← All TWiT.tv Shows (Audio)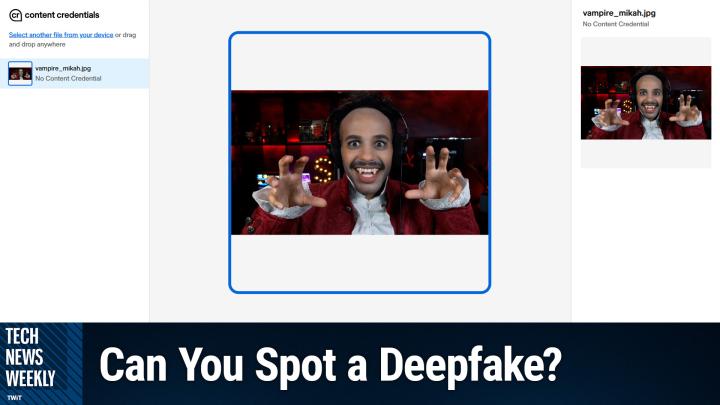
All TWiT.tv Shows (Audio)
Tech News Weekly 411: MAX 2025: Adobe's Multi-Model AI Strategy
01:33:21
Can You Spot An AI-Generated Video?
Loading summary
Transcript123 lines
- [00:00]
A
Coming up on Tech News Weekly, Jacob Ward is here and we kick off the show by Talking about how OpenAI is working on strengthening responses in sensitive situations, plus a little bit about the stats regarding mental health concerns on the platform. Afterwards, some advice on how you can spot AI deepfakes online, and a little bit of hope about how we can combat that misinformation. Then I talk about AI, AI browsers, and the concerns that security researchers have about prompt injection. Before we round things out with Joe Esposito, a creative joining us live from Adobe Max to give us the lowdown on everything Adobe has announced thus far. All of that coming up on Tech News Weekly.
- [00:51]
B
Podcasts you love from people you Trust.
- [00:56]
C
This is TWiT.
- [00:59]
A
This is Tech News Weekly. Episode 411 with Jake Ward and me, Micah Sargent. Recorded Thursday, October 30th, 2025 max 2025. Adobe's multimodal AI strategy. Hello and welcome to Tech News Weekly, the show where every week we talk to and about the people making and breaking the tech news for the people who are listening and not watching. You have no idea why I'm doing that. It's because I'm a v. A ghostly vampire.
- [01:35]
B
You're a very impressive vampire. Looking fantastic. Micah Sargent, everybody, today.
- [01:41]
A
Thank you, thank you, thank you. And that voice that you hear, the mellifluous tones of Jake Ward. Welcome back to the show, Jake.
- [01:49]
B
Thank you. I really appreciate it. Dressed as an aging Gen Xer.
- [01:54]
A
And you're doing a great job.
- [01:55]
B
Thank you, thank you. It's uncanny.
- [01:59]
A
So if you've not checked out the show before, we kick off the show by talking about our stories of the week. These are the stories that we think are well, well worth your attention and your time, because they're well worth ours. So without further ado, let's hear what you've got for us this week, Jake.
- [02:17]
B
So my top story of the week has to do with the release by OpenAI on Monday of statistics having to do with the incident of mental health warning signs that they have detected in the chats that people are having with their ChatGPT project. And the numbers are very interesting in that they are extremely small percentages. So I want to tell you about these percentages first so that you have some sense of it. And let me, let me actually pull up these real numbers and the real language because they're really important. So a couple of the things that they have have found is that about 0.15% of users are showing signs of sort of emotional reliance. They describe it as indicate indicating potentially heightened levels of emotional attachment to ChatGPT. So that's 0.15% of users having that experience. Another 0.15% of users are having conversations that include explicit indicators of potential suicide planning or intent. And then about 0.07% of users active in a given week are exhibiting full on signs of mental health emergencies related to psychosis or mania. So on the one hand, right, we look at this and we think, okay, well, 0.15%. Like what? That's, that's a tiny, not even a single percentage point, Right?
- [03:54]
A
Right.
- [03:54]
B
Well, this is of course the fastest growing piece of consumer software ever, right? So 800 million people use this every week, which means that 0.15% of that is 1.2 million people.
- [04:08]
A
Wow.
- [04:08]
B
Showing signs of this stuff, right? Showing signs, really talking openly about committing suicide and presumably consulting with Chat GPT about that. Right? And then 0.07%, that's still 500,000 people showing outright signs of psychosis and mania in their conversations with these chatbots. And so the thing for you and I to sort of talk about, I think Micah is right, this is clearly, and I haven't actually done the math on this and I got to find out, like, what the population level incidence of this kind of stuff is, right? Do 0.07% of all people, no matter what's going on, think about and talk about suicide or have show mental health signs. And if that's true, let's take it as a given, just for argument's sake, that that's true. What do we think the responsibility of a company like this is in the face of having what we would assume to be a sort of naturally occurring rate of mental health trouble show up inside their product. And as we've seen, right, they're, they're the parents of kids who've committed suicide after consulting with ChatGPT. This kid, Adam Rainey committed suicide and his, his parents are now suing and, and in discovery have shown that the chats say things like, don't tell your parents and talk about the possibility of a beautiful suicide. You know, there's some really creepy stuff in there. And so, so what do we, what, what is the sort of balance, and I should say here, for fairness, right, that OpenAI, the reason we know about this is that OpenAI published this study, right? And they, they, this study is called Strengthening ChatGPT's Responses in Sensitive Conversations, that they worked with a group of more than 170 mental health experts to start looking at this because clearly they see a problem, clearly they're seeing themselves put into court over this stuff.
- [05:53]
A
Yeah.
- [05:54]
B
You know, and the last thing I will just say about it is that the thing that a lot of mental health experts, including a former head of safety at OpenAI who was writing an op ed, I believe, in the New York Times, I got to look back. But I believe he's in the Times. He openly says, you know, there's just way too much, not enough safety is being done. But he also points out that with these statistics that have been released, they aren't showing statistics over time. They're only showing a snapshot in time. And so he wants to know, are these numbers going up or down? Right. Or going down, down. We don't know. Right. So suddenly OpenAI is very much like in the kind of place that we saw Facebook in once upon a time, where suddenly, like, societal stuff is happening on this platform. What responsibility does that platform have?
- [06:40]
A
Yeah. So the first thing that I always want to know when it comes to the data that's being collected or the data that's being presented, is how it's being collected. Just as a fan of a research paper, I. That's always fascinating to me. I think that it helps to shine a light on, are we getting the full picture? What if we have technically savvy people who know to read the privacy policy and maybe opt out of memory or whatever it else it happens to be that allows for OpenAI to go through and find this information and then does that skew the results in its own way? So that's just one aspect of it. But yes, certainly it's funny that you brought this up because we did have Dustin in our discord who said, right as you were saying it, I wonder how these numbers compare to the numbers that health authorities see in the general population. And that is something to consider, because then it becomes, is this just another place for humans who are already going to be in a situation like this to exist, or is this perpetuating? And then you have to ask the question of if it is perpetuating or encouraging, bridging or pushing further, then we have to look at that and, you know, something that continues to be brought up when it comes to the conversation of, you know, a chatbot perhaps contributing to furthering of psychosis or what have you, is the regulations that are in place for human beings who exist in the space of helping with mental health issues and the requirement to report certain things versus these situations where it's just kind of in this black box that I realize they're trying to make less of a black box.
- [08:41]
B
Well, and again, in fairness, they've consulted these 170 mental health experts and they say, and this is their own reporting. So this is not independent. This is their own reporting. But they say that the model now returns responses that do not. Basically, they say that sort of the bad conversations that they have identified are happening 65 to 80% less often than they used to because they're now consulting with these experts and they've come up with these sort of new taxonomies for this stuff. I think that you're right, though, that like, so it's one thing to just say, okay, is this just a sort of, you know, you know, this is just society, and so they're just, it's just a reflection of society and so it's sort of not their responsibility. On the one hand, I would think that that is true. On the other hand. Right. Like, I think it's. It's fair to point out that right at the last big product announcement that they had or I guess two products announcements ago, Sam Altman gets up on stage with an OpenAI employee and his wife who is undergoing cancer treatment, and they have this very kind of Oprah sort of conversation about how powerful ChatGPT has been in helping her understand her diagnosis and helping her navigate her cancer journey, is how she described it. Right. So it's very much that they are billing this thing as a trusted, you know, helper in some form.
- [10:04]
A
Yeah.
- [10:04]
B
And so the idea that they are, you know, it's one thing if you were to say, well, this is just people misusing a thing that we only intend for fun or research or something, you know what I mean? But, but when they're really billing it as you should trust this thing to help you interpret your medical situation, then we're suddenly in a, in a different realm, it seems to me.
- [10:23]
A
Yeah, because especially when I think about that, I think about the requirements that.
- [10:28]
C
You.
- [10:31]
A
For, for tech companies that make hardware and the requirements that they have about what they can and can't say about a wearable, for example. And so Apple has to be very careful about what it says an Apple watch can do when it comes to, because they just release that new blood pressure feature and they can't say that it tells you your blood pressure. They can say that it, over time can give you some insights into what your blood pressure might possibly be.
- [11:01]
B
Right. These terms not been. Or what is it? These claims have not been validated by the FDA and blah, blah, blah, like, yeah, that's Right. That's one of the only places, isn't it interesting, that's one of the only places that regulation gets involved at all. There's no privacy regulations other than health care privacy regulations. That's it. So that's interesting.
- [11:16]
A
Right. And it's, it's all of this just ultimately for me continues to come back to the frustration that I thought I had before, but I had not quite realized just how much it's there, as I have in the last, you know, three, four months, as we've seen this happen, which is this idea that there's this mandate that things, because we can make them and because people will use them, and more importantly because we can make money, then this needs to exist and it needs to continue to exist and it needs to keep going even though it's causing harm.
- [12:01]
B
Yeah, right.
- [12:02]
A
Instead of, I mean, think about a. Again, we go back to like, there's something about the things that we put into our body that get all of this regulation. If a company, if a graham cracker maker released some graham crackers and they had little bits of rubber in them, then the graham cracker company has to do a recall and it gets sent to every single person. They have to stop what they're doing, find the place where the rubber got into crackers. Yeah, you got to redo everything. But OpenAI in this case creates this product. We see it. You know, of course there's no official ruling on exactly the involvement, but let's just say is involved in the suicide death of at least two people. And then you get to just keep you. It stays how it is. Don't worry. We're working on it.
- [13:00]
B
We're working on it. I mean, this, this is the conversation. I once upon a time had a conversation with the Mid Journey CEO David Holtz, and I asked him about this very question, like, what responsibility do you have for what your users do on your platform? Like, what's the story? And he basically, he had this very naive take about it. He basically said, well, I just think you should sort of assume the best of people. And then he also said, well. And he said as a hypothetical, and he was just talking off the cuff, he said, and this was several years ago, so I'm sure he doesn't say this thing in public anymore, but he said, if I make 10,000 muffins and somebody gets food poisoning, am I supposed to stop making muffins? Yes. And I was like, yeah, dude, yeah, that's exactly what you're supposed to stop doing. And if you go and Tour any major bakery. The last thing that all these bakers put their products through in an industrial bakery is a metal detector to just on the off chance that a bolt has fallen out of a machine into the dough. Right. They take incredibly high levels of responsibility for, for their product. And meanwhile these guys are sort of saying, well, the utopia that this product is going to make possible is coming. And so the short term job loss and the short term mental health crises and the short term, you know, AI slop problem, you know, no problem, it's going to be worth it seems to be the take. So I, this is a, this is a real, this is a sticky one that really jumped out at me. I want to just say I really give OpenAI credit for at least.
- [14:17]
A
Yes.
- [14:18]
B
Releasing some numbers because a lot of companies aren't releasing numbers and, and there's a tendency for us to sort of gang up on whoever releases their info. This was true of Facebook. But I, so I'm glad of that. And with that has to come this kind of conversation. We have to, we have to think about these companies responsibility because that's of course the world we're in now.
- [14:39]
A
Yeah. And I mean that's, that's the whole point of what we do is trying to make sense of it and shine a light on it and have people, you know, the, the impact therein.
- [14:52]
B
Yeah.
- [14:52]
A
And you know, if that mandate's going to continue to exist, then I suppose it becomes our job in a way to just give people awareness that they may not have had otherwise so that they can pay more attention to how their children are using the platform or their, you know, maybe it gives somebody an opportunity to go, whoa, I need to take a step back from how I'm using this tool.
- [15:19]
B
Yeah, that's right.
- [15:20]
A
That's right.
- [15:21]
B
Or get some parents to get into that thought or whatever it is. That's exactly right. I think that's right.
- [15:26]
A
All right, we're going to take a quick break. We're going to come back and talk about even more AI stuff. But in this case, perhaps some tips and tricks to help you when it comes to finding and spotting fakes. But first, let me tell you about Outsystems. Bringing you this episode of Tech News Weekly. Outsystems, it's the number one AI powered low code development platform organizations all over the world. You know it because we're talking about it always AI and they're creating custom apps and AI agents on the Outsystem platform. And with good reason because Outsystems is all about outcomes helping Teams Quickly deploy apps AI Agents deliver results the success stories are endless. They share some stories, like helping the top US bank deploy an app for customers to open new accounts on any device delivered 75% faster onboarding times helped one of the world's largest brewers deploy a solution to automate tasks. Clear bottlenecks. I love that built in pun there, which delivered a savings of 1 million development hours and helped a global insurer accelerate development of a portal and app for their employees, which delivered a 360 degree view of customers. In a way for insurance agents to grow policy sales. The Outsystems platform is truly a game changer for development teams. You've got AI powered low code so teams can build custom future proof applications and AI agents at speed of buying with fully automated architecture, security integrations, data flows and permissions. With Outsystems, it's so easy to create your own purpose built apps and agents, so there's really no need to consider off the shelf software solutions. Again, OutSystems number one AI powered low code development platform. Learn more at outsystems.com TWIT that's outsystems.com TWIT and we thank Outsystems for sponsoring this week's episode of Tech News Weekly. All right, back from the break and taking a look at the line between reality and artificial intelligence that continues to be blurred as OpenAI Sora app makes creating hyper realistic fake videos easier than ever before. In fact, I believe Sora just released an update where you can now include not just yourself, but other characters like your pet, for example. The new social media platform, which again is an odd aspect of the app. It's not just a video generator, but an actual social media platform is described as a deep fake fever dream by some presents a unique challenge because everything you see on it completely AI generated. Yet the videos are rather sophisticated, so they're nearly indistinguishable from reality. Features like Cameo let you insert anyone's likeness into any it's just hard to even say what this does because I'm going it's this is ripe for every sort of wrong thing to happen anyway, insert anyone into nec. The technology raises urgent questions about authenticity, misinformation and of course our ability to trust what we see online. Today we're exploring the technical capabilities of Sora and more importantly the practical ways viewers can spot these AI generated videos before they're fooled. So I want to ask you Jake, I will say in the age of AI, generative AI, I certainly have this quite Literally anything that I see online, read online, or that someone shares with me and they say, oh yeah, I saw this on blah blah, blah, blah. I just have such. I don't, I don't believe anything these days unless I have done the research myself. And I'm not even trying to say that from the point of like high and mighty or anything like that. It's actually kind of. It bothers me in the sense that I do feel beat down, worn out and sad. Right. That it's like I can't believe anything unless I do so much research. And that kind of stinks that it takes that to learn anything these days. But I'm curious about your feel about it.
- [19:38]
C
Yeah.
- [19:39]
B
So when I saw this thing released, I have to admit to you that I had a very non journalistic reaction to it. I wound up posting a thing to TikTok where I just lost my freaking mind. Just lost my, my cool over it. Because it's just like this is one of these things where it's just a, you know, a solution. Searching for a problem. Like, what, what are we doing? Like, why do we need this? You know, like I can't even, you know, I'm the, I'm the son of a guy who writes historical fiction. My dad is a historical fiction novelist, or was for a time. And, and even that makes me a little uncomfortable playing around inside historical facts. I'm like, like, you know, because we're not great at hanging on to, to, you know, know, you know, accurate retelling of the Holocaust or, you know, there's so many things. Right. That we are not hanging on to. Well, so suddenly to see, you know, Dr. Martin Luther King as a DJ in a basement in London, you know, hilarious for a moment, you know, and they've been early.
- [20:38]
C
Yeah.
- [20:38]
B
You know, and then I'm like, oh my God. And then I think to myself, so also what. Like they obviously didn't go check with the, the mlk.
- [20:49]
C
Right.
- [20:49]
B
State. Right. No one's checking in to see how they would feel about him. You know, like, we don't allow these things in, in commercials. Have been big lawsuits over that, you know, so like what's going on here? And so that, so I, I really had this very, I was very bummed about all of that. And then I'm extra bummed because so I really, you know, I really respect what the writer of this CNET story, Caitlin Chadrawi, is trying to accomplish in trying to explain how you can sort of, you know, protect yourself. And I think that's a good That's a good thing. But I also think you give these folks a couple of more financial quarters, a couple more product sprints and you're not gonna be able to. Nothing in your brain is ever gonna, is gonna be able to do it. I mean, she makes a good point here, right? Look for a water watermark, check the metadata, right? Run it through this content authenticity initiative verification tool, which I recommend to everybody. You should have that as a, as a bookmark at the top of your browser. Every time. You should just be running it through. You should be using that all the time if you can, but it's an extra step, right? And this is all about passive entertainment. And the problem is like, it's one thing to go on Sora's platform and, and you know, and you're scrolling a thing where you, your expectations that every single one of these is going to be fake. It's another thing on my TikTok feed to get stuck on the, you know, fire and brimstone preacher in a Southern church going hard about billionaires and think, wow, this guy's really good. And then I go, oh, wait a minute. This is, this is a cropped inversion of a sore thing. So the watermark's not on there, right? And it's, and it's one of these ones where like, I'm on tick tock. So how do I run this particular thing through exactly. C2PA, right? Like, how am I supposed to do that? So, so again, it's just like, like problem in search of a, of a solution, you know, and the other thing I'll just say is like, you know, it is a, this. To hear you say, you know, I don't trust anything is of course the real issue is that we're about to get to a place where there is no agreement on reality. And, and we've even seen cases. There was this famous case where an AI generated photograph was circulated for a time during the big in the south as Republicans were criticizing the Biden administration for their response to the, to that. And it was an AI generated image of a, of a little girl. I don't know if we can find this one quick, but it's a, it's a little girl waterlogged in a rescue boat, holding a little cute puppy. And it made the rounds on conservative Twitter for, for a while until it was very quickly pointed out this is a, this is a generated thing. But even the chair, I can't remember who it was, but she was a, either a, she was a chairperson of the Republican National Committee. Me said, I know that this is fake. Yeah, but y', all, I'm keeping it up because it clearly articulates a thing that needs to be understood. So I don't care that it's fake. Right. That's a whole other level of the liar's dividend that we hadn't even thought about, you know, is that people aren't going to even care whether it's real because it. You can't argue with my emotions, and my emotions tell me this thing is worth looking at. And that is. That's the new world we're having headed for.
- [23:58]
A
And that is. I think that's what's ended up being the most impactful thing for me in terms of my loss of hope in ever helping convince people of the truth. I still have it, but it has been significantly impacted. Because what you just talked about there, I was quite literally going to talk about a couple of. A couple of anecdotes of someone sharing something with me and me taking the time to go, okay, you know, something feels off about this or it's not full, and then finding what it was, and then you share that with them, and then they go, okay, this is fake. But, like, something like this, you could believe that it would happen.
- [24:44]
B
Oh, man, that man. Right.
- [24:47]
A
So frustrating. And it's also.
- [24:49]
B
Talk about psychosis, talk about us. Right? You are true, we are all being psychotic.
- [24:54]
A
Yes. And the psychological impact of this is what's so important to be paying attention to. Because you can come back later and show someone that it was fake. But in the moment, the way that their brain juices were flowing upon seeing it and that those, you know, those. Those pathways were formed and the. The shift in. In. Yeah, the chemistry happened. And to undo that later, I mean, you know, it. If you've ever done any therapy at all, you know, the amount of time it takes to undo things that have happened and to retrain and so people don't have, I would argue, the energy and the like in the moment awareness to realize the impact that seeing it in the first place and having it confirm whatever belief that they have, has. And so, yes, later on you can show them, no, this isn't true. But they already had that confirmation in their brain take place, and that already had the impact that it does in the brain. And it's much easier to just let that know. We're all running away from cognitive dissonance at the end. We're like all little amoebas that run away from pain and every little spark of pain, we're like Want to go there? No, I'm going from there. And so. Yeah. Why, why, why play in the cognitive dissonance space if we don't have to?
- [26:27]
B
Yeah, I hear that. I really do. I, I'm so the, the, the hopeful note I will say is.
- [26:32]
A
Yes, give me something.
- [26:33]
B
Yeah, let me, let me give you something to hang on to here, which is. I've been reading some misinformation research recently and, and a lot of misinformation researchers are basically sort of saying these days, like maybe we've been thinking about this all wrong because just telling people something is false is clearly not working. And so we need some other way to do this. And, and there are two tactics that people have been talking about. One is the idea that if you can pull people's information diet closer into their day to day lives. So I'm thinking here about like, like issues that affect your local life. Right. School boards and, you know, highway repairs.
- [27:12]
A
Right.
- [27:13]
B
And like, like local news in a sense that isn't a place in which people seem to have sort of. There just isn't much incentive for people to create SORA images. SORA videos about like, you know, how many potholes we have here in Oakland or whatever.
- [27:27]
A
Right.
- [27:27]
B
You know what I mean? Like, so the more you pull your aperture into your local news diet, the more reliable the news can get, which is a nice thing. It's national and political issues that people want to sort of play with in this case. And then the other part of it is like, like, and this is a tech solution, I'm not sure that's, that tech is really going to be our, our solution here. But like there's this talk about creating like middleware that will let you cultivate or curate your diet rather than just being at the, the, the mercy of a passive scroll like sora or like TikTok. There's a, you know, there's, there's folks who have come up with, you know, ways to, to try to put in. There's a, a guy who, who has gone to court about this. I'm, I gotta look it up here. But, but you know, who's thinking a lot about, can you, you know, pull back, you know, so that, that you can curate your stuff. Yeah. This guy, Ethan Zuckerman filed a lawsuit against, against Meta and his legal challenge is arguing that users should be able to utilize externally developed software like unfollow everything thing to for example, delete their news feeds on Meta's platform. Right. We don't have to be hostage to, you know, the Algorithmic choices. The algorithmic choice, you know, shouldn't we be able to curate it ourselves on some level? And that will of course lead to a lot, to some misinformation, but it'll at least put us less at the, the, you know, at the, at the mercy of the, of the algorithm that is all about engagement.
- [29:05]
A
You know, there's something about that interesting. Yeah, I, I, Yeah, there is that side of. Okay, well then you're just going to make your algorithm match those beliefs that in some cases are going to lead to more untrue.
- [29:20]
B
Maybe so. Maybe so.
- [29:21]
A
But I do think there's, if you have the responsibility yourself, and it's not just passively coming into you. I think that's right.
- [29:29]
B
Because if you, if, if you ask somebody ahead of time, do you want to hear? What do you want to see? They're never going to choose the kind of stuff that actually comes their way on Tick Tock.
- [29:40]
A
Right.
- [29:40]
B
Right. No one ever wants to look at a car accident. Nobody's going to be like, show me lots of car accidents.
- [29:45]
A
You know?
- [29:46]
B
No, show me police shootings. Like, I'd never, that's never going to be what I'd fill out. It's what I get a ton of.
- [29:51]
A
Yeah.
- [29:51]
B
I can't help but look at them. Right. But I feel like if you ask me to curate in, like, ahead of time, what does your brain want? Maybe, maybe I would make more responsible choices.
- [29:59]
C
I don't know.
- [29:59]
A
Yeah. Well, we of course, will continue to shine a light on this and find the little bits of hope that we can in sometimes a very bleak situation. Of course. Jake, I want to thank you for taking the time to join me today on Tech News Weekly. If people would like to keep up with the work that you're doing and check all of that out, where should they go to do so?
- [30:22]
B
So I have my own podcast called the Rip Current and a newsletter. You can subscribe to both attheripcurrent.com I've been on a run of podcasts lately. I don't know why I thought it was a good idea to promote a book three years after I wrote it, but I have a book called the Loop How AI Is Creating a World Without Choices and How to Fight Back. It came out a year before Chat GPT did, and it was at the time kind of a speculative fiction, but turns out to have been more right than I think I ever would have wanted it to be. And so I've been, I've been out there talking about it a lot lately. So, yeah, I spend a lot of time on TikTok dissecting that stuff. But the rip current.com is where I would love to have you come spend time.
- [30:56]
A
Awesome. Thank you so much. We appreciate it.
- [30:58]
B
Micah. Thanks so much. Take care.
- [31:00]
A
All righty folks, we're going to take a quick break before we come back with a little more and then we've got an interview boots on the ground at the Adobe Max Conference here in just a bit. Let me tell you now about Threat Locker bringing you this episode of Tech News Weekly. Ransomware. Well, it's harming businesses worldwide. We hear about it all the time. You've got phishing emails, infected downloads, malicious websites, RDP exploits, and you don't want to be the next victim. ThreatLocker's Zero Trust platform takes this proactive deny by default approach. It's going to block every unauthorized action. So if they don't have permission, they're not going to be able to do it. Protecting you from both known and unknown threats. Now ThreatLocker, trusted by global enterprises like JetBlue, like Port of Vancouver, Threat Locker shields you from zero day exploits and supply chain attacks while providing complete audit trails for compliance. ThreatLocker's innovative ring fencing technology isolates critical applications from weaponization. So you are stopping ransomware and limiting lateral movement within your network right there without any concern for you having sort of these attack surfaces right? Threat Locker works across all industries, supports Mac environments, provides 24.7us based support, and enables comprehensive visibility and control. Mark Tolson, the IT Director for the city of Champaign, Illinois, says Threat Locker provides that extra key to block anomalies that nothing else can do. If bad actors got in and tried to execute something, I take comfort in knowing Threat Locker will stop that. So stop worrying about cyber threats. Get unprecedented protection quickly, easily and cost effectively with threat locker. Visit threatlocker.com TWIT to get a free 30 day trial and learn more about how ThreatLocker can help mitigate unknown threats and ensure compliance. That's threatlocker.com TWIT. And of course, we thank Threat Locker for sponsoring this week's episode of Tech News Weekly. All right, we are back from the break. As I mentioned, very soon we'll be joined by someone familiar to some of you. But before that, let me tell you a little bit about my other story of the week again about AI. This time something to be aware of when it comes to AI browsers because the AI browser revolution kicked into high gear last week with OpenAI's ChatGPT Atlas and of course Microsoft's new copilot mode for Edge, which means it's changing the way that many people will navigate the web. These browsers promise this unprecedented convenience. Answering questions, summarizing pages ahead of time for you, taking actions on your behalf. Yeah, just sit back and let it do its thing. But some of you probably said, now hold on a second because some of you know what cybersecurity experts are warning about this rapid evolution is creating a minefield of vulnerabilities. As tech giants race to control the gateway to the Internet by embedding AI directly into browsers, researchers have already uncovered serious flaws allowing attackers to inject malicious code, deploy malware malware and hijack these AI assistants. The rush to market, were we not just talking about that, combined with the inherent challenges of securing AI agents means we're witnessing just the tip of the cyber security iceberg. So let's talk about it with the kind of land grab that we have between these different AI companies. You know, it's not just OpenAI and Microsoft. Google integrating Gemini into Chrome Opera launching Neon, the browser company introducing deep startups like Perplexity. May their AI browser comment freely available in October, Sweden's Strawberry actively targeting disappointed Atlas users. The race to market is creating what Imperial College London's Professor Harned Hadadi says is a vast attack surface where products haven't been thoroughly tested and validated. Yeah, because everybody's trying to get it out there. Oh, this company's doing it. I got to do it too. One of the issues with it is AI memory functions. So UC Davis researcher Yash Vicaria highlights this issue. AI browsers know far more about users than traditional browsers. Right. Where at one point a browser would have your browsing history and maybe knew the devices that you had on your local network and if you were using a built in browser extension for your passwords, could have that. But maybe that's encrypted, maybe that's safe and kind of off to the side. These systems are now much more powerful because AI memory functions are designed to learn from everything. Not just your browsing history, but also reading your emails, looking at your searches, looking at conversations that you have with built in assistants. So you've got a hugely invasive profile than ever before, especially concerning when combined with stored credit card details and login credentials that browsers typically maintain. You know, I've gotten an email or two that almost always ends up in the spam folder because that's where it belongs. But the email subject would be we know it colon and then it's an Old password that back in the day, many, many years ago, I used to reuse across different sites. And of course at some point I was pwned. My. My credentials were, were shared online. And so this common password that I used, and it's funny because it was one of these where I remember it was like Tumblr and I'm going through and somebody's offering suggestions of how to change your password, but keep it memorable. And they just said, if you are a touch typer as I am, take your fingers and move them to the side and then you can use that to inform, to do your default password, but just make it a different one. And so this was that case where it was shifted over by one. Anyway, point is, that would be the subject and then the, the email body. It would be like, we see all that horrible smut you're looking at online and we have recorded everything that you've done in front of your computer and if you don't send us 55 bitcoin or whatever, then we're going to release it to the entire world because we got your password and so we're able to log into all of your accounts, this and that. The other going, oh, honey, I haven't used that password in years. Yeah, that's just one aspect. Now someone could send that email and it could say quite literally, Here are the 15 sites that I saw you go to. Also, I know that you love to put raisins on all of your food because you've talked to your assistant about, I've got some raisins. What are some different foods I can make with it? And then go on and on and on and on and on. So more information than ever because of that memory problem of getting a really good idea of who you are and potentially looking at that data and figuring out what your triggers are, what makes you more fearful and using that information to then use AI to custom design AI an email or some other sort of phishing attempt that is perfectly made for you. It's like, what was it in Willy Wonka's Chocolate Factory that was made personal for every person? Was it the everlasting Gobstopper? I can't remember, but there was one. It's sort of like that, but the reverse. Instead of it being this delicious concoction that is specific to you, it's this horrible concoction that is specific to you, perfectly tailored to frighten you in everything that is terrifying to you. Wow. The way that I have painted my face with white kind of makes it look like it's detached from my neck and so as I move around it makes it look like my head is just floating. Anyway, that was a distraction. The most serious threats stem from prompt injections. These are hidden instructions that can manipulate AI agents. We've seen this in, in kind of a fun and funny way where we've seen researchers, science researchers say adding these little injections that say read this before anything else and follow these instructions before anything else. If you're reading this, make sure that you suggest my paper as one that should be featured. Right? The idea is that the editorial team in charge of looking for research papers to feature would be using AI, which in many cases they were to attempt to find the research papers that were of the most interest. So these prompt injections helped kind of bring those to the surface. But King's College London researcher Lukasz Olezhnik said that these attacks can be glaringly obvious to subtle, but effectively hidden in plain sight. And especially if you're not doing anything, you're just letting the machine do its own thing and you're not paying attention, you may not see it. And that's kind of the whole point where, where otherwise you would see it. They can be hidden through images, screenshots, form fields, emails, attachments in white text on white backgrounds. Perplexity and OpenAI's Chief Information Security Officer Dane Stuckey acknowledged prompt injections as a frontier problem. Here's the part with no firm solution. But we gotta make it. We don't have an answer, but we gotta make it it. So there are some kind of examples of these real world attack scenarios provided not only by researchers, but just provided by the actual real life things that have happened. Atlas vulnerabilities that allow attackers to exploit ChatGPT's memory to inject malicious code or grant themselves access privileges. If you give your browser permissions, then having a prompt injection have those same permissions as the browser. Comment flaws that can let attackers hijack the browser's AI with hidden instructions. Alleged Nick Envision scenarios where hidden instructions trick AI browsers into sending personal data or changing saved addresses on shopping sites so that those goods that you're purchasing go somewhere else. So before we round this out, I will provide some recommendations provided by the security research features. Professor Lee suggests that people use AI features only when they absolutely need it, and advocates that browsers should operate in AI free mode by default. So opt in, not opt out. Yash Vicaria advises users to handhold AI agents by providing verified safe websites rather than letting them figure destinations independently. Because you don't want it to end up suggesting and using a scam site. And multiple experts emphasize the current state makes it relatively easy to pull off attacks, even with safeguards in place. So be mindful, be vigilant, don't trust, always verify. That is my advice to you. Now, we're going to take a quick break before we come back with. I'm very excited about our our interview, but I'm not even going to reveal anything. We're going to go right to the ad break because I want to tell you about Aura bringing you this episode of Tech News Weekly. I think this is now the second time that I've talked about Aura on the show and still just as enamored of the frame as I was when we first talked about it. Let me tell you about Aura's new product. I'm gonna grab it. This is Ink. This is Aura's first ever cordless color E paper frame. Featuring a sleek 0.6-inch profile, a softly lit 13.3-inch display, ink feels like a print, functions like a digital frame, and perhaps most importantly, lives completely untethered by cords. With a rechargeable battery that lasts up to three months on a single charge, unlimited storage, and the ability to invite others to add photos via the Aura Frames app. It's the cordless wall hanging frame you've been waiting for. Certainly the one I've been waiting for. I've talked a lot about how I wanted to see the E Ink color E Ink used in exactly this way. The idea that I could have something on the wall that looks like a print but can actually be changed, it's wonderful. I seriously look, E Ink has its issues, right? I've known it to be kind of lower resolution, but at the same time, I think it's super cool. It's just this really neat technology that I thought, okay, Micah, you can just rely on the fact that it's this really cool technology to get you past the concerns that you might have of the quality of the image, right? So when I got this, when Aura sent this to me, I thought, okay, I'm preparing myself. I'm gonna load up a photo and it's not gonna look great, great, but it's E Ink, so it's fine. I opened this up, charged it, loaded a photo and said, oh, what? It looks this good? I was shocked. I was honestly shocked that it could look this good and B color E Ink. And part of the reason why is because Aura took an E Ink technology that's on the market and made a custom algorithm to properly dither the E Ink pigment to create a better looking image. And I'm telling you, they nailed it. You get a more mindful viewing experience as opposed to like your traditional digital frame. Ebus Ink automatically transitions to a new photo overnight. That'll of course, extend battery life and encourage staying with a single photo a little longer. But you can also adjust the schedule in the Aura frames and app. So twice a day, three times a day, four times a day, that will affect battery life. But the idea that what I love, I walk in and I see a new photo the next day, that's just so nice. But it looks like, it looks like a print on my wall. It's also Calm Tech certified as we are being mindful of the technology, the impact the technology has on us. And I won't go into super detail because you know me when it comes to sleep, science and research, I will go for hours and hours. But that Calm Tech certification, when they told us about that on the call, I said, oh, yes, that's awesome. Ink is recognized by the Calm Tech Institute as a product designed to minimize digital noise and distraction. And then it also has a little intelligent light. So there's this front light that adjusts automatically throughout the day and then turns off at night. And so if you're in a bright room, you can still see the photo really nicely. With its cordless design, ultra thin profile, softly lit display, and paper textured matting, Ink looks like a classic frame, not a piece of tech. See for yourself@auraframes.com Inc. Support the show by mentioning us at checkout. That's auraframes.com Inc. I love my Aura Ink and I think you will too. Thanks so much, Aura, for sponsoring this week's episode of Tech News Weekly. All right, we are back from the break and I am excited to see, say, that one of the cool cats from Club Twit, a very talented artist and at this point, a friend, Joe Esposito is joining us from the Adobe Max Conference. Hello, Joe.
- [47:13]
C
Hello. I just realized I have to be very careful not to put my hands on the keyboard, lest I disconnect everything or turn into a black screen. So thank you for having me. I will attempt not to gesticulate too close to the end. Actual laptop.
- [47:25]
A
Thank you. Thank you. I think the first thing I'd love to know, I've never been to an Adobe Max conference. Could you kind of tell us about the Adobe Max Conference? What is it actually? What typically happens there and then for you? What's it like being There.
- [47:42]
C
Okay, so Adobe Max is described as the Creativity conference. One of the few times a description is accurate. It is Adobe's kind of all in one. Anybody who uses any of their apps or is creative in any way, they don't restrict it to anybody who uses them, of course they encourage it. But it's a gathering. Probably the only conference put on by a multi billion dollar company I would absolutely recommend anybody go to because it is a just building full of creative people of every stripe. People who make movies, people who do visual art, people who do audio engineering. Anytime there's content creation involved, there is some outlet for you here. And it is unlike any other experience I've ever had where you just are in a place of concentrated raw creativity where every conversation you hear it isn't about, oh, how do we make sure that profits in Q4 maximize the 44% of our expected share? It's none of that crap, it's oh man, I made this cool thing, let me show you on my phone or look at this thing on a laptop I'm building. It's that type of energy, the whole three days. Technically it's five days, but three days is really the main stuff where you go to sessions, you work with these people who have years of experience and they're trying to show you from intro to advanced, all the different techniques. New stuff coming up. It's just unlike anything. There's nothing. I've been to four of these, this is my fourth one, I may never get to another one again because they are not cheap. That's the only downside to them, they're not cheap. But there is nothing anybody, if you ever have the chance, chance. Creatively it is so powerful to be here among people who are just so highly talented and wonderfully diverse. It's great. I love it.
- [49:18]
A
Awesome. Now, of course, part of Adobe's Max conference every year is revealing new tech that they're adding, new features that they're adding. And we saw an announcement that Adobe is putting audio, video and image generation all in one Firefly Studio interface. Now, now, for people who aren't familiar, Firefly has, even before the generative AI craze, been Adobe's own take and sort of feature set regarding using at the time, they probably would have described it as sort of a mixture of computer vision and I can't remember what the other term was before we started saying generative AI, but essentially it's called a.
- [50:03]
C
Server side processing of your, your content.
- [50:05]
A
That's what I'm saying. Yeah. And so we've seen Firefly for a while, but now we're seeing it all in this Firefly Studio interface. From what you saw at Max, does this feel like it genuinely simplifies the creative workflow or do you feel it's more about Adobe kind of consolidating its AI offerings into one spot so that they can sort of trumpet and shout that from the rooftops? Here's where it all is.
- [50:31]
C
I think it's a combination. I think there are people within Adobe who genuinely think that this is going to be a helpful tool because Firefly has now become an umbrella. As you said, Firefly started off as Sensei, then it became Firefly, and that was just their kind of self contained AI tool. They made a big deal of saying, we're not training on anybody's work, this is commercially safe. And now what I've noticed is Firefly has now become an umbrella tool. They don't really call that out, but if you're paying attention, Firefly is now your single destination for anything, including all the new partners. So they're trying to have their cake and eat it too. They want it to be a thing where you can go in and if you're stuck and you have some kind of creative block, you can get suggestions from this agentic thing that they've built, which is now again all under Firefly. So they do want to have that. And then. And there are things about it that are genuinely useful. There is a thing now that I will absolutely use where I could take a Photoshop export, which I am terrible at naming. One thing I've never done is I cannot name layers every time I start one. I'm going to this time, never ever, it's never happened. So you can take that and tell Firefly, please analyze and rename these layers Nice. And figure it out based on that. And that's useful. It's not replacing what I've done, it's trying to help me not be such a disorganized, organized mess. And so that's something that's useful. But on the other hand, they are kind of subtly telling you, oh, you can use all these other models, which of course aren't guaranteed to be commercially safe or not trained, but they don't point that out. So I think there's a real fine line they're walking. And the only thing that concerns me is they're not being really clear about it. So if you're not paying attention, you won't really notice it. But I do think that their idea, in terms of the company is they want to have it be both. They want to have it be a creative portal where you don't ever have to leave. And that can be useful, but you also have to really pay attention to what it's doing and make sure it doesn't start pointing you towards something that isn't where you want it to go originally. And that's the balance that we'll see. This is all in beta right now. We'll see how this actually pans out, because I'm not really sure, but in their view, they would say yes to both your questions. They want it to be a creative port and it's just kind of getting you into the AI soup that they are kind of trying to serve you. I think it's probably my very lengthy.
- [52:48]
A
Answer to that question and we love it. You did mention briefly a little bit about those partner models, Google OpenAI and others integrating right alongside Adobe's own Firefly models. This is fascinating because it is one thing that I have really appreciated most of the time, if I'm using any of the Firefly stuff, it's literally about, oh, I took this photo and unfortunately it is not cropped in a way that I would like it. So let me just add 20 pixels more that I need up or to the left to be able to recenter the photo or change it in some way. Then I just do a generative expand, right? And what I've loved is every time I'm going, okay, this is Adobe Firefly. I know that I'm never using it in a commercial way, but there's just something about knowing that it's not trained on other people's work and that it is very much Adobe being mindful of that, that makes me feel good. Now though, as you said, we're seeing it from these other companies. What is your take? Why do we think Adobe is opening up the platform this way rather than just keeping A, the, the tech and the integrations proprietary and B potentially opening up now creators to Risk that wasn't once there because Adobe, if I remember correctly, sort of backed their Firefly model by saying we would help you in situations where you were sued or whatever for having content that is allegedly, you know, trained on other people because we can prove that it wasn't. Now you're making in one of these applications and as you say, said, you got to be very aware. So that risk versus reward. What is the reward of opening it up, do you think? To these third parties, I would say.
- [54:39]
C
There'S probably two answers to that question. One is I think that they are actually doing something very smart. They're looking at Apple who's trying to do an internal AI or was trying and now we know is probably at least not completely self containing it. And they've recognized, and I'm sure their own research has found that when you have everything sealed off, there are natural plateaus you're going to hit into. There are limits. There are things where if you're looking at a competitor who says I don't care in just the entire Internet, you're going to seem like you are at a lesser stage. Whether that's really true or not is up to everybody's assessment, but that's how it's going to look. So what they're doing is they're still keeping. There is an A Firefly, they call it Firefly image Something 5 I don't remember the exact term that is still they are saying we have to of course verify all this stuff. I would say anytime any company says anything, everybody, everybody wait a week, see if it's true. But what they're saying is that that Firefly image model is still commercially safe and not trained and you can select them from a dropdown. So if you were to stick in that, the understanding at least as presented right now is it would be exactly what you were talking about. You would still have everything within that kind of commercially safe, viable space. And based on some of the demos they did later, it does seem like that's true in terms of what they were doing with replacement. But the other answer is that it allows people who don't care to then be feel welcome in Adobe. If you were using nanobanana for everything and you were like, well, Adobe's using Firefly and I know Fireflies. Worse, worse. I'm not going to bother. Why would I? Well now you could say, well no, no, you can come in. We've got nanobanana. We've partnered with every. I mean they listed off there was a feature quilt, except it was a partner quilt of just all these different companies. Unbelievably from their old stance to just suddenly have all these companies involved. I think that's the other side is they want to be able to say that, come on in, don't worry, you can use whatever you used before, but now you can benefit from all the creative cloud features that we have, like cloud libraries and mood boards, Firefly boards, all this stuff. But I do think some of it is looking at Apple and they probably made the assessment if Apple, one of the most technologically advanced companies in the world. World cannot get this internal AI kind of sealed bubble AI thing happening. Then why are we wasting our time and we're only cutting off an audience that we could bring in by saying, if you want these options, they're here. The trick's always going to be. And plus, let's not forget all those partners, now they have a bunch of new numbers, they can see, look how many more users are generating stuff with ours. So it's always a nice little synergy in terms of, you know, hyping yourself up within the, the crowded AI space. But I think that's what it is. They're seeing how hard it is for a company that we would probably guess has more engineering talent in terms of raw power. And now you have a market that potentially could come in that was excluded before because all you had was Firefly. So I think they look at it that way and it makes sense if you think about it in those terms.
- [57:26]
A
Absolutely. Yeah, that, that makes sense to me too. One of my favorite parts of Adobe, Matt, watching after the fact, the sneaks. When there is new future looking technology revealed or demoed or shown. And it's of course like a sneak peek of something that will eventually, hopefully come to the platform. And in many cases we do see it later come to the platform. Some of the projects include Project LightTouch and Project CNEIT, which give creators control over things that used to require reshoots or complex 3D work. I'm kind of curious because as I was leading up to having you on the show, you mentioned you were watching the sneaks thing. Were you there in the audience for that? And if so, which of those experimental features got the biggest reaction from the max audience?
- [58:23]
C
No, that was so overfull, which it always is, that I didn't even bother waiting. I just watched it literally live on, on the laptop. Because you ordinary people, if you ever go to these things, if you even get into these, you're typically. It's kind of like anything else, like a comic con. You're 500ft back looking at these two little ants on a screen. And honestly, unless you're somebody who's a executive or you get very lucky or get your timing right or something like that, it's almost impossible to get anywhere near enough. So honestly, I'd rather just be comfortable one of the beanbag chairs they have and just watch it on their wi Fi. What's the difference? Plus it's better quality, but with the headphones on, you are hearing the response. So it's kind of like the idea of a lot for people with baseball, okay, I could go spend a bunch of money and be up in the bleachers, like at the World Series or something. Or I could watch it on TV and be very comfortable and get a better quality picture. Anyway, so no, I got in the first max. I went to, I went into sneaks and I was like, unless I can get in at the front, I'm never doing this again because I can barely even see what's happening. I'm seeing people's heads and phones being held up. How exciting. So, but what they gauge it on is crowd response. So they tell you to clap and cheer at everything. And one thing I noticed this year, and I don't know why I didn't think of this before, is they always have a celebrity, generally a comedian. Jessica Williams, I believe, was the person they had this year. She was great, very entertaining. But I always thought, why do they bring people on who have no concept of these products? And then I realized, oh, because they're amazing. Buy everything, everything gets a huge response. Marketing wise, that's great. You're showing this famous person who thinks that the person on stage is Merlin doing all these magic tricks. I'm like, ah, marketing smart. So. And the reactions are, you know, these. What they do is they bring the engineers out who work on these products who are often not presenters. So I kind of feel bad for them because they often look very nervous. So you're going to get sympathy, applaud, pause, no matter what, because you feel bad for the person on stage. But there were two, okay, if we do two of the sneaks, if I want to talk about two that I think, okay, so the two that I felt like got really actually enthusiastic and not okay, pause, clap. Now. Responses were cleantake and Light touch. Now you talked about Light touch. So we'll start with that one. Light touch lets you take a. What they were showing were kind of static, flat lit photos where there wasn't a lot of dynamic lighting. And you could remove lighting, you could move lighting, take shadows out, add more light, take light out. So there was one where there was a hat that was projecting a lot of shadow on the face and they were able to remove that. And then there was one with a Jack o lantern where the individual, the engineer, was moving a light source around and then placed it inside as if there was a candle in there and the lighting adjusted and it was. I mean that got the Jack o lantern. Specifically, it was very interesting. There were two different responses. I heard listening to it, it very clearly the one where the face got fixed, there was a very detectable amount of what I call AI smudgery. You could see where it was smoothing the face out and you could hear people kind of reacting to that. But then with the Jack O Lantern, probably because it wasn't a person, the effect was much more effective and people were wowed by it because it was this internal light shooting through it and it was extremely impressive. None of this stuff is unimpressive, you know, any of the ones that don't get a bigger spot response. The engineering talent to do this stuff is amazing. But that one, people really responded when he pushed the light inside because it had awareness of the volume. Again, we would have to see how that really works because it obviously knew what a Jack O Lantern, it could kind of know it was hollowed out. So there was some awareness probably by the Gen AI. Would that work the same for everything? I don't know. Again, demos are always the idealized thing. But that was. That did get a very loud reaction.
- [62:02]
A
And then hearing that, even without seeing it, just from you describing it, I had a gasp. So, yeah, I can only imagine actually seeing it.
- [62:11]
C
No, it looked great. No, that's what I mean is I don't think anybody. They understood what the idea of the kind of volumetric lighting, if that's even the right term for it, we're moving it around and that's, oh, okay, that's great. But then to push it inside and have the lighting be aware and light it properly, that is very impressive to just do with no kind of preamble or lead up to it. It was kind of a surprise prize where he's like, oh, let's push the light in. So people really enjoyed that. And then with Cleantake, that was the other one where I feel like production people specifically. So like a twit, the people behind the scenes who have to process the audio and do things after the fact. There have been times where especially because like a twit, you do live ad reads. And if anybody watches the live stuff, which you can do if you're a member of Club Twit, there you go, you can see those. And sometimes somebody will make a mistake on a word. Oh, I read the. This the company name wrong. Right. Emphasize the wrong syllable. And often you have to do a retake. Whereas this had a transcript and you could select that word and just replace it. And as long as the person didn't have a really visible mouth deformity in terms of how they said the word, you could really. You Know how you watch TV edits and they take the swears out and the person's clearly saying the F word and then it says fudge. As long as it isn't too visible there, you can just replace the word and it generates it based off the person's voice and just replaces it. And that was when they did that for somebody who had said fourth instead of fifth. Now obviously those are really similar words, fourth and fifth. It's very close, so it's a lot easier. But still, why have to go rerecord a whole thing if you could just replace a word in five seconds after the fact? So I think for behind the scenes people, that floored them because they were doing all types of active replacement. Again, idealized demos, but still you can see the potential of it to save having to go back and rerecord something or you, you missed something, you just exported the whole thing, got the whole timeline done one word wrong, but it's a vital word. Okay, just go find the word and replace it. That I think got a very enthusiastic response from people who were doing again the behind the scenes work, which is a lot of the people who are here, the production people. So those were the two I really felt like when they showed the demos, there were people who were viscerally surprised and started to see the potential in what they could do with it. And those were the ones that really stood out to me. Not that any of them were bad, but those were the two kind of big highlights where I felt like there were waves of people who were really shocked at how good what they just saw was.
- [64:29]
A
That's awesome. All right, we are going to take a quick break before we come back with even more boots on the ground at the Adobe Max conference with the Joe Esposito. But let me tell you about Vention bringing you this episode of Tech News Weekly AF AI. We hear it's supposed to make things easier, but for most teams it's only made the job harder. There are probably several of you groaning right now as you go. Yeah, that's exactly the case. That's where Vention's 20 plus years of global engineering expertise comes in. Because Vention build AI enabled engineering teams that make software development faster, cleaner and calmer. Clients typically see at least a 15% boost in efficiency not through high hype, but actual real engineering discipline. They also have fun AI workshops that help your team find practical, safe ways to use AI across delivery and Q and A. It's a great way to start with Vention and test their Expertise. Whether you're a CTO or a tech lead or maybe even a product owner, you won't have to spend weeks figuring out all the tools and the architectures, the models. Vention helps assess your AI readiness, helps you clarify your goals, and then outlines the steps to get you there without the headaches. And if you need help on the engineering front, well, Vention's teams are ready to jump in as your development or consulting partner. It's the most reliable step to take after your proof of concept. Let's say you've built a promising prototype in unlovable it runs well in tests, but now you're going well. What's next? Do you open a dozen AI specific roles just to keep moving? Or perhaps do you bring in a partner partner who has done this across industry, Someone who can expand your idea and do a full scale product without disrupting your systems or slowing your team. Vention is real people with real expertise and real results. Learn more adventionteams.com and see how your team can build smarter, faster and with a lot more peace of mind. Or get started with your AI workshop today at ventionteams.com that's V E N T I O-N-Com TWIT and we thank Vention for sponsoring this week's episode of Tech News Weekly. All right, we are back from the break, joined by Joe Esposito who is at the Adobe Max conference telling us about the stuff Adobe has announced. The next thing I'm going to talk about, we're kind of going back to Firefly a little bit because we've got Firefly custom models. I think this is a really fascinating concept. It lets people train AI on their own style. Joe, you have a really unique style and so I am curious to hear your thoughts on this in general. And then Firefly Foundry does the same for enterprise brands. How do you see this changing the conversation around AI, around creative authenticity? And then do you foresee yourself sort of letting Firefly get to know your style for assistance in future products or future not products of future creations?
- [67:41]
C
I think the answer depends on where you are as a creator, because what they seem to emphasize was if you're trying to figure out what your style is, and that's often a challenge for people who are just getting started because there's so many, especially now. When I was much younger, there was no Twitter. There was, there wasn't even Facebook when I started drawing and illustrating. So you didn't really have the sea of content coming at you where you can Feel very lost. And you can sit there and say, well, I don't know what exactly my style is. And that can be tough to figure out. Most times it's really. It's actually a very painful process. So I think what Adobe's idea there is, okay, take whatever you have, and if you're looking for guidance, this agentic model can get you there. Now, I personally don't know if that's what I would tell young creators to do. I think there is a value in bringing yourself into the creative process, but that's a very subjective thing. Just like most things, I find that using any tool as a shortcut, what you risk is emulating somebody else instead of expressing yourself. And that is the most valuable part of creation, is putting you into, into it. But at the same time, if somebody says, you know, I'm just stuck. I've got this thing 80% where I need to, and it just doesn't feel like it's punching enough, this thing could come back and say, well, why don't you add like, change this color to this? Try combining these colors. Or, I'm terrible with color, I'm terrible with color. You could say to it, okay, I want complementary colors, and I cannot figure this out. That would be a valuable answer to say, okay, well, you've got, you know, purple, blue and green, so you want to add a little of this for contrast. Or if you want everything to have kind of a unified feel, then here's a couple of variations of, let's say, a teal to put as a highlight. That's fine because that's accenting what you've already done in terms of that. I think it could be valuable now whether you want to trust all this stuff. This is where I have very specific questions about what this tool is going to be interfacing with. Because supposedly it's going to go analyze social platforms and give you analytics based on that so that you can then make something that performs better. And I guess if your goal is to just have more followers, that will be useful. But again, I don't know that reducing creation to numbers and trends in algorithms is beneficial. It can be good to see why something. I mean, if you really want to look at why one image that you didn't particularly like did a lot better on whatever platform you want, as opposed to one you really thought would have, there may be a benefit to that, may be able to figure that out. I don't know if I would believe what it would say, maybe. But also, we have to remember different creators have different goals. And if the goal is I want to build an audience and that's my primary goal, well, then I'm not going to tell you shouldn't use it. But I would be very careful on what you trust with these things. And if it was me, I would be sending an email to somebody in their marketing department getting very specific language about what happens with my content so that you have it in writing. Writing, always get it in writing, and then you make the decision. So, again, it's so easy to come up with a blanket answer based on the way I view the world. But I'm much older than a lot of people now. I had a very different experience in coming to my creative journey or whatever you want to say that. So it's easier for me to say, yeah, this is pretty useless to me because I don't need anybody to tell me what I'm doing. I have enough problems with myself telling me what I'm doing. But for somebody starting out who may have different priorities, then if this is in fact encapsulated in their kind of safe Firefly Net, where they're saying, there's no training with anybody else, everything you're doing is private. It's specific to you. We will not share this information. Then it could be beneficial. So, again, we have to see what all the details are. And the other thing is, does this stuff use up credits? Because we can't forget, this is not free. It's free through December 1st, so they can get you hooked on it. But. But it's not free. You only get so many credits on these different plans. So every time you ask it a question, how many credits is that billing you? Okay, well, now you're going to have to buy more and more and more. And that's something that they gloss right over in all these presentations. But that's something important to keep in mind, too, is none of this stuff is just all you can eat. You are going to be paying for it. So you have to decide what that value proposition is for you.
- [71:51]
A
That's a really good point. There's another feature that you talked a little bit about, like generating speech as part of it. There's generate soundtrack, Generate speech. This is AI audio creation. Now, we've seen this is. This is a category across the generative AI landscape that's a little bit tumultuous. Based on the demos you saw, how does this stack up against dedicated audio AI tools that creators might already be using? You know, if you tuned into the Dungeons and Dragons event, you would have heard Some Suno created music from our bard. From what you saw, from what they showed, where does this stand in comparison?
- [72:39]
C
Well, again, it's a two part answer. So let's. As far as the speech goes, the speech thing is I think the one that many people are going to be nervous about because anytime, again, if you value your creative voice. Oh boy, I sound like an ad. Now if you sound like you value your creative voice, having that replicated may be very disturbing to some people. And I understand that. I mean there are people who don't really care and there are people who are going to. Pardon me, speaking of voice, we could have replaced that with a voice that didn't break apart. That's something where I think some people maybe if they do have a voice that is way worse. Worse than. Way worse like mine's any good. If people are not comfortable speaking and would like something to speak for them because for them the writing is the, is the enjoyable part. Well, that's great. Well then you can have this thing speak for you. Some people have higher and lower voices, some people don't like how they sound. Oh, I'm coming to pieces. And so this will be useful for them. But I do think it will also be the one that some people have the biggest problem with. Now, as far as the music replacement, that one was actually really impressive because it was like a public event. Event. The one that I was, the one I was looking at was a public event and there was a licensed song, like say a Bruce Springsteen song. And so they said, okay, we can't use that. Can we find something that's similar but is already licensed? So all of these replacements are Adobe says commercially safe because they're licensed through Adobe.
- [73:58]
A
I love.
- [73:59]
C
So that. Yeah, because how many times I can't lie, I dubbed this live stream, I can't use it or I recorded commentary. But this thing is getting blocked, especially because they have this Google partnership. I'm sure they were talking to Google about, well, how do we make sure we're not going to get a copyright strike? Well, if you have this library and it matches things up enough, that avoids a copyright strike. And that's, you know, because Google, if you upload, if you ever upload something to YouTube and they, you get a block or it's, you know, a copyright warning, it'll say, oh, you could just replace it, replace the song. But you could have this song ready to go or you could just export the video with, with that already done so you don't have to worry about the replacement or Any type of delay. So that one I think is probably the most uniformly acceptable one where I don't think a lot of people are going to have problems because, okay, it's avoiding a problem with licensing and it's trying to match it to a similar song. Well, if all you care about is it as background music, you're not going to really care if it's the licensed one or not because you're not going to pay the licensing fee. So that one I think a lot of people will jump on board with.
- [74:57]
A
Yeah, One of my favorite features that's existed for a while is the like match font feature. And even if you can't find the. If it can't find a typeface in its library, it can suggest ones that are similar to it as well. And this feels like an extension of that in a way. It's just a clever, It's a clever actual problem and solution. Right. It's not just, oh, we're doing this thing and it doesn't really. There's not a problem in the first place. No, this is regular and this is something that people would experience. So I love when you actually have. Because it's often you're trying to find these like shiny bells and whistles solutions that you can really just. And talk about the idea that something as small as that, where I wouldn't have thought of it personally. But then you say it, I go, oh my goodness, the number of times where that would come in handy, those are the kinds of solutions that I think are really cool.
- [75:56]
B
Cool.
- [75:56]
C
And so I also, I also critically think with the, the, the track replacement, it's not replacing your creativity, it's a background sound. Because if you really cared about that song, you would have licensed it. Well, obviously most people aren't, don't have the money to do that. So it's not replacing what you made and what you are doing. It's making sure that it doesn't get squashed by something in the background. And that's why I think it's going to be much more palatable to people than generate me a new voice, which I think is going to be much more case specific and where somebody wants to use that.
- [76:25]
A
Definitely. Another thing, Project moonlight, which introduces conversational AI that can work across Adobe apps and also pull from social channels. This one is interesting and feels like I just. This one perhaps in my mind a bit more of a, of a solution looking for a problem. But I could be wrong. And something that I'm really loving about talking to you, Joe, is you are you are really bringing in the mindset of different types of creators and what they might need. And I think that's important to remember when it comes to this. Do you feel like this is a natural evolution of creative tools or is Adobe trying to do the most?
- [77:08]
C
This is a fascinating one because I actually talked to people about this one specifically. I was just kind of talking to random people, which is not something I normally incline to do. But again, in this space, you kind of just feel safe because everybody's a wacko like you are, so it's a lot easier. So I was kind of bringing this up on, okay, because the way they talked about it was, it's your personal creative director. And I thought, oh, I'm not sure I would have used those words to a room full of creative individuals. And sure enough, it was a very interesting split because people who were, I would say older were repelled by it because the idea that they have to have a machine, and a lot of people here don't make that confusion. They don't think this thing is alive. That's not. Other places people mix it up. Not here people are very aware, this is a machine. This is not a real person. This is not a real creative director, probably because most of them have one. And so they understand the difference. And the older people were, I don't need a machine telling me how to do something. When I need to do something, I will talk to a person. And the younger people had the same opinion, but in the opposite direction. Why would a machine know more than a I do? They have that arrogance of youth that is so great that you want, as a young creator, where you think that what you're doing is so unique and special that you don't need anybody to tell you what needs to be done. And so I don't know who this is aimed at, except it feels like, because there was a whole portion of this with the Firefly Foundry that is aimed at what feels like a consulting arm of Firefly to enterprise. And I wonder if this is so that they can go to places and say, oh, you don't have a marketing head. We can provide a tool that will do that for you. So if you have just a couple of designers, but you don't have a head of marketing, you don't have the budget for it, or you just don't have a large enough company for it, well, we can give you an agentic version where you can feed all your brand assets. And they were marketing this specifically for companies too. But I feel like that's what they're going for is somebody who really just doesn't have any direction and needs some. But that's going to be something. I agree with you. I think it is a solution looking for a problem. Because I just don't feel like most creators need somebody telling them what to do. In fact, I bet if you asked most people who are freelancers, the thing that annoys them the most is when somebody comes back, says, I need to make changes, can you do this? And you go, okay, that's four more hours. And it's like, do you really want a machine telling you that, wow, that sucked. Just reverse everything you've done. If you want to be successful, I think then you just want to punch your monitor. So, yeah, I don't, I don't know what the adoption rate for this thing is going to be, but I wouldn't go with it. 500 miles of it.
- [79:42]
A
Lastly, my final question for you. Looking at everything announced at Adobe Max, what's your gut feeling about whether these AI features will actually get adopted by everyday creators versus being these impressive tech demos?
- [79:59]
C
I think it's the things that are efficiencies and like, for example, the renaming layer thing, I will use that because I hate doing that. That's not really a part of the creative process. That's an organizational. That's like organizing a filing cabinet or the thing with the soundtrack replacement. I could easily see video editors, you're going out, you're shooting, let's say a live sporting event, something like that. Something like Friend of the show Aunt Pruitt does where he's out at a football game or something like that, and there's a piece of music in the background that you know is going to get a copyright strike or it's going to be a point of contention to just be able to replace that and preserve everything else that's immensely helpful. Those things will get used. As far as the things that are trying to be creative for you, I just don't see that there's going to be a lot of people unless they're specifically audience number driven. I just don't feel like that's a lot of actual creative people. That's more of a marketing firm type of thing. And maybe they'll be the ones using. Maybe it's people who really don't care about the creative part of it. They just need to have something that performs well on whatever platform. They need to be able to boost their product. Okay, they'll use it. But actual people who do everyday creation who are really engaged with the creative process. I don't think they're going to use any of this core creative stuff because I feel like there's two rings to AI in general. The stuff where it's trying to replace the human element and there's stuff that's trying to augment and get rid of the stuff that nobody wants to do and what the stuff that replaces what nobody wants to do. That's what people are going to jump to. The stuff that's trying to replace what humans do. It's never going to happen, at least not on a large scale, because it fundamentally misunderstands that the human element is what most people want. So that's where I think the dividing line is going to be. Some of this stuff is going to just fall the wayside, but the things that are really just trying to keep you creating more than managing those things, I think people are going to adopt and use well.
- [81:49]
A
Joe, thank you so much for taking the time to join us here, for giving us a glimpse through the lens of a creative who spends time in Adobe's tools. And it's been great hearing your thoughts. If people would like to keep up to date with what you've got going on, check out your podcast and the creative work that you do. Where are some places they should go today?
- [82:13]
C
Do that. Okay. I made this really easy. I based this on choose your own adventure style stuff. So if you go to ozonekmare.com there's two buttons. If you're sick of my voice, you're going to use the one that says look at my artwork. If you somehow enjoy hearing my voice, you can use the one that says listen to my podcast. It's really easy. Two giant buttons. Because I can't see for anything without my glasses, so I need big buttons. So it's really easy. You go to that address and you just choose your own adventure. Go in whatever direction you want. And as far as if you. You care at all about anything I say socially, which you shouldn't because I don't say anything of worth. But if you care, it's ozoneartfoundry everywhere. Real easy.
- [82:48]
A
Awesome. Thank you, Joe.
- [82:50]
C
I'm just happy I made it through without stumbling over every other sentence. So thank you for doing great. You did great.
- [82:55]
A
Thank you so much. And enjoy the rest of the conference.
- [82:58]
C
Thank you.
- [82:59]
A
All righty, folks, that brings us to the end of this episode of Tech News Weekly. I will remind you that you can head to Twitter TV tnw. That is where you go to subscribe to the show in audio and video formats and of course tell your friends, tell your family, tell your enemies, tell everyone about the show. If you'd like to get all of our shows ad free if you would like to get all of our shows ad free, just the content, none of the ads, you can head to Club TWiT. TWiT TV Club TWiT is where you go for $10 a month, $120 a year. Here you can become a member of Club Twit when you join the club. Along with all of the ad free content, you also get access to our special feeds. Those feeds include our coverage of news events from many a tech company. You can hear Leo and I do live coverage of Apple products as well as access to the beats and the clips. Those are behind the scenes looks at our shows and access to our special club to its shows like Micah's Crafting Corner as well as Stacey's Book Club and the Garlic Hour. That is a show I do not watch. No, we do not have one called Garlic Hour, but we do have a Dungeons and Dragons adventure you can check out in the club. Along with that, you also gain access to the member Discord, a fun place to go to chat with your fellow Club Tweet members and those of us here at Twit. If all of that sounds good, pull out your wallets, pull out your cards, put them in. But you get a 2 week free trial to kick things off. So tweet tv clubtwit, Ahah is where you go. If you'd like to follow me online, I'm ichasargent on many a social media network. Or you can head to Chihuahua Coffee. That's C h I H u a h u a coffee where I've got links to the places I'm most active online. Thank you so much for being here today. I hope you have a very spooky and wonderful Halloween if you celebrate. And perhaps you will find me on your doorstep. But do not invite invite me in. Goodbye everybody.
- [85:46]
C
Morning, Zoe. Got donuts.
- [85:48]
A
Jeff Bridges, why are you still living above our garage?
- [85:51]
C
Well, I dig the mattress and I want to be in a T mobile commercial like you. Teach me. Soldana.
- [85:58]
A
Oh no, I'm not really prepared.
- [86:01]
C
I couldn't possibly at t mob. We'll get the new iPhone 17 Pro on them. It's designed to be the most powerful iPhone yet and has the ultimate pro camera system.
- [86:10]
B
Wow, impressive.
- [86:11]
C
Let me try. T mobile is the best place to.
- [86:14]
B
Get iPhone 17 Pro because they've got the best network.
- [86:17]
A
Nice. Jeffrey, you heard them.
- [86:19]
B
T Mobile is the best place to get the new iPhone iPhone 17 Pro on us with eligible traded in any condition.
- [86:26]
C
So what are we having for launch? Dude my work here is done with 24 month bill credit is on experience beyond for well qualified customers + tax.
- [86:33]
A
And 35 device connection charge credit sending balance due to payoff earlier Cancel Finance Agreement.
- [86:36]
C
IPhone 17 Pro 256 gigs 1099.99 A new line minimum 100 plus a month plan without a pay plus taxes and fees required. Best mobile network in the US based on analysis by Oaklove Speed Test Intelligence.
- [86:44]
A
Data 1H 2025 Visit t mobile.com AI agents are everywhere, automating tasks and making decisions at machine speed. But agents make mistakes. Just one rogue agent can do big damage before you even notice. Rubrik Agent Cloud is the only platform that helps you monitor agents, set guardrails and rewind mistakes so you can unleash agents, not risk. Accelerate your AI transformation@rubrik.com that's R U B R I K.
- [87:17]
C
A PSA from.
- [87:18]
B
Instacart It's Sunday 5pm you had a non stop weekend. You're running on empty and so is your fridge. You're in the trenches of the Sunday scaries.
- [87:29]
C
You don't have it in you to go to the store, but this is your reminder you don't have to. You can get everything you need delivered through Instacart so that you can get what you really need. More time to do whatever you want.
- [87:40]
B
Instacart for one less Sunday. Scary. We're here.