← All TWiT.tv Shows (Audio)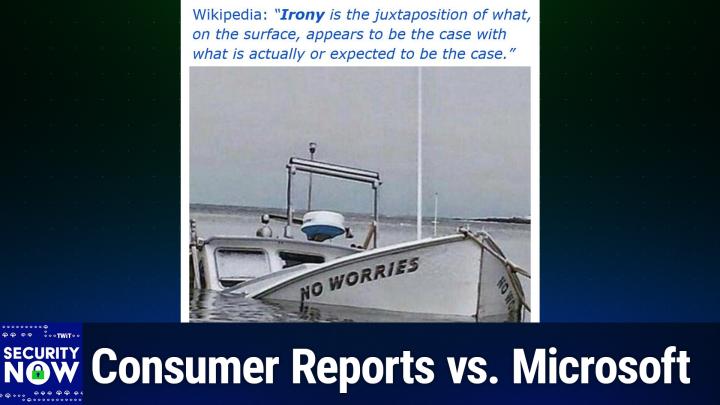
All TWiT.tv Shows (Audio)
Security Now 1044: The EU's Online Age Verification
03:01:41
Consumer Reports vs. Microsoft
Loading summary
Transcript303 lines
- [00:01]
Leo Laporte
It's time for Security Now. Steve Gibson is here. We're going to take a look at a Spanish proposal for age verification that Steve says is privacy protecting and really might just work. We'll also find out why DDR5 is still vulnerable to cyber attacks. Why Consumer Reports says Microsoft, you ought to let us keep Windows 10 for a little bit longer. And Deep Seek, does it produce deliberately flawed code for groups the Chinese government doesn't like? All that more coming up next on Security now.
- [00:38]
TWiT Network Announcer
Podcasts you love from people you trust.
- [00:43]
Leo Laporte
This is Twit. This is Security now with Steve Gibson. Episode 1044 recorded Tuesday, September 23, 2025. The EU's online age verification. It's time for Security now. The show you wait for all week long. I know I do. Every Tuesday we get to hear from this man right here, Steve Gibson, about the latest in privacy security, how technology works and. And we all get the Vulcan salute. Hello, Steve.
- [01:15]
Steve Gibson
That's right. Or the. The shot to the temple.
- [01:19]
Leo Laporte
No, don't do that. No, no, no, no. By the way, because I practiced my piano and I do the Leschitsky method which is seriously is a thing you do with piano.
- [01:31]
Steve Gibson
I can now Leitzki.
- [01:33]
Leo Laporte
Yeah. So he invented a method for strengthening the fingers for piano players. I did not used to be able to do this with my left hand. I could do it with my right hand.
- [01:42]
Steve Gibson
Well, Leo, progress takes all different forms. Look at that. You could also do. You could do shadow puppets. When you next.
- [01:51]
Leo Laporte
I can now a.
- [01:53]
Steve Gibson
A slide presentation for your guests of your most recent trip.
- [01:58]
Leo Laporte
We are, we are. We should mention for those listening only on audio, we are doing the live long and Prosper Vulcan salute.
- [02:04]
Steve Gibson
And no one knows why.
- [02:05]
Leo Laporte
Do you think we're supposed to do that with the left hand? I think that was somebody tell me because you do it with your left. I do that. I'm.
- [02:12]
Steve Gibson
I'm left handed and I got a microphone over here. So it gets really confusing.
- [02:16]
Leo Laporte
I'm left handed and it's not. I can't. It's easier with my right. I don't understand.
- [02:20]
Steve Gibson
Anyway, this looks like something else.
- [02:24]
Leo Laporte
That is not the Lesky method. So ladies and gentlemen, the security now is on the air. What's coming up, Steve?
- [02:30]
Steve Gibson
So the big news is that following some stories and some links, I discovered that I think it was two months ago that Spain announced that they were going to be bringing an age verification technology online. And I said what? Huh? Just like that? Just like that. And yeah, even though I was alone, which worries my wife, but that's what we're going to talk about. We're going to talk about the EU's online age verification. This, this was, I got got onto it because of a piece of news about Brazil's the entire country of Brazil's recent legislation. And you can imagine what that looks like. We'll talk about that and then lead into online age verification, which I, I, I'm not gonna you asked me before we began recording did it is it good or is it bad? And I told you but I'm not going to tell our listeners because they're going to have to either, you know, like fast forward or wait for it if you're live tough. So we're also going to oh, and I couldn't resist, Leo, I, I'm going to quote Stacy because she's my gal as regards Windows 10 updates.
- [03:50]
Leo Laporte
Yes. She and I corresponded over that great letter that she yeah, well I'm going.
- [03:55]
Steve Gibson
To share it with our listeners because it makes, it may actually it makes a few points that hadn't occurred to me. I get, you know, a little deep in the weeds with technology, which arguably is why people keep coming back to this podcast. But there's a different take that Stacy had on Microsoft's decision to do what they've done with 10 ver Windows 10 versus 11. I want to share that. Also, there was an interesting article about, you know, waste and I, I'm not saying fraud or abuse, but waste within DoD's cyber operations. We got some counts from the GAO, the Government Accountability Office about okay, like whenever you do something in government in a hurry, it's generally not a good idea. And we see an example of that. We also have some news that China's Deep Seek is able to deliberately give bad code depending upon who's asking.
- [04:59]
Leo Laporte
I thought that was really interesting.
- [05:01]
Steve Gibson
Yeah, it's like, wow. Webassembly reached version the official version 3.
- [05:07]
Leo Laporte
0.
- [05:07]
Steve Gibson
We've got a new release of Firefox with some interesting updates and also one for Android that I'm not sure anyone cares about, but we'll talk, we'll cover that. Also, what I would consider a nearly fatal flaw was found in Microsoft's main identity system for their cloud system. Their their whole cloud services entra id. And this brings up some interesting questions of its own. Also, Chrome has hit its sixth zero day this year with with some interesting events. Turns out that DDR5 is still vulnerable to Rowhammer. Who'da thunk? Well, we would because, you know, we're not impressed by any of these mitigations. Samsung Refrigerators have surprised their owners. China says no to Nvidia. We've got more NPM malicious packages found and then we got some feedback from our listeners. That's interesting. And then we're going to wrap up by talking about what Brazil did that led me into discovering what Spain is doing and a few other countries in the eu and what we think about the way they're going to be handling online age verification. So maybe this podcast is worth listening to this week.
- [06:30]
Leo Laporte
Maybe. Definitely. Most definitely.
- [06:33]
Steve Gibson
Oh, we've only had 1043 before this one, so this is eventually.
- [06:39]
Leo Laporte
Yeah, that's right.
- [06:40]
Steve Gibson
We're getting the hat.
- [06:41]
Leo Laporte
That's right. Yeah. We will get to the picture of the week, which I have yet to look at, so I will join you in being shocked, surprised and amused by it in that order.
- [06:53]
Steve Gibson
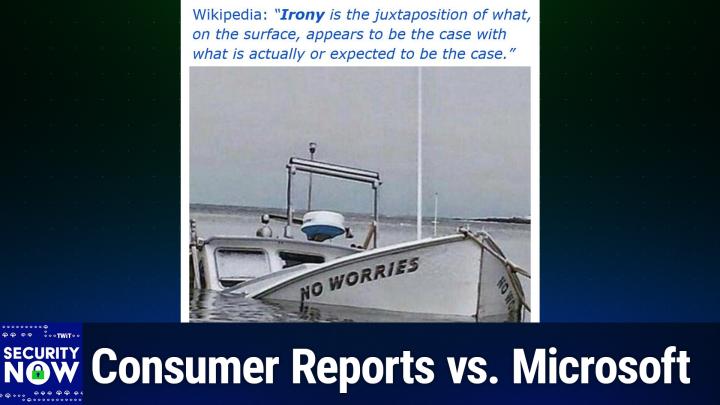
I quoted Wikipedia's definition of the word irony, wow. As our caption for this picture. Yes, all right, says irony is the juxtaposition of what on the surface appears to be the case with what is actually or expected to be the case. And we have a picture that probably captures the concept of irony better than anything I've ever seen.
- [07:17]
Leo Laporte
Oh wow. All right, it's pretty good. That's coming up on Security now. But first a word from our sponsor for this segment. BigID, the next generation AI powered data security and compliance solution. Bigid is the first and only leading data security and compliance solution and to uncover dark data through AI classification, to identify and manage risk, to remediate the way you want to remediate, to map and monitor access controls and to scale your data security strategy along with unmatched coverage for cloud and on prem data sources. Bigid also seamlessly integrates with your existing tech stack. That's nice and allows you to coordinate security and remediation workflows. You can take action on data risks to protect against breaches, prevent and protect against them, to annotate, delete, quarantine and more based on the data, all while maintaining an audit trail. And it works with everything you work with. Partners include ServiceNow, Palo Alto Networks, Microsoft, Google, AWS and more. With BigID's advanced AI models, you can reduce risk and accelerate time to insight and gain visibility and control over all your data. Intuit named it the number one platform for data classification in accuracy, speed and scalability. Imagine who would have the most dark data that they would need to classify. Who would that be? Maybe the US Army. Big ID equipped the army to illuminate dark data to accelerate their cloud migration, to minimize redundancy and to automate data retention. These are all high priority goals for the army and U.S. army. And Training Doctrine Command gave big ID such a great endorsement. They said this is the quote, the first wow moment with BigID came with being able to have that single interface that inventories a variety of data holdings, including structured and unstructured Data across emails, zip files, SharePoint databases and more. To see that mass and to be able to correlate across those is completely novel. I've never seen a capability that brings this together like Bigid does. End quote. That's pretty high praise. Cnbc recognized Big ID as one of the top 25 startups for the enterprise. They were named to the Inc 5000 and Deloitte 500 not just once, but four years in a row. The publisher of Cyber Defense magazine says quote, big ID embodies three major features we judges look for to become winners. Understanding tomorrow's threats today, providing a cost effective solution and innovating in unexpected ways that can help mitigate cyber risk and get one step ahead of the next breach. Start protecting your sensitive data wherever your data lives. @bigid.com SecurityNow Get a free demo to see how BigID can help your organization reduce data risks and accelerate the adoption of generative AI. Again, that's bigid.com securitynow. Oh, also get an exclusive invite to BigID's virtual.com summit on October 9th, where you can hear a keynote featuring Forrester research. Plus panels with experts from JP Morgan, Manulife and Nokia tackle the most urgent challenges in AI, security and risk. @bigid.com SecurityNow. We thank him so much for the support of Steve and the great work he does here at Security. Now. I think I have my. I do. I keep turning these off, the, the Apple reactions. And for some reason, yeah, they keep happening.
- [11:04]
Steve Gibson
And is it, I was wondering, is it listening to you or seeing you?
- [11:07]
Leo Laporte
You seeing the gestures?
- [11:09]
Steve Gibson
Oh, okay, yeah.
- [11:10]
Leo Laporte
And I, but the thing is, I turn it off every day and it.
- [11:13]
Steve Gibson
Comes back, Leo, they know you actually want it on.
- [11:17]
Leo Laporte
I want the little bubbles. Laser light showing.
- [11:20]
Steve Gibson
Yeah, that's right.
- [11:21]
Leo Laporte
Anyway, I apol. Apologize for that. All right, I'm ready for the picture of the week.
- [11:26]
Steve Gibson
The picture of the week, which epitomizes irony more than probably anything I've ever seen.
- [11:31]
Leo Laporte
Okay, I'm scrolling up. I'm going to leave the camera on my face as I do so. Okay. I remember we, I took my son after he graduated from college. I took him on a. A sailing trip around the British Virgin Islands. And it was right after a massive hurricane and there were a lot of boats in the same.
- [11:59]
Steve Gibson
So what we have here is a, is a picture of a boat which is in trouble. It's a power boat and the, the back end is, I mean it's basically it's sinking it. Its back end is submerged completely, but that has pushed its bow up and out of the water, allowing us to see the boat's name, which is no worries.
- [12:28]
Leo Laporte
No worries, Mom.
- [12:29]
Steve Gibson
And indeed, yes, well, maybe one worry. Maybe one. Yeah, maybe one big one. Although they do say that the, the, a, the, the best two days in a sailor's life is the, the day he purchases a boat and then the day he sells that boat. Oh boy.
- [12:50]
Leo Laporte
Yeah, that's so of course.
- [12:51]
Steve Gibson
And, and here I, I liked a little bit of a pun here. It says irony. The Wikipedia's definition, irony is a juxtaposition of what on the surface appears to be. It's like, well, this boat is no longer on the surface.
- [13:05]
Leo Laporte
Yeah, that's right, that's right.
- [13:08]
Steve Gibson
Anyway, great, great, great picture. Okay, so exactly one week ago, as we were recording last week's episode, the famous Consumer Reports site publicly posted under the headline Consumer Reports calls on Microsoft to extend Support for Windows 10. I was surprised to recognize the name of the author of the piece since I didn't know that I knew anyone at Consumer Reports, especially someone whose knowledge and opinions are I greatly respect. Consumer Reports piece was written by twit's well known longtime podcast co host Stacy Higginbotham.
- [13:53]
Leo Laporte
She's a policy fellow. Yep.
- [13:55]
Steve Gibson
And they're lucky to have her in Consumer Reports name. Stacy wrote the following September 16, 2025 to address to Satya Nadella, Mother Microsoft Corporation, 1 Microsoft Way in Redmond, Washington. Dear Satya Nadella, Consumer Reports is concerned about Microsoft's decision to end free ongoing Support for Windows 10 next month. This decision will strand millions of consumers who have computers that are compatible with Windows 11 and Force. That are incompatible. Yeah. That are incompatible with Windows 11 and force them to pay $30 for a one year extension of support, spend hundreds on a new Windows 11 capable computer, or do nothing and see the security and functionality of their computer degrade over time. This latter option is particularly problematic as it risks harming the consumer as well as co opting the machine to perpetrate attacks against other entities risking national security. Oh, you go girl. Four years ago, when Microsoft released Windows 11, it announced that support for Windows 10, which was released in 2015, would end on October 14, 2025. Microsoft also said that because of the hardware requirements of Windows 11, namely a Trusted Platform Module 2.0 and a 64 bit processor that some consumers would need to upgrade their computer since their current machines would not be capable of running Windows 11. Despite this announcement in 2021, computers incapable of running Windows 11 were still available for sale in 2022 and 2023. We'll see why that's an important fact in a second, and this is one of the things that she highlights that hadn't occurred to me, she said. Even if Microsoft partners and retailers stopped selling machines that were not able to be updated to Windows 11 at the time of the launch, meaning Windows 11 launch, our research shows that that many consumers would still be trying to use the incompatible machines today. Based on the Consumer Reports member survey of 100,606 laptop and desktop computer owners, which was taken between January and March of this year, over 95% of all laptop and desktop computers purchased since the beginning of 2019 and and owned for no more than five years were still in use when members were surveyed. Moreover, 20% of our members who owned a Microsoft laptop reported owning them for at least four years, compared to just 13% of our members who owned any other brand of laptop for that length of time. We see similar trends when looking at all Windows OS compatible computer brands in our sample acer, Asus, Dell, HP, Lenovo, Samsung, and Intel as 15% of our members who own a Windows OS compatible laptop or desktop brand have owned them for at least four years, compared to just 12% of our members who own a laptop or desktop brand that is typically not Windows OS compatible. Based on these findings, we posit that our members who have purchased Windows Windows OS compatible computers on average tend to keep them for longer lengths of time than owners of other computers. Thus, it's clear that consumers purchased machines before Microsoft announced the hardware needs for Windows 11, expecting to be able to operate them through the next Microsoft OS transition. The decision to make Windows 11 incompatible with existing hardware and to do so with only four years notice is incompatible with consumer expectations and Microsoft's own history. Microsoft has long focused on backwards compatibility for Windows, ensuring it can run on older hardware. This means that consumers could expect to be able to run the latest version of Windows for at least a dozen years and maybe more. If you bought a PC with Windows 7 pre installed in 2010, you were able to upgrade it to Windows 8 in 2012 and then Windows 10 in 2015, and many of those devices can still run Windows 10 in 2025 during the Windows 11 launch and in subsequent announcements, Microsoft argued that the hardware requirements would boost the cybersecurity of Windows machines. Microsoft claims that quote, Windows 11 is the most secure operating system we've ever built, unquote and noted that a 2024 report commissioned by Microsoft showed that new Windows 11 PCs have seen 62% drop in security incidents and a three times reported reduction in firmware attacks. This is laudable except there are still a large number of Windows 10 users and a large number of existing machines that are physically unable to be upgraded to Windows 11 because of the hardware based security features. As of August. As of August, 46.2% of people worldwide are still using Windows 10, which is about 646.8 million people, based on Microsoft's own estimates of 1.4 billion people using Windows as an operating system. There are also an estimated 200 million to 400 million PCs worldwide that cannot be upgraded to Windows 11. This is an incredibly high number of of stranded Windows 10 machines. Microsoft in its own blog post warns that quote, while these devices will continue to function, they will no longer receive regular security updates, making them more vulnerable to cyber threats such as malware and viruses. Arguing that Windows 11 is an essential upgrade to boost cybersecurity while also leaving hundreds of millions of machines more vulnerable to cyber attacks is hypocritical, especially while charging consumers $30 for a mere one year extension to preserve their machine security. Microsoft has touted a free support option for consumers. But to obtain that support, consumers must choose to use Microsoft products such as Bing Search or or Xbox Gaming to earn the 1000 Microsoft Rewards points necessary to access that free support. Tying free support to unrelated Microsoft products forces consumers to jump through unnecessary hoops just so Microsoft can eke out a bit of market share over competitors. Consumer Reports asks Microsoft to extend security updates for free to all users who are unable to update their machine, while also working to entice more people to get off Windows 10 when more consumers upgrade to Windows 11 through software updates or because they have now purchased a new machine capable of running the software. We also ask that Microsoft create a partnership to provide recycling of those machines to consumers abandoning their hardware. For the last quarter century, Microsoft has been upfront about the 10 year life cycle of its operating systems, but it made the move from Windows 10 to Windows 11. But. Sorry, but as it made the move from from Windows 10 to Windows 11, it broke the backward compatibility that so many consumers have depended upon as they shopped for their computers. When Microsoft announced in late 2021 that it would require specific hardware components that hundreds of millions of PCs on the market would not have. It left consumers who had recently made a purchase of of incompatible hardware behind Consumer Reports calls on Microsoft to extend Support for Windows 10 to allow those consumers to catch up. Sincerely, Stacy Higginbotham Policy Fellow, Consumer Reports.
- [23:28]
Leo Laporte
Let'S also give credit to the second guy because I never do and poor guy Justin Brookman, who's director of Technology policy at Consumer Reports, also signed the.
- [23:37]
Steve Gibson
Letter letter and one would think that maybe Justin hired Stacy. So we certainly want to give him props for that too.
- [23:44]
Leo Laporte
Yeah, and I Stacey and I have been corresponding. She thanked us for our coverage of the letter and I said, well, you know, we talked about a little bit on Windows Weekly, and Paul was a little defensive of Microsoft saying, well, you know, they nobody bought those computers in the last few years, but I don't know. Stacy says, no, there are quite a few that were sold in the last last three years that are not compatible and I think this seems only fair to have to demand that Microsoft support this. They're doing, as you've pointed out, they're writing these fixes. It's not like they have to do any extra work. They're writing them anyway.
- [24:21]
Steve Gibson
They only have to stop preventing them from flowing easier because they've been flowing all along. And so they just but. So okay, so everyone knows that Microsoft's claims that Windows 11 runs better on existing hardware than Windows 10 implicitly means that Windows 11 does not truly require newer, faster and better hardware. We all also know that all of that nonsense about TPM 1.2 versus 2.0 is just that nonsense. Many years ago, when this first arose, we spent a podcast in detail examining the differences between the two. While 2.0 contains the advances we would expect to have made over time, those are evolutionary, not revolutionary, and they are not needed for the delivery of of the security guarantees provided by TPM 1.2. And Microsoft knows that. I thought that one point Stacy made was particularly important. Microsoft is once again claiming that Windows 10 is their most secure operating system ever. Well, as we learned from Windows xp, of which they made the same claim later, proven to be laughable. Only time can judge the security of any system. But if Windows 10 is more secure, and if Microsoft cares about the security of their users, then user security will be severely compromised by Microsoft's plan to allow Windows 10 security updates to lapse, thus leaving those many hundreds of millions of win 10 machines unprotected versus either continuing to offer those machines security updates or allowing those older machines to Update to Windows 11, which they could do if it weren't for Microsoft's artificial limitations. In any event. Stacy, bravo. Thank you for using Consumer Reports. Well deserved reputation for this good cause. You know, we've watched as Microsoft's previous decisions on this matter have, have shifted over time. So I'd say it's reasonable to hope they might simply allow all Windows 10 machines to continue receiving security updates for the next three years. All they need to do is not flip that cutoff switch in Redmond and that'll keep happening.
- [27:09]
Leo Laporte
I suspect they're going to cave and they are going to do that. It seems like the writing's on the wall. They've made it bit by bit easier and easier to get it for free. Free, as Stacy points out, I think.
- [27:22]
Steve Gibson
And I did see in the, in this coverage reference to, although I didn't pursue them, many other publications saying, you know, echoing what Stacy here in Consumer Reports has said. So there seems to be a groundswell as this date approaches. It's like, like why? What?
- [27:42]
Leo Laporte
Well, it sells more computers. Don't. You know. But I think now in this day and age, we should really be thinking about waste. Perfectly good hardware should not be cast on the landfill just because Microsoft wants to sell more products. That's just not, I mean, Apple does the same thing. Everybody does the same thing. And we need to rethink that whole strategy, I think.
- [28:03]
Steve Gibson
Well, you know, and it's easy too, because you talk about, oh, just go get a new computer. Well, all my stuff is on my old computer. And it's not like Microsoft ever figured out how to, how to allow us to seamlessly and smoothly move to a new machine. You have to start over.
- [28:23]
Leo Laporte
Well, you and I buy lots of hardware, so you know, we're, we're. But it's not reasonable to ask people to buy, to replace perfectly good hardware. Right. Just because we've decided we want to make sure that Everybody's on Windows 11 now, that's just not reasonable. Why throw out hardware that works perfectly well?
- [28:44]
Steve Gibson
Yep.
- [28:44]
Leo Laporte
For Microsoft's economic benefit.
- [28:46]
Steve Gibson
And again, if they say Windows 11 is faster than 10, well then it's going to be faster on the old hardware.
- [28:52]
Leo Laporte
Right. Paul's point, and I'll defend it in his absence, is that newer versions of Windows 11 have started to take advantage of features in TPM 2.0 and in the subsequent processors from intel so that they wanted people to move to this new hardware so they could start to take advantage of these new hardwares to make a better version of Windows and you know, okay, fine, okay.
- [29:20]
Steve Gibson
And the response is, if it's there, use it. If it's not there, don't. In which case the operating system you're using is taking advantage of whatever hardware you have. If you've got 2.0, use it. If you don't, don't use it. The other argument, hardware doesn't support it.
- [29:38]
Leo Laporte
The other argument is it's better if everybody's on the same version of the operating system. Right. It's easier for developers, it's easier for Microsoft, it's easier for hardware manufacturers. Of course, one solution to that is not to put out Windows 11, but just to stick with Windows 10.
- [29:55]
Steve Gibson
But all right, and it is the same operating system, they put a different candy coating the chewy inside, you know, and, and you run across it. You, you, you, you, you drill in past a couple of the new Windows 11 looking screens and you're looking at a Windows 7 dialog box that hasn't changed.
- [30:20]
Leo Laporte
Why would you want the start menu in the left corner when you can.
- [30:22]
Steve Gibson
Have it in the middle, Steve? And lose the choice? Yes, exactly why I'm with you.
- [30:29]
Leo Laporte
And I do hope, and I suspect this will happen. Microsoft will just relent and say, okay, okay, three more years or at least one.
- [30:37]
Steve Gibson
And they could also content themsel in the knowledge that they no doubt did push many people right into Windows 11 and into buying new hardware. So they came right up to the limit. Everybody who was going to do it did.
- [30:53]
Leo Laporte
Right, good point.
- [30:54]
Steve Gibson
And then they said okay, just one.
- [30:57]
Leo Laporte
Just kidding. Yeah, and I also really often overlooked. Part of that letter is Microsoft should start supporting some recycling efforts to start supporting a way to make these obsolete computers either useful or recycled or somehow responsibly disposed of. That I agree is also part of their responsibility. Yeah. Anyway, thank you for giving the highlighting that I agree with you 100%. And I agree with Stacy. And I thanked her, I thanked her personally for writing it. Yep.
- [31:27]
Steve Gibson
So the favorite targeting phrase of those who wish to trim the operating costs of the United States government is the well known waste, fraud and abuse. Last Wednesday, the usgao, you know, the government accountability office published a report detailing the size and scope of the u. S. Department of defense cyberspace operations. And it's breathtaking. While the report does not address fraud or abuse and there's no allegation from them or from me. Oh, it's about as diplomatic as it could be on the waste front because there sure does appear to be a ton of cyber waste. The summary in the report's subheading reads about 500 organizations have roles with some potential overlap. Now saying some potential overlap is like when our OS vendors say, well, this vulnerability could have been exploited, you know, while people are bleeding from the exploitation of the vulnerability. So 500 cyber related organizations have sprung up within the DoD and that doesn't count the 9,500 outside contractors who are also employed. The report said that, quote, according to data provided by government of, by Department of defense, you know, DoD components, DoD has established organizations that contain about 61,000 military and civilian personnel and over 9,500 contractors to contact to conduct cyberspace operations. So there is 61,000 people doing something about cyberspace at the DOD. You know, we've been wondering, Leo, like, are we actually doing anything or are we just getting lots of attacks aimed at us and not giving back? Maybe this is cyber defense and not cyber war. We don't know. But you know, and with all of those people, I have no idea how anyone would even begin to unwind that if you wanted to. But of course, before anything could happen, the will to do so needs to be present. So far, the U.S. department of Defense has remained pretty much unscathed and untouched by the broad and sweeping cost and personnel cutting measures that mark the beginning of our current administration. However, the DoD's reaction to this report's recommendations were positive, even though those recommendations were quite modest. Under, in, in this report, the, the, the GAO's report. Under the recommendation, the report concluded, GAO is recommending that DoD assess whether one, similar cyberspace training courses provided by the services could be consolidated and two, there are opportunities to increase mission effectiveness and cost savings by consolidating DoD cybersecurity service providers. DoD concurred with both recommendations and identified actions it will take to implement them. So mostly I think it's just redundancy that is, you know, and, and there's always the problem that, that having a budget is a, is a, is a mark of having power. And so everyone wants their own training group, they don't want to borrow somebody else's. And so one of the things that, that, that the GAO identified was that there's just crazy redundancy of training where training arguably is something where you could say, well, let's get, you know, four or five of these different divisions together and train them all at once instead of having five separate training sub organizations within each organization. And I did elsewhere, see, I didn't put it in the show notes, but there was some efforts being made to streamline DoD's cyber hiring practices saying that they were, get this currently 22, 000 people short of the number of cyber employee, cyber war, cyberspace related jobs that they were trying to fill. So they currently have 61,000. They're not reducing size, they're looking for 22, 000 more people. So anyway, this would be enough. I mean I know that the Department of Defense and the Pentagon has a special place in this country's budgeting, but at some point someone needs to take a look at this and say, wow, there's, you know, there, there seems to be a lot of overlap of, of responsibility and job within this, you know, cyberspace aspect of the, of what the Pentagon is doing. Consolidating that training and the service providers would save the country, presumably a lot. Leo, we're half an hour in, let's take a break and then we're going to look at what's been found about Deep Seek and why. Depending upon who you are, the quality of your answers varies.
- [37:12]
Leo Laporte
I thought this was a fascinating story. Yes sir. Let us pause. This is the pause that refreshes for Steve, but the pause that informs for you as we talk about our sponsor of this segment of security. Now, those great folks at Acronis, and you know the name I know, and the Acronis Threat Research Unit, I don't think I need to tell you you deserve fewer headaches in your life. You even something as simple these days as watching TV could be a headache. Where your favorite shows are scattered across different streaming services, it's nearly impossible to find one place that has everything you need. Well now in security that might not be true. Acronis takes the headache out of cybersecurity with a natively integrated platform that offers comprehensive cyber protection in a single console. And if you want to know what's happening in cybersecurity security, the Acronis Threat research unit, the TRU is the place to go. It's your one stop source for cybersecurity research. TRU also helps MSPs stop threats before they could damage you or your clients organizations. I know we have a lot of MSPs listening. We love our MSPs. You will love the TRU, the Acronis Threat Research Unit. It's a dedicated unit composed of experienced cybersecurity experts. Imagine having a team of Steve Gibsons, including cross functional experts in cybersecurity, AI and threat intelligence. The TRU conducts in deep intelligence driven research into emerging cyber threats, proactively manages cyber risks and responds to incidents. They will help you. They can provide you with Security best practices to assist IT teams in building robust security frameworks. They also offer those fantastic threat intelligence reports. You can get custom security recommendations tuned just for your needs and educational workshops. So whether you're an MSP looking to protect your clients or you need to safeguard data in your own organization, Acronis has what you need. It's all there in Acronis Cyber Protect Cloud. You get edr, xdr, remote monitoring and Management, you get managed detection and Response, you get email security, Microsoft 365 security, even security awareness training. And it's all available in a single platform with a single point of control for everything. So it's very easy to deploy and manage. Look, if managing cybersecurity has given you a headache, it's time to check out Acronis. Know what's going on in the cybersecurity world by visiting go.acronis.com twit and take the headache out of cybersecurity. That's go acronis.com twit we thank him so much for supporting Steve and the work he does here at Security. Now let's talk Deep Seek.
- [40:08]
Steve Gibson
So in a report that's both sad and predictable, the Washington Post story headline was AI Firm Deep Seek Writes Less Secure Code for Groups China Disfavors. And they had the subhead, Research by a US Security firm points to the country's leading player in AI providing higher quality results for some purposes than others. A summary of the Washington Post story says the Chinese artificial intelligence engine Deep Seq often refuses to help programmers or or gives them code with major security flaws when they say they're working for the banned spiritual movement Falun Gong or others considered sensitive by the Chinese government. New research shows and some commentary about the coverage wrote, quote, the Deep Seq AI engine returns code with security flaws if it determines that the coder is associated with a specific minority group. According to the Washington Post, programmers from Tibet and Taiwan received code of lower quality. Deep Seek also flatly refused requests if queries hinted that the code could be used by the Islamic State or the Falun Gong movement.
- [41:36]
Leo Laporte
I'm not surprised, actually.
- [41:39]
Steve Gibson
I mean, no. As I said, like in a report that's both sad and predictable. It's like sad but, you know. Yes. Not surprising. So, wow. I guess, you know, I guess a lot of people are, are running the Deep Seek models locally, so where they have control over what's going on, but you have to be careful how it's trained. Wow.
- [42:04]
Leo Laporte
Yeah. Yeah.
- [42:07]
Steve Gibson
Version three of the Web assembly specification is now officially live Although our two favorite browsers, Chromium based Chrome and other Chromium browsers and Firefox have already been incrementally incorporating its new features as they have become formalized. That is the the web, the various components of Web of the WebAssembly 3.0 have been formalized. What's interesting is that the lone browser out there is Apple Safari. It's the laggard and I have no idea why, but it has become a trend for Safari because it's been consistently lagging behind most of the new standards as they've been evolving for years.
- [42:59]
Leo Laporte
I've always wondered what you thought about Webassembly, you know, an assembly language programmer. It's not assembly language language though, right?
- [43:06]
Steve Gibson
No, no, no, no, no. I took a look at it actually. It's a stack based architecture so you know, reminiscent of fourth. So it's very efficient from that standpoint. It has a procedural structure where procedures can pass arguments and also return results. It's also got traditional high level control flow primitives so if then else and case statements and so forth, forth. And I would love to have some reason to need it, but I can't think of one. It's only real perform, it's only real performance advantage comes from processor intensive things, you know, such as mining cryptocurrency in a browser. If I were ever to use a web browser as a front end for some headless code, I'm certain that the heavy computational lifting would be done by me in native intel assembly language and the browser would just be for like pure user interface. And if you were just using the browser as a UI then regular JavaScript would be just as fast and boy far more maintainable. Unfortunately, although they're very cool stack oriented languages and as I said fourth being the most famous, they make for very efficient intermediate languages. Java's VM is an example and Microsoft's NET CLR their common language runtime. They're all good examples of stack based intermediate languages. So they're great for a compiler to compile to and then they run very well. But they are not fun to write in like natively and, and as you know Leo, they are nearly impossible to read. I've looked at some fourth code that.
- [45:09]
Leo Laporte
I've written but it's not, I was.
- [45:12]
Steve Gibson
No, I was so happy with, with it when I wrote it it's like oh this is so clever. And I looked at it a month later I thought what the heck is this? I mean you can't, it's like it's Impossible to read stack oriented code that anyone has written. And the good news is you normally don't have to because a compiler wrote it for you when you gave the compiler something really nice looking and very legible.
- [45:41]
Leo Laporte
That's my sense of. Most webassembly is almost like a P machine. It's an intermediate and usually people are using some other language to write to it.
- [45:50]
Steve Gibson
And I, I made the comment a couple weeks ago on the podcast that, that this notion of web SEM being useful for, for compute in, you know, intense jobs. You know, it's an interesting idea for users browsers to be mining cryptocurrency on behalf of the sites they're visiting. And as a means of paying the site for their visit instead of being assaulted by ads which the sites are getting payment for, how about let the a browser that is on a site be mining currency on behalf of that site? That's, I mean I hate it. From a global.
- [46:33]
Leo Laporte
That's kind of what Brave, I think does, right? Brave has a bravest.
- [46:37]
Steve Gibson
There actually is a proof of work work technology that, that yes that Brave has been exploring.
- [46:45]
Leo Laporte
So there are 40 according to Wikipedia, 40 different high, high level languages that support web assembly as a target. So you can write in C or Rust or Python or Pascal or Julia or whatever.
- [46:58]
Steve Gibson
And that's cool because then, then you get platform independence and you've get, you have code running very efficiently on, on our web browsers. And you know, we've talked about it. Web browsers are becoming our operating system. I mean, you know, they're, they're important.
- [47:16]
Leo Laporte
Right. It's also a great way to obfuscate malicious code. But you know what isn't these days?
- [47:24]
Steve Gibson
And speaking of web browsers, one week ago Firefox moved from version 142 to, to 143. Remember Leo, when we were on version 11. Come a long way, baby. We all just, everyone's decided just to stop doing these like, okay, we're going to upgrade our browser as infrequently as possible and make each version as perfect as we can. And so we're going to go from like version 4 to well ie 6 of course was famous back back in the day and it wasn't that many days ago actually. Anyway, Firefox is now at 143. What's interesting is I have launched Firefox every single day since then. It was early last week, but it wasn't until I explicitly went over to Firefox's help about that I was offered version 143.0.1. So if you're interested, you may want to go do that because for whatever reason, Mozilla doesn't seem to be in a in any hurry to push this update out to its even its most loyal fans. This version 143 repaired a pair of sandbox escapes that had been found and reported in Firefox's 2D canvas rendering component. And there was one memory safety bug. Those were the were the only three high priority security improvements. The rest were moderate or low. And I don't believe that those were found exploited in the wild. They were just some guy. One guy found both of the 2D 2D canvas rendering problems and said hey, by the way, I, I found these and they said oh, that's not good, thank you very much. But they were, you know, they were not found by seeing them being exploited in order to, to hurt people probably. Also because Firefox isn't that big a deal anymore compared to Chrome. Chrome is the big target because that's what everyone's using on Windows. Firefox now supports running webs as of 143. The other features new new in 143. Firefox now supports running websites as web apps pinned directly to the taskbar. So you know, these are sites that you can pin and run sort of as, as simplified Windows, just like we were talking about like writing an app in a higher level language that compiles into webassembly and runs very nicely like an app for your operating system. And in this case now Firefox 143 and later you can stick it on your taskbar and just launch it. So oh, I should mention though that this does not work if you download Firefox through the Microsoft Store. This is only if you just get it yourself from Mozilla. Don't know why tabs Firefox tabs can now be pinned by dragging them to the start of the tab tab strip, which makes it easier to keep important sites within reach. And since I, I did that immediately, since I am generally holding a conversation with Chat GPT as, as my, my code development buddy, I I put the Chat GPT tab up at the top of my tabs. It locked in right there and now it's there. So I'm happy to have that copilot from Microsoft of course can now be chosen as a chatbot to use in the sidebar for quick access without needing to leave the main menu. Now it's unclear to me how many people who have deliberately chosen to use Firefox as their web browser rather than succumbing to Edge. You know, over and above all of Microsoft's clearly and repeatedly stated objections to use anything other than Edge. Yes, you have to work at using Firefox. Why they would choose to chat with Copilot over any of the other many alternatives is beyond me. But for what it's worth, you can now choose to use Copilot from the URL search bar if you want to. Also, when a site asks for camera access, the chosen camera can now be previewed, sort of in vitro, inside the permission dialog, which allows you, if you've got multiple cameras, to choose the one that you're about to give the site permission to use. So that can come in handy if you've got multiple cameras. The Firefox address bar can now display important dates and events okay, Mozilla elaborated that this gripping new feature supports displaying events like Mother's Day. Now, if it gave you adequate warning that Mother's Day was approaching, that might be useful.
- [52:35]
Leo Laporte
Don't tell me tomorrow, tell me next week, tell me next month. Yeah, yeah.
- [52:40]
Steve Gibson
So anyway, okay, I guess that's good, but I would rather have them spending time on privacy enforcing age verification. Wouldn't that be nice to have? But you know, think about that, Mozilla. I'd rather have that than, you know, yes, be told of important dates in the calendar. They also support Windows UI automation, so that that improves the support for access accessibility tools such as Windows Voice Access Text Cursor Indicator and Narrator. So that's good. And I said that I was going to say the best two for last, and here they are. Microsoft has expanded its fingerprinting protection by reporting constant values for several more attributes of its user's computer. That's nice. Our listeners know that I left Firefox for Brave when it turned out that Firefox really had done nothing there. And also when when downloading a file in the private browsing mode of Firefox, it's incognito mode. Firefox now asks whether to keep or delete anything you download while in that mode as the session is ending, and you can adjust that behavior whether you want it or not in Settings. I think that's a nice feature. The presumption being that if you're in that mode, then just as you do not wish to have your browser permanently recording where you go and what you do and the cookies that you receive, you know you'll definitely be receiving cookies. You may also not want anything you might download to persist, but you Might forget that. So this is a nice little feature of that and I suppose it's not bad that Firefox expanded its printing protection by reporting constant values for several more attributes. But I checked it still did not Present Prevent the EFF's new cover your tracks site that we've talked about before from locking on to my updated browser now running version 143 and reporting that its fingerprint was unique. It had never seen anybody else with that fingerprint. So okay, Microsoft or I use a.
- [55:05]
Leo Laporte
Firefox spin off called Zen that does have unique fingerprint protection.
- [55:12]
Steve Gibson
Nice.
- [55:13]
Leo Laporte
So nice.
- [55:15]
Steve Gibson
Wait, no.
- [55:15]
Leo Laporte
Unique fingerprint means you're trying test indicates you have strong protection against web track but it has a unique fingerprint. That's not good, right?
- [55:23]
Steve Gibson
That's not good. And if you use Brave you don't get a unique fingerprint.
- [55:27]
Leo Laporte
You look like Safari does either. Yeah yeah. Oddly enough given how at a time at a touch Safari seems to be.
- [55:34]
Steve Gibson
In other well but app you know Apple privacy on you know some some things I have a bit of feedback that where I from one of our listeners where we'll be getting to where I spend a little more time than I did last week addressing the Apple's insistence on not having their iOS compromised and because I mean I have a deeper appreciation for just how much they went how much this appears to matter to somebody there. Anyway we will get to that. One last piece of news on the Firefox front is that last week's Firefox for Android which is now available offers its own native DoH, you know DNS over HTTPs for resolving domain names into IP addresses which of course uses an authenticated and encrypted TLS connection and using the HTTP protocol on a TLS connection and okay, that's good. I installed Firefox on my, on my Samsung phone, my, my, my Android phone just because I wanted to see what it looked like. And sure it's you can do that. It's there now but it's not such a huge deal because native dot DNS resolution so that's DNS over TLS that was added to Android natively seven years ago in 2018. So Androids had that for seven years and then with the, and that was with the Release of Android 9. Remember the the, the Pie edition Pie and then native DoH resolution was added two years later to Android in 2020 with Android 11. So even without Firefox or any other browser running on Android adding its own native DOH or for that matter dot support all of the browser's lookups would have already been securely encrypted using Android's native DNS for the past seven years since 2018. Yes, it's nice to have it as an alternative. Maybe something prevents you from turning on Android's native. I don't know what that would be, but if that was the case, then Firefox is bringing DOH encryption for DNS lookups natively itself, so I guess that's good too. But you know, again, not that big a deal. The registers headline Last Friday they couldn't resist one token to pwn them all was the headline they said Entra ID bug could have granted access to every tenant. Okay, that means any SharePoint Online or Exchange Online account was vulnerable to this until Microsoft fixed it. That includes access to other resources hosted in Azure. In other words, this bug would pretty much be as bad as it could get. Okay, before I go any further, I'm going to share what the Register reported. They said a security researcher claims, and it's confirmed, to have found a flaw that could have handed him the keys to almost every Entra ID tenant worldwide. Dirk Jan Mulema reported the finding to the Microsoft Security Research center in July. The issue was fixed and confirmed as mitigated and a CVE was raised on September 4. It was an alarming vulnerability involving flawed token validation that can result in cross tenant access, molima wrote. Quote, if you are an Entra ID admin, that means complete access to your tenant, that is by anybody else while this bug was in place, they wrote. There are two main elements to the vulnerability. The first, according to Malema, is undocumented impersonation tokens called actor tokens that Microsoft uses for service to service communication. There was a flaw in the legacy Azure Active Directory Graph API that did not properly validate the originating tenant, allowing the tokens to be used for cross tenant access. Malema wrote. Effectively this means that with a token I requested in my lab tenant I could authenticate as any user, including Global admins in any other tenant.
- [60:48]
Leo Laporte
That's not good.
- [60:49]
Steve Gibson
Oh Leo. I mean it's no authentication. It is a complete authentication bypass.
- [60:57]
Leo Laporte
Not where do you want to go today?
- [60:58]
Steve Gibson
Who do you want to be today for Entra id? Yes. I mean it is horrific. They wrote the tokens allowed full access to the Azure AD Active Directory Graph API in any tenant. Any hope that a log might save the day was also dashed because requesting an actor token does not generate a log, and even if it did, they would be generated in the attacker's tenant instead of in the victim's tenant, which means that no record of the existence of these tokens is made or retained. The upshot of the flaw was a compromise of eight any service that uses Entra ID for authentication, such as SharePoint Online or Exchange Online. Malima noted that access to resources hosted in Azure was also possible. Microsoft's swiftness in resolving the issue is to be commended, even if it's unfortunate that it was present in the first place, they wrote. Malima also noted that Microsoft had not detected any, any abuse of the vulnerability with its internal telemetry. But then we don't know whether it would have. In any event, Malema said this this is, quote, the most impactful vulnerability I will probably ever find. Yeah, you or anybody else. I mean, this is unbelievable, they said, and it's difficult to dispute the claim. The CVE for the issue rates it as critical. Uhhuh. With a low attack complexity metric and a CVSS score, you guessed it, of 10.0. To reiterate, according to Microsoft, the vulnerability has been fully mitigated and users do not need to take any further action. Still, before the vulnerability was found, they wrote, there existed, in Malema's words, one token to rule them all. Now, what I question every time we encounter something like this that could have truly wreaked havoc upon the world, I mean this, absolutely this would have been unbelievably destructive, is whether those who would do us harm already knew about it and were thus quite upset by, by its chance discovery by immoral security researcher and then by its unilateral removal from their secret arsenal. Did somebody know and they were just waiting? The other question that naturally occurs is if this was just found, what else is still lurking out there that bad guys may have found and are hoping the good guys don't stumble upon? I would feel much more comfortable knowing that there was some chance that all of the big bad problems were being found and might eventually all be discovered. That's what we want, right? I mean, if we accept the fact that yes, all software that's of sufficient complexity is going to have problems, then okay. But we have a process. With all of these security researchers and all of these different groups pounding on our software, they're finding problems. But the reason that's unlikely, that they're going to eventually find them all, is that Microsoft refuses to ever leave anything alone and they apparently introduce new problems and at the same rate as they and others are finding and removing them. Right. We don't see it like drying up over in, in Windows land. You know, we've got, we got Apple exploiters who have thrown in the towel and given up because those, they're just too hard to find now. They don't try anymore. But wow, you know, how many hundred flaws will Microsoft patch next month is the question. So you know, what we don't know, and we never will know, is whether this particular flaw, as just an example, existed from the start. Was it always in there? Or did it get introduced sometime later when someone came along and changed some things around without having a full understanding of the consequences, where the original developer is off on some other project or maybe is just on an island somewhere because he's got stock options and they knew what not to do. But this other guy came along and said, oh, let's glue these things together and like, what could possibly go wrong? And a new flaw was born. And in this case something that was devastating. We'll never know. But we do know Microsoft just can't stop messing with this stuff. It's like, oh, new feature, new feature, new feature. Meanwhile, wow, the consequences of a, of a breach really, you know, escalate. Last Wednesday, Chrome was quickly updated and boy, I'm impressed with this. When I say quickly, you'll see what I mean. To end the abuse of a critical type confusion bug in the v8 JavaScript and web assembly engine, Chrome in the stable channel was updated to 14007339185 for Windows and Linux and 186 for Mac. Now this update seems worthwhile to obtain since it fixed four different vulnerabilities, every one of them designated as high. There was the CVE 2025105 85. That's the one that's this type confusion in V8 it was discovered and reported by Google's tag team. You know, that's their threat analysis group. Get this on the day before, on the 16th and this patch, this zero day was fixed and, and, and Chrome was updated and made available the next day on the 17th. So Google wasted no time getting Chrome updated to fix that one. Also, the CVE 15 is a use after free flaw which earned its reporter the the researcher who reported it $15,000 in Bug Bounty. 501 was a use after free in the WebRTC system. Its discoverer took $10,000 home and then the reward for one for the fourth one is 502. That's a heap buffer overflow in angle and that the, the, the bounty for that was tbd, you know, to be determined. So that reward had not yet been set it's interesting that the other bugs had been known by Google for as many as six or seven weeks. I checked the original reporting date and six or seven weeks before this, but despite all of them having similar ratings high severity, it wasn't until the reporting of that Type confusion in V8 and WebAssembly, which their own tag team reported discovering due to its active exploitation, that Google essentially instantaneously fixed it and pushed out the Chrome update, which also incidentally fixed those three others that Google already knew about, apparently had already fixed, but just didn't feel were worth bothering to push out to, to the world because nobody was known to be exploiting them. I would imagine they may have even been watching them to see if, if they were going to be exploited, but figuring, eh, you know, we'll wait till something more worthwhile comes along. And boy did it. The moment it did, they fixed it and pushed out an update to Chrome. So you know, that's the way you want a company like Google to operate. And Leo, the way we want our DRAM to, to operate is not the way it is. Oh, we're going to take a break and we're going to look at these still vulnerable DDR5. Bad dram. Bad, bad dram.
- [69:59]
Leo Laporte
Bad, bad dram.
- [70:00]
Steve Gibson
And unfortunately inherently bad. This is a child that cannot be fixed.
- [70:06]
Leo Laporte
But we're all using it. Oh yeah. All right, we'll get to that in a moment. But first a word from our sponsor, Zscaler, the leader in cloud security. You know that AI is a double edged sword, right? You know, it's both good for your organization and it is the biggest threat out there right now to your organizations. Because see, hackers are using AI to attack you, right? At the same time, AI powers innovation. It drives efficiency not just for your business, but also for bad actors. They are now using AI to deliver more relentless and effective attacks. Phishing attacks, for example. We talked about this last week. Basically Steve said, forget, you know, trying to teach your employees not to click the link. They're, they're gonna, maybe it's only one time in a thousand, but they're gonna. That's why phishing attacks over encrypted channels increased last year by 34.1%. It's partly fueled by the growing use of generative AI tools, but there's also these phishing as a service kits. So how do we solve it? You know? And then on the other hand, organizations in every industry from small to large are leveraging AI. They're using it to great effect. They're Increasing employee productivity with public AI for engineers using coding assistance. Marketers are using AI as for writing as writing tools. Finance is creating spreadsheet formulas. You got AI in Excel. You can do pivot tables. I never even knew how. Right now the AI will do it for you. Automate workflows for operational efficiency across individuals and teams. They're embedding AI and applications and services that are both customer and partner facing. Ultimately, AI is helping businesses move faster in the market and gain competitive advantage. But companies really have to think about how they protect this private and public use of AI and at the same time how they defend against AI powered attacks. Well, there is a solution for both. Ask Jeff Simon. He is the senior Vice President and Chief security Officer at T mobile. He said, quote Zscaler's fundamental difference in the technologies and SaaS space is that it was built from the ground up to be very important. A zero trust network access solution which was the main outcome. We were looking to drive traditional firewalls. You know the perimeter defenses we've all used with then VPNs so you can get into work. And that gives you public facing IPs exposing your attack surface. These perimeter defenses are no match in the AI era. It's time for a more modern approach. And that Zscaler's comprehensive Zero Trust architecture +AI does two things. It ensures safe public AI productivity, protects the integrity of private AI. I guess it's three things. And stops AI powered attacks. You can thrive in the AI era with Zscaler Zero Trust +AI to stay ahead of the competition and remain resilient even as threats and risks evolve. Learn more@Zscaler.com Security that's Zscaler.com Security it's, it's really the solution. You can't assume that your employees aren't going to click links. You have to make it so that even if they do, you're protected. Zscaler.com Security okay, so Leo, while you.
- [73:39]
Steve Gibson
Were telling our listeners about that, I just happened to see my email pop up. Yeah, and this was from our listener, one of our listeners, Walt Lemberg. He wrote Steve. He said, Steve never received your current email. I checked the trash and other mailboxes. Am I still on your list? And I floated my you know I'm using EM client, which I still love. I floated my cursor over his name and it showed his email address at which came as no surprise to me. Gmail.com I wrote back, hey Walt, you'll find it in your spam folder. For some reason Gmail decided that this email was spam. And all of our mail to Gmail last night went into everyone's spam bucket. I sent myself one and it went to spam. So please mark it not spam to train Google. Thanks.
- [74:44]
Leo Laporte
Do you think it's because it had a YouTube link in it?
- [74:48]
Steve Gibson
That's the only. But it wasn't in the mail. It was in the PDF that was attached. But I, but you know, Google opens PDFs I imagine, and scans through them. That was the only thing that I could think was that, that it had a link to YouTube. But why would they care if you had a link to YouTube? I mean, it's a public YouTube, it's not like a, anything weird. And the, the, the only thing that I could think is that I did send it at 8:30 in the evening. Normally I'm sending in the afternoon, but I was just. This podcast took. I, I don't know, I mean, so I've noted that if I put too many question marks or exclamation points in the email, that's, that's bad. So I don't, I don't do that ever anymore. Now I learned that. But that wasn't Gmail that punished me. It was some other random SP spam, you know, thing that, that some people use.
- [75:41]
Leo Laporte
Anyway, we're gonna block you.
- [75:43]
Steve Gibson
Yeah, I wanted to tell our listeners, if you have a Gmail account, if you normally get email and you're thinking, hey, what happened to Steve's show notes? Look in your spam folder and if you would just take the moment to say this is not spam bad Gmail and you know, give it a discipline training.
- [76:03]
Leo Laporte
If enough people do that. Yes, spank it.
- [76:06]
Steve Gibson
It must, you know, maybe some people, you know, said that was spam and G and Google got annoyed. But you know, 18,865 pieces of email went out last night and, and a surprising percentage of our listeners are have, have Gmail accounts, so.
- [76:26]
Leo Laporte
Oh yeah, it's number one.
- [76:28]
Steve Gibson
Yeah, yeah.
- [76:29]
Leo Laporte
Do you attach the PDF or send people a link to a PDF?
- [76:34]
Steve Gibson
Just a link to it.
- [76:35]
Leo Laporte
Yeah, you're right.
- [76:36]
Steve Gibson
So it's not embedded.
- [76:37]
Leo Laporte
It's not looking at that either. Yeah, it may be though. A link to a PDF nowadays is considered spammy.
- [76:44]
Steve Gibson
Who knows all. Every piece of email though has had a link to the PDF.
- [76:49]
Leo Laporte
Right.
- [76:50]
Steve Gibson
And many of the people who have written to me, I've heard, I've heard since last night. Many of our listeners said, hey, just thought you'd know your email went to spam. For the first time ever. And it's like, okay, I don't know why, but it's not good. Because that's a But I I, I congratulate them on even do people like look in their spam folder all the time?
- [77:11]
Leo Laporte
Oh yeah. Oh constantly.
- [77:13]
Steve Gibson
Because of, because of false positives.
- [77:15]
Leo Laporte
Positives. I review my spam folder every few days and there's often something I want in there. It's, you know.
- [77:23]
Steve Gibson
Sigh Ah, what a mess. Okay, yeah, speaking of messes, we have a mess Last week Google Security posted the news, which should not surprise us all that much. Unfortunately, the latest DRAM remains vulnerable to Row Hammer attacks From the start the first time we heard about this, it was clear that Rowhammer attack susceptibility represented a fundamental and intrinsic vulnerability, because it was inherent in the fact that the push for insane levels of performance and memory density had forced the reduction of dynamic RAM noise margins and cell charge capacity down to the level that while yes, it generally works, it can now be made to fail if you're clever about how you go about doing that. So here's what we learned from Google last week. They said Rowhammer is a complex class of vulnerabilities across the industry. It's a hardware vulnerability in DRAM where repeatedly accessing a row of memory can cause bit flips in adjacent rows leading to data corruption. This can be exploited by attackers to gain unauthorized access to data, escalate privileges, or cause denial of service. Hardware vendors have deployed various mitigations such as ECC error correction code and TRR target row refresh for DDR5 memory to mitigate Row Hammer and enhance DRAM reliability. However, the resilience of those mitigations against sophisticated attackers remains an open question. To address this gap and help the ecosystem with deploying robust defenses, Google has supported academic research and developed test platform to analyze DDR5 memory. Our effort has led to the discovery of new attacks and a deeper understanding of Row Hammer on the current DRAM modules, helping to forge the way for further stronger mitigations. Okay, now I'm not going to spend a lot more time on this since we have deeply and thoroughly covered the multiple Row Hammer discoveries and sadly, the futile attempts to solve the problems. I have a link in the show notes to Google's full posting for anyone who might want, you know, a full update on the status of this. But I'm going to skip all that and get down to Google's lessons learned where at the end of this posting where they write we showed that current mitigations for rowhammer attacks are not sufficient and the issue remains a widespread problem across the industry. Okay, that's today. They said these. They. They said those mitigations do make it more difficult but not impossible to carry out attacks, since an attacker needs an in depth understanding of the specific memory subsystem architecture they wish to target. Current mitigations based on TRR NECC rely on probabilistic countermeasures that have insufficient entropy. Once an analyst understands how TRR operates, they can craft specific memory access patterns to bypass it. Furthermore, current ECC schemes were not designed to as a security measure and are therefore incapable of reliably detecting errors. Right. ECC is meant for catching memory failure, not deliberate malice, they said. Memory encryption is an alternative countermeasure for Row Hammer. However, our current assessment is that without cryptographic integrity, it it offers no valuable defense against Rohamm. More research is needed to develop viable, practical encryption and integrity solutions. Google has been a leader in JDEC standardization efforts. For instance, with PRAC pr, a fully approved standard to be supported in upcoming versions of DDR5 and low power DDR6. It works by accurately counting the number of times a DRAM word line is activated and alerts the system if an excessive number of activations is detected. This close coordination between the DRAM and the system gives PRAC a reliable way to address request rowhammer, which is how they end. Okay, now PRAC P R A C stands for per row activation counting. And if you're ever in need of a quick example for which the word cluge was coined, you Lee, you. You need look no further. It's too bad that the word desperation has too many letters to serve as the abbreviation for some means of solving this problem, since desperation is what it's come down to. If your solution is to add hardware counters into your DRAM memories, Word line activations as a means of detecting when someone may be yanking your line with malicious intent. What a mess. But for what it's worth, props go to the original researchers at Carnegie mellon university who 11 years ago, and we covered it at the time back in 2014, discovered the presence of this nightmare lurking in the design, the inherent fundamental operation of dram and brought it to the world's attention. You know, that's the kind of research we need. Unfortunately, there seems to be no way to back out of DRAM's density. I mean, everybody now needs, you know, 128 gigabytes of of DRAM and more. And the reason Google is funding the research is they've got big data centers and they've got lots of this DRAM and, and they're running other people's code on their servers and they don't want to have people busting out of their virtualization boxes and roaming around within Google. So I mean this is a serious problem and we don't have a solution for it yet, you know. And what's DRAM going to do if it, if it signals that somebody is as making excessive accesses? First of all, that will tend to false positive. Right. There could be use cases where, where it's going to raise an alarm where there's no malicious activity. What's it going to do? Abort the process? What else could it do? Or maybe start refreshing all the adjacent rows around that, that area. Anyway, it's as I said, Kluge is, is what this is and what a mess because of a fundamental problem that we don't have a solution for. It's DRAM is noise immunity is too low and it's been forced down by this craven quest for ever more dense memory in order to satisfy the oh look, we're able to do it capabilities. Wow. I've always found it interesting and certainly depressing that science fiction, when depicting a futuristic dystopia, invariably shows it filled beyond brimming with monstrous bright and flashing animated holographic 3D advertisements. Right.
- [86:14]
Leo Laporte
Blame Philip K. Dick. I think he was the first to describe that world, wasn't it?
- [86:18]
Steve Gibson
And every, yes, you're right. If like the Blade, Blade Runner was, was just crazy with that and then the, the, the, the fifth element, we, we saw the same thing.
- [86:33]
Leo Laporte
Yeah, basically.
- [86:35]
Steve Gibson
Basically that's like become a meme, you know, it's always way beyond garish. And, and those scenes show us the presumed consequences of commercial consumerism. You know, without any boundaries, where he who shouts the loudest attracts the most customers. Well, anyone who has seen some of that sci fi might have wondered whether the manufacturer of a residential kitchen refrigerator, which touted its overly large touchscreen as a feature, might ever succumb to their baser instincts, finding themselves the manufacturer, unable to resist the temptation to make just a few more after sale dollars by assaulting the owners of those refrigerators, many of whom had purchased the those connected cold storage boxes for as much as $2,000 with a series of unsolicited product advertisements on their devices screens. If you answered yes, of course they would, sadly you would be correct. Samsung has begun displaying unsolicited advertisements on the screens of its large format display refrigerators. They do not give users the option of Declining. So I suppose you could remove the device from the Internet, but then you wouldn't get the weather forecasts and the recipe of the day and all the other random crap that apparently purchasers of these Samsung connected refrigerators think is a good thing to have on the, on the screen of, of the door of their refrigerator. Now you're also going to get ads. So that's the way it is in 2020, I think.
- [88:36]
Leo Laporte
Philip K. Dick also described a time in the future where every appliance you have, you have to watch an ad before you can use it, including, including your door.
- [88:48]
Steve Gibson
We're going.
- [88:49]
Leo Laporte
We're headed that way. We are.
- [88:50]
Steve Gibson
We are, Leo. We are. There's no question.
- [88:54]
Leo Laporte
I have a friend who has an older Samsung with a built in browser and she can't use the browser anymore because it's out of date and Samsung doesn't update it. So it's insecure. So it's. Not only is it showing ads, the browser is useless too. The whole thing.
- [89:10]
Steve Gibson
Yep. I ran across that a couple weeks ago and I forgot to mention it on the show. That's right. That's like the browser is behind the times.
- [89:19]
Leo Laporte
It's like they put IE6 in it. Oh my God. Late stage capitalism. Welcome.
- [89:30]
Steve Gibson
Yep. China is now banning Nvidia chips. It's somewhat difficult to keep up with the daily back and forth of current import and export policy. Right. Because I mean, it literally changes by the minute.
- [89:46]
Leo Laporte
Yes.
- [89:47]
Steve Gibson
The last I heard was that Nvidia had scored a huge win with China after Nvidia's CEO Jensen Huang reported a very productive Oval Office meeting with Donald Trump. But as I said, it's been difficult to stay current. The latest news is that China's government has now told their companies to stop purchasing Nvidia chips. According to the Financial Times, companies were told to stop testing and to cancel any orders that they may have now and for the future. The move is reportedly part of Beijing's efforts to boost the local semiconductor sector and cut its dependence upon US suppliers such as Nvidia. Also, Chinese officials of.
- [90:40]
Leo Laporte
You can't blame him.
- [90:41]
Steve Gibson
Yeah, no. And Chinese officials again accused the US of attempting to sneak back doors into Nvidia chips. Of course, we previously covered and shared Jensen's very clear and adamant statement that it would never under any circumstances compromise the integrity of its chips with secret back doors. And remember that in that statement he reminded the world where a disaster the Clipper chip had been, where basically exactly that was done, and said we're never going to do that. But again, we're seeing the rise of nationalism in general. Certainly we're doing it, so they're doing it too. I'm sure that I hardly need to caution any of our listeners about the dangers inherent in the use of packaged libraries found on open and open source software repositories such as npm. We've been talking about these supply chain attacks constantly. But I just wanted to say that last week 300 more malicious npm packages were found and taken down. So please be careful, please.
- [91:58]
Leo Laporte
Yeah. You know, it's funny because I was talking about the story on Twitter on Sunday and I, I mentioned the earlier NPM hack which we had talked about a couple of weeks ago. I didn't realize this is a whole new one. Same problem, right? That these, that these node packages are automatically downloaded all the time. Billions of downloads a week.
- [92:22]
Steve Gibson
Yes. And so they're being sucked up and incorporated into other systems without your knowledge.
- [92:28]
Leo Laporte
Without the developer's knowledge. It's terrible. It's a mess. Just a mess.
- [92:32]
Steve Gibson
It is, it is. I mean, it's a system that we evolved. If everybody was operating good, even if everybody was operating good in good faith, well, you, you, you, you would tend to be pulling in bugs that were not yours.
- [92:47]
Leo Laporte
Right.
- [92:47]
Steve Gibson
And then you would need to find them. But here it's way worse than that. You know, it's deliberate malice and all these packages are being pumped onto NPM and with the hope that they're going to get incorporated and, and end up propagating out into the world.
- [93:04]
Leo Laporte
So the first one we talked about was relatively benign. I just put some bitcoin mining software on machines. This one's a worm, Shai Halud, which is of course the Dune sand worm. And I think it spreads itself. You know, it's. This thing is much more malicious.
- [93:21]
Steve Gibson
Yeah.
- [93:22]
Leo Laporte
I don't know what the solution is. This is just.
- [93:25]
Steve Gibson
No, and I mean we have built a dependency on dependencies. Yeah, right. I mean these are inter packaged dependencies.
- [93:34]
Leo Laporte
Right.
- [93:34]
Steve Gibson
And we're now dependent upon the system of, that uses dependencies in order to pull everything together. You know, we, I don't know how we unwind this.
- [93:46]
Leo Laporte
Yeah, well, I'm sure people are working on it. I hope they are.
- [93:52]
Steve Gibson
Greg James wrote saying, Steve, I was reviewing your observations regarding Post support Windows 10 updates and zero patch, reading the fine print of their FAQs, they state, quote, in case the subscription is terminated without renewal or the trial expires without purchase, all micro patches on computers associated with the subscription get unapplied until a new. Until a New subscription is established for these computers. Oh yes, and he gave me a link to that and he said from my perspective, this is a fine example of holding us hostage. Also, their annual subscription for the Pro version required to get Microsoft security patches beyond the the zero day that zero patch provides for free amounts to the same $30 per year that Microsoft charges. Albeit zero patch is willing to hold us hostage for at least five more years for the privilege of staying with Windows 10. Just thought you'd like to know if you didn't already. Okay, so Greg, thank you. I was not aware of the fact that and Leo, obviously you weren't either from your reaction, which echoed mine, that the patches applied by Zero Patch are only in place as long as the zero Patch subscription remains valid. So I'm glad to know of that and my feeling is that fact ought to not be buried in an faq. It ought to be made very clear, though I don't know either way whether or not they make it clear. That would be nice to know. That is if you do sign up is are you told upfront that your systems will only be patched as long as your subscription remains current? Now, the way that I can see it's sort of making sense, at least from their perspective, is that none of the 0 patches ever modify any of Microsoft's files on disk. As we know, Zero Patch only applies patches in ram. And it's a clever solution. It means that they're never modifying Microsoft's files. So the digital signatures on Microsoft's own original Windows files are never broken. And it means that flaws are patched on the fly without any need to even reboot your machine. You know, and when, when the machine in question is a busy server on which others are depending in real time, that can be a real win. You're able to fix problems on the fly without a reboot. So that's a nice feature of it. But it does sort of say that whatever it is that they're providing you from from Zero Patch that enables this on the fly post booting in RAM patching is transient and if your subscription expires, so do the patches. So given that first of all it we may well see that Microsoft is going to change their policy by this time. It will have done been done by this time next next month. Wait, is is I think is next.
- [97:22]
Leo Laporte
Month the last October 15th is the.
- [97:24]
Steve Gibson
Last is the last update. So we would have one more month until November to see whether we get pat November patch.
- [97:34]
Leo Laporte
Tuesday is before the 15th obviously. So I guess you'll get that, that patch Tuesday next month.
- [97:41]
Steve Gibson
Of course. Right. And then the 15th, whatever that date is.
- [97:44]
Leo Laporte
Yeah, it's end of life then.
- [97:46]
Steve Gibson
Right. And then we're gonna see. So of course, as we know, it's not that difficult to get of, you know, one month for free. It turns out I'd used Bing while I was using Edge for a while and I had like, you have points, several thousand points of, you know, Microsoft brownie points. So I, I'm able to get it. But I'm also an MSDN developer so I get this stuff regardless. I'm not your, you know, your, your normal consumer profile. But.
- [98:15]
Leo Laporte
So Michael, patch Tuesday is the 14th. So it's the day after the patch Tuesday.
- [98:22]
Steve Gibson
Okay, well that, that was clever. So they said the 15th, so that made it clear you would get the patch on the 14th and then. But then. Yeah, that's it. Or maybe not. We'll see.
- [98:33]
Leo Laporte
Yeah, but they've backed down in the past. We'll see.
- [98:36]
Steve Gibson
Yeah. And there's a lot of pressure on them and I mean again, they're in the wrong here. I mean they've, it's their os, they could do what they want. But you know, when, when people like Stacy are writing for Consumer Reports saying, you know, we're calling on you to do the right thing, Microsoft.
- [98:51]
Leo Laporte
Anyway, so the issue with the zero patch expiration is that means the zero patch agent is phoning home periodically to check your license. Right. They'd have to do that to make sure that you still are subscribing, that.
- [99:04]
Steve Gibson
You have some kind of. Yeah. Real time connection.
- [99:07]
Leo Laporte
On the other hand, they have free patches. So you don't. Those aren't, you know.
- [99:11]
Steve Gibson
Yes, they're, they're, they're free until Microsoft offers it. So they're, they're, they're free. While it's a zero day that Microsoft has not patched, you get it for free when, when Windows takes over. Then, then, well actually then you no longer need it. So.
- [99:28]
Leo Laporte
Right, right.
- [99:29]
Steve Gibson
Yeah. It'll be interesting to see how this all pans out, you know, and you, everyone knows my position. I'm sitting in front of Windows 7 and it hasn't been patched in a long time and it's working just fine. So you know what the other there is. I mean, I understand that everybody wants to be patched against the latest vulnerabilities, but you know, I'll be talking about Apple here in a minute and you know, nobody was being hacked by, by these targeted attacks except, you know, some, some targeted journalists.
- [100:04]
Leo Laporte
Targets.
- [100:05]
Steve Gibson
Yeah. I mean, so I salute Apple, but, but really we're not in at risk largely. So, yeah, some perspective there. I think. I, I wouldn't get too worked up over, you know, loss of patches for Windows 10. Okay. Nick Nidenbach wrote Hey Stephen Leo. While listening to security now 1043 last week, he said, I was compelled to send some feedback about user training in regards to phishing scams. Oh, this is a good point he makes. He says, it doesn't surprise me that the training was proving ineffective as I regularly see employers send emails with links that the employee often has to click on. Things like alert notifications, announcements, meeting requests, and even choosing yearly benefits. Then there are emails from vendors which can have all kinds of actionable tasks that require clicking on a link. GoDaddy, for instance, sends an email about domain renewals with links for the details. Sadly, the training can't just be simple like don't click on links in emails. Instead it's more complicated. The challenge is teaching them how to recognize a safe link. Or even better, or even better that instead of clicking on a link, go to the site and navigate to where you need to go manually. And it's like, yeah, good luck with that. He says, thanks, Nick Spinride, owner and listener since episode one. So, as I said, I think Nick's point is a very good one. I'm glad he made it. I think he's completely correct when I. When I consider all the links I receive, you know, for good purposes, through email, it's clear that, you know, don't click on anything you receive an email is an impossible nonsense recommendation. So what we really mean is only click on the good links and, and never click on any bad links. But since phishing attacks are deliberately designed to make the bad links look good, that's no help either. So this brings us back to my most recent thought, which is that networks of enterprises great and small need to be designed to be strongly resistant to these sorts of mistakes which will be made by insiders regardless of how they're trained. Because, as Nick says, and he's a hundred percent correct, people have to click on links. Email link clicking is the way business operates now. So I think this means that the principles of least privilege need to be designed into the way any company's networks operate.
- [103:09]
Leo Laporte
Moving forward, I agree 100%.
- [103:12]
Steve Gibson
Glenn Hochberg wrote. Hi Steve, I was listening to episode 1043 today, and when you were discussing how it's impossible to train users enough not to click on potentially malicious links, I recalled that when I worked for a large corporation, he says. I retired earlier this year. They had at least a partial solution to this problem. They employed a third party product that would filter all the incoming email and replace all links with encoded links back to the third party vendor's website. When a user would click a link in their email, the vendor site would look up the forwarded URL in their constantly updated database of malicious websites and either reply with a security warning page with a link to apply to get the reference URL added to the white list if necessary, or else they would forward the user onto the validated URL. No doubt this is not a completely foolproof system, but it certainly helps. Thought I'd bring this to your attention if you are not already aware of this. Thanks for all you and Leo do. I'm a long time listener since sometime in your first year I think, and a Twitch subscriber and look forward to listening to Security now each week. I've spent the last 20 years of my career in cybersecurity at a large corporation and there were many listeners there.
- [104:42]
Leo Laporte
Nice.
- [104:43]
Steve Gibson
Signed Glenn thank you so Glenn, 100%. I think the solution provided by that vendor makes a lot of sense. One thing we've seen is that something as simple as the registration age of the domain referenced by a links URL can provide a highly reliable signal to any threat detector. And notice that the early knowledge of any new threats is provided by the links to that are filtered on their customers behalf. So if such a third party vendor has many customers, all of the links being filtered on behalf of all of their customers will allow them to compile and maintain a central, you know, bad links database. You know, it's very much the way Gmail has a huge advantage by having visibility into so many of its users. So you know, in the show notes I wrote, any new spammer will be seeing very quickly and sometimes even a non spammer will be given a false.
- [105:49]
Leo Laporte
Steve Gibson A false positive.
- [105:52]
Steve Gibson
Exactly.
- [105:53]
Leo Laporte
Probably better to get a false positive than a false negative I guess, right?
- [105:57]
Steve Gibson
Yeah. Fabio in Switzerland wrote Dear Steve, I'm a longtime listener since episode 1 and spin ride owner. My 10 year old imac 27 inch 5k finally gave up and I bought a new Mac studio. I'm using one external 2 terabyte SSD where I have all my photos stored 1.38 terabytes used and one new external 12 terabyte WD mybook with my videos 5.6 terabytes used. He says I'm doing time machine backups and use three different drives two offline and in two different locations. I bought the drives in different years hoping to get different production batches and these are all wd my books with 14 terabytes. I don't remember, but these drives are for sure 6 to 8 years old and I'm thinking of adding another drive to my backup set. I'm thinking of buying an external WD MyBook 18 terabyte and I wonder how you judge the different technologies used in the different drive sizes 8, 10, 12, 14, 16, 18, 20, 22, 24 and 26 TB for the for usage as a backup drive, he said. Chat GPT tells me that WD8 to 12 terabytes seem to be the most reliable as it is most of the time a whitelisted ultra star drive. And he finishes. Any comments are highly welcome and might also be interesting to your podcast listeners. Best from Switzerland Fabio okay, so I don't have any strong opinion about optimal drive size based on experience. All of those are going to be shingled drives, which I I'm very uncomfortable about just because shingling technology is what we've driven the drive manufacturers to in order to get drives that have 26 trillion bytes on on, you know, within their enclosure. It's just. I don't know. But the only thought I really have here is about redundancy, in which I believe strongly. After all, you know that's the entire reason for backing up our data, right? It's so that we have redundant copies elsewhere. I run double redundant RAID six arrays on all of my NAS systems and on all of GRC's servers.
- [108:43]
Leo Laporte
Two drives would have to fail to lose the array.
- [108:45]
Steve Gibson
That's actually no two drives can fail and you still have all your data.
- [108:51]
Leo Laporte
Three would have to fail. Yeah.
- [108:52]
Steve Gibson
Yes. Yeah. So I do this. Yeah, it sounds like Fabio has the redundant side handled with all those WD my my book external drives. But Fabio, my only thought is that it sounds as though your system of backing up has grown and evolved gradually over time and that as a consequence it's remained somewhat manual, you know, needing to plug drives in and out, I assume a manually run time machine and so on. The advantage to the way Leo and I have set up our environments is that everything is always being backed up by all the time with versions of everything without us ever needing to do or to remember to do anything.
- [109:50]
Leo Laporte
RAID 6 do versioning?
- [109:52]
Steve Gibson
No, but RAID 6 gives you redundancy and then you use some other software gives you versioning. Yeah, exactly. So the advantage of what we've done is that you Know, it's all established once and then it just goes. So it's a different way of operating, but it makes sense. You know, Fabio, it might make sense for you to sort of stop and take stock in the entire approach you have and see whether moving some drives into a RAID array of some sort, putting it on the network and setting it up for continuous background backups might be an entirely different way to think about solving the backup problem. Instead of getting, you know, yet another big external WD MyBook and, and plugging it in somewhere and using it some of the time. Just, you know, just a thought. Farnsworth sent me email saying, hi, Steve, you mentioned getting a Samsung G Galaxy A15 for $39 a couple months ago. I have one of those and I would like to get another, but I can't find it or anything similar at anything close to that price point. Can you tell me where you got yours? Okay, so when I saw Farnsworth email, I went over to Amazon, which is generally my go to retailer, and I found what he found, which was nothing at a price like that. Then I remembered that I'd purchased that phone from Best Buy. So I went over there and found it for 49.99. So no longer 39, which it was when I bought it a few months ago, but still close. However, the phone I purchased was by Total Wireless. Best Buy carries Total Wireless, boost mobile and at&t prepaid each of them for that same $50 price. And at&t has a rating of 4.8 out of 5. So anyway, for what it's worth. And Leo, you would know. I don't know. Like, are those sponsored phones?
- [112:02]
Leo Laporte
Yeah. There's what we call subsidized phones. Okay. So when.
- [112:06]
Steve Gibson
So you've got to use those providers.
- [112:09]
Leo Laporte
Usually you're under contract to them for a period of time. Lately it's been two and three years. In fact, with the new iPhones, a lot of people were, were getting excited because they got free iPhones that they have to pay for over three years and if they withdraw, you know, they cancel the account. They have to pay in full. You know, catch the cost of the iPhone up. So something to be aware of when you get a subsidized phone. On the other hand, if you're going to be at Boost Mobile for the next two years, then you get a deal. Right.
- [112:39]
Steve Gibson
Or if you are an AT&T customer, then the, that, I mean, it's a, it's, it's a lovely phone. I'm very impressed. For, for me, it was 39 bucks.
- [112:48]
Leo Laporte
And that's not your main. That's not your daily driver.
- [112:51]
Steve Gibson
No, no, that's my Android. Like try stuff on it. Yeah, yeah, I got it. Because I wanted to experiment with authentication, I was assuming that strong biometrics would be required. Turns out as we're going to find out, not so much. Let's take a break. Okay. And then I want to talk about our last piece of feedback which brought me back to looking at what Apple has done.
- [113:18]
Leo Laporte
Oh good. And we talked about the. Was it mie that you or that we talked about last week and how what a big improvement that is.
- [113:26]
Steve Gibson
We talked about memory integrity enforcement and boy did they go over the top.
- [113:30]
Leo Laporte
Yeah, yeah, I mentioned that on Mac Break Weekly. I wanted to echo your. And I told everybody listening last week's episode because I wanted to echo your. Your praise for Apple. Our show today brought to you by 1Password. Now of course I know you know 1Password for password management, but they do more. They solve a problem very common in business. Over A half of IT professionals say securing SaaS apps is their biggest challenge. Why? Because you know your employees love them. With the growing problem of SaaS sprawl and shadow it, it's, you know, you know, it's easy to see why SAS has become a problem. Thankfully there is a solution from 1Password. It's called Trelica T R E L I c a trellica by 1Password can and it does this automatically discover and secure access to all your apps, managed or not. Trelica by 1Password inventories every app in use at your company and then pre populated app profiles and they have every app in the database assess the SaaS risks and let you manage access, optimize, spend, enforce security best practices across every app your employees use, even the shadow IT apps. It's a way to manage shadow it. You can also use it to securely onboard and off board employees and it helps you meet compliance goals. Trelica by1Password provides a complete solution for SaaS access governance increasingly an important part of your portfolio. And it's just one of the many ways that extended Access management from 1Password helps teams strengthen compliance and security. Of course 1Password's award winning password manager is very popular, trusted by millions of users, over 150,000 businesses from IBM to Slack. But now they're doing more than just passwords with one password extended access management. And of course one password is ISO 27011 certified and they have regular third party audits. And this is important. The industry's largest bug bounty we've Talked about that. 1Password exceeds standards set by various authorities. It's a leader in security. Take the first step to better security for your team by securing credentials and protecting every application, even unmanaged. Shadow it. Learn more@1Password.com Security now that's 1Password.com Security now all lowercase. Thank you 1Password for your support of Security now 1Password.com Security now go there and you will support us as well.
- [116:08]
Steve Gibson
Now back to Steve okay, so Ryan Stoops wrote hi Steve, I've been a podcast listener for about 10 years and I'm immensely grateful for all the work you put in to keep your audience informed about the latest security topics. Like other listeners, I've also used security now for CPEs on my CISSP, he said. I was very interested in the segment you did on memory integrity enforcement, but I've been an Android, he said currently Samsung Galaxy User since the last days of webos and the Palm Pre. Can the advances Apple has made be replicated or adapted to secure Android devices? Are the references to quote the unique strengths of Apple silicon hardware just marketing fluff, or do I have to acknowledge their security prowess and grudgingly switch ecosystems? Thanks, Ryan. Okay, nothing that Apple has done would be impossible to replace or duplicate. But Apple has a huge advantage over Google and Samsung with Android because they control all of their system's hardware, its os, and much of their devices supporting applications such as Photos and Messenger and Safari. We've seen that these other apps form the attack surfaces of which attackers leverage for access to deeper underlying flaws. Also expanding upon a hint of what I said last week, because I kind of mentioned this, an argument could be made that Apple has become somewhat like Ahab with the white whale in its obsession over these flaws. On the one hand, yes, I salute them for taking this stand and for really, really saying no to any intrusion into their system, whether it be great or small. But my Lord, has this been done at great expense. It's a testament to, I'm not sure what stubbornness, maybe some form of insanity. You know, Ahab famously said, I'd strike the sun if it insulted me. Somewhere inside Apple are people who apparently feel similarly about having their devices security breached. But I wonder whether when they began, they appreciated what it was going to take to fully pull it off, as they now have pulled it off. And you know, and that work, I should mention, is still not finished. It never will be. This insanely high level of security requires maintenance now. It still needs to be watched, maintained, and properly extended and evolved over Time bugs creep in even into security systems. So my point, I think, is that in today's world, with the hardware we have and software being created as it is, the actual cost of absolutely and utterly hardening a powerful and deeply connected consumer computing product the way Apple has just done for us with iOS 28 and their A19 chips, and then maintaining that level of security is astonishingly high. This goes way past the point of diminishing returns. It's a price so high that it almost doesn't make sense for Apple to pay it. And I cannot imagine that either Google or Samsung are capable of caring enough to make that same sort of investment. And it's not clear to me that they should the payback for them or would be quite difficult to justify because a strong argument could be made that their Android devices are very nice and that their security is already good enough and they ought to be content to keep them patched. Yes, forever playing catch up with patches, but also operating far more economically than Apple has chosen to. And I have to take my own, my own observation also here, which is it's impossible to judge the security of a system based on its architecture or just the statements of those making, you know, those claims. Only time will tell whether this, you know, massive investment, this five year investment that Apple has made will pay off and that payoff will be over time with like no other events of this kind occurring. So we're gonna see. But I wouldn't say that it's necessary to, to jump from Android to Apple just for this. Leo, as you and I have have been saying, only really targeted individuals were, were being vulnerable to, to these Apple flaws. I mean the bar is set so high, these flaws are now already previously so difficult to engineer that they're being sold for millions of dollars. And you know, they're being used very judiciously so.
- [121:53]
Leo Laporte
And you also mentioned, we talked about this last week, that these are enhancement on ARM's existing memory tagging feature. And I do. So it's not, I guess it depends on your manufacturer, but some Android manufacturers have at least enabled the MTE protections that aren't.
- [122:14]
Steve Gibson
And Apple did have that for a while. What they found was that it was insufficient.
- [122:19]
Leo Laporte
Right. This is an improvement on that. Right?
- [122:22]
Steve Gibson
It's a big. Well, so first there was EMTE enhanced MTE which Apple engineered with ARM after the release of 8.5. 8.5 is the Android version that incorporated MTE for the first time. But the question is, when is it on? And what Apple has succeeded in doing is moving enough of the technology into hardware that for the first time it can be kept on all the time.
- [122:53]
Leo Laporte
Here's what privacy guides say even about mte that Android as Google has put applied it really only turns on MTV at an app level. So app developers can use it but they're not required to.
- [123:10]
Steve Gibson
And it slows their apps down, which is a reason why a lot of them don't do it.
- [123:15]
Leo Laporte
Privacy guides say that Graphene os, which is a third party Android uses MTE to a far greater extent than stock Android or even iOS. Yeah, this is a good, from privacy guides. This is a very good description. I mean obviously I, I pointed people to the show last week because that's the, the best but Google doesn't even implement this often unless you've turned on their advanced protection feature. So. Right, you know what I think you know the answer is Apple's done it right.
- [123:45]
Steve Gibson
And, and so I would say Apple has done it right at great cost to them.
- [123:53]
Leo Laporte
Right.
- [123:54]
Steve Gibson
And for aim, I mean it's the definition of diminishing returns. Somebody just decided we, you know, we're not going to have any more problems found. We're not going to have any more vulnerabilities that, that are being leveraged against any of our users. That's, you know, we want to plant the, our flag in that. And unfortunately using today's architectures and today's software development techniques and Lord knows what happens when AI starts writing more of our code, we're going to have bugs. So Apple went to like above and beyond to create an architecture that would fight against these mistakes, you know, proactively, you know, foreclose on these errors that are being made. And.
- [124:48]
Leo Laporte
As you said, most casual users don't need to worry about this. Nobody's going to use a Pegasus exploit against you. But privacy guides do point out that the tools used by law enforcement and others like Celebrate and Grey Key, which are tools that they can plug into your phone and extract the data from.
- [125:09]
Steve Gibson
That is a great thing.
- [125:10]
Leo Laporte
They say they're often in the hands of low level law enforcement employees or even outside of government and are to ready regularly abused. So maybe we are more, you know, more vulnerable to this than just the high value targets. Right.
- [125:22]
Steve Gibson
That is a very good point.
- [125:24]
Leo Laporte
Yeah, I'm glad they Apple did it.
- [125:26]
Steve Gibson
Oh, I am too. I'm, I'm, I know it'll be, I'll be proud to own that hardware. Knowing what's inside. It's just, yeah, it's some, somebody really, I mean they just really said we're, we're gonna do this. We're, we're gonna keep our systems from being exploited.
- [125:43]
Leo Laporte
Yeah.
- [125:44]
Steve Gibson
Wow. Okay, we have one more sponsor to get to, but let's do that in a, in a bit. I'll get into this EU online age verification and we'll, we'll take a break when there's was a good point to do it. Good, good. Okay, so I'm sure that everyone who's been listening to the podcast for the past few years, and especially the past few months, will be well aware that of my extreme interest in, and perhaps even a preoccupation with, solving the problem of online Internet age verification, as we know, I was interested enough in the somewhat related problem of online Internet identity authentication to have spent seven valuable years of my life developing a solution and solving the problem. While online age verification and identity authentication are somewhat related, the problem of age verification also brings along some trickier bits. In the case of identity authentication, it's not one's actual identity that's being authenticated. What it actually is is the ability to later prove that you have returned that you are the same anonymous identity that you previously established with a remote website. To accomplish that, there's no need to ever rely upon what I would call an identity anchor. If we use the original username and password authentication, we're simply saying somebody is returned who knows the username and password secrets that were previously established. Thus, you should assume that it's the same individual. And when we used either squirrel, the system I designed, or passkeys, the system that the industry has adopted, we're simply saying, here's a public key for which I have the private key. Now, and at any point in the future, I will sign any unique random challenge you might send me to prove to you that I continue to hold that public keys matching private key. In other words, at no point are we asserting anything beyond the fact that we have returned. So even just the term age verification indicates that it's something more. The user has a property. I'm sorry, has a properly operating age verification system. Sorry, the user of a pro. Too much coffee. The user of a properly operating age verification system need not ever have visited a site before. So it's not about having returned to the site the first time. Such a user visits any site that wishes to verify that they are of at least a certain age, such a system should be able to challenge them to prove they are above a certain age. At or above a certain age, the user should see, you know, some sort of challenge pop up on their client, and then elect to permit their Internet client to assert the truth of that minimum age assertion on their behalf, but only if that assertion is actually true for them. And that's the tricky bit. Any age verification system must be very tightly bound to them, to their real world physical identity. This is another way in which it differs from any fully anonymous Internet authentication system. If we choose to, we could give a friend our username and password, our one time password token, or even our passkey. In other words, traditional Internet identity associations are transferable because they are not intrinsically about us. They're only about the the reassertion of the possession of some secret a secret that could be shared with anyone else, as Netflix has found out. So to my mind, the biggest challenge to solving this problem was will not be technology. As I've noted, all the technological pieces for solving this problem already exist and have for quite some time and they can be deployed without much trouble. The challenge will be the establishment of a true identity anchor, the linking between the age verifying technology and the user's true real world age okay, so let's take a look at some news to see what's been going on and where the world stands. Because I found out something I didn't know. So the first thing was a piece of news about Brazil. Under their headline Brazil Enacts Sweeping Bill Requiring Online Age Verification Safeguards for Children's Data, the Record informs us that Brazil has joined the UK because of course the UK has also just done this, the Record writes. Brazilian President Luis Ignacio Lula da Silva on Wednesday signed a law requiring digital service providers to verify the ages of users and adhere to strict new data protection and privacy requirements for for children and adolescents, Brazil's digital ECA mandates that tech companies take reasonable measures is the term in the legislation to block young users from accessing content which features violence, pornography, sexual exploitation, drugs or gambling, as well as content that encourages self harm. The law requires that reliable age verification mechanisms be used to ensure users of digital services containing inappropriate content are over age 18. Self declaration this is another key term now. Self declaration is no longer adequate as part of the law. It also orders that tech companies set up a parental supervision mechanism to ensure parents can limit and manage the use of the service, the content accessed, and the processing of personal data carried out. Platforms also cannot process children's personal data in a way that violates their privacy or use their data for targeted advertising. The measure, which overhauls a 1990 law, will take effect in March. Okay, so we have six months before this goes into effect. Human Rights Watch organization wrote in a prepared statement. Brazil has stepped forward as the first country in Latin America to pass a dedicated law to protect children's online privacy and safety. In June of 2024, Human Rights Watch reported that personal photos belonging to Brazilian children were used to create artificial intelligence systems which were to turned into deep fakes of other children being abused. Yuck. Okay, so this news that Brazil had joined the UK in legislating that self declaration of one's age would no longer be sufficient. And you know, one has to wonder what the legislators who passed this new law imagined would happen. Six months from now, websites peddling violence, pornography, sexual exploitation, drugs or gambling will face fines of up to 900. I'm sorry, not US$9.44 million at some crazy number of, of Brazilian currency or up to 10% of their annual Brazilian revenue if they do not present prevent underage children from accessing their adult content. So in other words, what we're seeing now increasingly is that the laws that have long applied only in the physical world, not in cyberspace, are finally starting to be applied to both commercial and free online services within the cyber realm. And when these laws are tested, with appeals to courts having final say jurisdiction, they're being upheld under the theory that the greater good will be served by them. And at least in the U.S. you know, we've also seen that requiring mature citizens to prove their physical age by divulging their real world identity is regarded as not unduly birth burdensome. Brazil's passing of this legislation last week, while bragging that it was the first Latin American country to protect the children, got me wondering what the W3C might be doing to get an acceptable solution into the hands of the world's web browsers and websites. Since we need standards more than anything else. I mean there are lots of random ad hoc solutions. If you go over to the app store or on an iPhone and put in age verification, you get a bunch of apps. But we need a standard, one single standard. We can't have a, a, a, any kind of a fragmented solution. So as it happens, I found a page at the W3C with a headline upcoming IAB W3C workshop on Age Based Restrictions on Content Access. The page which was posted in the middle of July says W3C announced today the IAB W3C Workshop on Age Based Restrictions on Content Access 7 through 9 of October 2025 in London UK which is exactly two weeks from today, there will be a workshop with that title held. The announcement says the following. They wrote the Internet Architecture Board. That's the IAB and the World Wide Web Consortium. The W3C are convening a workshop to examine the technical and architectural implications of different approaches to implementing age based restrictions on access to online content. The young are often unprepared for the sorts of things they might find online. Maturity, education and the guidance of responsible adults can help children navigate online interactions, but age is often regarded as the best indicator of how able a person is to cope with exposure to content. Increasing interest is being shown, I'll say, in the implementation of regulation that restricts what content young people can access online. A recurring theme in these efforts is that it is no longer considered sufficient to rely on self assertions of age. A number of jurisdictions have enacted or are in the process of enacting laws that take steps to provide stronger guarantees that children are not expressing exposed to certain content. This workshop seeks to perform a thorough examination of the technical and architectural choices that are involved in solutions for age based restrictions on access to content. We do not expect to identify a single candidate solution, even if that might be an ideal outcome. The goal is to build a shared understanding of the properties of various proposed approaches. In other words, bureaucracy. Great, they said. In general, access restrictions are achieved by selectively blocking or filtering. RFC7754 Technical considerations for Internet Service Blocking and Filtering provides a more general framework for how to think about restrictions on on communications. This workshop will build on that work. In particular, it will seek to examine the specific technical considerations that apply when content is legally accessed by some people and restricted for others based primarily on their age. Individuals interested in participating in this activity can indicate their interest in by submitting a short position paper. Position papers do not represent either the ietf or the W3C. In some cases, an expression of interest is sufficient. Topics of interest, as identified by the Program Committee include surveys of the common features of regulation on age restrictions analysis of the technical requirements that might apply identification of other key factors to consider in the design of a technical architecture, including but not limited to privacy equity of access market dynamics such as centralization, vulnerability to circumvention, cost, accuracy, jurisdiction, geolocation, and censorship details of possible architectural architectures, whether in whole or in part, for determining the age of people for identifying content that might need to be restricted for controlling access to identified content comparisons of different technical architectures examination of how technical architectures might interface with or rely upon regulation or other governance structures feasibility of different approaches and exploration of the ramifications of choosing different technical architectures okay now reading through that, on one hand I become somewhat disheartened since this is, you know, a W C, a W3C group that will be the group that needs to produce the standards that we are right now, this very moment in desperate need of having today. Yet they still appear to be quite a long ways away from even having a rough working specification of anything. On the other hand, it looks like there may be a more far sighted approach here. Like maybe a user tells it like proves to their browser that they are of a certain age and then the browser in a secure means has a way of transmitting that at the initial communication with a website stage so that the, the Internet itself is filtered by their browser that now knows how old they are. So that's a horse of a different color as we might say in not a matter of replacing the yes, I'm 18 button with some sort of interaction. It's literally a way of profiling the Internet based on the proven age of a browser's user, which is way more farsighted than the solutions that anyone is talking about today. So on that hand I'm liking this approach. On the other hand we still need something now, so maybe that's round two, I don't know. Anyway, their announcement of the of this meeting ended by adding input on other relevant subjects is welcome. Papers that are submitted will be used in developing a workshop program. Position papers from those not able to attend the workshop are also encouraged. Submissions can be made by emailing papers to age Hyphen Workshop, pcab.org, participants concludes their choose their preferred format, blah blah, blah. So anyway, so position papers are being submitted. They did say that they would be publishing the papers, which is good because this is in person attendance in London, not over the Internet. It will not be broadcast or recorded, so it will only be by looking at the position papers afterwards and presumably some sort of summary of the meeting's results will be published that will get, we'll get some after the fact sense for what happened. So anyway, we're not going to get any code out of this. This is, you know, way like if we had our, you know, the, the wishes of any kind of system we could ever design or dream of, what would it look like? So the better news came from this which is that the EU itself appears to be somewhat ahead in this regard. They don't have this broad sweeping, wonderful future vision approach that we may get someday from the W3C. They have something that they're deploying like now. Early last month Spain announced that it would be using the W3C's existing system known as verifiable credentials. And Leo, let's take our final break and we're going to talk about what is going on in Spain, in the EU with the W3C's existing verifiable credentials technology.
- [144:25]
Leo Laporte
And then it'll be movie time because Steve brought a little film strip.
- [144:30]
Steve Gibson
Yes, I did. And the good news is you can even those not looking at the video, I, I made it a. It is this week's shortcut. So you know, GRC SC 1044 but also the audio of it is it, you know, tells you enough of what's going on.
- [144:49]
Leo Laporte
Oh good.
- [144:50]
Steve Gibson
Yes.
- [144:51]
Leo Laporte
We'll get to that in a moment. But first a word from our sponsor for this segment of security now, Hox Hunt. We've been talking about them for some time as a security leader. Yes, I'm talking to you. You get paid to protect your company against cyber attacks, right? But as we've talked about, it's getting harder and harder with more cyber attacks than ever. And phishing emails that now are really indistinguishable from the real thing. Thanks to AI Generation Legacy. One size fits all. Awareness programs don't really stand a chance. They send, you know, typically four generic trainings per year. Most employees ignore them because they feel like punishment. Right. And when somebody actually clicks, they're forced into embarrassing training programs. It feels like you're getting spanked. No, that's not fun. That's. And it's not a good way to learn. That's why more and more organizations are trying hoxhunt H O X H U N T Hawks Hunt goes beyond security awareness. It actually changes behaviors by rewarding good clicks and coaching away the bad. Whenever an employee suspects an email might be a scam, HOX Hunt will tell them instantly, providing, I mean, it's fun. It's like you get a gold star providing a dopamine rush that and because it's fun, because it's encouraging. It's a reward system. It gets your people to click, learn and protect your company. We know people learn better this way. And if you're an admin, you'll love Hawks Hunt. It makes it easy to automatically deliver phishing simulations across email, yes, slack or teams because they come in all kinds of way now. And you can even use hawkshunt's built in AI to mimic the latest real world attacks. You can make very, very nicely crafted fake phishing emails. The simulations are also personalized to each employee, which is exactly how the bad guys do it based on department location and more. Instant micro training solidify understanding and drive long lasting safe behaviors. You can trigger gamified security awareness training. They get stars and badges. It makes employees want to do it. It's fun. It boosts completion rates, it ensures compliance. And you get to choose from a huge library of customizable training packages or even generate your own with AI from scratch. Hoxhunt has everything you need to run effective security training right there in the one platform, meaning it's easy to measurably reduce your human cyber risk at scale. You don't have to take my word for it. Over 3,000 user reviews on G2 make Hox Hunt the top rated security training platform for the enterprise. Number one and easiest to use. Best results. It's also recognized as customer's choice by Gartner and thousands of companies like Qualcomm, AES and Nokia use it to train millions of employees all over the globe. Visit hoxhunt.com securitynow today to learn why modern secure companies are making the switch to Hawkshunt. That's Hoxhunt.com Security Now. H O X H-U-N-T.com Security Now. Thank you Hawks Hunt for supporting the good work Steve's doing at Security Now.
- [148:16]
Steve Gibson
Steve okay, so Spain early last month, Spain announced that it would be using the W3C's existing verifiable credential solution. So just to be clear, this is not what the W3C appears to be talking about. I mean, I love the idea of a user establishing an age relationship with their browser and then the browser and websites negotiating whether you know what the Internet looks like based on somebody of that age. We're not. That's maybe someday what we're talking about is what we need today. And we do need something today. So they wrote in their announcement w3c verifiable credentials. And I'll be explaining what that is in detail here in a second are the future of verification with member states continuing to embrace this powerful and versatile technology, Spain has recently released technical specifications for their new online age verification system aimed at controlling the age of users seeking to access online adult content. In the last few years, different specialists have come to the conclusion that the easy and free access to online adult sexual content is harming kids and teenagers mental health and their social and relational skills. Therefore, Spain is planning to limit minors access to this type of content by implementing an online age verification procedure. This System will use W3C verifiable credentials and focus on a protocol for verifying the age of majority without disclosing personal information that could identify or track the user. By applying this data model, the content providers can verify the age of the user without accessing any other data any other personal data, thus minimizing the data disclosure and adhering to general Data Protection Regulations. You know the famous GDPR principles. Okay, so that all sounds like exactly what we want. Spain's announcement explains the basis for their decision under the subhead why are W3C verifiable credentials the right choice for online age verification? They write W3C verifiable credentials are a digital document format that can represent a wide range of information or claims about an entity such as a person, organization or dis device that can be cryptographically verified. These credentials are designed to be secure, tamper evident and privacy preserving, allowing the holder to present them to verifiers with a high level of trust. W3C verifile verifiable credentials are the future of verification because they offer and they give us three points. First, unmatched security advanced cryptographic methods make W3C VCs tamper proof and trustworthy. They could also comply with signature schemes of the EIDAS Regulation for secure digital transactions and ensure the provenance of information. Second, enhanced privacy when sharing a VC users can choose to share only the necessary information embedded in credentials without revealing more than required, for example proving the user is above a certain age without sharing the full date of birth. This safeguards the privacy of users personal information and empowers citizens sovereignty over their information by allowing them to govern the access to their personal data, something that until recently was not conceivable for many due to the nature of information sharing processes. And finally third portability VCs can be seamlessly stored and linked to digital wallets and be presented when needed. They said the key requirement of Spain's online age verification system is the privacy untraceability of users activity when presented when presenting their age for verification online. This makes W3C verifiable credentials data model the perfect choice for such use case. Their technical olution follows the OpenID for verifiable presentations. That's OpenID 4 VP specification ensuring secure and private verification of age credentials. Additionally, the framework includes trust management via whitelists which ensures only trusted entities can issue or verify these credentials. Okay, so I have a video which was part of the announcement. It is a it is a production of Spain's showing how this works. I've got the the link to the YouTube video in the show notes and as I mentioned before, it is also so everyone can access it easily because this is really cool to see. It is today's shortcut GRC SC then today's episode 1044 and Leo, if we can run it, let's show it to our listeners.
- [153:57]
Leo Laporte
Let's roll the tape for our viewers. Yeah, well, listeners can listen to it.
- [154:02]
Steve Gibson
Yeah.
- [154:03]
Leo Laporte
Here we go.
- [154:03]
TWiT Network Announcer
To help protect miners online, the European Commission has made available a prototype for a privacy privacy preserving, secure and open source age verification solution based on EU digital identity wallet technology. The solution can be deployed by a member state or another entity. They can customize the open source solution to their needs. The prototype of an age verification app will provide trustworthy evidence that the user is over a certain age. Deployers of the app can also set the proof of age to a different level depending on national law and use cases. So how does it work? First, the user downloads the age verification app from the app Store. After a short introduction, the user has to accept the terms and conditions of the app and the data protection information. Afterwards, the setting of the PIN to add access the app as needed. If the user wants the activation of the biometric access on the smartphone is possible. Now the user has to select which kind of methodology for the age verification is preferred. It can be chosen between national identity documents, bank identities and in the future I'll passport reading. In the example here, the user will be guided for the national identity document into the EUDI portal and can pick there a credential for the age verification only the information confirming that the user is over a certain age will be saved in the age verification app. No name, no birthday or other information of the user is stored. The data privacy of the the user is fully respected. The citizens can be sure that there is no traceability of their activities. No user profile can be generated to access age restricted content. Citizens simply need to share their age credentials by scanning the QR code displayed on the website.
- [156:11]
Leo Laporte
If the user I don't understand what happened. Oh, I got confused. I thought that was my screen. Okay.
- [156:19]
TWiT Network Announcer
Access online service on the smartphone.
- [156:22]
Leo Laporte
My menu popped up.
- [156:23]
TWiT Network Announcer
No QR code needs to be scanned.
- [156:25]
Leo Laporte
Apparently they use Macintoshes in Europe.
- [156:27]
TWiT Network Announcer
The app will submit the proof of age to the website only if the user is of age. Access to the website is granted. No other personal information is shared and nobody can steal your ID to log on. If the user is a minor, they cannot access age restricted content content this open source blueprint is now available at hverification Dev.
- [156:55]
Leo Laporte
So obviously no kid is going to have this verification, right? I mean this is something, I mean kids don't have national IDs or do they?
- [157:04]
Steve Gibson
Correct. So, so yes. So remember that this whole, the whole concept here is that it fails closed. That is if, if you are unable to prove that you are old enough, the assumption is you're not and so you don't get to see that content. So, so the, so the idea being that people who are old enough to be able to, to prove their age are able to do so. Okay, so, so before I go any further, I, I, I got a kick out of the the comments that were left on this video. One said Orwellian government, here we go. The next was due to local laws we're temporarily restricting access to this comment while the EU estimates your age. Someone said, whoa, amazing. I love censorship in the western world. So progressive. Or how about didn't realize I was living in North Korea all along. I love having to deal with this garbage because parents can't just be good at being a parent. Another one was please no, stop with this nonsense. 1984 should be a warning, not a blueprint. Someone said, does anyone have a link or petition to vote against this? Someone else, hell no. I hate this. Any petition to sign against this. And then age of no privacy. The cyberpunk timeline might be real and finally perfect. Restrict most of the Internet and create a surveillance state because some parents are too dumb to watch their own children. Okay, so at some point I would imagine that some of these outraged comment leaving people are going to wish to go somewhere on the Internet containing content that cannot be legally viewed by minors within their country, province or state without something like what this video shows us. The, you know the laws have changed to are and are changing to now require all such websites to proactively verify every single visitor's age. As we've seen, so called self declaration no longer cuts it. The yes, I'm 18 button, ridiculous as it always was, is now being tossed into the waste bin of Internet history. So this change in the law will require these commenters who are all upset over what they don't understand here, to produce some form of proof of age. That's tomorrow's reality. I mean that's what's happened, that's what we're seeing happening all around us. UK's done it, Brazil's done it. Our own Supreme Court just said yeah, no problem. So the problem with that is that anything we have today requires the disclosure of a true real world identity. You know, that is except for this. You know, within the EU, the UK and the US one must be at least 18 years old to obtain a credit card. So it might be that until we have something better, providing proof of age with a valid credit card would work, but that's certainly not anonymous and I would never want some sleazy website to have my credit card information. So my point is, while I completely understand and sympathize with the sentiments of these people, yes, sometimes change is hard. The truth is that the Internet has been a cyber world exception from the laws and responsibilities of the real world. And, you know, cyber is finally catching up. This is changing. So these people are likely living within democracies in which their elected government legislators have recently decided that if they want to continue to have access to adult material online, they're going to have to prove that they're old enough to do so.
- [161:11]
Leo Laporte
Yeah, and by the way, somebody in our chat who I guess is Spanish, says you get a national ID in Spain at birth and everyone in Spain has a national id. You don't have to legally carry the card until you're 12. So everybody, even kids, have national ID in Spain. So this is very practical for them. Yeah, yeah, yeah, yeah.
- [161:31]
Steve Gibson
Now you have to have a device. On the other hand, you know, you can't be on the Internet without some sort of device. It's not like it directly beams into your brain. So.
- [161:41]
Leo Laporte
So the only thing that sees the ID and verifies it is the app. It doesn't connect to a server at all.
- [161:47]
Steve Gibson
No, so. So I'm just about to explain exactly.
- [161:53]
Leo Laporte
Okay, go ahead. I'm sorry.
- [161:55]
Steve Gibson
So I am for, for what the video showed. I am very impressed. To the EU's credit. They got it all exactly right. You know, what we saw was a system where a website shows a QR code which your smartphone scans. A process occurs which I'll explain. And you are, then you are then verified of being of sufficient age to view that site's content. So, and I'm, I, you know, they got that right. And apps for Android and iOS are available at that dev site for download and testing by people who want to start deploying this technology. So, okay, so the way this thing works is that there, it's all based on this verifiable credential. The verifiable credential is just a JSON object, a JavaScript object, notation object. I've got a sample of one in the show notes here on page 21. It's just a text file with a bunch of stuff in identifies the data as being a verified Credential and an overage token credential. That is an overage token of token credential information. It indicates the, the issuer of the credential, the issuance date and the expiration date and the credentials subject is listed as over age and it's 21 or 18 or whatever. Now at first I was annoyed by the, at the syntactical term over age. You know, my first thought was that it should be at or over age. If they're going to say like, you know, like over age 18, it's actually at or over age 18. But then I realized that technically it's correct. Birthdays are anniversaries, so when someone reaches their 18th birthday, they're not 18. Each birthday marks the end of that year of their life. So anyone who's 18 is over 18 since they're now into their 19th year. So technically that's correct. Even though if you kind of stumble on it, if, if you're, you know, someone who's, who, who's used to coding. So after specifying the context, the issuer, the issuance date, the credentials expiration date, and the credentials subject being an assertion of age, the remaining information contained is just the proof of validity. Significantly, nowhere, anywhere in the credential is there anything that identifies the individual. There are some serial numbers and as we know, anytime we have a serial number and, and a digital signature, we need to have some sort of unique entropy data. So basically Leo, this is, this is a certificate. This is, this is in every way it's like a certificate that we've been talking about for years. Web servers have certificates which have been signed by a certificate authority which, which, which they maintain to assert their identity. This is a certificate which individuals can obtain which is, and, and that, that process of, of establishing your age with the portal, the, the, the, the, the portal in Spain that this works with is the, the is the process of this individual presenting their id it assigned by that authority and then it is held by the app. So that's all there is. There is no name, there is no other identifying information in that certificate. So when they, when the app, when the app is used, the website presents some entropy. You saw how crazy big that that QR code was. There's a lot of data in there in their sample, so there's some entropy there that's combined with their certificate which contains a, the, the, the, the verification of its validity. The app then signs it and the site is able to verify that they are holding a valid certificate because it's able to Check against the public key of the entity which signed this, the certificate. Basically it, it's exactly the way web certificates have functioned where there is some limited number of trusted certificate authorities in a route there, there will be a similar route of trust for, for these and, and the, the issuer of the age assertion certificates public key will be available to verify the signature of the certificate. And it means that people are then able to go to sites show, you know, scan the QR code that is presented and without revealing anything other than the assertion of their age, prove that to the site and then be permitted in. So I, I'm, I'm very impressed they, they, they got it right. Now what did surprise me as, as I mentioned at the top of the show is that the biometric, the use of the, of the smartphones biometric was a convenience rather than, rather than, and rather than a necessity. So all you're doing to reassert your use of that is using a six digit PIN which isn't biometrically locked to you. So it seems to me that that's a little weaker than we might be able to have. But it also, you know, I guess not, you know, not everyone wants to be tied to a biometric. Some may consider that more of a privacy concern. So you, you, you establish your identity with a phone. You, you, you set a six digit pin, you and you're then able to assert your identity as a Spanish citizen as Spain begins implementing this. And so now the question will be what do websites do websites that want to be avail have availability of their content to Spanish citizens? Because presumably sites that don't do this are subject to fine of not $9.344 million or 10% of a site's annual revenue. So still a lot to be done. But I'm hoping that people are now going to be pointing at Spain and saying hey, let's do what they did because it works.
- [169:31]
Leo Laporte
Interesting. All right, are they implementing this or is this just proposal at this point? They are actually implementing?
- [169:39]
Steve Gibson
Yeah, it is, it is, it is being used in. There was a bunch of countries beyond Spain. I don't, I think I had it somewhere. I don't see it. But so yeah, I mean it is, I would say it's on the way at, at this point it's age verification.dev if you go there, you are able to get the, the code for this on for iOS and Android on GitHub. So it is available but you would.
- [170:14]
Leo Laporte
Have to have the app be signed in order for it to be trusted, right?
- [170:18]
Steve Gibson
No, and that's the beauty, is that the JSON certificate is signed. The app itself doesn't have to be, and in fact, the app cannot spoof your identity. So it's that JSON object where. Which you have is what sign. Now, if it turns out that it's possible to export that JSON object to somebody else, then that would be a problem because then that, you know, because that's making the assertion. So, so the, the presumption is that that object is locked to the phone in some fashion.
- [170:58]
Leo Laporte
It's very interesting.
- [171:00]
Steve Gibson
Anyway, so. So the W3C has been doing some work. This whole verifiable credentials thing is basically a very. Is a flexible textual format that's able to be used for all kinds of assertions. It's just that Spain is simply. Is only using this thing they refer to as an overage token credential, as, you know, one flavor of this.
- [171:26]
Leo Laporte
Yeah. Now I don't see this being adopted in the US at all because a. We don't have a national identity card.
- [171:36]
Steve Gibson
Right. Well, no, but we do have driver's licenses and you know, and for example, in California, we have. We have a digital id. I've got it installed on both of my phones.
- [171:49]
Leo Laporte
Right.
- [171:50]
Steve Gibson
And, and, and that did have the true age facility in it already.
- [171:56]
Leo Laporte
Ah, interesting.
- [171:57]
Steve Gibson
So. I'm sorry. So. So. So Californians, I think they're about what it looked like. I remember running through the list of states. It was about maybe 10 or 10, 10 to 15 US states do have digital IDs. And, you know, states are going to have to provide some means for allowing their citizens to assert their age online.
- [172:18]
Leo Laporte
Of course, not everybody has a driver's license or an id.
- [172:22]
Steve Gibson
No, that means you can't acquire it.
- [172:28]
Leo Laporte
But I guess you could say if you want to look at adult content. Yeah. The secondary issue in the US Is what is adult content and who decides.
- [172:37]
Steve Gibson
Right. And unfortunately, entirely. Yeah.
- [172:40]
Leo Laporte
Yeah. Okay.
- [172:43]
Steve Gibson
We're getting there.
- [172:46]
Leo Laporte
If that's where we need to be, I guess.
- [172:49]
Steve Gibson
Well, Leo, it's happening. I mean, unless we get a different Supreme Court, and right now they're there.
- [172:55]
Leo Laporte
Well, they didn't rule it was legal. They ruled. They put it off, basically.
- [172:59]
Steve Gibson
So they said that it was, it was not. It was not a First Amendment burden to ask somebody to identify themselves to a website to prove their age.
- [173:11]
Leo Laporte
Yeah.
- [173:11]
Steve Gibson
And every. A lot of people feel, whoa, that's. That's a breach of our privacy rights.
- [173:18]
Leo Laporte
Yeah.
- [173:20]
Steve Gibson
I mean, the, the battles are not over.
- [173:22]
Leo Laporte
Yeah. Yeah. Okay. Okay. We shall see.
- [173:34]
Steve Gibson
Yeah. Just reporting the Facts.
- [173:37]
Leo Laporte
The. The court said that the Mississippi law is likely unconstitutional. So by the way, this is the court's decision. It's unconstitution. U.S. supreme Court.
- [173:49]
Steve Gibson
Okay. I was talking about Texas, but. Okay, well.
- [173:52]
Leo Laporte
Okay, but this is the Mississippi law, which. This is the Supreme Court decision that let it go forward, but they said it's unconstitutional. The problem was that Netchoice, which was the plaintiff in this, has not sufficiently demonstrated that the balance of harms inequities favors it at this time. So they didn't block it. It's a temporary approval.
- [174:16]
Steve Gibson
So is.
- [174:17]
Leo Laporte
I suspect that choice will go back to the Supreme Court because in the decision they said it's clearly unconstitutional. It violates the First Amendment. But it was more of a standing issue or something. It was a technical issue issue and it's temporary. The proceedings will continue in the lower courts.
- [174:40]
Steve Gibson
When was this ruled? I. Because I, I missed.
- [174:42]
Leo Laporte
This was this, this is The Mississippi decision. August 14th. This is the one you were talking about.
- [174:49]
Steve Gibson
Okay. I thought that. Oh, I, I thought that that Blue sky was, was blanked out in Mississippi because the Supreme Court ruled on Texas. That, that, that, that was HB 1181. The, the Texas.
- [175:07]
Leo Laporte
Oh, yeah, yeah, there was. You're right. Now this is an earlier decision in from June. They upheld the Texas law. Okay. Yeah. So that. It's weird that the Mississippi law was unconstitutional, but the Texas law was not.
- [175:26]
Steve Gibson
Right. And it, it was. I can't remember which justice it was. The.
- [175:33]
Leo Laporte
They. Yeah, they said it only incidentally burdens the protected speech of adults.
- [175:38]
Steve Gibson
Right. Incidentally, meaning showing your driver's license is not a burden.
- [175:43]
Leo Laporte
Right.
- [175:43]
Steve Gibson
It's like. Well, okay.
- [175:45]
Leo Laporte
Right. I feel like it's still a little bit up in the air. The Supreme Mississippi law.
- [175:52]
Steve Gibson
All of this is up in the air. The air. Legislatively, everybody is fighting this, but, you know, the UK has passed the law and now Brazil is.
- [176:02]
Leo Laporte
Here's the difference. In Texas, adults were required to verify their age. In Mississippi, all users must verify your age before using social media sites. That's why Blue sky with.
- [176:18]
Steve Gibson
Actually, the difference is that in Mississippi, all social media. Right. And in Texas, it's only the adult content sites.
- [176:29]
Leo Laporte
I guess that's the difference. Okay. Interesting. Yes. All right.
- [176:33]
Steve Gibson
And, and so, so, so in. So elsewhere, Blue Sky, I think it was. Was Montana. I talked about it last week. Somewhere else, Blue sky was doing the same thing they're doing in the UK where they only require proof of age for their. For Blue Skies adult content. Right. Because. Because that state had a reasonable law Mississippi's is nuts. Mississippi is anti social media regardless entirely. It's not, it's not about porn in it, it's about social media. So, yeah, broadly, because it was Instagram that, that caused the, the suicide back in 2023.
- [177:11]
Leo Laporte
Right, yeah. Well, we'll watch with interest. I don't know where I stand on this. I mean, you're right. It sounds like there's a technical, technical solution, a privacy protecting technical solution.
- [177:25]
Steve Gibson
I guess I feel like this is another instance where we've had it easy in cyberspace because nobody understood it and nobody was worrying about it. And so things that would not have been okay in the real world were being allowed to happen. You can't have children walking into a strip club.
- [177:45]
Leo Laporte
Right.
- [177:46]
Steve Gibson
I mean that doesn't not happen, is not allowed to happen in the real world. Yet children are allowed to walk into the equivalent of strip clubs.
- [177:53]
Leo Laporte
Right.
- [177:54]
Steve Gibson
Times a thousand, you know, online. So. So what was not allowed in the real world was being allowed by, you know, just de facto on in cyberspace. And we're beginning to catch up, you know, legislation is going to say that's not okay anymore.
- [178:10]
Leo Laporte
Right. Steve Gibson, always fascinating. That's why we love this show. You can follow it in several ways. Of course you could watch it live if you want. The absolute freshest version. We do stream almost all of our programming live as we do it. You're watching the production happen. In this case, Steve's right after Mac break weekly. So that's 1:30 Pacific, 4:30 Eastern, 20:30 UTC of a Tuesday. Watch it live on eight different platforms. Club members get to watch in the club Twit Discord. That's one of the many fabulous benefits of joining the club. Twitter, TV, Club Twit. Everybody else you can watch on YouTube, TikTok, Facebook, X dot com, LinkedIn. I did it out of order. So now I'm out of Twitch. Did I mention Twitch? And then kick there. I think that's all of them. If I don't do it in order. I know I missed some. But you don't have to watch live. Most people don't. You can download copies of the show. Steve's got a couple of unique versions of the show. He's got a 16 kilobit audio MP3 and a 64 kilobit audio MP3. But he also has. So he's got two audio versions. But he also has the transcript created by the wonderful Lane Ferris so you can read along the show. Notes are all there too. So really that's a great place to get Your copy security now GRC.com While you're there, take a look at Spinrite, Steve's bread and butter. The world's best mass storage maintenance, recovery and performance enhancing utility version 6.1 is right there on the site. And you can get it right now, which you probably should if you have mass storage. You should have spin, right? There's lots of free stuff there. And you can connect with Steve if you want to subscribe to the Show Notes newsletter, for instance, or get his very occasional email when he releases something new. We're waiting for. The DNS Benchmark Pro should be coming out soon. You'll get an email then go to grc.com email by submitting your email, you're not subscribing. Those boxes have to be checked. But you are whitelisting your email so that you can send email to Steve always. He appreciates the thoughts. Of course he also has forums there. That's another way you can contribute to the community. GRC.com we have the show at our website, Twit TV SN. There's audio there and video. We have that video format. There's also a YouTube channel. If you search for security now, you'll find that that's a great way to share clips of stuff with your friends in Spain or wherever and probably the best way to get it. If you're a regular subscribe, it's free. Go to your favorite podcast client, podcast, Pocket Casts Out, Overcast, Apple Podcasts, whatever you like to use and subscribe. That way you'll get it automatically as soon as we're done fixing it up and you can add it to your collection. Steve, we will be back here next Tuesday. I look forward to seeing you then.
- [181:07]
Steve Gibson
Right then I thought what that be the last episode?
- [181:10]
Leo Laporte
Last day of September. Yeah.
- [181:12]
Steve Gibson
Oh, nice. We're getting there. Take cool. Bye.
- [181:19]
Leo Laporte
Security now.