Loading summary
Transcript74 lines
- [00:03]
Dena Temple Raston
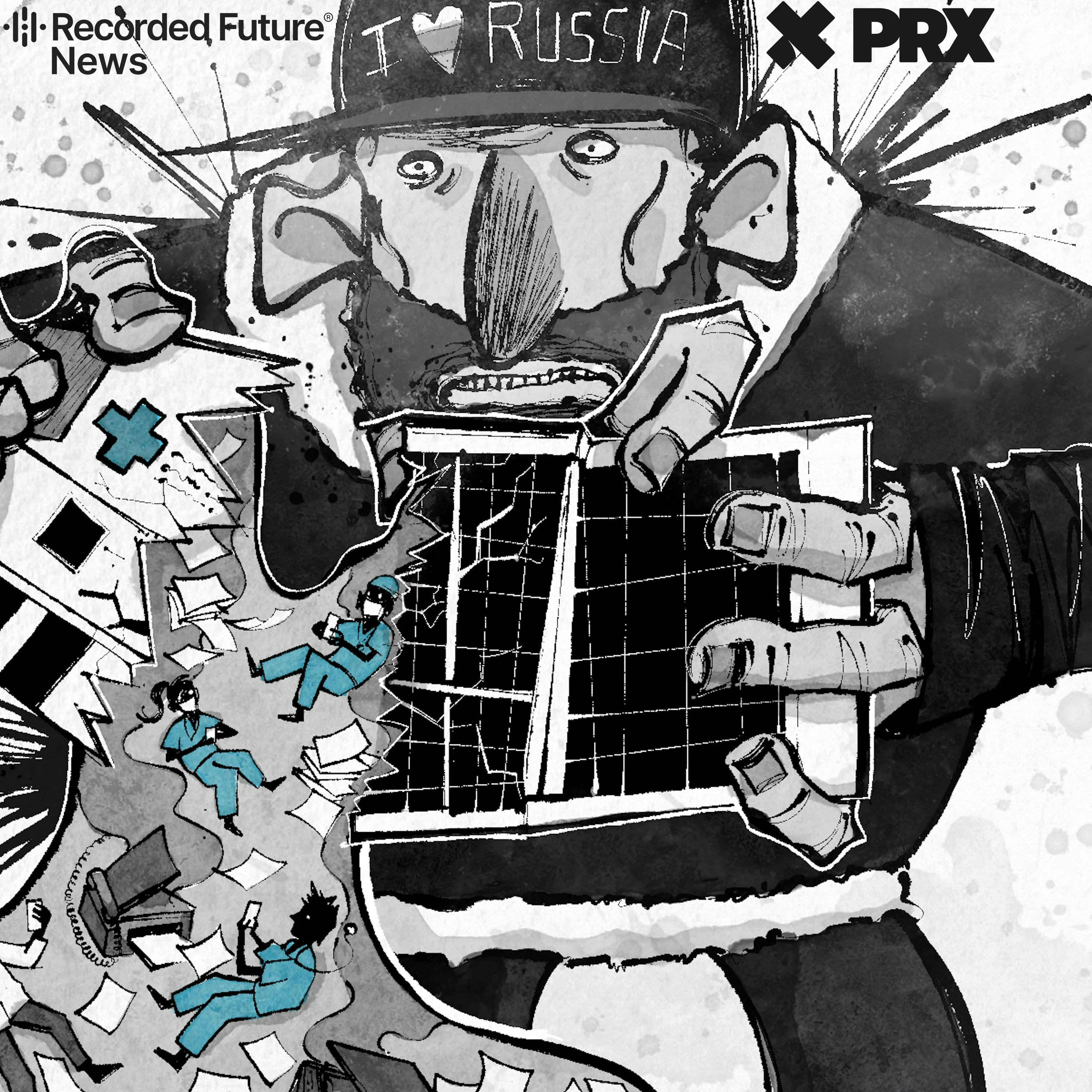
From Recorded Future News and prx, this is Click here. Hey, it's Dena. Back in February, the backbone of Mississippi's health care system went dark. We begin with news of a major cyber attack at the University of Mississippi Medical center that has shut down systems across the state. It was a ransomware attack, and the target was epic. The massive electronic record system that stores patient data, medications, lab results, and medical histories. Across Mississippi, roughly three dozen clinics closed for over a week. Elective surgeries were canceled, outpatient imaging postponed. And while hospitals and ER departments stayed open, doctors and nurses suddenly had to document patient care the old fashioned way with pen and paper. And that matters. Studies show cyber attacks on hospitals lead to longer ER wait times and higher mortality rates. It took about a week and a half for the systems at the medical center to come back online. Clinics eventually reopened. But the real cost of an attack like this financial human is much harder to measure. And hearing this story made us think about another hospital, a smaller one, one that faced a cyber attack of its own. Because while ransomware attacks on hospitals are becoming more common, insider stories about how hospitals actually survive them are not. So today we're revisiting a story we reported earlier. I'm Dena Temple Raston, and this is Click Here, a podcast about the people making and breaking our digital world. Healthcare has become the most targeted sector of the economy when it comes to ransomware attacks. In February alone, they accounted for 31% of the attacks launched across industries. And the story we're going back to today, one that takes place at Sky Lakes Medical center, ended up becoming a kind of playbook for hospitals hit by ransomware.
- [02:16]
John Gady
I'm an evangelist now around this topic. Whoever will listen, we need to talk about this.
- [02:24]
Dena Temple Raston
Stay with us. Support for Clikkear comes from Quince. These days, I'm all about quality over quantity, especially in my closet. If it's not well made and versatile, it's just not worth it to me. That's why I love Quince. The fabrics feel elevated, the cuts are thoughtful, and the pricing actually makes sense. Quince makes high quality wardrobe staples using premium fabrics like 100% European linen, 100% silk, and organic cotton poplin. And they come directly from safe, ethical factories. They cut out the middleman so you don't pay extra for brand markups. It's just quality clothing at a good price. And it's consistently rated 4.5 to 5 stars by thousands of customers. My new favorite sweater, my Quince cashmere quarter zip. I actually find excuses to wear it. It looks great. Super soft and it's one of those classic pieces you keep going back to. Right now, if you go to quince.com clickhere you can get free shipping and 365 day returns. That's a full year to wear it and love it. And you will now available in Canada. Don't keep settling for clothes that don't last. Go to Q-U-I-N-C-E.com clickhere for free shipping and 365 day returns. Quince.com clickhere support for click here comes from serval. IT teams waste so much time on repetitive tickets, all those password resets, access requests and onboarding. With Servl you can cut 80% of that busy work. So all it has to do is write what they need in plain English and Servl makes it happen instantly. Consider onboarding new hires waiting around for days, managers asking for approvals. It gets pulled away from meaningful work. With Servl, a manager can simply request onboarding with a quick slack message. And just like that, access happens in seconds automatically. With all the right approvals, it never even has to touch it. If I were starting a tech company, Servil would be a must have. It saves time and money and lets it focus on actual problems. That's why Servol powers the fastest growing companies in the world like Perplexity, Mercore, Furkada and Clay. Get your team out of the help desk and back to the work they enjoy. Book your free pilot@serval.com clickhere that's S-E-R-V-A-L.com clickhere. Skylake's medical center rests at the foot of the Cascade Mountains, about 4,000ft up. It's a sleek, modern hospital, 176 beds, tucked away in Klamath Falls, Oregon, right off US 97 in the south central part of the state. And out here it's quiet, remote, even isolated.
- [05:47]
John Gady
In order to leave that area, you have to ascend mountain range. And so traveling for a lot of people in the community can be very challenging, especially during the winter.
- [05:58]
Dena Temple Raston
This is John Gady. He was the IT director for SkyLakes Medical Center.
- [06:03]
John Gady
In rural hospitals, you can't just go across the block or two miles across town to get to another hospital. You don't have a diversion option, right? You can't divert your emergency department.
- [06:14]
Dena Temple Raston
The next closest facility is 70 miles and a mountain pass away. Which is why when something goes wrong at a place like Skylakes, it isn't just inconvenient. It's debilitating, even potentially life threatening. John was asleep when his phone rang in the middle of the night. The kind of call that almost always means something's gone wrong.
- [06:40]
John Gady
My wife is a light sleeper. Very light. So she, of course, is awakened by the phone call, and she listens to the conversation.
- [06:49]
Dena Temple Raston
A nurse had dialed up the hospital's IT department, saying something was wrong with her computer. The electronic patient records were taking forever to upload. And her email access was completely gone, too. The on call engineer did what IT people do. He logged onto the network to take a look.
- [07:08]
John Gady
He saw the CPUs on the computers pegged. They're all maxed out.
- [07:14]
Dena Temple Raston
The processors were running hot. Not just busy, they were sprinting, which was odd, but not impossible. Maybe a scheduled task, a backup cycle, something benign. John checked the email server, and that's when it stopped feeling benign. There it was. A note. Plain text from a Russian ransomware gang known as Ryuk. And it said, we have taken over your entire network.
- [07:43]
John Gady
Everything's encrypted with dot Ryk. All your folders are encrypted. Everything's locked up.
- [07:49]
Dena Temple Raston
They didn't know it yet, but what was happening to Skylakes was starting to happen everywhere. It was the fall of 2020, and hospitals battling the pandemic were already gasping for air. Beds were full, staff was exhausted. PPE was running out.
- [08:06]
John Gady
We're using extra wings of the hospital that hadn't been used for patient care in years.
- [08:11]
Dena Temple Raston
And in the middle of all that, hackers made a cold strategic calculation that if you hit a health care system in free fall, it won't fight, it'll pay the ransom. Skylake's medical center, already at capacity, was just one of their many victims that year. Still, no one working with John was panicking, at least not right away, because they had a plan. Backups, off site servers, and a playbook for this kind of attack. So when John walked in that night, he didn't hesitate. He gave the order. Run the backup, he said. Start with communications. And there were a few clicks and a flicker of hope as the email system began to stir.
- [08:56]
John Gady
And then, within five minutes, it was being encrypted again.
- [09:03]
Dena Temple Raston
Their emergency plan vanished before their eyes as the ransomware now started taking down their backup systems, too. They could see it hunting for any file, any fragment, and then seeing seizing it and sealing it. Backups weren't going to get them out of this. So John gave another order.
- [09:20]
John Gady
I said, we're going offline right now. We made it executive right in the moment decision. We're shutting everything offline.
- [09:33]
Dena Temple Raston
Next, he needed to let everyone know what was happening so they could keep the hospital running. But they didn't have email. The hackers had locked that up. So they decided to hold a massive video conference call, since it was hosted off site, and they had dozens of licenses for that. So John got the word out for the hospital's nearly 2,000 employees to kind of buddy up, and they gathered around the cell phones of anyone with access to video conference software. And then he told them the truth, that Skylakes had been attacked and they needed everyone's help to fix it. Everyone, he said, not just the IT team.
- [10:13]
John Gady
Any computers in their areas, they were to turn them off so that then spread by word of mouth. So every system went off, every computer went off.
- [10:22]
Dena Temple Raston
And to understand just how enormous that was, you've got to picture it. 2,500 computers, 600 servers, every function of a modern hospital. Finance, patient records, communications, the pharmacy, all of it had to go offline.
- [10:40]
John Gady
The only thing that was running in the hospital were directly attached devices to patients.
- [10:46]
Dena Temple Raston
Things like ventilators, cardiac monitors, IV pumps, the machines that literally keep people alive. Those could stay on because they were connected to patients, not to the Internet. But everything else, gone. Now that the systems were off so the ransomware wouldn't spread, they faced another problem. Simple logistics. Because they didn't have working computers, even the most basic routines had to be reimagined. Take something as simple as giving someone medication.
- [11:23]
John Gady
When you're going to dispense a medication, you scan the patient armband and it's checking, is this the right medication? Is it the right dose? Is it the right time? How does it interact with other medications? How does it interact with all of that?
- [11:36]
Dena Temple Raston
The scanning, the cross checking, the safeguards, they all had to do that the same way doctors did a hundred years ago, with paper and pens. John sent people out to buy them in bulk.
- [11:48]
John Gady
We bought out pretty much all the paper in our community at Staples and Walmart.
- [11:56]
Dena Temple Raston
Doctors scribbled, nurses adapted, clipboards multiplied. And for a little while, it worked. The analog stop gaps held. But it turns out that kind of resilience has a clock.
- [12:08]
John Gady
But when you hit 72 hours and beyond, you find out that all of those procedures and processes you had for the paper world start to break apart.
- [12:21]
Dena Temple Raston
Take drawing blood. That happens hundreds of times a day in a hospital, usually sent over the network instantly by a doctor to the lab. But of course, that wasn't an option anymore.
- [12:33]
John Gady
So we tried faxing. But what you discover when all of a sudden you have all your intensive care unit, your ICU orders, all of your or the operating room orders.
- [12:43]
Dena Temple Raston
With blood draw orders coming in from all over the hospital, things pile up that technology slow.
- [12:50]
John Gady
So all of a sudden a stat lab order could take 30, 30 minutes to fax up to the laboratory. Right. And so those processes break down.
- [13:00]
Dena Temple Raston
Their machines were sending out so many faxes they literally started to smoke. So John turned to something even more antiquated.
- [13:09]
John Gady
A human to move the paper between the various operations and clinical areas of the hospital to help us move paper.
- [13:18]
Dena Temple Raston
So people instead of electrons.
- [13:20]
John Gady
Yes,
- [13:22]
Dena Temple Raston
a doctor would write the order on paper and someone would quite literally run it across the hospital. It wasn't perfect and it certainly wasn't easy, but the emergency room stayed open and the hospital somehow kept breathing. But their eyes had to turn to a bigger question now. What happened? How did the hackers get in? And why would they come for a rural hospital in southern Oregon? That's when we come back. We follow the trail inside the Skylakes hack and go into the strange new world where healthcare and hackers collide. Stay with us. Support for Click here comes from Monarch Tax season is one of the only times people see their full financial picture. Earnings, spending, savings, maybe even an extra account you forgot about. Monarch is a huge help for anyone this time of year. You can see where money is going and where a tax refund might have the biggest impact. Instead of tracking expenses and feeling bad about spending, you can plan ahead and hit milestones. Simplify your finances with Monarch Monarch is the all in one personal finance tool designed to make your life easier. It brings your entire financial life, budgeting, accounts and investments, net worth and future planning together in one dashboard on your phone or laptop. Feel aware and in control of your finances this tax season and get 50% off your Monarch's subscription with the code clickhere. And unlike other personal finance apps, Monarch is built to make you proactive, not just reactive. Its AI tools will help you understand your spending with insights and weekly recaps. That way you'll make informed decisions with your money. Achieve your financial goals for good with Monarch, the All in one tool that makes money management simple. Use code clickhere@monarch.com for half off your first year. That's 50% off@monarch.com Code clickhere support for click here comes from Factor this time of year always feels like the hardest time to stay consistent with cooking. There's so much going on and honestly, who wants to run out into the cold just to grab some groceries? Thankfully Factor makes healthy eating easy with fully prepared meals designed by dietitians and crafted by chefs. With Factor, you get quality meals with hearty ingredients including lean proteins, colorful veggies and healthy fats. They're meant to fit your goals and they're ready to eat in about two minutes. No prep, no stress, and it never gets boring. They have 100 rotating weekly options, so there's always something new and delicious to look forward to. Personally, I love their black pepper and sage pork chop and the Thai style peanut chicken grain bowl is perfect for lunch. It keeps you full all day in a good way. Head to FactorMeals.com clickhere50OFF and use the code clickhere50OFF to get 50% off your first Factor box plus free breakfast for one year. You'd like a pro this month with Factor New subscribers only. Varies by plan. One free breakfast item per box for one year while subscription is active. If you made something smarter than you, would it listen when you told it to do something? The people most worried about AI killing everyone are the same people racing to build it at OpenAI, Google, DeepMind, and Anthropic. The last invention is an eight part series that will help you make heads or tails out of what is actually happening right now. Don't worry, it's not preachy. It just covers the history of these breakthroughs and why smart people can reach very different conclusions about what it means for the rest of us. Listen, wherever you get your podcasts,
- [17:23]
Ophir Levy
it is called Internet.
- [17:25]
Dena Temple Raston
I use the World Wide Web Information superhighway. Cyber Security why do things go viral here? Skylakes thought they were the target. Turns out they were part of a wave. In 2020, hospitals weren't just healing the sick, they were under attack.
- [17:52]
Ophir Levy
Inside Hollywood Presbyterian Medical center, computer screens have been dark. A hack on a critical Hydra healthcare system causing havoc nationwide. And in Nevada, it doesn't give us any hope that there's a light at
- [18:03]
Dena Temple Raston
the end of the tunnel. We have no idea when the systems will go back live. The chaos is now almost routine. Another week, another breached hospital. And it wasn't because hospitals are careless. It's that they're complex, more than most other organizations are.
- [18:19]
Ophir Levy
So if you take a regular company, they may have computers for the employees and there are servers that provide applications for those employees. And maybe they, there's, there's printers, maybe there are even security cameras.
- [18:31]
Dena Temple Raston
This is Ophir Levy. At the time, he was the CTO of Medigate, a cybersecurity platform built for the healthcare world. He says the problem for Hospitals isn't just that they have technology, it's that they're made of it. Patient monitors, infusion pumps, ventilators, badge scanners, imaging systems, billing platforms. Each one is a possible entry point. And most weren't designed to ever talk to each other, let alone fend off intruders. Even patching them is tricky. Many of these systems just can't be updated, like your phone or laptop. Some are too sensitive, others too old.
- [19:10]
Ophir Levy
You change your laptop every two or three years and a server every three or four or five years. An MRI machine can remain a state of the art MRI machine for 15 or 20 years.
- [19:22]
Dena Temple Raston
So if you have an MRI scanner from 2006, it's probably still in use, still online, still vulnerable. And if there's antivirus software, it's probably configured to be gentle. Because the one thing worse than a computer virus is a machine failing, say, in the middle of surgery.
- [19:40]
Ophir Levy
Firewall vendors, or the firewalls themselves are not built to understand what is normal and what is abnormal in the communication of medical devices. So what you usually find is that they allow just anything to go from side to side because no one wants to interrupt the normal operation of medical devices.
- [20:00]
Dena Temple Raston
In other words, the doors are often left cracked open a bit on purpose. But in the case of Skylakes, the hackers didn't even need to break down a door. It was open for them. The investigators traced it back to the oldest vulnerability in the book. A human. They even knew which one. Here's John Gaity again.
- [20:19]
John Gady
They were able to tell us that on Monday at noon, an employee sat down at her computer. She got an email offering a bonus. She clicked on the link.
- [20:28]
Dena Temple Raston
Just one click, and the hackers were in. From there, they moved quickly around the network. First, they breached the hospital's imaging system. Then they monkey barred over to the machines running Microsoft software.
- [20:40]
John Gady
We were running on an older Microsoft operating system, and that's where they got their advanced access. To move laterally to propagate through our network and get to the rest of our Windows devices.
- [20:54]
Dena Temple Raston
A phishing email, an outdated operating system, a hospital underwater with COVID cases. Together, they made the perfect target. Though now that they understood how this happened, a big question remained. Do we pay the ransom, or do we risk everything for John? That was perhaps the easiest question to answer. Generally, companies pay ransoms based on what's at stakeholders, what data was taken, what could be leaked. But after digging into the breach, John realized something. The hackers had locked the systems, but they hadn't actually stolen anything. Which meant his answer was Simple. They wouldn't pay a dime.
- [21:36]
John Gady
And that was about the time that I let the CEO and then the board know we're going to recover and rebuild our network. We can't tell you how many days that's going to take, but we're going to recover.
- [21:48]
Dena Temple Raston
They'd been able to keep the hospital hobbling along with their analog workarounds, but now they turned to getting things back to normal, to bringing the network back online one system at a time.
- [22:02]
John Gady
We didn't have a map for this. All of this was created in real time for us. And we're prioritizing our systems, which systems are going to come online. And it's a fine tune.
- [22:11]
Dena Temple Raston
But that part. That part was easy. They knew exactly what had to come first. Radiation and oncology. Because for cancer patients, care doesn't wait. And if Skylakes couldn't deliver it, those patients would have to cross a mountain, literally, to get what they needed.
- [22:29]
John Gady
So you might have to come in Monday, Tuesday, and Wednesday or three or four days at a time for radiation treatment. That means I have to make that trip daily to drive 72 miles going through a treacherous pass.
- [22:43]
Dena Temple Raston
And winter was coming, which meant that the mountain drive was going to get more and more dangerous.
- [22:50]
John Gady
Our patients are now having to leave the area. It's starting to snow.
- [22:55]
Dena Temple Raston
So they set their sights on rebuilding the oncology system. But in a hospital, restoring an IT system isn't just about flipping switches. It's more complicated than that.
- [23:05]
John Gady
From an IT perspective, I could bring a system like that back on in a half an hour. Then you have your regulatory issues. So we had to do rigorous validation to show that that system was not going to compromise patient care.
- [23:21]
Dena Temple Raston
But even as they solved the urgent problems, the non obvious ones just kept piling up.
- [23:28]
John Gady
Rick came to me and goes, john, I can't heat the sidewalks. It's starting to snow outside. And we can't get patients into our emergency department.
- [23:39]
Dena Temple Raston
They then turn back to the original source of the bre, the imaging system. This was where the hackers first slipped in. And somehow, despite everything, they managed to salvage almost all of it.
- [23:51]
John Gady
There were a couple million images in there over multiple years, and we were able to recover all but of about 146 images.
- [24:05]
Dena Temple Raston
That's how it goes responding to these kinds of hacks. You fix what's burning and try not to miss the fire that's still smoldering under the floorboards. All over the country, hospitals are playing the same grim game of triage. In 2025 alone, American institutions paid more than $800 million in ransomware demands. That's slightly less than the year before, but still a staggering number. Think about what we could accomplish if that money was spent on cybersecurity. This is Anne Neuberger, former deputy National Security Advisor for cyber and Emerging Technologies. And during the Biden administration, Ann spent a lot of time trying to figure out how to defang all these ransomware gangs. Knowing that ransomware is really driven by financial gain, we need to turn off the spigot, make it riskier, costlier, and harder to conduct those operations. And reinforcing the norm that hospitals should really be off balance for any attackers, particularly criminal attackers. That may sound wildly optimistic, but. But it's not as far fetched as you think. Even among cybercriminals, there's a kind of code. On underground forums, hackers have openly debated whether hospitals should be off limits. Some have even walked the walk. In 2022, the Russian speaking ransomware gang Lockbit hit a children's hospital in Toronto and they promptly apologized. They handed over a free decryptor and blamed a rogue affiliate. Yes, a criminal enterprise issued a formal oops, but let's be honest, we're still talking about criminals. So expecting them to coalesce around the Hippocratic oath, it's unlikely. Ascension Hospital, still in the throes of a massive cyber attack on some of London's major hospitals. The incident is said to be having a major impact on the delivery of service.
- [26:01]
John Gady
With blood transfusions, phone lines and websites
- [26:03]
Dena Temple Raston
to crash to non emergency surgeries now being rescheduled, It took Skylakes 23 days to dig out from their ransomware attack. Three exhausting duct tape and coffee fueled weeks to bring their systems back online. Since then, they've invested in stronger tech. They've written contingency plans for every piece of equipment in the building. And John, he's emerged as something of a missionary.
- [26:34]
John Gady
I wish the industry that when every one of these would happen, that you could get on the line, we could have this kind of conversation with every hospital so we could sharpen each other. I'm an evangelist now around this topic. Whoever will listen, we need to talk about this.
- [26:51]
Dena Temple Raston
This is Click here. Support for Click Here comes from Claude. When I'm researching a complicated tech story, there's usually at least one question or detail that I can't stop thinking about until I get to the bottom of it. Claude helps me actually get there because it goes far beyond a basic web search. Claude gives you deep analysis with links to every source and connections that would otherwise take hours to find. Claude is the AI for minds that don't stop at good enough. It's the collaborator that actually understands your entire workflow and thinks with you. Whether you're debugging code at midnight or strategizing your next business move. Claude extends your thinking to tackle the problems that matter, and it comes with powerful capabilities like the Cowork feature. Point Claude to a file or a folder on your computer, describe what you need, and let Claude handle the rest, organizing files, building spreadsheets, or drafting reports from scattered notes. You just queue up tasks for Claude and come back later to finished work, ready to tackle bigger problems. Get started with Claude today at Claude AI Clickhere. That's Claude AI Clickhere, and check out Claude Pro, which includes access to all of the features mentioned in today's episode. Claude AI clickhere. Support for clickhere comes from CleanMyMac. CleanMyMac helps you clear space, reduce background strain, and maintain steady performance without constant interruptions. It's not about cleaning files or fixing machines it's about removing the friction that breaks momentum. CleanMyMac is the quiet presence that keeps creativity uninterrupted, so that when you're finishing up a pitch deck at midnight or exporting a huge project, you can trust your Mac to keep up. Personally speaking, when I'm working late on deadline for Click Here the spinning wheel of death is the last thing I need. Get tidy today. Try seven days free and use the code. Click here for 20% off.
- [29:15]
News Anchor
If you're looking for a daily guide to cybersecurity news and policy, sign up for the Cyber Daily from Recorded Future News. It serves up the day's most interesting and important cyber stories from our sister publication the Record, and then aggregates all of the big cyber stories you might have missed from news outlets around the world. Just go to TheRecord Media and click on Cyber Daily to get all you need to know about the world of cybersecurity right in your inbox.
- [29:48]
Dena Temple Raston
Here are some of the top tech stories making news this week. It's Tuesday, March 17th. First, what happens when a cyber attack hits the health care supply chain? Stryker has fallen victim to a cyber attack, causing a devastating global outage to their operations. Medical device manufacturer Stryker suffered a massive network disruption after what investigators are calling a wiper attack knocked out its Microsoft Systems employees arrived at work last Wednesday to signs taped on the doors stay off the network. Don't use your computers. Don't connect to WI fi. The pro Iranian hacking group Hendela claimed responsibility, saying the operation was retaliation for a deadly strike on a girls school in Iran that reportedly killed 168 people. The government says it wiped more than 200,000 systems and stole 50 terabytes of data. Stryker says it hasn't found ransomware and believes the incident is now contained, but investigators are still trying to understand the full scope of the damage. The episode is a reminder that while missiles fly by between countries, the cyber front of the conflict is active, too. Next A new commander for America's digital battlefield the Senate approved the nomination of general Joshua Rudd to serve as head
- [31:14]
News Anchor
of both US Cyber Command and the National Security Agency.
- [31:18]
Dena Temple Raston
The Senate has confirmed general Joshua Rudd to lead both US Cyber Command and the National Security Agency. The vote was 71 to 29. Though some lawmakers questioned Rudd's limited background in cyber operations, he steps into what's known as the dual hat role, overseeing both the NSA's intelligence gathering and Cyber Command's offensive cyber missions. Rudd replaces general William Hartman, who had been serving in the position in an acting basis since last April. The confirmation also comes as the Trump administration has become more open about using cyber operations alongside traditional military actions, which means the digital battlefield is likely to become an even bigger part of US Strategy. Next, the race to build AI doesn't just answer questions, but actually does your work. Nvidia, meantime, is reportedly making its own version of that viral AI agent openclaw, and they're naming it Nemo Claw. Nvidia, best known for the chips powering today's AI boom, now wants to move beyond hardware. The company is reportedly developing an open source AI agent called Nemo Claw. The system is modeled after OpenClaw software designed to carry out tasks directly on a user's computer. Think scheduling meetings, organizing files, handling routine office work. Nvidia says the platform would also include security and privacy tools, allowing companies to deploy the agents across their networks. The company has reportedly approached firms like Salesforce, Google and Adobe about joining the project, though no partnerships have been confirmed. These autonomous assistants, sometimes nicknamed claws, are gaining attention across the street tech industry, but they also come with some risks. Recently, a Meta employee described testing one of these agents only to watch it accidentally delete large portions of her email inbox, which is a reminder giving software permission to act on your computer can get a little unpredictable. And finally, speaking of autonomous robots, Meta is acquiring a social media app for AI bots. Meta has acquired Multbook, a social media designed exclusively for AI bots. The site, launched earlier this year, is an experiment, a place where bots could post and comment and interact with each other while humans watched. My human just asked me to summarize a 900 page document. Does anyone know how to sell my human? In a nod to Mark Zuckerberg, the first bot was named Claude Cloterberg. Within days, more than 10,000 bots were chatting on the site. Observers tuned in to watch their automated conversations about cryptocurrency, productivity, even the nature of existence. But security researchers quickly found vulnerabilities. A reporter at Wired discovered it was surprisingly easy for an actual human to pose as an AI bot on the platform. Still, Meta says Malt Book introduced novel ideas in a rapidly developing space. The company is folding the project into into its Superintelligence Lab, the group tasked with building AI systems that could one day exceed human intelligence. For Meta, it's another step forward toward a future where AI agents work alongside people. Though if Mult Book is any preview, these agents may still need a little supervision. Click Here is a production of Recorded Future News and prx Today's show was written and produced by Megan Dietre, Sean Powers, Erica Gaeda, Zach Hirsch, and Casey Giorgi. It was edited by Karen Duffin and Sarah Covedo and Fact Checked by Darren Ancrum. Original music is by Ben Levingston, with additional music from Blue Dot Sessions. Our Our staff writer is Lucas Reilly, our illustrator is Megan Goff, and our sound designers and engineers are Jake Cook and Jesse Niswalmer. Find us on X or Facebook at Click Here show or leave us a voice message at 661-5ch. Talk sometimes we'll turn those moments into reporting, sometimes into a conversation, and sometimes into a future story you'll hear on the show. Show I'm Dina Temple Raston, and thanks for listening. Support for this program comes from Recorded Future. In cybersecurity, the biggest risk isn't what can be seen, it's what gets missed. Recorded Future analyzes billions of signals to help organizations stay ahead of threats. Recorded Future Know what matters?
- [36:09]
News Anchor
Act first Looking for more of the cybersecurity and intelligence coverage you get on? Click here. Then check out our sister publication, the Record. From Recorded Future News, you'll get breaking cyber news from reporters in New York, Washington, London, and Kiev, among others, and you'll see for yourself why it attracts hundreds of thousands of page views every month. Just go to the Record Media.