Loading summary
Transcript132 lines
- [00:00]
Carvana Salesperson
Thanks for selling your car to Carvana. Here's your check.
- [00:03]
Carvana Customer / Cliff Stoll
Whoa. When did I get here?
- [00:04]
Carvana Salesperson
What do you mean?
- [00:05]
Carvana Customer / Cliff Stoll
I swear it was just moments ago that I accepted a great offer from Carvana online. I must have time traveled to the future.
- [00:10]
Carvana Salesperson
It was just moments ago. We do same day pickup. Here's your check for that great offer.
- [00:15]
Carvana Customer / Cliff Stoll
It is the future. It's.
- [00:17]
Carvana Salesperson
It's the present. And just the convenience of Carvana. Sorry to blow your mind.
- [00:21]
Carvana Customer / Cliff Stoll
It's all good. Happens all the time.
- [00:24]
Narrator / Sally Helm
Sell your car the convenient way to Carvana.
- [00:28]
Carvana Salesperson
Pick up. Times may vary and fees may apply.
- [00:30]
TJ Watt
I'm NFL linebacker TJ Watt and this is my personal best. YPB by Abercrombie is the activewear I'm always wearing. That's why I reached out to co design their latest drop. I worked with designers to create high performance activewear that holds up to my toughest workouts. Shop YPB by Abercrombie in store online and in the app. Because your personal best is greater than anything.
- [00:58]
History Channel Announcer
The History Channel Original Podcast.
- [01:05]
Narrator / Sally Helm
History this week, September 10, 1986. I'm Sally Helm. It's 7:51am A quiet morning in Berkeley, California. Cliff Stoll wakes up. His pager is ringing. For a while now, he's been monitoring the computer system at Lawrence Berkeley Lab where he works as a systems administrator. His main concern is keeping the computers running 247 so that scientists at the lab can use them for research. But today, he's on a different mission. He's tracking a computer user who has been breaking into the network. A hacker. Cybersecurity isn't his job. In fact, the term hasn't even been invented yet. Regardless, Cliff is on the case. He's not sure what this hacker is up to. Could be harmless, but he wants to find out. And today, his beeping pager tells him that that hacker is back. Stoll heads to his office at the lab, and there he learns that when the intruder logged in this time, they used a connection in the lab's network to access another computer network over 2,000 miles away, near Huntsville, Alabama, at the US Army's Redstone Missile Complex. And this hacker wasn't just browsing. They'd exploited a bug to become a software super user, likely able to insert their own programs into the code at this military installation. Stoll immediately dials the security team at Redstone to let them know. As it turns out, they already do know. They've been monitoring this hacker's activity on their network for four months. And Cliff Stoll is like what, some hacker is running freely through a highly sensitive military computer network and they're just allowing it to. It turns out Redstone had called both the FBI and the Army's Criminal investigation Division, but neither was interested in pursuing the case. Not only is cybersecurity not really a thing, but neither is cyber crime. The consensus was that this was probably some harmless kid, maybe a high school student who's good at computers. Probably just curious. Nothing to see here, but Cliff Stoll can't accept that something isn't right today. Cliff Stoll versus the Hanover hacker. How did a 75 cent bookkeeping error lead him to uncover an international espionage operation? And how did this shape the future of Cybersecurity?
- [04:06]
Carvana Customer / Cliff Stoll
So it's 1986. I was working at the Keck Observatory designing an off axis hyperbolic segment.
- [04:12]
Narrator / Sally Helm
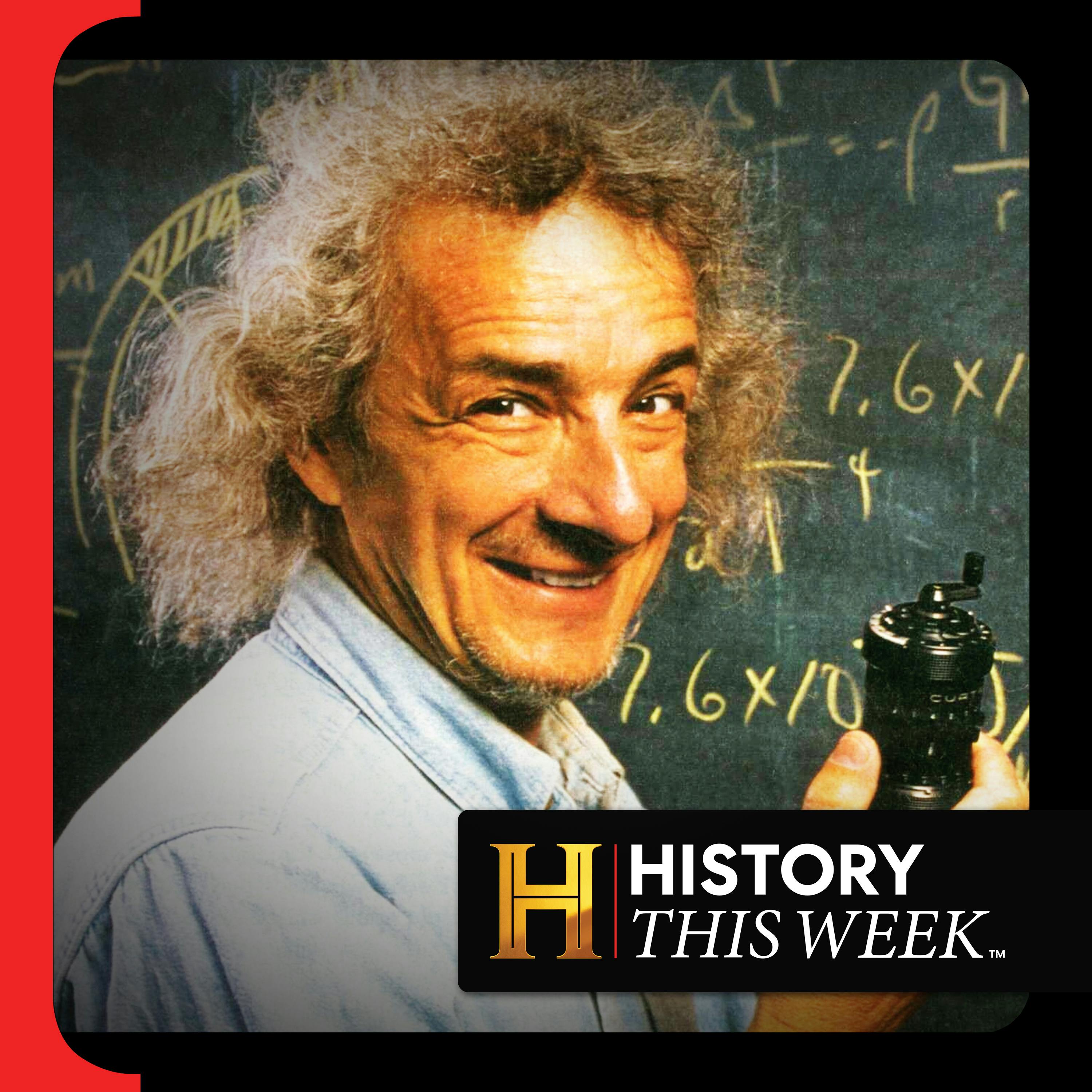
That is Cliff Stoll. He is now 75 years old, talking to us from his makeshift lab. He's got long, wild white hair, looks a little like Doc Brown from Back to the Future. And as excited as Doc Brown was about time travel, that's how Cliff Stoll gets about his specialties.
- [04:34]
Carvana Customer / Cliff Stoll
My background's in astronomy, computing and physics.
- [04:38]
Narrator / Sally Helm
Back in 1986, he's in Berkeley, California, helping to design a telescope, the astronomy.
- [04:45]
Carvana Customer / Cliff Stoll
Group at Lawrence Berkeley Labs.
- [04:46]
Narrator / Sally Helm
But then his grant money runs out.
- [04:49]
Carvana Customer / Cliff Stoll
So I looked around and said, well, I'd better figure out what to do.
- [04:52]
Narrator / Sally Helm
Now he ends up in the basement of the same lab in the computer center.
- [04:57]
Carvana Customer / Cliff Stoll
I went down and started working on.
- [04:59]
Narrator / Sally Helm
Just being a sysadmin, that's a systems administrator. This is the person responsible for the configuration and security of computer networks. And just two days into the job, something weird happens.
- [05:12]
Carvana Customer / Cliff Stoll
Somebody calls us and says, hey, Glif, the accounting system has crashed.
- [05:18]
Narrator / Sally Helm
The accounting system accounts for each user's time on the computer. They're charged by the second.
- [05:27]
Carvana Customer / Cliff Stoll
So if you want to use our computers, you're going to pay for it. This was 40 years ago when computers were not yet commonplace. They were quite rare.
- [05:36]
Narrator / Sally Helm
And Cliff Stoll's lab is connected to a very primitive version of the Internet.
- [05:41]
Carvana Customer / Cliff Stoll
You used something called a modem and a telephone. And telephones were connected with these things called wires. You'd have a dedicated pair of copper wires going from the phone over here along the wall out up to the telephone pole, from that telephone pole to a central office, from that central office through a switch connecting to the long distance line.
- [06:06]
Narrator / Sally Helm
But again, to get onto the Internet, you'd need to be one of the few people on Earth with access to.
- [06:13]
Cybersecurity Expert JJ Widener
A computer really, it was military installations, higher education institutions performing research. Those were the ones that were on the backbone of the Internet.
- [06:22]
Narrator / Sally Helm
That is cybersecurity expert JJ Widener. He said if you did have a computer, you'd still need a login, a username and password for the network you're trying to access. As you may know, people often use very guessable passwords.
- [06:38]
Cybersecurity Expert JJ Widener
Oh, my goodness. Like, don't make them your kids names. 1, 2, 3, 4, 5. If you're really secure, you put an exclamation mark at the end, because everybody knows that exclamation mark is going to protect you to the nth degree.
- [06:50]
Narrator / Sally Helm
And once you had a password, everything was kind of up for grabs.
- [06:54]
Cybersecurity Expert JJ Widener
Whenever you logged in, you could almost communicate with anything that was on there, kind of like it is now. I can hop on the Internet and I can start communicating. If you don't have a good firewall, you know, if it's wide open.
- [07:08]
Narrator / Sally Helm
Okay. So Cliff Stoll is told that this accounting system that tracks all the network activity at Lawrence Berkeley Labs and charges money for it has crashed. Turns out the error is caused by a 75 cent discrepancy on the balance sheet. And that seemingly tiny fact means that a mystery user had logged in to the network.
- [07:32]
Carvana Customer / Cliff Stoll
A user had been added to one of the computers without being added to the accounting system. This person had used 75 cents worth of computer time.
- [07:43]
Narrator / Sally Helm
There could be legitimate causes for this 75 cent error. Like, say you were a researcher working on a paper about orbital dynamics. You might dial into the Lawrence Berkeley Lab computer center and take a quick look at their database. So maybe this was legitimate, but it could be something else.
- [08:03]
Carvana Customer / Cliff Stoll
This is interesting. My curiosityometer moved into the yellow zone. I started out saying it's probably somebody at my laboratory, Lawrence Berkeley Labs, yanking my chain. Maybe it's some high school student.
- [08:16]
Narrator / Sally Helm
Yep, that's a possibility, too. At this stage of the Internet, many users are curious young people exploring this new world of networked information, sometimes with unintended consequences. Now, of course, the last possibility is that this could be something really illegitimate. Some kind of hacker with a nefarious purpose in mind. Stoll finds the account with a 75 cent charge and deletes it. If someone had been sneaking in to use the system, they'd have to find another account to use. The next day, Stoll gets an email from a company that provides network services to sensitive government agencies. And this networking company says, hey, overnight, someone from your network tried breaking into our network. Stoll looks at the logs and finds that only One user was logged in at the Sventek and Joe Sventek was.
- [09:16]
Carvana Customer / Cliff Stoll
A real person, a well known computer jock that used to work at Lawrence Berkeley Labs.
- [09:21]
Narrator / Sally Helm
But Sventek wasn't there anymore.
- [09:25]
Carvana Customer / Cliff Stoll
He had moved out a year earlier and probably had never disabled his account.
- [09:31]
Narrator / Sally Helm
Had Sventech reactivated his account after a year away from the lab and then used it to try to break into a government network? Highly unlikely. So Cliff Stoll sets up a trap.
- [09:49]
Rula Therapy Advertiser
On this show we spend a lot of time talking about how people in history dealt with stress, upheaval and uncertainty. Imagine if they had therapy. I'll be honest, therapy has been a big help in my own life. Having a space to work through stress or burnout has made me more grounded. And I know a lot of people could benefit from that too. But here's the Finding a therapist is hard, and finding one who takes your insurance almost impossible. Most online platforms don't work with insurance at all, which means you're left paying full price out of pocket or signing up for an expensive subscription. That's why I really like Rula. They do things differently. Rula partners with over 100 insurance plans, so the average copay is just $15 a session, sometimes even zero. That's real therapy with licensed professionals at a price that actually makes sense. And it's not random matching. Rula considers your goals, your preferences, your background. They connect you with a curated list of in network therapists who are actually aligned with what you need. No wait lists, no frustrating back and forth. Appointments are often available as soon as the next day. And Rula doesn't disappear once you've matched. They stay with you on your journey, checking in to make sure your care is helping you move forward. Thousands of people are already using Rula to get affordable, high quality therapy that's actually covered by your insurance. Visit rula.com htw to get started. After you sign up, you'll be asked how you heard about them. Please support our show and let them know we sent you. That's r u l a.com htw. You deserve mental health care that works for you, not against your budget.
- [11:34]
Erin Moriarty
In 2013, two brutal murders left the city of Davis, California paralyzed in fear.
- [11:41]
Cybersecurity Expert JJ Widener
The victims were an elderly couple.
- [11:43]
Carvana Customer / Cliff Stoll
It was up close and personal.
- [11:45]
Erin Moriarty
I'm 48 Hours correspondent Erin Moriarty. I thought I had seen it all until I encountered the mastermind behind those murders.
- [11:54]
Carvana Customer / Cliff Stoll
He's. I think the word is psychotic.
- [11:57]
Erin Moriarty
This is 15 Inside the Daniel Marsh Murders. Follow and listen to 15 Inside the Daniel Marsh Murders on the Free Odyssey app. Or wherever you get your podcasts. When did making plans get this complicated? It's time to streamline with WhatsApp, the secure messaging app that brings the whole group together. Use polls to settle dinner plans, send event invites and pin messages so no one forgets mom 60th and never miss a meme or milestone. All protected with end to end encryption. It's time for WhatsApp message privately with everyone.
- [12:38]
Narrator / Sally Helm
Learn more at WhatsApp.com September 1986. Cliff Stoll has a plan. He's now getting alerts every time this rogue user Sventek logs into the Lawrence Berkeley Labs network. Because what is Sventek up to? He wants to find out.
- [12:58]
Carvana Customer / Cliff Stoll
The way to do it is to print out traffic. All the information coming in, all of it going out.
- [13:05]
Narrator / Sally Helm
The lab's network is connected to the outside world through 50 different phone lines, each with their own stream of activity. Which means Stoll needs 50 printers to print a record of every keystroke, every command entered on each of those 50 phone lines.
- [13:27]
Carvana Customer / Cliff Stoll
One of the very few things I learned in graduate school school was that it's a lot easier to apologize afterwards than to get permission in advance. So I waited around till 5:30 or 6 on a Friday afternoon. Then I went around with one of these push carts going from office to office, liberating people's critters and carrying down to the basement at Large Berkeley Labs and hooked them up so that every time somebody would connect into the machine, it would print out whatever they were typing.
- [14:01]
Narrator / Sally Helm
All of this network activity is being printed out in real time, and Stoll wants to be there to catch Sventek in the act.
- [14:10]
Carvana Customer / Cliff Stoll
So I just rolled out a sleeping bag, got some foam rubber under me. Remember this is 1980s, when one computer took up four or five rack panels filled with fans, and there are fluorescent lights overhead because they don't want any incandescent to poison the atmosphere. Every now and then there were these things called teletypes that would go clackety, click, clack, clack. It was like trying to sleep in a noisy room where there's a lot of traffic next to you. Eventually you get tired enough that you're able to sleep. Next morning I wake up and look over at my critters, and I'll be damned. One of them has 10, 20, 30ft of printout coming out of it. I'm looking at this printout and I could see somebody connecting into a computer, shutting off the local accounting system and then going out over our Internet connection, trying to break into 20 or 30 military computers across what was then known as the Milnet.
- [15:15]
Narrator / Sally Helm
This is kind of the worst case scenario. Sventech, or whoever is pretending to be Sventech, is using Lawrence Berkeley's network to break into the US Military's computer network.
- [15:29]
Carvana Customer / Cliff Stoll
This is not what you expect to find on a physics computer in Berkeley. I mean, it's Berkeley. I figure somebody might be searching for things like granola recipes, but no, they're searching for things like nuclear bomb secrets.
- [15:46]
Narrator / Sally Helm
And Cliff Stoll now has access to all of Sventek's activities, which he reads through page by page.
- [15:55]
Carvana Customer / Cliff Stoll
I'm looking at this, and I could see how they're doing it. They're logging in as guests, they're logging in as anonymous. Sometimes they log in with already known usernames and passwords.
- [16:07]
Cybersecurity Expert JJ Widener
He was able to use that account and then pivot and use a vulnerability on the system to escalate his privileges.
- [16:14]
Narrator / Sally Helm
J.J. widener again.
- [16:16]
Cybersecurity Expert JJ Widener
And once he escalated his privileges, meaning he was like an administrator of the system. Now, he started planting these little eggs everywhere on the system and other systems to make sure he had an established presence. So if one account got turned off, he would have another account.
- [16:32]
Carvana Customer / Cliff Stoll
I'm, like, stunned. I mean, I get pissed off. So naturally, we did what any other bureaucracy would do. We held a meeting.
- [16:42]
Narrator / Sally Helm
Cliff shows all of these printed out records to his boss, Dave Shirley.
- [16:47]
Carvana Customer / Cliff Stoll
Dave says to us, look, this guy is a threat to what we're doing. He has no authority to be there. I want him caught and shut down. I want you to nail the bastard.
- [17:00]
Narrator / Sally Helm
Cliff gets the green light to spend more time tracking Sventek. The lab's attorney also escalates the case and contacts the FBI office in Oakland.
- [17:12]
Carvana Customer / Cliff Stoll
The FBI says, oh, my God, that's serious. How long has it been going on for? How much money have you lost? I said, well, we've lost about 75 cents in computing time. And the guy says, right now it ain't worth my time to even listen to you when you lose half a million dollars. Call me back.
- [17:35]
Narrator / Sally Helm
They are able to get local law enforcement on board the Oakland district attorney and to work with them. Stoll, of course, sets up a system.
- [17:45]
Carvana Customer / Cliff Stoll
I built an alarm system so that every time this guy would come into my system, it would call out on a Radio Shack dialer, call my pocket pager. I'd get a beep, beep, beep. I'd look at it. I'd say, ah, Sventech is active.
- [18:00]
Narrator / Sally Helm
Every time Sventec logs on, Stoll calls the Oakland police, I'd run over to.
- [18:06]
Carvana Customer / Cliff Stoll
The nearest payphone, throw a quarter in and call my local police, and they would call up a telephone company. They in turn, would send a technician through to read off what line is connected to what and figure out what number it's coming from. It wasn't simple. The whole process might take half an hour. It might require two hours. Phone traces were really complex.
- [18:32]
Cybersecurity Expert JJ Widener
They would have to start the physical trace, you know, on the phone line. So he was persistent. It was like almost the same day over and over. And then just logging what he learned.
- [18:42]
Narrator / Sally Helm
This goes on for weeks. Cliff meticulously records each network intrusion.
- [18:49]
Carvana Customer / Cliff Stoll
In physics, if you don't write it down, it didn't happen. So I keep a notebook. Every time this hacker comes in, I write down date, time, what do I observe, what's happening, and so on.
- [19:02]
Narrator / Sally Helm
Then Stoll gets an unexpected call from the national security agency, the nsa, the big guns.
- [19:10]
Carvana Customer / Cliff Stoll
Somebody from the NSA calls me and says, I hear you've got some computer security problems. They say, can I have a copy of your notebook? So I go to the photocopier, copy it, send it off to the nsa.
- [19:22]
Narrator / Sally Helm
Stoll hopes they're finally taking this seriously, that they're going to do something. But then he realizes maybe not.
- [19:30]
Carvana Customer / Cliff Stoll
He says, look, we're at the nsa. I can't even confirm that I'm talking to you. They want to know what was happening. But help me. No, come on, They've got other fish to fry.
- [19:44]
Narrator / Sally Helm
Then another phone call from the CIA.
- [19:48]
Carvana Customer / Cliff Stoll
They sent some agents out to talk to me. It was bizarre. We go over to blondie's pizza, and there are these two CIA agents wearing suits and ties when everybody else is wearing, you know, flannels and grateful dead t shirts.
- [20:08]
Narrator / Sally Helm
But the CIA, also, just curious, they don't want to participate. This investigation isn't getting any help from the feds. And at this point, Stoll's mission to find the hacker has been going on for months.
- [20:23]
Carvana Customer / Cliff Stoll
The hard part for me was to convince my boss to allow me to continue to work on this. My boss kept saying, we have no budget for computer security, so you can do this as a hobby as long as you keep doing your system manager stuff.
- [20:40]
Narrator / Sally Helm
So cliffstol keeps his two systems admin and cyber detective, filling up his logbook every time Sventek logs in, tracking his activity. Until one day, A breakthrough. Up until now, he'd had no idea where Sventek might have been logging in from.
- [21:01]
Carvana Customer / Cliff Stoll
They found that the connection came from Lawrence Berkeley labs through Oakland switching system across north America, over from a place in northeastern Virginia called mitre.
- [21:11]
Narrator / Sally Helm
Mitre Inc. Is a defense contractor.
- [21:15]
Carvana Customer / Cliff Stoll
So I call up their sysadmin and they say, it's impossible that anyone could possibly break into your computer from our system because we have a secure computer. We have passwords, we have users and accounts that are secure. It's impossible. I said, look at the logs of your outbound modems. And they did, and said, uh, oh, we have a problem. This is serious stuff.
- [21:43]
Narrator / Sally Helm
The records showed that someone was logging into mitre's systems and using their outbound modems to access computers across the US.
- [21:52]
Carvana Customer / Cliff Stoll
And they shut off all incoming and outgoing traffic in and out of Mitre.
- [21:57]
Narrator / Sally Helm
And then Sventech goes dark.
- [22:03]
Carvana Customer / Cliff Stoll
It worked for a week. Nobody broke into our systems. And then, bam, here they come again.
- [22:09]
Narrator / Sally Helm
The hacker has adapted. They've gone digital. No phone lines.
- [22:14]
Carvana Customer / Cliff Stoll
They're coming over a very primitive early digital system called Timenet.
- [22:19]
Narrator / Sally Helm
And because Timenet is a digital service, the process of completing a trace is streamlined.
- [22:26]
Carvana Customer / Cliff Stoll
They're able to just trace the digital information.
- [22:30]
Narrator / Sally Helm
And that trace leads well outside the United States.
- [22:36]
Carvana Customer / Cliff Stoll
By December of 1986, four or five months into this whole project, they're able to identify it as coming from the.
- [22:42]
Narrator / Sally Helm
City of Hannover Hanover, Germany, across the ocean. In a country currently split in two by the Cold War, this lone hacker trying to obtain American military secrets might be connected to something much, much bigger.
- [23:10]
State Farm Announcer
This episode is brought to you by State Farm. Checking off the boxes on your to do list is a great feeling. And when it comes to checking off coverage, a State Farm agent can help you choose an option that's right for you. Whether you prefer talking in person on the phone or using the award winning app, it's nice knowing you have help finding coverage that best fits your needs. Like a good neighbor, State Farm is there.
- [23:37]
History Channel Announcer
Lowe's knows you've got a job to do, and we help get it done. With the Myloes Pro Rewards program, eligible members save more with volume discounts on qualifying orders through a quote of $2,000 or more. Join for free today. Lowe's we help you save offer can't be combined with any other discount contract and or special pricing exclusions. More terms and restrictions apply. Details@lowe's.com Terms subject to change.
- [24:06]
Indeed Advertiser
This episode is brought to you by. Indeed, when your computer breaks, you don't wait for it to magically start working again. You fixed the problem. So why wait to hire the people your company desperately needs? Use indeed sponsored jobs to hire top talent fast. And even better, you only pay for results. There's no need to wait. Speed up your hiring with a $75 sponsored job credit@ Indeed.com podcast terms and conditions apply.
- [24:39]
Narrator / Sally Helm
By January of 1987, with the revelation that SF BendTech is based in Germany, the FBI has finally joined the investigation.
- [24:50]
Carvana Customer / Cliff Stoll
If you bother somebody often enough, eventually they'll learn your name. You'll annoy them enough that their no will morph into a maybe. And if you apply enough pressure that maybe you can squeeze out into sort of a yes.
- [25:06]
Narrator / Sally Helm
The FBI works with the German phone company to trace Sventek's origins. The hacker had gone digital, but they still had to use a phone line from their point of origin.
- [25:17]
Carvana Customer / Cliff Stoll
They're able to get the bundlespost, the German telephone operator, to begin making phone traces.
- [25:25]
Narrator / Sally Helm
Cliff Stoll works with the FBI to set up yet another phone tracking system. This time, whenever Stoll is notified on his beeper that Sventek has accessed the Lawrence Berkeley lab network, he has to call the FBI, who calls the German police, who calls the German phone company. Then they have to send out a technician to manually track the signal.
- [25:47]
Carvana Customer / Cliff Stoll
Some guy had to take his pajamas off and put on clothing, drive downtown, go up to the third floor of the switching system in Hanover, figure out what number was going out and trace backward to see where it was coming from.
- [26:04]
Narrator / Sally Helm
This whole process can take several hours, and if Sventech logs off, they lose the trace. So Stoll gets good at keeping the hacker entertained.
- [26:17]
Carvana Customer / Cliff Stoll
How do I get the hacker to stay on my system for an hour, two, three hours? We know that he's looking for defense related stuff. He's looking for nuclear information. He's looking for things related to rocket launching and missile data. So I know what to do. I'll build a collection of completely bogus files about a military network called the Strategic Defense Initiative Network, SDI net, tons and tons of stupid bureaucratic memos so that it would take him a couple hours to download it all today.
- [27:01]
Narrator / Sally Helm
Cybersecurity experts would call that a honey pot.
- [27:04]
Carvana Customer / Cliff Stoll
You put a pot of honey out there so that people will go in and have all the food they want. Meanwhile, you are tracing them backwards.
- [27:13]
Narrator / Sally Helm
The honey pot works. After a few weeks, they have an.
- [27:18]
Carvana Customer / Cliff Stoll
Address, number 16 Lachsestrasse in Hanover, Germany.
- [27:25]
Narrator / Sally Helm
And eight months after a 75 cent accounting error, they have their hacker.
- [27:31]
Carvana Customer / Cliff Stoll
My sweetie and I are dancing in the backyard singing Ding Dong, the witch is dead. The powers that be have figured out who's responsible for it. Presumably they'll bust them and everything will be fine. But the German Bundeskriminaut, the German version of the FBI, says let's wait a while. Let's just Watch and see.
- [27:57]
Narrator / Sally Helm
Another government agency that wants to wait. So Stoll keeps adding to the honeypot, generating more files for the fake Strategic Defense Initiative network.
- [28:08]
Carvana Customer / Cliff Stoll
They keep swallowing it all. A week goes by, Two, three weeks, a month. Two, three months goes by.
- [28:16]
Narrator / Sally Helm
Stoll thinks they're wasting their time.
- [28:18]
Carvana Customer / Cliff Stoll
But then I'll be damned. A letter comes in. Not from Germany. It comes in from Pittsburgh, Pennsylvania. Huh?
- [28:30]
Narrator / Sally Helm
A letter from someone named Laszlo Belo asking for more information on Cliff Stole's entirely made up SDI Net.
- [28:39]
Carvana Customer / Cliff Stoll
The only place they could have found out about this completely fictitious network was the files that were sent from Berkeley and wound up in Hanover, Germany.
- [28:49]
Narrator / Sally Helm
Whoever this Laszlo Balo was, he's somehow connected to this hacker in Germany.
- [28:55]
Carvana Customer / Cliff Stoll
So I did exactly what you were doing. I say, okay, hot damn. I call up the FBI and say some guy wrote Laszlo Bailo, Pittsburgh, Pennsylvania. And the guy at the FBI says, whatever you do, whatever you do, don't touch that piece of paper. It's got fingerprints on it.
- [29:13]
Narrator / Sally Helm
Laszlo Bello is a bit of a man of mystery, claiming at various points to have been a Hungarian refugee, a diamond dealer, a CIA hitman. He'd most recently showed up in the newspaper as an FBI informant on an unrelated case. And turns out Laszlo Belo is connected to the kgb. The Soviet spy agency had used him to verify the the information passed along by a hacker in Hanover, Germany named Markus Hess, AKA Sventek.
- [29:48]
Carvana Customer / Cliff Stoll
These hackers were by no means just a bunch of kids fooling around, but were on the puppet strings of Eastern European, East German and Bulgarian and Russian intelligence organizations.
- [30:04]
Narrator / Sally Helm
Marcus Hess is part of a ring of hackers who had broken into nearly 400 computers around the world to steal information which they had then sold to the kgb. The Hanover hacker affair becomes a watershed moment in the history of computing and cybersecurity. Before this, even though it was almost exclusively used by research institutions and government agencies transmitting sensitive of information, the Internet wasn't really seen as a place that law enforcement would need to patrol.
- [30:38]
Carvana Customer / Cliff Stoll
But now this little special area has become a place that governments and spy agencies have discovered and are beginning to sniff around. It was the end of Innocence of the Internet. It took about a year from detecting these people breaking into our computers in August of 1986 to arresting them in summer of 1987.
- [31:13]
Narrator / Sally Helm
Cliff Stoll testifies against the Hanover hackers at their trial in Germany. In the end, only one of the hackers was convicted. Marcus Hess. He was given a suspended sentence of 20 months. The Berlin Wall had just come down and Cold War mania was fading away. But Cliff Stoll is invited to testify before the US Senate about his entire investigation. His dogged pursuit, and the legal precedent set by this case serve as a wake up call.
- [31:45]
Cybersecurity Expert JJ Widener
He was taking in logs. He was looking at connectivity patterns. He was looking at what systems are connecting to what systems, what accounts are being utilized. All that stuff is exactly what cybersecurity defense operations does. Yeah, he definitely wrote the book on some of this stuff, man.
- [32:01]
Narrator / Sally Helm
Soon, federal agencies were spinning up dedicated cybercrime units, and around the world countries started working together like never before to track hackers across borders. All because of 75 cents.
- [32:17]
Carvana Customer / Cliff Stoll
When something's there and you can't figure it out, it's not a problem. It's an opportunity.
- [32:30]
Narrator / Sally Helm
Thanks for listening to History this Week, a Back Pocket Studios production in partnership with the History Channel. To stay updated on all things History this Week, sign up@historythisweekpodcast.com and if you have any thoughts or questions, send us an email at History this week@history.com Special thanks to our guests, Cliff Stoll, astronomer, teacher and author of the Cuckoo's Tracking a Spy through the Maze of Computer Espionage and JJ Widener, cybersecurity expert currently serving as Director of Cybersecurity Architecture at Kimberly Clark. This episode was produced and sound designed by Dan Rosado. It was also produced by me, Sally Helm for Back Pocket Studios. Our executive producer is Ben Dickstein from the History Channel. Our executive producers are Eli Lehrer and Liv Fiddler. Don't forget to follow rate and review History this Week, wherever you get your podcasts and we'll see you next week.