years, Alien was critically reassessed and is now considered to be one of the greatest and most influential science fiction and horror films of all time. Indeed, they said. In 2002, Alien was deemed culturally, historically or aesthetically significant by the Library of Congress and was selected for preservation in the United States national film registry. In 2008 it was ranked by the American Film Institute as the seventh best film in the science fiction genre and as the 33rd greatest film of all time by Empire. So for what it's worth, James Cameron's sequel, Aliens Plural is without any doubt one of my own personal favorite science fiction films of all time. For those who don't know, Aliens original theatrical release was missing some very interesting additional plot development footage that was later included in various of the directors cuts of the movie. They were worth watching. There was the, the scene where the, the family left the enclave and went out in their rover and actually brought the original infection back. That was completely missing from the original theatrical release. But we now know about that thanks to some of the director's cuts and there were a few other little scenes. I mean nothing hugely dramatic, but still. Anyway, I've watched all of that, all those movies several times and all the follow ons anyway. So it is with some anticipation that tonight Lori and I will be watching the first two episodes of the Ridley Scott produced big budget Alien Earth series which I didn't even know it'll be premiering on fx. FX on Hulu and internationally on Disney plus. So if you have access to FX or Hulu, the first two episodes are there. Now the first one of the these two was pre released a few weeks ago during San Diego's Comic Con which garnered the series a remarkably high IMDb rating of 8.8. Which you know, over the years I found IMDb ratings to generally be useful with 7.0 being my threshold for watchability. You know, if it's much below seven, you're not. It's like it's probably may not be worth the time, but if it's 8.8, we may have another winner. The first season is eight episodes. So seven weeks from today, on September 23rd, the eighth and final episode of the first series of the first season will be released. Oh, and Leo, one of the stars is Timothy Oliphant, who I also really like.
- [134:50]
Leo Laporte
What's the rough plot?
- [134:53]
Steve Gibson
It's the. So what's. What I don't understand is that is two years before the Nostromo encounters the alien in space. So it's actually set two years before the events of the first film. But an alien infected starship crash lands on Earth, thus Alien Earth. And we also have an, we have the, the, the A, A young egocentric, greedy corporate techie who's trying to create a more perfect human or something. And so he wants the technology that the alien represents. Of course. So anyway, it's meant to be many years. Apparently they spent more than $250 million on this. So I mean it is big budget. Lots of special effects trailers are online. So anybody who's curious can go. You know, maybe by the time you're hearing this, the whole. The, the first two episodes are already available. I mean, I guess they're available right now. Right. Because it is Tuesday, August 12th. But anyway, I just want to let everybody know I've always been a fan. Some of the follow on movies were kind of marginal.
- [136:16]
Leo Laporte
I like Prometheus. I don't understand.
- [136:19]
Steve Gibson
I didn't understand Prometheus. I still don't know what that guy was doing. Yeah, I don't know. I guess I could read the book, but. And the most recent one was kind of good. Romulus.
- [136:31]
Leo Laporte
I liked Romulus. Yeah.
- [136:33]
Steve Gibson
Yeah. So anyway, we have a. We have a big budget. Eight, eight episode multi. It's planned to be a multi year series. So let's hope it's good.
- [136:47]
Leo Laporte
Alien Earth.
- [136:49]
Steve Gibson
Alien Earth launches tonight. Yeah, I, and I. I'm hoping that it's not really over the top horrific because I'll have a problem with Lori. You know, I mean nobody wants to go that. Right. You know, go through that right before bedtime. So she saw some of the preview. She saw the pre. She watched the, the trailers with me and it does look really promising.
- [137:15]
Leo Laporte
Well, it's by Noah Hawley, who did the Fargo TV series.
- [137:19]
Steve Gibson
Yes.
- [137:20]
Leo Laporte
Which is one of the best TV series ever.
- [137:23]
Steve Gibson
I Agree. And of course Timothy has a great.
- [137:25]
Leo Laporte
Sense of the weird too, which is nice.
- [137:28]
Steve Gibson
Yeah, Timothy Oliphant, the actor I really like. He, he of course played the Marshall on, on Deadwood and, and he was Raylan Gibbons on the, on the, on FX's Justified series.
- [137:40]
Leo Laporte
Oh, he was good. All right. Yeah, I know who you're talking about.
- [137:43]
Steve Gibson
Yeah, yeah, yeah, yeah. He plays a cyborg.
- [137:46]
Leo Laporte
Oh, how funny.
- [137:47]
Steve Gibson
Yeah, so.
- [137:48]
Leo Laporte
Oh, I'm looking forward to this. Okay.
- [137:51]
Steve Gibson
Yeah, yeah. Okay, last break and then we're going to talk about perplexities, Duplicity, perplexities.
- [137:56]
Leo Laporte
But visit. Not easy to say. So I'm glad you said it. Not me. Well, we're so glad you're all here watching the show and we want to thank you for your support. Yes, we are an AD supported network. 75% of our revenue comes from the ads, but not all of it. The other 25% comes from you, our listeners. And I kind of like it that way. I always thought that all of our shows should be basically listener supported. So here's your chance to cast a vote. If you like the programming you hear on this network, not just Steve, but the Twitch show and Mac Break and Windows Weekly and Intelligent Machines and all the other things we do, we'd like you to join the club. Now you do get some rewards for being so perspicuous because of course, whatever that means, you get to be in the club Twit Discord, which is a great place to hang out for smart people talking about all kinds of topics, including aliens and more. We also do stuff in the club Twit Discord. We do shows in there. In fact, all of our coverage of keynotes is now in the club so we don't get taken down by overactive attorneys. So if you want to watch, for instance, our coverage of the Google event made by Google, their debut of the Pixel 10. We're going to do that. August 20, 10:00am Micah Sargent and I will be doing that. Micah does a lot of things. He's got a, he's planning a Dungeons and Dragons game night. You can go in there and vote on his D&D one shot adventure. He will, will be the dungeon master. But we're also gaming Friday night. This is something new Anthony Nielsen and John Ashley put together. They're going to be playing a co op climbing adventure called Peak. And there is more room for people in the team if you want to help them climb that mountain. But you can also watch, which I don't know, maybe I'll be doing that. We Have Micah's crafting corner. We got four photo time, we've got our AI users group. We're going to do some fun stuff with the local AIs and server technology. I can, I can go on, but I, I won't because I know you want to get back to Steve, but let me just put in a pitch, please. If you want to support what we do, if you want to get the benefits of ad free programming and all the events we do in the club, consider joining Club Twit. Only about 2% of you are members right now. That means that 98 out of the 100 people listening should be joining right now. Twit TV Club Twit, is that you? I look forward to seeing you in the club. Let's map out this week's amazing destinations and travel tips.
- [140:44]
Steve Gibson
Honestly, Will, I didn't plan any trips, but I did switch to T Mobile with their new Family Freedom offer.
- [140:52]
Leo Laporte
That's not the itinerary we're following.
- [140:54]
Steve Gibson
Well, I'm departing from ATT and embarking on a new journey with T Mobile. They paid off my family's four phones up to $3200 and gave us four new phones on the house.
- [141:07]
Leo Laporte
Bon voyage.
- [141:09]
Steve Gibson
Introducing Family Freedom. Our lowest cost will switch our biggest family savings all on America's largest 5G network. Visit your local T Mobile location or learn more@t mobile.com familyfreedom. Up to $800 per line via virtual prepaid card typically takes 15 days. Free phones via 24 monthly bill credits with finance agreement eg Apple iPhone 16, 128 gigabyte $829.99 eligible trade in eg IPH for well qualified credits end and balance due if you pay off early or cancel contact T Mobile. Ever notice how ads always pop up at the worst moments when the killer's identity is about to be revealed during that perfect meditation flow on Amazon Music, we believe in keeping you in the moment. That's why we've got millions of ad free podcast episodes. So you can stay completely immersed in every store story, every reveal, every breath. Download the Amazon music app and start listening to your favorite podcasts. Ad free included with Prime.
- [142:10]
Leo Laporte
Now back to this, the man of the hour, Mr. Steve Gibson. Okay, and security. Now, as soon as I get my mouse to respond. There we go. Go ahead.
- [142:21]
Steve Gibson
So as I said, this is one of those news bits that began in today's show notes as just another piece of news up at the top. But the more I dug into it, the more I appreciated its significance.
- [142:33]
Leo Laporte
All Right. I'm very interested in this because I'm a heavy Perplexity user.
- [142:37]
Steve Gibson
As everyone will see, the deliberate and extensive behavior Cloudflare uncovered and discovered of Perplexity's Internet behavior is significant. And I should mention I did not think to say this when I was going through this the first time. There's no reason to believe Perplexity is unique in this way. I mean, this is misbehavior. But we know OpenAI is not doing it. We'll. We'll talk about that, but we don't know who else might be. So it isn't my intention to single them out as the only bad guy around. Okay. But as we know, controversy emerged right alongside the appearance of the new capabilities of generative AI. The images being generated upon request often bore striking similarity to the known and copyrighted work of human artists. Poems and music sounded eerily familiar to those who were familiar with other original works of writers and musicians. Long before we began to realize that, you know, you know, so, so there was something, you know, familiar about this, right? And before long we began to realize that when massive large language models are trained on the Internet's content, all of which up to that point had been created solely by the application of human effort and creativity, anything that a generative AI might spit out was inherently a derivative work. Although it wasn't so directly. What we created carried a whiff of plagiarism. And in many cases it was much more than that. News sites began seeing the recognizable content of their human reporters appearing in the answers being offered by AI chatbots. None of this sat well with human creators who wish to receive recognition and support in return for their life's work. The solution was to deploy the Internet's well established automation controls to exclude these web scraping agents from websites that had no interest, thank you very much, in having their content absorbed by and used to train massive AI in the cloud. One of this twit network's own sponsors, which catered to programmers of all ilk, advertised their AI bot blocking as a feature so that their users could feel confident that their collaborations would remain theirs and not be leaked out into the ether to become the unpaid for property of this new generation of rapacious AI sponges. The Internet has a long history of bots. The bots most websites want and even actively invite and solicit are those belonging to search engines. Search was the early breakthrough application that entirely transformed the web. What good was it to create a quantity of terrific content of any kind, if only your friends and family would ever be aware of its existence. Search changed all that. But the reason search bots were wanted is that search engines would list links back to the sites containing the desired content. So search bots would indirectly drive human traffic to the website where humans would see where that link led them and then perhaps poke around and discover other goodies, all the while being presented with advertisements that were producing supporting revenue for the destination website. By comparison, AI model building bots are not indexing a site for later discovery and linking. They're proactively scraping up all of the site's content, every juicy little morsel, and then feeding that original content into a massive AI model in the cloud. Effectively, the entire site's content is being incorporated into the AI model so that no one will ever need to visit that site again. They'll simply be able to ask the AI to obtain a homogenized and digested version of that site's once exclusive knowledge and wisdom. They say that imitation is a sincerest form of flattery. That may be true, but flattery doesn't pay the bills, nor does it give credit to an idea's originator. The consequence was that websites the world over quickly moved to closing their doors to content sucking, model building, AI scraping. Thanks, but no thanks. It quickly became clear that AI bots were the exact antithesis of search bots. Whereas search bots drive serve to drive future traffic back to a site, as I noted, the effect of an AI bot's visit is to reduce that site's future traffic. The problem was, for any AI modeler, the entire Internet was the biggest and juiciest source of free, ready to go, machine readable content imaginable. You couldn't design a better source of training knowledge. Oh sure, there was that annoyance that the Internet, being a product of humans, also contained a large amount of nonsense and crap, and that the AI was no more able to tell the difference between truth and fiction than most of the humans who were consuming it. But none of that prevented the AI developers from turning their new scrapers loose on all that material to see what would happen. And then of course, AI became totally and utterly dependent upon that big, juicy, flowing source of ever changing knowledge. The fundamental problem of the entire approach is that it operates to model knowledge that it doesn't own, and in the process does not again need. So AI inherently takes from the world's websites without ever giving anything back. So as those website doors began closing to AI, it had a problem. What it needed, what it had selfishly grown utterly dependent upon, was being denied increasingly everywhere its Bots turned They were encountering bots Txt files sitting passively in the roots of website domains that were permitting and welcoming the world's known search engines to enter, but were also denying entry to anything and everything else, and definitely to anything that hinted at being AI. Thanks anyway. Go suck out someone else's brain without even saying thanks. Problem is, the robots. Txt file concept was created to help out bots. It's there for their own good, so it inherently depends upon the honor system. It's a file that by convention sits in a website's root directory. Shortly after I added the Shields up facility to GRC, I added a robot.txt file to my site. GRC's site today contains a bunch of automation that makes no sense to index the DNS spoofability pages. The Shields up service itself, our extensive Internet port references, and much more just cause bots to become all tangled up and lost. So GRC's robot TXT page lets bots know beyond where dragons lie. Importantly, the robot. Txt file is informational only. It is not any sort of enforcement mechanism. If some bot never looks at that file or chooses to ignore its warnings, it might become tangled up in endless link chain loops, pulling reams of nonsense data and wasting a great deal of its own time and resources. But if so, so be it. It's been warned. As a consequence, search engines are thankful and appreciative of of these robots. Txt files. They figured that since their presence and services are a benefit to the site's management, anywhere a site doesn't want them to go is fine with them. But as things have evolved with AI, this is not the case. A visit from an AI scraper is not seen as offering the same benefit to a website as a visit from a search engine. Search engines are visiting to find an index AI is here to steal. Last week, Cloudflare posted the news under the headline Perplexity is using stealth and undeclared Crawlers to evade Website no crawl directives, cloudflare wrote. We are observing stealth crawling behavior from Perplexity, an AI powered answer machine. Although Perplexity initially crawls from their declared user agent, when they are presented with a network block, they appear to obscure their crawling identity in an attempt to circumvent the website's preferences. We see continued evidence that Perplexity is repeatedly modifying their user agent and changing their source addresses to hide their crawling activity, as well as ignoring or sometimes failing to even fetch robots. Txt files. The Internet as we have known it is for the past Three decades rapidly changing. But one thing remains constant. It is built on trust. There are clear preferences that crawlers should be transparent, serve a clear purpose, perform a specific activity, and most importantly, follow website directives and preferences based on Perplexities observed behavior which is incompatible with those preferences. We have delisted them as a verified bottle and added heuristics to our managed rules that block this stealth crawling. So what happened? We received complaints from customers who had both disallowed Perplexity crawling activity in their robots. Txt files and also created WAF web application firewall rules to specifically block both of Perplexity's declared crawlers, Perplexity Bot and Perplexity User. These customers subsequently informed us that Perplexity was still able to access their content even when they saw its box its bots successfully blocked. We confirmed that Perplexity's crawlers were in fact being blocked on the specific pages in question. We then performed several targeted tests to confirm what exact behavior we could Observe. Get this, Leo. We created multiple brand new domains similar to testexample.com and secret example.com. these domains were newly purchased and had not yet been indexed by any search engine nor made publicly accessible in any discoverable way. We implemented a robot. Txt file with directives to stop any respectful bots from accessing any part of a website. We conducted an experiment by querying Perplexity AI with questions about these domains and discovered Perplexity was still providing detailed information regarding the exact content hosted on.
- [155:48]
Leo Laporte
Did they ask by name for those domains? Did they specifically say to Perplexity tell me what's on those domains?
- [155:57]
Steve Gibson
I don't know.
- [155:57]
Leo Laporte
Yes, they did. Okay, so everything they just said about it. Well, we made a new thing and it never could have known they told it where to go.
- [156:07]
Steve Gibson
They also blocked it in the robots. Txt file.
- [156:09]
Leo Laporte
That's not what robots. Txt is for. It's to keep your domain or pages from your domain domain out of a search index. This is a very controversial subject, Steve. I think you might be misunderstanding. I think Cloudflare is wrong on this one. But I'll let you finish and we can talk about it at the end. But I think it's more complicated, it's more nuanced than that. If you create a site and then ask an AI to go look at that site, just as you would ask a browser to look at that site, you can't complain when the AI goes to look at the site. If you do, you're going to break all agentic AI, all MCPs all research AI, same thing.
- [156:49]
Steve Gibson
So one problem. You're, you're saying the problem is that they created the site and they asked Perplexity. Yes, but that's not the. That's not the. The abuse case. They created the site and anybody could ask Perplexity.
- [157:03]
Leo Laporte
Right. If you ask a browser to go to a site and the browser shows you the site, that's how it's designed. Perplexity is very clear. They said, we are not looking at the site to add. To train on it. We're not training on that site. But the user asked us for a summary of that site. So we gave them that. It's like you going there on a browser. How is. That's not what they were doing. They weren't training on it. I understand if you say, oh, they're just training on every site they can find. By the way, if, if you didn't have AI training every site that you could find, it wouldn't be very useful either.
- [157:40]
Steve Gibson
Oh. So unfortunately, this doesn't say either way whether they were. Whether they were training or not. What?
- [157:47]
Leo Laporte
No. Perplexity had a response which you should read.
- [157:49]
Steve Gibson
Okay.
- [157:50]
Leo Laporte
Because they say they were not.
- [157:51]
Steve Gibson
Oh, okay, good. Well, then in that case, that's significant. Although Perplexity goes to great lengths to avoid. So, okay, so let me just finish what Cloudflare saw. So they said, we conduct an experiment by querying Perplexity AI with questions about these domains and discovered Perplexity was still providing detailed information regarding the exact content hosted on each of these restricted domains. The response was unexpected, as we had taken all necessary precautions to prevent this data from being retrievable by their crawlers.
- [158:33]
Leo Laporte
Except for removing it from DNS. If they hadn't published the domain, Perplexity wouldn't have found it. They couldn't have asked for it.
- [158:42]
Steve Gibson
Well, it's a valid website, Leo, so just hold on, let me finish this.
- [158:47]
Leo Laporte
It's a valid. That's very important though. It's a valid website.
- [158:50]
Steve Gibson
Okay. They said are multiple test domains explicitly prohibited all automated access by specified and robots Txt and had specific web application firewall rules that blocked crawling from Perplexity's public crawlers, their crawlers. We observed that Perplexity uses not only their declared user agent. Fine. But also a generic browser intended to impersonate Google Chrome on Mac OS when their declared crawler was blocked. So they are explicitly and deliberately bypassing someone's attempt to block them. We have two user agent strings in the show notes which Cloudflare shared the standard perplexity AI user agent and then the stealth one which pretends to be Apple WebKit Safari. They said both their declared and undeclared crawlers were attempting to access the content for scraping contrary to the web crawling norms as outlined in RFC 9309. This undeclared crawler utilized multiple IPs not listed in Perplexity's official IP range and would rotate through these IPs in response to the restrictive robots TXT policy and block from Cloudflare. In addition to rotating IPs we observed requests coming from different ASNs in attempts to further evade website blocks. This activity was observed across tens of thousands of domains and millions of requests per day. We were able to fingerprint this crawler using a combination of machine learning and network signals. Okay, so Perplexity LEO is deliberately and purposefully working hard to bypass a website's a web management's own decision whether they want Perplexity to have anything to do with their site or not. And I would argue that any website has that right.
- [161:06]
Leo Laporte
It raises it's. Look, I'm not going to say I know for sure what the answer is because there are all sorts of problems with crawlers bringing sites down. Wikipedia's had a huge problem with crawlers doing that. There is a. In my mind, there's a difference between training on a site and going to a site because a user requested information about that site from the AI. All anytime you use a research AI, if you go and say, hey, tell me more about vitamin D to ChatGPT Research or DEEP Seq or any of these, if they're using the modern web, they're basically doing the same thing, which is they're going to a bunch of sites, they're going to give you, you know, a source on the site and summarizing it. Now we can decide that we don't want that to happen and that they I think you need more than robots txt, but let's say you have you use robots txt and you're saying you don't want them to do that. That's going to very much impede Agentic and MCP usage. It's going to impede research AIs.
- [162:12]
Steve Gibson
It's going to all of it's the sites. Right? Cloudflare is saying that their customers said we don't want Perplexity on our site. And so they put rules in following Perplexity's guidelines. Perplexity lists the IP ranges that they come in from. Perplexity has a user agent. Yes. And Perplexity did not abide by the block. And not only that, they went to extreme. They managed to generate IPs from other top level ISPs using different ASNs, because even using a different IP within the same top level provider could be seen as a signal. So they've gone out of their way to evade the clear. The, the, the cleared request by a webmaster. We don't, you are not welcome here. And I think end of it, period. Anyone has a right to say I don't want you visiting my site.
- [163:20]
Leo Laporte
Does anybody have a right to say if you don't see my ads, I don't want you to see my site? I guess they do, right? You could say you've got to have the ads or you can't see my site.
- [163:29]
Steve Gibson
Many people do that. Yeah. Huh.
- [163:31]
Leo Laporte
An ad blocker does that. An ad blocker is deciding what part of the site to display and what part of the site not to display, violating probably in many cases the desire of the site's owner. And yet we use ad blockers. I think there's an issue here because the real question is an AI company different than a browser? If I decide to use an AI to look at a website versus a browser to look at a website, you're saying the webmaster should be able to distinguish between the two. And I say, yes, that's probably true, but it's not as clear cut as you say, because I'm just using a different tool, a browser like tool to look at that site. Maybe I want to aggregate information about vitamin D from 20 sites. I could manually go to each site or I could ask a tool to go out, look at those sites and aggregate that data.
- [164:27]
Steve Gibson
So certainly if the site were to block access by perplexity, then perplexity would not be.
- [164:38]
Leo Laporte
Couldn't include that site in its sources.
- [164:40]
Steve Gibson
That's right, exactly. And so that would be the site's loss if they wanted to be included in perplexity sources. Apparently some of Cloudflare's customers don't want to be. I mean, I'm not here to psychoanalyze them. I don't know what they're thinking or why they don't want to be. Be part of that. It may be because they feel that AI is not in their benefit. Mean we had that advertiser who was boasting about the fact that they keep AI off the site. They didn't want AI, you know, sucking in all of their, all, all of their customers dialogue.
- [165:14]
Leo Laporte
Again, there's difference between training and going there to read the site, though. Yes. And I think people conflate the two. I understand you may say if you're read it or the New York Times, I don't want AIs to train on my content, but I think it's a very fine line to say I don't want a person to go read my content versus an AI. And this is a complex legal issue. It goes back to the First Amendment and the right to read. We talk about this a lot on im, which is probably where we should move this conversation. But Kathy Gellis, who's a constitutional lawyer, has often talked about if you start restricting the right of AIs to read, it undermines a fundamental First Amendment right, the right to read. And that's problematic.
- [166:03]
Steve Gibson
Wow.
- [166:04]
Leo Laporte
Yeah. Prep. So remember, we're not training here. We're asking for the contents of the site on behalf of the user.
- [166:15]
Steve Gibson
Now.
- [166:17]
Leo Laporte
Clapflare says it did everything to prevent that, except it published the site publicly.
- [166:22]
Steve Gibson
Well, everyone has a right to publish the site publicly.
- [166:25]
Leo Laporte
Yeah. So don't I have the right to use the browser of choice? And if my browser happens to be Perplexity, as opposed to Firefox, I guess.
- [166:35]
Steve Gibson
My only problem is that a very clear rules were put up which Perplexity themselves said they would honor.
- [166:44]
Leo Laporte
Right.
- [166:44]
Steve Gibson
The site said, we don't want you. So we, we don't, you know, we're. We're blocking you. And then Perplexity demonstrated that they will go to extreme measures to circumvent that preference stated by the site.
- [167:02]
Leo Laporte
Right.
- [167:03]
Steve Gibson
So, you know, and for example, OpenAI doesn't do that at all. They ran the same test against other.
- [167:10]
Leo Laporte
AIs that honorable rules, because OpenAI, when it does research, does do that. And I suspect that Cloudflare, to be honest, was more interested in getting attention with this than they were in actually doing this deep research. And that's certainly the claim that Perplexity makes. I think it's complicated. I don't know what the right answer is. You're right. One of the things Perplexity said is that Cloudflare's diagram of how Perplexity works was incorrect. It was just fundamentally wrong. And they never asked us. That's not how it works. Perplexity said Cloudflare is either dangerously misinformed in the basics of AI or simply more flare than Cloud. Remember, the Cloudflare has a vested interest in people saying, you know, using its tool.
- [168:08]
Steve Gibson
I get it. Yep.
- [168:10]
Leo Laporte
Even more embarrassing, Perplexity said Cloudflare published a technical diagram supposedly showing Perplexity's Crawling workflow. That bears no resemblance to how Perplexity actually works. If they were interested in understanding the data, they could have done what we encourage all Perplexity users to do. Just ask.
- [168:25]
Steve Gibson
Okay, so the. That's not fair. I saw the diagram. I study the diagram. I understand the diagram. The diagram is correct. The diagram is something different than what you're reading, that Perplexity is saying that, okay, what Cloudflare showed in that diagram was the exact behavior they observed. So that is a diagram of observed behavior based on when Perplexity Bot was blocked and what they then saw Perplexity do as a consequence of the blocking.
- [168:59]
Leo Laporte
So that's because Perplexity occasionally uses something called Browser Base, which is an automated browsing service. They say Cloudflare misattributed 3 to 6 million daily requests from Browser Base to us.
- [169:12]
Steve Gibson
That's entirely reasonable.
- [169:13]
Leo Laporte
Yes, because we don't use all. We didn't use and do not use all of Browser Base's capacity. We use a small fraction of it on occasion.
- [169:24]
Steve Gibson
And that could also account for the differing ASN sources of the IPs.
- [169:28]
Leo Laporte
Exactly.
- [169:31]
Steve Gibson
Is coming from, from a different top tier provider.
- [169:34]
Leo Laporte
I don't know what the answer is. I read the Cloudflare thing and I was as incensed as you were. And then I read Perplexity's response and I thought, well, this maybe is more complicated, but there is also this fundamental issue of.
- [169:46]
Steve Gibson
Yeah, that's really interesting. It's interesting that, I mean that the First Amendment protects AI to read.
- [169:53]
Leo Laporte
Well, it protects. See, the courts haven't said it protects our right to read. And Kathy Gellis's concern is if the courts say, well, AIs don't have the right to read, that it may well impinge on our right to read. Is that being tested? Not yet. I think that what's important is there's this concept of the open web, the idea that you put something on the web, you're putting it out there for everybody to read. Now, I understand there's a lot of issues around this bandwidth issue.
- [170:23]
Steve Gibson
All the economics that have developed economics.
- [170:26]
Leo Laporte
Ads and all of that. So this is really complicated. But fundamentally, I'm a believer in the open web. The whole point of the web is putting that information out there for everyone. And I think it's discriminatory to say, well, there's only one way you can look at my website, and that's in Firefox or Chrome. What if some website said, we don't want anybody with Firefox to visit our website, they'd have the right to do that. But is it fundamentally. But it fundamentally to me undermines the concept of an open web.
- [170:57]
Steve Gibson
Yeah, but then, you know what, what about a paywall?
- [171:01]
Leo Laporte
Right? We're talking, we're really talking about is property rights and I think the web. I'm a hippie.
- [171:10]
Steve Gibson
Did you see that Perplexity has offered to buy Chrome?
- [171:14]
Leo Laporte
Yeah, that's a publicity stunt because it's actually. They're offering more money than they're worth.
- [171:18]
Steve Gibson
Yes, 34 million or billion, rather. Yeah, yeah.
- [171:22]
Leo Laporte
You know, it's Perplexity. What Perplexity does, it does better than anybody else. I've used Perplexity for two years and I really like it. I have a paid account with Perplexity, but of course I have a paid account with every single AI I can get, including Kagi and, but Perplexity Kagi have assistance that do this kind of aggregating and I think it's incredibly valuable. And I think we have to ask ourselves whether we want the open web to be truly open or whether we want it to be fiefdoms that are pulled by the property owners.
- [171:54]
Steve Gibson
Perplexity does no training. They're not an AI that has a model.
- [171:59]
Leo Laporte
Well, they use other, other people's models. For the most part they are front end to a variety of models. In fact, when you're using Perplexity, you can use variety of different models, including.
- [172:10]
Steve Gibson
Are they the trainers of those models? No, no, no, I guess is the question.
- [172:14]
Leo Laporte
They're tuning them maybe, I don't know. But no, they primarily they started as being an aggregator of other people's models, third party models. So.
- [172:21]
Steve Gibson
So like calling into their, like to OpenAI's API and getting the results of its training or are they training.
- [172:30]
Leo Laporte
Yes, themselves, the former. Huh. Now I think over time Perplexity has added some additional LLMs of its own, but. And also they're not completely forthright on exactly how they're combining AIs and so forth. But the whole idea of Perplexity was it was a meta AI, it was an AI that let you choose the model. Anthropic or OpenAI.
- [172:55]
Steve Gibson
Well, and it would be interesting to know why these Cloudflare customers are not wanting Perplexity to visit their site.
- [173:02]
Leo Laporte
Well, remember, this wasn't Cloudflare customers. This is Cloudflare setting up dummy sites.
- [173:07]
Steve Gibson
No, no, no, this was instigated by, by Cloudflare customers who, who put up all the blocks themselves. And then Perplexity got around them and then they complained. Perplexity is not Honoring our request for it not to. So this is our site.
- [173:25]
Leo Laporte
This was in response to.
- [173:27]
Steve Gibson
Yes. And then Cloudflare investigated.
- [173:29]
Leo Laporte
Yeah, and maybe investigated making some mistakes. I'm not sure. I think it's very complicated, and I think we really have to think about what our fundamental values are when it comes to the web. How open we want the web to be, or do we want to carve it up into little fiefdoms? And if we do, then we should probably abandon the concept of research AIs and AIs in general, because if AIs can only train on a very limited set of information, they're going to be less.
- [174:00]
Steve Gibson
Well. And it's very clear that this does upset the traditional economics.
- [174:06]
Leo Laporte
Well, so does Google. I mean, we're at Google Zero, right? Google no longer sends site traffic. Well, they claim they do, but I don't believe Google sends as much traffic as they used to.
- [174:15]
Steve Gibson
Right.
- [174:15]
Leo Laporte
And by the way, so do paywalls. I mean, they also cut your site traffic. So it gets. It's complicated, I guess, is my answer. And I don't fully credit what Cloudflare says. I think it's more complicated, more nuanced. That's all I wanted to say.
- [174:33]
Steve Gibson
Okay.
- [174:34]
Leo Laporte
I think you make an excellent point that ultimately a property owner should be able to decide who enters their property. But then we have to ask the question, well, is that what we want on the web is a bunch of private property?
- [174:48]
Steve Gibson
That's what we have. That is what has happened. You know, and now we're putting age restrictions and laws behind.
- [174:56]
Leo Laporte
Yeah, none of that seems to me to be the right direction. I feel like we could have more value out of the web if it were more open.
- [175:04]
Steve Gibson
But yeah, it's just, it's. You know, the Internet's become a microcosm.
- [175:08]
Leo Laporte
Of our world, but this is why we do podcasting in the old fashioned way. This is why we're not exclusive on Spotify or Audible or Amazon, but we do RSS feeds. Because it's open.
- [175:20]
Steve Gibson
Yep.
- [175:20]
Leo Laporte
Right. And I'm a. See, I'm a believer in the open web. We do Creative Commons content. My blog is open. I don't have any robots txt on it, because I think that's the right way to go. But I understand not everybody feels that way. And we need to figure out there are competing needs in this.
- [175:39]
Steve Gibson
That's what makes all this interesting, my friend.
- [175:40]
Leo Laporte
It is. It's what makes it interesting, isn't it? Anyway, thank you for letting me interrupt.
- [175:44]
Steve Gibson
No, no, I'm done. I think We've, we've had a great conversation about this and I'm glad you brought that view because it was, you're right, mine was single sided and Cloudflare centric.
- [175:55]
Leo Laporte
Yeah. Read what Perplexity says. There's a lot of debate on the net. We've talked a lot, we talked last week extensively on intelligent machines about it and I don't know what the right answer is. I do agree with you. A property owner should be able to build a fence that nobody can go over. I agree with you. I don't think it's the way to divide the web up, but if that's.
- [176:16]
Steve Gibson
What happens and, and I guess I'm a bit of a Cloudflare fanboy. I really do believe those guys. They're, I agree. Everything they do is, you know, they know their technology, they know the web. I, I just think they're on the right side. And so, you know, that may have biased me toward them, but you know, Perplexity has something to lose too if it's, you know, you know, it's needing to respond to this. I, I just don't know, you know, how open they've been.
- [176:43]
Leo Laporte
Right. Perplexity says when companies like Cloudflare mischaracterize user driven AI assistants as malicious bots, they're arguing that any automated tool serving users should be suspect a position that would criminalize email clients and web browsers or any other service. A would be gatekeeper decided they don't like. And then you're saying gatekeepers should be able to keep their gates.
- [177:08]
Steve Gibson
Yes. And they specifically list the range of IPs that their bots operate from. And so if someone says thank you for that.
- [177:20]
Leo Laporte
Oh, that's, this is that third party tool that they were using. And that's part of the problem.
- [177:24]
Steve Gibson
Yeah, yeah.
- [177:26]
Leo Laporte
And I think that's where the real disconnect was, that Cloudflare misunderstood.
- [177:31]
Steve Gibson
I hope I would be interested in Cloudflare's rebuttal to Perplexity's rebuttal because, I mean, I'm just, I'm academically interested. But it does seem that, you know, when Perplexity's named user agent is denied suddenly a non. Perplexity.
- [177:49]
Leo Laporte
Right.
- [177:50]
Steve Gibson
Safari. You know.
- [177:53]
Leo Laporte
There is a history too of Perplexity doing this is the wired story from June 19 not mincing any words. Not mincing any words. There is a history of Perplexity doing some shady things. So I'm not saying perplexity is absolutely in the right on this. I'm saying it's a larger Subject than just perplexity versus Cloudflare. It's about what we want the web to be kind of.
- [178:21]
Steve Gibson
Yeah, yeah. Anyway, we get the world we want.
- [178:26]
Leo Laporte
Yeah. I don't know if we get the world we want. Well, we get the world. We get the world we deserve. Maybe, maybe the world we deserve. Steve Gibson is@grc.com interestingly, you don't block anything from your site, do you?
- [178:41]
Steve Gibson
No.
- [178:42]
Leo Laporte
Do you have a robots txt only.
- [178:45]
Steve Gibson
To keep shields up and DNS spoof ability because you don't want Google trying to index something that is. That is checking a user's, you know, bandwidth connection.
- [178:56]
Leo Laporte
See, that's a very good use for robust text.
- [178:59]
Steve Gibson
Yeah.
- [178:59]
Leo Laporte
And should be absolutely honored. GRC has a number of things you probably want to know about. First of all, if you want to email Steve with your comments or suggestions. Actually Steve has a couple of feedback mechanisms, as do I. Steve's got a forum@grc.com which is. I want. We don't talk about it enough. It's a great forum, great place to talk about all of the stuff, stuff that goes on. Here is where Squirrel really was a big part of the Squirrel development. There's also a place where you can get your email whitelisted so that you can email them. That's grc.comemail but when you do submit your email to that and Steve will vet it and say, oh good, yes, you can send me emails because you're not a bot. There are two checkboxes unchecked by default, but you might want to check them. One for the weekly newsletter that is the show notes for this show. Another for a much less frequent newsletter or just even an email about new products, things like that. Important stuff. He sent out one email in 10 years, folks. It's not a very. That is as infrequent as you can get.
- [180:00]
Steve Gibson
And I was thinking I. If this incontrol actually was creating a problem, I might have to send out the second one. Perfect example to let people know maybe you want to turn off for a minute and then update, you know, update Windows.
- [180:14]
Leo Laporte
So that's the kind you check those boxes, you want those emails. He's not going to bombard you, trust me. He's certainly not going to sell your email address. This guy. Are you kidding me? You can also get the show there. Steve has unique versions in every respect. There's 128. No, sorry. There's a 16 kilobit audio version, really small. There's a 64 kilobit audio version which is frankly all the bits you need. Full fidelity mono. There's also the show notes that he writes and very complete links and everything. I mean, they're the best show notes I've ever seen. It's like a. It's like a magazines. It's not even a column. It's like a how. What is the 8,000-Word-article? It's huge. Then there's. And he works hard on it, so you certainly want that. And like I said, you could subscribe to that. Also the transcript written by Elaine Ferris, who does a very good job. She's an actual human being.
- [181:07]
Steve Gibson
She'll be typing furiously in the next couple days.
- [181:12]
Leo Laporte
Takes a few days, but she's a court reporter, so she's pretty quick. So she'll get that out. And that also goes@grc.com you know, really, while you're there, you might want to check out Spin, right? We're just talking about how you could save your Kindle with Spin, right? It's the world's best mass storage and that means hard drives and SSDs and even embedded EMM memory inside your object like a Kindle. It can maintain it, it can restore it, it can improve its performance. In many cases, it's a must have. Grc.comspinrite there's lots of other free services. As he mentioned the DNS benchmark, the shield's up. There's so much good stuff. GRC.com we have copies of the show at our site. We have different copies. We have for reasons far too complex and boring to go into 128 kilobit audio version of the show. Unnecessary bits, I acknowledge that.
- [182:06]
Steve Gibson
But that's for those with excess storage.
- [182:08]
Leo Laporte
Those with plenty of storage. And you really want to store the big file, get the video. Because we do do video of the show. If you don't want to store it, you just want to watch it. There's a YouTube channel dedicated to security now. Great place to watch. Even better place to clip and share so you can tell other people about stuff. And then the best thing to do, probably subscribe in your favorite podcast client. You can get the show automatically via a miracle called rss. It just happens. And there are plenty of podcast clients. Any one of them will work. Leave us a good review. If you do use one that has reviews. Five stars or whatever, 18 pickles, whatever it is that they, that they use. I used to say five stars and then I found out there's some that do 10 stars, some that do three stars. So the maximum number of all the stars. All the stars. We do the show and you can watch us live if you want. The very, very, very freshest kind of unbaked version of the show. We do it live every Tuesday right after Mac break weekly. That's usually if we're on time. 1:30 Pacific, 4:30 Eastern, 20:30 UTC. The live streams are. Well, there's one in the discord. That's for all the club members, but there's also for everybody else. YouTube, Twitch TV, TikTok, X.com, facebook, LinkedIn. I'm bringing a tear to Steve's eye. We've got to get out of here. He's crying, folks. And kick Twitch. Oh, okay. I thought you were just. I thought you were weeping over how many different things I have to do at the end of every show. Steve, I'm done with the business. I wish you the very best week. Always a pleasure.
- [183:45]
Steve Gibson
Well, we're going to have to decide next week whether we're going to have any spoilers for what happens on Alien Earth tonight.
- [183:52]
Leo Laporte
I'm gonna. I'm gonna watch. I better watch. I don't want. I don't want spoilers.
- [183:57]
Steve Gibson
8.8.
- [183:58]
Leo Laporte
I think there will be. I'm just thinking something that goes. But I don't know.
- [184:04]
Steve Gibson
Thinking there'll be something to grab our attention. If not. If not, somebody's face.
- [184:09]
Leo Laporte
Not Sigourney Weaver either. Unfortunately, no. All right. Enjoy that show. Best to Lori. Steve and I text during the week. I might be sending you a little tidbits as you send me. And we will see you next time on Security Now.
- [184:23]
Steve Gibson
Bye.
- [184:25]
Leo Laporte
And it's a long close. I apologize. The prologue or the post? We don't know how.
- [184:32]
Steve Gibson
We don't know how many people listen to it, but that's fine.
- [184:34]
Leo Laporte
Well, we got to do it. Yeah, that's right. They probably just say, okay, mine is done. Leo's doing that.
- [184:38]
Steve Gibson
We got all the good stuff.
- [184:39]
Leo Laporte
Oh, my God. Yeah. I wish I could watch it tonight. We're going out to dinner. But, like, you know what? I think I could tape record it.
- [184:47]
Steve Gibson
It'll. Yeah, you can. You can TiVo it. Leo.
- [184:50]
Leo Laporte
TiVo it. Thanks, Steve.
- [184:53]
Steve Gibson
See you guys next week.
- [184:55]
Leo Laporte
Take care. Is this your last Security now for a while?
- [185:00]
Steve Gibson
No, no, I got next one more and then I'm off for two.
- [185:04]
Leo Laporte
This is Security. Security now.